In this post, I will show you NAC deployment strategies for Small and Medium-Sized Businesses.
Small and medium-sized businesses (SMBs) are increasingly the targets of cyberattacks. Once considered too small to be of interest to malicious actors, they are now seen as soft targets, often lacking the robust cybersecurity infrastructure of larger corporations.
Data from recent cybersecurity reports indicate that a significant percentage of all cyberattacks are aimed at small businesses. This evolving threat landscape underscores the necessity for SMBs to adopt advanced security measures. One of the most effective, yet often overlooked, solutions is Network Access Control (NAC).
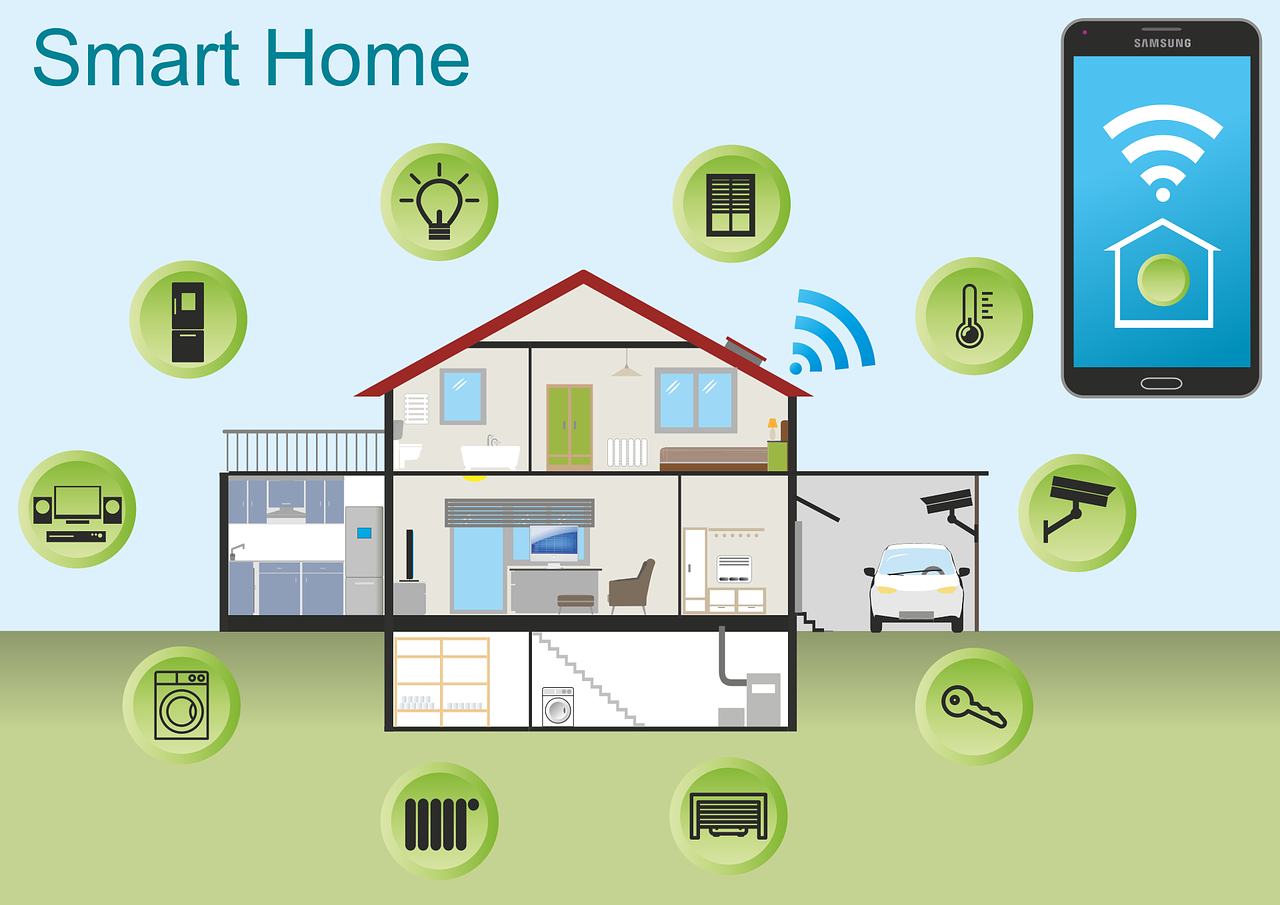
Implementing a NAC solution provides foundational security by granting visibility and control over every device connecting to the network. For SMBs, which often contend with a mix of company-owned devices, employee-owned devices (BYOD), and various Internet of Things (IoT) gadgets, managing network access is a critical challenge. This article will explore practical NAC deployment strategies for small and medium-sized businesses, clarifying the process and demonstrating how to secure the network without overwhelming limited IT resources. We will cover the initial steps, different implementation models, and best practices for a successful rollout.
