In this Tor over VPN Guide, we will show you how to combine the Tor Browser with a VPN. Also, we will show you the best VPN for the Tor browser network.
Using the Tor Browser with an excellent VPN service is a complete privacy, security, and anonymity package. Using Tor ensures privacy; a VPN ensures anonymity, and a mix of the two should not be a bad idea.
When a connection is made over the internet, it is almost sure that there is a third-party spy. Hackers and even the government may get information about pages visited, location, and IP address.
To hide this information, the combination of the Tor browser and a VPN is the ultimate solution.
Table of Contents
Short On Time, Here Are The Best VPNs For Tor Browser
What Is Tor Browser?
Tor Browser is a free software project that enables users to anonymize their online experience. The Tor Browser is suitable for hiding the details of its users. This feature makes it a sturdy and well-downloaded app.
Tor is used daily by human rights activists, journalists, and government critics. Once a connection is made using the Tor Browser, the internet connection is encrypted and routed among multiple Tor servers around the world. Unless the entire Tor network is being monitored (including the servers), third-party websites can’t see the user’s IP addresses.
The Tor Browser can also connect to onion sites or the Deepweb. Onion sites are only available on the Tor network, as Tor itself is otherwise known as the Onion Browser.
READ ALSO: Best VPN For 2022
What Is A VPN?
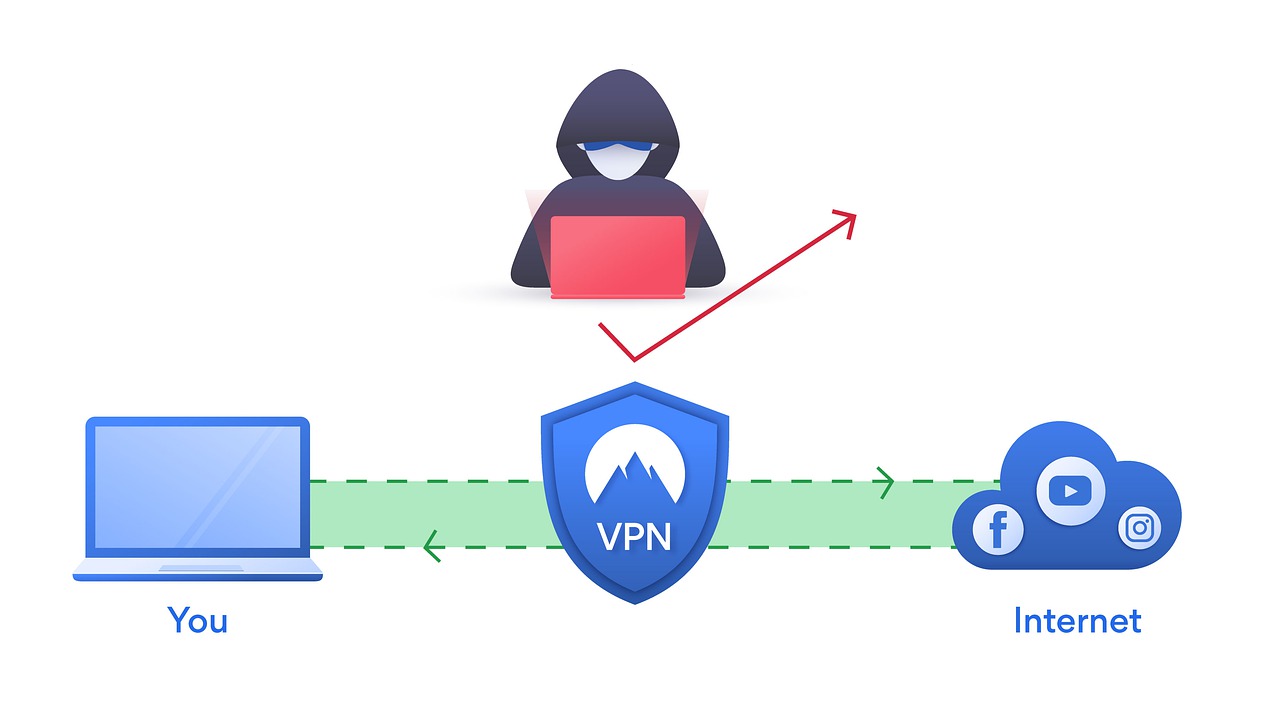
A VPN, also known as a virtual private network, is an encrypted route between the user’s device and the internet. When web traffic is routed through a VPN server, it encrypts virtually everything about the connection.
