This post will show you the best VPN for a coronavirus quarantine holiday to access geo-restricted content from Netflix, Hulu, Spotify, etc., for a pleasurable stay-at-home period.
Additionally, you will learn a few tricks to use a VPN to keep you safe from cyber attacks during this COVID-19 lockdown period.
Table of Contents
Coronavirus Pandemic And Cybersecurity
The Coronavirus pandemic ravaging the world is highly contagious and has no cure; however, the spread of the virus is curtailed through social distancing and other sanitary measures.
To combat the coronavirus outbreak effectively, industries, institutions, and organizations worldwide (excluding health organizations and other essential services) have suspended all activities. They have also instituted a work-from-home policy to protect their members and staff from COVID-19 infection.
This has led to a rising rate of cyberattacks, ultimately resulting in online fraud, scams, and data theft. Therefore, whether you’re working from home or not, it is essential to use A VPN service to keep you safe from cyberattacks.
READ ALSO: 450+ Best Torrent Websites That Are Active & Working
What Is A VPN?
VPN – A Virtual Private Network is an intermediate network of computer servers between your PC/device and online resources or websites.
When you connect to a VPN server, your data traffic is channeled through their secure virtual tunnel to the website server. That way, your IP address is obfuscated.
Why Do You Need A VPN During the Lockdown Period?

A VPN is a must for you if you’re working from home or intend to enjoy the best online content (movies, TV shows, music, etc.) while obeying the stay-at-home order.
You need a VPN to protect the sensitive nature of data exchange taking place remotely between your computer and other client computers or workplace servers to prevent such data from falling into the wrong hands.
A VPN lets you stream content from torrenting sites without compromising your IP address and location.
Also, outside the US, you can access geo-restricted websites like Netflix US for their fantastic entertainment content.
READ ALSO: What is VPN? What are its Features and Benefits?
How Does A VPN Work?
Tapping the ‘Connect’ button creates a secure data transmission tunnel between your device and your chosen VPN server. The encryption tunnel encrypts your data to protect it from spies and attackers.
The VPN acts as an intermediary by channeling your data securely to the website server you’re connecting to. Therefore, data exchange takes place via the VPN server.
Since you’re connecting to the internet via a VPN, only the IP address and the location of the VPN server you’re currently connected to will be revealed to the website server.
Hence, the VPN server effectively masks your device’s IP address and location from websites, spies, and attackers, making you appear anonymous online.
READ ALSO: Best VPN For 2023: Top Picks Reviewed by Our VPN Experts
Criteria for Selecting the Best VPN for Coronavirus Quarantine

Since you will be spending much of your time either working from home, gaming, or watching movies and TV shows on Netflix, Hulu, or streaming sites, you must choose a VPN that can meet your stay-at-home needs.
Although you might want to stick with premium VPN services, you should consider the following factors before jumping at the first VPN that pops up in your search engine.
OpenVPN protocol
There are six types of VPN protocols, including OpenVPN, L2TP, PPTP, and TSL. However, the right VPN provider will provide you with several options. Hence, you’re left to make a choice based on your needs.
Number of VPN servers available
Ideally, a VPN provider should have hundreds, if not thousands, of servers widely distributed worldwide.
Also, if you intend to access Netflix US or other streaming services based in the US, it will be wise to choose a VPN provider with several servers in multiple locations within the US.
The location of your VPN servers plays an essential role if you intend to hide your activities from the Government’s prying eyes. For this purpose, you should choose a VPN provider with a base in a country that offers its citizens high internet freedom or a country that is not your close ally.
Unlimited bandwidth
No doubt, you will use up a large bandwidth to kill boredom while obeying the stay-at-home order. Therefore, the best VPN for coronavirus quarantine should offer unlimited bandwidth to enjoy unrestricted data exchange while working from home stream movies, music, TV shows, etc., from popular streaming sites.
A VPN provider should not keep a log of users’ activities
The best VPN for Coronavirus season should not keep a log of its users’ activities, so even if law enforcement comes knocking, there will be no logs to hand over.
Observing a strictly ‘no log’ policy benefits the users and the VPN providers because keeping a log entails having ample storage space and even paying much for its maintenance. Therefore, when choosing a VPN, be sure their policy reads, ‘no logging.’
Kill switch technology
A VPN kill switch automatically disconnects your device from the internet if there is a sudden disconnection in VPN services. Before paying for a VPN subscription, ensure the VPN provider has a kill switch technology to protect your data traffic from accidental exposure.
Number of connected devices to a single subscription
Most people have more than one internet-enabled device, such as a computer, mobile device, smart TV, WiFi router, or other devices belonging to family members.