Table of Contents
Why SMBs Cannot Afford to Ignore Network Security
The digital transformation has leveled the playing field for SMBs, but it has also expanded the attack surface. The rise of remote work, cloud services, and BYOD policies means the traditional network perimeter has dissolved. A 2023 report highlighted that compromised credentials remain a leading cause of data breaches, a risk that is amplified when personal devices access corporate resources. Without a mechanism to verify the identity and security posture of each device, SMBs leave their networks vulnerable to unauthorized access and malware propagation.
This is where the importance of NAC becomes evident. NAC acts as a digital gatekeeper, enforcing security policies at the point of entry. It ensures that only authorized users and compliant devices are granted access. For an SMB, this means preventing a compromised personal laptop or an insecure IoT device from connecting to the network and potentially serving as a launchpad for a ransomware attack.
By controlling access, NAC significantly reduces the risk of initial compromise and limits the potential for lateral movement within the network, containing threats before they can spread to critical systems.
Laying the Groundwork for NAC Implementation
Before deploying a NAC solution, SMBs must undertake some preparatory steps to ensure a smooth and effective rollout. A rushed implementation can lead to network disruptions and frustrated users. A thoughtful approach begins with a clear understanding of the existing network environment.
First, conduct a comprehensive inventory of all devices that connect or attempt to connect to the network. This includes corporate laptops, employee smartphones, printers, security cameras, and any other IoT devices. This discovery phase provides the necessary visibility to create effective access policies. You cannot protect what you cannot see, and a full inventory will likely reveal numerous “shadow IT” devices that were previously unknown to the IT team.
Second, define your access control policies. These rules will determine who gets access, what they can access, and under what conditions. Policies should be based on the principle of least privilege, meaning users and devices should only be given the minimum level of access required to perform their functions.
Consider creating different roles with varying access levels. For example, a guest should have internet-only access, while an employee in the finance department needs access to specific financial servers, and an executive might require broader access. These policies form the logical core of your NAC system.
Choosing the Right NAC Deployment Model
NAC solutions are not one-size-fits-all. SMBs can choose from several deployment models, each with its own advantages. The choice often depends on the company’s existing infrastructure, budget, and IT expertise.
On-Premises NAC
An on-premises solution involves deploying physical or virtual appliances within the company’s own data center. This model gives the IT team full control over the hardware and software. It can be a good fit for businesses with strict data residency requirements or those that prefer to keep all security infrastructure in-house. However, it requires a significant upfront investment in hardware and ongoing maintenance, which can be a strain on SMBs with limited capital and IT staff.
Cloud-Native NAC
Cloud-native NAC solutions have become increasingly popular, especially for SMBs. These services are delivered from the cloud, eliminating the need for on-site hardware. This model offers several benefits:
- Lower Upfront Costs: A subscription-based pricing model avoids large capital expenditures.
- Scalability: The solution can easily scale as the business grows, without the need to purchase new hardware.
- Reduced Management Overhead: The cloud provider handles maintenance, updates, and infrastructure management, freeing up the internal IT team.