Firstly, the user’s IP address is masked, and then all sent and received data over the connection are also protected.
Before a VPN is used, it is essential to verify the authenticity of the VPN provider’s claims. While many VPN providers claim security, anonymity, etc., it is deplorable that they later go on to steal their user’s information, selling it away.
- READ ALSO: Best VPN For 2023
- READ ALSO: Best Antivirus For 2023
Why Use Tor And VPN?
Every time a connection request is made over the Tor network, the traffic is encrypted and routed through several nodes known as the Tor network, which makes it highly secure.
When a new connection request is made, the traffic is routed through completely different nodes, which makes it impossible to be traced. The process is purely random and not controlled by any authority, so trust is not needed.
Using the Tor network may offer some degree of anonymity. Still, users must note that the entry and exit nodes are documented, and anyone could have access to them with permission.
Some countries block access to Tor Browser nodes, while others are well-censored. In high crime rates countries, using Tor could mark you as a criminal.
Using a VPN blocks anyone from discovering how the information is being made, as a VPN encrypts the data before or after it gets to Tor nodes.
READ ALSO: Dos and Don’ts of Using a Public Wi-Fi: Your Ultimate Guide
Which VPN Service To Choose From?
The VPN market is flooded with several VPN providers, and it becomes confusing to choose a VPN service provider. The following questions and suggestions will help you make the right choice of VPN service.
- Ask yourself why you need a VPN. Do you need a VPN for privacy, security, speed, streaming, or torrenting? Will I be sharing my connection with my family?
- Does the VPN provider have the features you desire in a VPN?
- Are your devices compatible with the VPN?
- Does the VPN have a simple user interface?
- Does it have servers spread in locations you desire?
- Can it bypass geo-blocks?
- Does it have affordable plans?
- Does it have excellent customer service and a money-back policy?
How Do You Know Which VPN Is Best For Tor?
A VPN that is best for Tor must have servers optimized for Tor. In addition, it must use modern VPN protocols that balance speed with security, e.g., WireGuard VPN protocol, and must also support obfuscation technology. Other features you should watch out for include server coverage, kill switch, and split tunneling.
Above all else, it must have strict privacy policies that do not support retaining users’ data. Having zero-trust RAM-based servers is an added advantage.
5 Best VPNs for Tor Browser
Tor browsers give users a higher degree of anonymity, and it is the gateway to accessing the dark web. However, combining a VPN with a Tor browser lets you enjoy benefits not accessible to Tor-only users; you can enjoy services not available to Tor users and also enjoy protection from some of Tor’s compromised exit nodes known as spoilt onions.
In essence, the Tor Browser slows down internet connections because it routes it via multiple nodes. A VPN does a similar job. Combining a slow VPN with Tor results in an unbearable online experience
To avoid this, a fast VPN with high security and a good no-logs policy should be used to connect to the Tor network.
Not all VPNs are ideal for use with Tor’s browser; hence, I have carefully selected some VPNs optimized for use with Tor.
Below is a list of the best VPNs for Tor Browser.
1. Surfshark
Surfshark is a merged VPN service headquartered in the Netherlands. It is an affordable, high-speed VPN service optimized for torrenting, streaming, bypassing China’s Great Wall, and other use cases. Surfshark has more than 3200 VPN servers Spread in 60 countries worldwide.