Therefore, the best VPN for coronavirus should allow for multiple simultaneous connections to a single VPN subscription. Ideally, most VPN providers allow up to five connected devices to an individual VPN subscription.
Pricing
Pricing and plans vary from one VPN provider to another. Hence, you might want to compare pricing alongside other VPN features to get the best offer. Most VPN providers offer several plans ranging from a month to 2 years.
However, long-term plans are more financially beneficial than monthly plans because you get to enjoy more than 50% discounts on such long-term plans.
READ ALSO: Free VPN Vs. Premium VPN
Best VPN For Coronavirus Quarantine Holiday
CyberGhost VPN
CyberGhost VPN is a Romanian-based VPN provider with over 15 years of operation and over 6000 servers in more than 90 locations worldwide. This makes CyberGhost one of the best VPN providers you can subscribe to and enjoy the best of VPN features.
In addition, CyberGhost VPN is adapted to meet all types of needs with its wide range of features and simple user interface.
Hence, whether you need a VPN for security purposes or streaming, you’re sure to enjoy CyberGhost’s robust security features and optimized servers, the most extensive collection of servers in the VPN industry.
Critical features of CyberGhost VPN
- Military-grade AES 256-bit encryption protocol, which makes it one of the most secure VPNs to use for online data protection
- Supports OpenVPN, L2TP, IPSec, and PPTP on significant OS platforms like Windows, Mac, iOS, Android, and Linux for high-speed connectivity
- It has an effective kill switch technology for data safety
- DNS and IPV 6 are leakproof for protecting your IP and location
- Unlimited bandwidth
- Supports seven devices in a single account
- 45-day money-back guarantee
Get CyberGhost VPN
READ ALSO: Full Review of CyberGhost VPN
Ivacy VPN

Ivacy VPN is owned and managed by PMG Private Limited. Established in 2007, Ivacy VPN won the Fastest VPN award in 2019.
Critical features of Ivacy VPN
- It has more than a thousand servers spread in over 100 locations around the world
- It uses Split tunneling technology, which allows you to determine what apps connect to the VPN selectively
- Ultra-fast connectivity speed
- Internet Kill-switch technology
- Supports ten devices simultaneously with a single account
- Uses Military-grade AES 256-bit encryption protocol
- Supports Advanced IPsec and IKEV Protocols compatible with significant OS, including Android, iOS, Mac OS, and Windows
- Supports a ‘no log’ policy
- 30-day money-back guarantee
Get Ivacy VPN
READ ALSO: Full Review of Ivacy VPN
PureVPN

PureVPN was established in Hong Kong in 2006 by GZ Systems, makers of Android sports apps. This makes it one of the oldest VPN service providers in the industry you can rely on. Its changing IP address ensures that you remain anonymous online.
Key features of PureVPN
- Supports ten devices on a single account
- Split tunneling, which lets you selectively use apps with a VPN
- More than 2000 servers in 180 countries, including servers optimized for Netflix
- Military-grade AES-256 bit encryption protocol to ensure data safety and security
- Ultra-fast connectivity speed
- Unlimited bandwidth
- No logging policy
- Compatible with Major Operating Systems and over 50 devices
- Supports Port Forwarding
- More than 300,000 IP addresses
- 31-day Money-back guarantee
Get PureVPN
READ ALSO: Full PureVPN Review
Surfshark VPN
Although the two-year-old British Virgin Island-based SurfShark VPN is a relatively new player in the VPN industry, it is one of the best VPNs for this coronavirus holiday and the fastest-growing VPN provider. It has a thousand and forty optimized VPN servers in 61 countries.
Aside from significant price slashes that put it ahead of other notable VPN providers, subscribers also enjoy numerous innovative features from SurfShark VPN.
Critical features of SurfShark VPN
- OpenVPN, UDP, TCP, and IKEv2 protocols
- AES-256-bit GCM encryption protocol, RSA-2048, and Perfect Forward Secrecy to ensure data safety and security
- Intelligent kill switch technology
- Unlimited devices connected to a single subscription
- Compatible with major OS platforms and devices
- Malware and phishing protection feature which ensures you enjoy a secure browsing experience
- No-log policy
- WebRTC leak-proofed web browser plugins and add-ons compatible with Chrome and Firefox browsers
- Multihop VPN services which allow users to connect to two servers simultaneously
Get SurfShark VPN
READ ALSO: Full Surfshark VPN Review
BullGuard VPN
Although BullGuard VPN boasts relatively fewer servers spread in less than 20 countries, majorly in Europe, subscribers enjoy premium VPN services with maximum online safety and data protection.