- Simplified Remote Access: Cloud-native NAC is inherently well-suited for managing a distributed workforce, providing consistent policy enforcement for users regardless of their location.
Given these advantages, many SMBs find that a cloud-native NAC service provides the most efficient and cost-effective path to robust network security. It aligns with the modern trend of moving to cloud-based services and supports flexible work environments.
Phased Rollout Strategies for a Seamless Transition
Implementing NAC across an entire organization overnight is rarely advisable. A phased approach minimizes disruption and allows the IT team to fine-tune policies based on real-world feedback.
A common strategy is to start with a “monitor-only” or “audit” mode. In this phase, the NAC solution is configured to observe and log all connection attempts without actively blocking any devices. This allows the IT team to see how the defined policies would affect network access in practice. It helps identify legitimate devices that might be unintentionally blocked and provides an opportunity to adjust policies before enforcement begins. This phase is crucial for understanding the importance of NAC in providing visibility before control.
Once the policies are refined, you can begin enforcement in stages. Start with a low-impact segment of the network, such as the guest Wi-Fi. This allows you to test the enforcement capabilities in a controlled environment. From there, you can gradually roll out enforcement to other segments, such as the corporate Wi-Fi for employee devices, and finally to the wired network.
Communicating with employees throughout this process is key. Let them know about the upcoming changes, explain the security benefits, and provide clear instructions for ensuring their devices are compliant. This proactive communication can prevent help desk overload and foster user cooperation.
Integrating NAC with Your Existing Security Stack
NAC is most powerful when it works in concert with other security tools. Integration amplifies the capabilities of your entire security ecosystem. For example, integrating NAC with a Mobile Device Management (MDM) solution allows for more granular policy enforcement. The MDM can provide the NAC system with detailed posture information about a device, such as whether its operating system is up to date or if it has required security software installed. The NAC can then use this information to make more intelligent access decisions.
Another valuable integration is with a Security Information and Event Management (SIEM) system. The NAC solution generates a wealth of log data about access events. Forwarding these logs to a SIEM provides a centralized view of security events across the entire organization. This consolidated data can be used for threat hunting, incident response, and compliance reporting.
The detailed access logs from the NAC system provide critical context, helping security analysts quickly understand the scope of a potential incident. This highlights the importance of NAC not just as a preventative tool but also as a rich source of security intelligence.
For SMBs, the ability of a NAC solution to integrate easily with existing tools is a major consideration. Modern, API-driven NAC platforms are designed for this kind of interoperability, making it simpler to build a cohesive and automated security defense. The enhanced automation that comes from these integrations helps to reduce the manual workload on small IT teams, making advanced security more manageable.
Final Analysis
For small and medium-sized businesses, securing the network is no longer an option but a necessity. The financial and reputational damage from a single data breach can be devastating. Network Access Control provides a foundational layer of security that is perfectly suited to the challenges of the modern SMB environment, characterized by BYOD, remote work, and a growing number of IoT devices.
The importance of NAC lies in its ability to provide complete visibility and granular control over every device seeking network access, enforcing security policies before a connection is even established.
By starting with a thorough assessment of the network, choosing a deployment model that fits their resources—often a cloud-native solution—and executing a phased rollout, SMBs can implement NAC effectively without disrupting business operations. Integrating NAC with other security tools further strengthens defenses and automates responses, allowing small IT teams to manage security more efficiently.
Ultimately, deploying a NAC solution is a strategic investment in business resilience, protecting sensitive data, ensuring operational continuity, and building a secure foundation for future growth.
INTERESTING POSTS
- 3 Tech Tips For Small And Medium-Sized Businesses
- WELEAKINFO.COM has been Seized by the FBI: A Blow to Personal Data Marketplaces
- Exploring Model Monitoring Tools and Platforms for Effective Deployment
- AI in Breach Detection Threat or Safeguard (or Both)
- 6 Strategies To Make Your Model Serving API More Robust With Testing & Analysis
- Responsible Web Intelligence at Scale: An MCP-Driven Architecture
- Optimizing Your Event Log Management with a Maturity Model