Features that make it one of the best VPNs for the Tor browser include:
- GPS spoofing for Android (this feature masks physical locations for Android device users)
- Modern, fast, and secure VPN protocols (WireGuard, OpenVPN, and IKEv2)
- RAM-only servers
- Obfuscation technology (prevents ISPs, organizations, etc. from detecting VPN traffic)
- AES-256-bit encryption protocol
- 2FA
- Double VPN (MultiHop)
- Split tunneling
- Adware and malware blocker
- IP rotator (makes it harder for you to be tracked)
- Unlimited device connectivity
- Strict Privacy protocols and a no-logs policy
- Multi-platformMulti-platform support
- Very affordable (price starting from $2.49 per month)
===> Get Surfshark VPN
2. CyberGhost VPN
CyberGhost VPN is one of the best VPN service providers. It was established in 2011 by Robert Knapp, a German tech expert, but was sold to an Israeli technology company, Kape Technologies, formerly Crossrider.
CyberGhost has the highest number of servers and subscribers, with over 14 million subscribers.
Some of its key features include:
- More than 7,800 servers in 94 countries worldwide
- Over 3,500 servers spread in 94 countries worldwide
- Supports routers
- Encryption protocols: 4096-bit CA, and AES-256- CBC, and TLSv1.2 encryption protocols
- VPN protocols: WireGuard, OpenVPN (TCP/UDP), IKEv2
- Supports Tor, streaming, and torrenting
- Private DNS (prevents leaks)
- Adware and Malware blocker
- Seven simultaneous device connection
- Supports browser extensions
- Multi-platform support
- Kill switch and split tunnelling
- Strict privacy policies, including no-logging
- The price starts from $2.29 per month
===> Get CyberGhost VPN
3. NordVPN
NordVPN is a premium VPN service provider established in 2012 by Nord Security, a cybersecurity company owned by a group of childhood friends.
Notably, NordVPN has a specialized Onion over VPN feature that gives users access to the Tor network without using the Tor browser.
Other features that make NordVPN an optimized VPN for the Tor browser include:
- More than 5600 servers spread in 60 countries
- Optimized for P2P and streaming
- Onion over VPN (for accessing Tor sites)
- VPN protocols: Proprietary NordLynx (Based on WireGuard), OpenVPN, and IKEv2
- Encryption technology: Military-grade AES-256-bit encryption protocols
- Obfuscation servers (makes it possible to work in China)
- Adware and Malware blocker
- Split tunneling
- Kill switch
- Dedicated IP
- Double VPN and double encryption
- Six simultaneous device connectivity
- Multi-factor authenticator
- Supports browser extension
- Verified No-logs policy
- The price starts from $3.29 per month
===> Get NordVPN
4. ExpressVPN
ExpressVPN is a top VPN service founded in 2009 and acquired by Kape Technologies in 2021. the VPN has more than 3 million subscribers.
ExpressVPN has advanced and proprietary features that make it stand out as a VPN of choice for Tor and other purposes. It is one of the VPNs with the widest location coverage worldwide.
Other features that make ExpressVPN stands out include:
- Over 3,500 servers spread in 94 countries worldwide
- Supports routers
- Encryption protocols: 4096-bit CA, and AES-256- CBC, and TLSv1.2 encryption protocols
- VPN protocols: Lightway (based on WireGuard), OpenVPN (TCP/UDP), SSTP, L2TP/IPSec, and PPTP
- RAM-only server
- Private DNS (prevents leaks)
- Adware and Malware blocker
- Five simultaneous device connectivity
- Supports browser extensions
- Multi-platform support
- Built-in ping tester (connects to the fastest network)
- Kill switch and split tunneling
- Strict privacy policies, including no-logging
- Password manager/generator
- Accepts cryptocurrencies for payment
- The price starts from $8.32 per month
===> Get ExpressVPN
5. ProtonVPN
ProtonVPN was established by Proton Technologies AG, owners of ProtonMail. It is one of the most secure VPN services with robust privacy and security features. It is headquartered in Switzerland, a country with people-friendly data policies.