Critical features of BullGuard VPN
- No log policy
- Optimized servers for streaming geo-restricted content
- High-speed internet connectivity with unlimited bandwidth
- Compatible with iOS, Android, Mac, and Windows devices
- Supports six connected devices simultaneously
- Kill switch technology
- 24/7 live support and a 30-day money-back guarantee
Get BullGuard VPN
READ ALSO: 8 Best Antivirus with VPN
ZenMate VPN is a German-based VPN with a relatively simple user interface for non-tech users.
An exciting perk about ZenMate VPN is its free plan, which offers users unlimited bandwidth connection but with limited features. This gives you ample opportunity to try out Zenmate VPN before committing your cash to it.
Although it is located in Germany, part of the ‘5 Eye country’, it operates a ‘no log’ policy, ensuring that your online activity is anonymized and out of reach.
Critical features of ZenMate VPN
- It has more than 3,600 servers located in 74 countries
- Unlimited devices connected to a single subscription
- Ideal for streaming content from Netflix US and other geo-restricted streaming platforms
- Ultra-fast internet connection speed with unlimited bandwidth
- Chrome, Firefox, and Opera browser extensions
- Uses either AES-126 or 256-bit encryption protocols to protect users’ data
- It works based on IPSec, L2TP, and OpenVPN protocols
- Kill switch technology
Get Zenmate VPN
Private Internet Access
Private Internet Access was established in 2010 by London Trust Media INC. It has become one of the cheapest and the best VPNs for the Coronavirus quarantine season, with more than 3 381 servers spread in 41 countries.
In 2017, Private Internet Access won the Most Stable VPN award, making it a VPN to be reckoned with amongst top VPN providers.
Although PIA VPN is based in the US, it operates a ‘no log’ policy, which prevents it from keeping a log of its clients’ activities.
Key features of Private Internet Access VPN
- Supports OpenVPN, PPTP, L2TP VPN protocols, and SOCKS5 proxy
- It does not keep a log of users’ activities
- Offers up to ten simultaneous connections from a single account
- Users enjoy unlimited bandwidth connectivity with multiple VPN Gateways
- Supports anonymous payment methods via gift cards and bitcoin
- DNS leakproof to prevent location and IP compromise
- It has 3,381 servers optimized for unblocking censorship filters and streaming geo-restricted content across the globe
- Very low pricing
READ ALSO: Full Private Internet Access VPN Review
TunnelBear VPN
TunnelBear was established in 2011 but was acquired by McAfee in March 2018. Although TunnelBear has far fewer servers than other top VPNs, it guarantees its users security and online anonymity.
A unique distinguishing feature you’re sure to enjoy is the notification you get when connecting to an unprotected wireless connection.
Key features of TunnelBear VPN
- A kill switch technology that protects your data traffic when the VPN disconnects accidentally
- Optimized servers located in 23 countries for accessing censored sites and contents
- It uses the military-grade AES 256-bit encryption protocol to keep your data safe and encrypted.
- Compatible with Windows, Mac, and iOS platforms
- It has Chrome and Opera browser extensions
- Impressive connectivity speed with unlimited bandwidth
- Allows a maximum of 5 connected devices to a single account subscription
- It logs your OS type and version and the TunnelBear app. It, however, does not keep a record of your IP address or your activities online.
Get TunnelBear VPN
READ ALSO: Full Review of TunnelBear VPN
Avira Phantom VPN
Avira Phantom VPN is a VPN service offered by Avira, an anti-malware firm, as part of the Avira Security suite.
One unique feature that guarantees security is its automatic connection each time you go online.
Key features of Avira Phantom VPN
- A strict ‘no log’ policy
- Mechanical connection: whenever you go online
- It has optimized servers in 38 countries
- Automatic kill switch
- It is DNS leakproof, your IP and location protected
- It uses military-grade AES-256-bit encryption technology to protect your data
- 30-day money-back guarantee
READ ALSO: 6 Best VPNs for Gaming You Should Consider in 2020
Panda VPN
Panda VPN is part of the Panda security suite, which means that Panda Antivirus subscribers get an additional VPN feature for free.
Although the VPN has a simple user interface, it lacks customizable features such as the choice of VPN protocol and does not have a kill switch technology in place.
A great advantage you will enjoy over other VPN services is its high-speed connectivity, which puts it in the league of the fastest VPN services.
Key features of Panda VPN
- Panda VPN uses the Catapult Hydra VPN protocol, which is one of the fastest VPN protocols.