In addition, ProtonVPN is an open-source community project built with users in mind, making it one of the most user-friendly VPNs optimized for privacy, torrenting, streaming, Tor, etc.
Its Tor-optimized features include:
- 1,761 servers spread in 63 countries
- Servers optimized for speed, Tor, torrenting, and streaming
- Built-in Tor support
- Encryption: AES-256-bit military-grade encryption with 4096-bit RSA, HMAC with SHA384 (message authenticator)
- VPN protocols: WireGuard, OpenVPN, and IKEv2
- Sever disk encryption to protect servers from DDoS attacks
- Perfect Forward Secrecy (protects against compromised keys)
- Kill switch and Always-on VPN (protects your data traffic round the clock)
- VPN Accelerator (boosts your speed)
- Netshield (ProtonVPN adware and malware blocker)
- Anonymous subscription
- Supports ten devices simultaneously
- Multi-platformMulti-platform support
- Price starts from E8 per month
- It has a free version
===>> Get ProtonVPN
How To Use Tor Over VPN
This is the most common way to use the Tor Browser with a Virtual Private Network. It involves connecting to a VPN client and encrypting the connection data before the data packets are connected to the Tor network.
This system is advantageous in many ways, as it hides the fact that the connection was made over Tor, and it prevents Tor from accessing the user’s IP address. It also unblocks Tor, even where it is blocked. If the Tor Browser were to encounter a security flaw, a user accessing Tor over a VPN would be protected.
READ ALSO: Browser Compartmentalization: How to Compartmentalize Your Web Browsers
Another Tor advantage over VPN is its ease. To set it up, the users connect to their favorite VPN and launch the Tor Browser.
Can I Route the VPN Over Tor?
It is also possible to route the connection through Tor at first and subsequently connect it to a VPN. This is, however, more difficult and not worth doing.
READ ALSO: VPN Chaining: Can You Use Multiple VPNs at Once?
While the exit node does not have access to your connection data, the VPN service becomes empowered to view your connection details, which is riskier if the VPN provider is untrustworthy.
A trusted VPN can be trusted with this setup, but virtually all trusted VPNs, including the above-listed ones, can support VPN over Tor.
What Is The Difference Between Tor And A VPN?
Tor is a free, open-source browser that routes data traffic from your device through multiple layers of nodes (servers); hence, the name The Onion Router. A VPN, on the other hand, is a Virtual Private Network of servers spread worldwide.
Both Tor and VPN conceal users’ privacy and identity while online; however, Tor users do not get to choose what node or server to channel their data traffic to, unlike VPN, where the users choose the server to connect to, along with a range of customizable privacy features.
Data traffic entering the Tor network is channelled through multiple server layers, which are run voluntarily by Tor users, while data traffic entering the VPN goes through a centralized server in the users’ location.
Lastly, a Tor browser can access the dark web, i.e., all websites ending with .onion, whereas you cannot access .onion websites on the dark web using a VPN.
What Is The Difference Between Tor Over VPN And VPN Over Tor?
Tor Over VPN means you’re connecting to a VPN server first before entering a Tor network. This prevents your ISP from knowing that you’re connecting to a Tor network and protects you from compromised Tor servers.
Using a virtual private network over Tor means you’re first connecting to the Tor network before connecting to a VPN service.
In essence, VPN over Tor lets you access websites that block data traffic from the Tor browser. It also prevents Tor’s exit node from decrypting and knowing the destination of your data traffic.
However, using a virtual private network over Tor does not hide the fact that you’re using a Tor browser from your ISP, and it also exposes your data to Tor’s entry server.
What Is Onion Over VPN, And How Does It Work?
Onion over VPN is a VPN feature that lets you connect to the Tor network without using the Tor browser. Onion Over VPN works by channelling your data traffic through several server layers (or nodes) (Onion), similar to the Tor network, adding extra security and encryption layers to your data traffic.
The only way to use this feature is by subscribing to a service with Onion over VPN features. Examples of such VPNs include NordVPN, ProtonVPN, etc.
Should I Use A VPN With The Tor Browser?
Depending on your privacy needs, you should use a VPN with the Tor browser to add an extra security layer to your data traffic before entering the Tor network.
This gives you the advantage of using Tor in countries where the use of Tor is restricted, and it also protects your data traffic should the Tor network be compromised.
To use a VPN with Tor, you should first connect to a VPN server before launching the Tor browser.
What Is Tor, And How Does It Work?
The Onion Network (Tor) is an open-source browser project that makes you an anonymous internet user by encrypting and channelling your data traffic through several nodes (server) layers (hence the name onion) operated by voluntary contributors.
Tor works by encrypting your data traffic and bouncing it through a circuit of nodes (also known as relays), encrypting your data traffic at each node.
However, your data traffic gets decrypted at the exit node before reaching its destination server. Hence, there is a need for an additional security layer at Tor’s exit node (Tor over VPN).
What About A VPN Over Tor?
VPN over Tor means that you’re first connecting to a Tor network before connecting to a VPN server. This is ideal in Tor-friendly locations for accessing websites and services restricted to Tor users.
A VPN over Tor encrypts your data traffic as it leaves Tor’s exit node into the VPN hop, channelling it through a military-grade encryption tunnel to its destination server.
How Does Tor Work Without A VPN?
Tor works without a VPN by encrypting and channelling your data traffic through several node layers. This masks your IP address and location in a similar way that a VPN does.
Unlike a VPN, Tor routes your data traffic through several server layers (at least three nodes) but leaves your data traffic exposed at Tor’s exit node.
However, using Tor is much slower since your data traffic has to be bounced through several nodes before getting to the destination server, hence making it less suitable for everyday use.
Tor Over VPN: Frequently Asked Questions
Can You Be Tracked When Using Tor With VPN?
No, you cannot be tracked on Tor with a virtual private network. Using Tor with VPN adds an extra security layer over your activities by protecting you if the Tor network is compromised.
Connecting with Tor over VPN means that the server will shield your data traffic from your ISP and also prevent the Tor entry node from knowing the origin of your data. Hence, there’s no way your data traffic can be traced back to you when using Tor over VPN.
Can You Be Tracked When Using A VPN Over Tor?
Yes, you can be tracked when you use a VPN over Tor. This means that your ISP knows that you’re connected to a Tor network, and Tor’s entry node knows the origin of your data traffic; hence, a tracker can track your data traffic if the tracker can find your Tor’s entry node.
On the other hand, your data traffic destination cannot be tracked because your data traffic at the exit node is channelled to your chosen VPN server before connecting to your destination web server.
Does The Tor Network Function The Same As A VPN?
No, the Tor network does not function the same as a VPN. Although both Tor and VPN encrypt your data traffic and channel it through a server, Tor offers you more anonymity by channelling your data traffic through several server layers (remember, it’s the onion router!).
Also, Tor slows down your speed considerably, making it unsuitable for everyday use cases, while VPN balances between speed and security.
In addition, VPNs have extra privacy features, including a Kill switch, several servers to choose from, tunnelling, etc., while Tor does not let you choose your server; rather, it sends your data traffic through a circuit of nodes not known to you.
Each node in the circuit operates a zero-trust by preventing each node from seeing the whole circuit of nodes.
Should I Use A VPN On Tor With Tails?
Yes, you should use a virtual private network on Tor with Tails to get the best of both worlds. Using a VPN on Tor with Tails, add a VPN connection at Tor’s exit node, preventing accidental data exposure.
It also enables you to access websites, services, and features that are not available when you use Tor with tails only. However, your identity can be compromised should the Tor network be compromised.
Should I Use A VPN To Connect To Tor Or Use Tor To Connect To A VPN?
Depending on your needs, you should use a VPN to connect to Tor. Using a virtual private network to connect to Tor means connecting to a VPN first before connecting to a Tor network.
Connecting to a virtual private network first masks your internet traffic, preventing your ISP from detecting that you’re using the Tor network, and also adds an extra encryption layer to your data traffic.
Using the onion router to connect to a virtual private network gives you access to services not accessible to the Tor network and also encrypts your data traffic at Tor’s exit node, preventing accidental data exposure.
Should I Use Tor Bridges Instead Of A VPN?
No! Rather, you should use a VPN instead of Tor Bridges. Tor bridges are also Tor nodes but are not made public because they are not included in Tor’s directory of nodes.
Setting up a tor bridge is far more complex than setting up a virtual private network, and not all bridges can work for your situation.
If, after setting up a Tor bridge, it does not work, you will have to go through the pains of searching and setting up a new Tor bridge. Hence, it is advisable to use a Virtual Private Network instead of a Tor bridge.
How To Connect To Onion Over VPN?
To connect to Onion over a VPN server, you should change your VPN protocol to OpenVPN (TCP) and select an Onion over a VPN server listed under the speciality server for NordVPN users. The process is relatively more straightforward for Proton VPN: search for ‘Tor’ using Proton VPN’s search bar and select a Tor-optimized server to connect to.
Does using Tor over a VPN make me completely anonymous?
No, it doesn’t guarantee complete anonymity. Here’s why:
- Increased Complexity: The setup can be complex, and misconfiguration might expose your identity.
- Potential Performance Impact: Running Tor over a VPN can significantly slow down your internet connection due to double encryption and routing.
- VPN Exit Node Visibility: While the VPN encrypts traffic entering the network, your activity at the VPN’s exit node might still be visible.
Why would I use Tor over a VPN?
There are a few scenarios where this setup might be beneficial:
- Highly Censored Networks: If you’re on a network that heavily restricts access to certain websites, Tor can help bypass those restrictions, and the VPN adds an extra layer of obfuscation.
- Increased Anonymity: For some users with a high threat profile, the combination might offer a theoretical advantage. However, it’s important to weigh the complexity and performance impact.
Are there any risks involved?
Yes, there are a few potential risks:
- Misconfiguration Issues: If not set up correctly, you might expose your identity or even compromise your security.
- Legal Concerns: In some regions, using Tor itself might raise suspicion. Make sure you understand the local laws regarding Tor usage.
- Slower Speeds: As mentioned earlier, expect a significant slowdown in your internet connection.
What are some alternatives to consider?
- Just Tor: If your primary goal is anonymity and you’re comfortable with the technical aspects, using Tor alone might be sufficient.
- Just a VPN: For basic privacy and location masking, a reputable VPN can be a good option.
Conclusion
Tor is an invaluable tool for online privacy. If anonymity is desired, the importance of the Tor Browser cannot be overemphasized. Using the Tor Browser with a credible VPN service makes an unbreakable security firewall.
To recap, here are the best VPN for Tor Browser:
What’s more, it is as easy as getting a VPN subscription from above, connecting it to the device, and accessing the Tor browser right away.
RELATED ARTICLES
- Best Antivirus For 2022
- 5 Concealed Best Tor Browser Alternatives You Didn’t Know
- 5 of the Best Secure Web Browsers
- How to Configure Popular Web Browsers with Proxy Information
- What are Cyber Threats? How to Secure your Computer against Cyber Threats?
- 15 Best VPN For Coronavirus Quarantine Holiday
- Surefire Tips – How To Protect Your Data From Cyber Attacks
About the Author:
Daniel Segun is the Founder and CEO of SecureBlitz Cybersecurity Media, with a background in Computer Science and Digital Marketing. When not writing, he's probably busy designing graphics or developing websites.