- It keeps zero logs of users’ activities
- It has optimized servers in 23 countries
- WebRTC is leakproof to keep you anonymous online
- It uses the AES-256-bit encryption protocol to secure your data
Get Panda VPN
Express VPN is one of the best VPNs for the coronavirus quarantine season because of its widespread distribution of servers in 94 countries and over 160 locations.
Also, it is a VPN service with rich features, robust encryptions, a kill switch, and other customizable features.
Hence, if you desire a perfect VPN for a secure work-at-home experience or to stream content from popular streaming service providers, ExpressVPN is the ideal choice.
Key features of ExpressVPN
- DNS leakproof to ensure you remain anonymous online
- Combines AES-256 bit encryption with 4096-bit RSA key and SHA-512 HMAC encryption protocols to provide its users with powerful data security feature
- It uses OpenVPN, L2TP, and PPTP VPN protocols to guarantee high-speed connectivity
- Kill switch technology
- Compatible with major OS and browsers, including Tor
- No logging policy
READ ALSO: 4 of the Best VPNs for Upwork (with a dedicated IP address)
VyprVPN is a Swiss-based VPN service provider with a presence in 70 countries and wide-range compatibility with Operating systems, browsers, and devices.
It is one of the few VPN services that work in China, thanks to its Chameleon mode, which camouflages your use of VPN.
Key features of VyprVPN
- Over 700 servers optimized for torrenting and streaming from Netflix, US, Hulu, etc.
- Its Chameleon feature enables it to bypass the Government’s censor on VPNs without detection
- Allows a maximum of five simultaneous connections to a single account
- No logging policy
- DNS leakproof to protect your IP and location
- 30-day money-back guarantee
READ ALSO: Full Review of VyprVPN VPN Service Provider
NordVPN is one of the top VPN providers, with more than 5000 servers spread in 59 countries.
Although NordVPN suffered a data breach in the past, it is repositioned for providing its clients with the best privacy features to guarantee 100% data security.
Key features of NordVPN
- Automatic server selection
- Supports OpenVPN, IKEv2 VPN protocols
- Double VPN (multihop) connection
- CyberSec tool, which offers subscribers protection from malware-infested sites, along with other features such as NordLocker (and encrypted file vault) and NordPass (a password manager)
- Uses the AES-256 bit GCM encryption technology
- Keeps zero logs
- Based in Panama outside of the 5/9/14 eyes
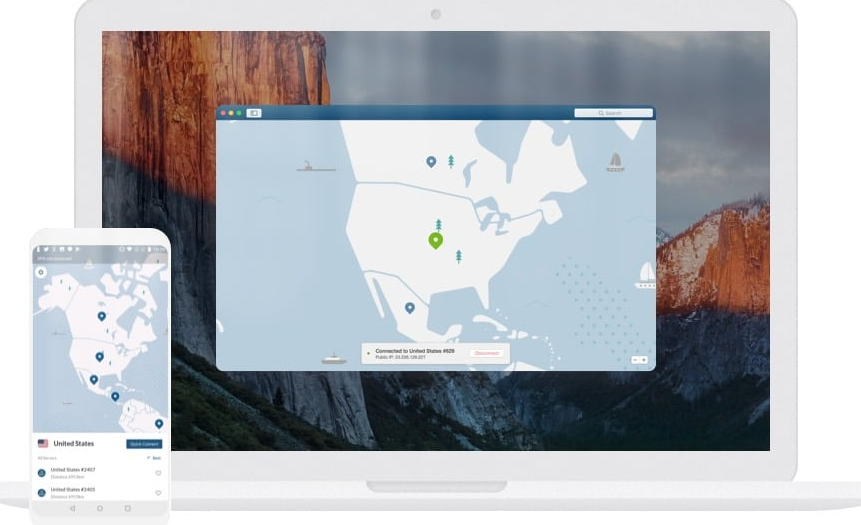
IP Vanish is a US-based VPN service. That means users outside of the US can enjoy high-speed content streaming from Netflix US and other geo-restricted streaming service providers.
If you spend much of your stay-at-home time watching movies and TV shows or streaming other content from US-based providers, then IP Vanish will be your best choice.
Key Features of IP Vanish
- More than 1400 optimized servers
- Uses OpenVPN protocol for faster internet connectivity
- Supports major Operating systems
- Supports ten connected devices for a single account
- No logging policy
- Uses 256-bit encryption protocol to ensure maximum data security
- 7-day money-back guarantee
Hotspot Shield combines speed and security, making it a formidable VPN service for this coronavirus quarantine season.
If you’re working from home, you will find HotSpot Shield’s robust encryption feature capable of providing maximum data security and online anonymity.
If you’re a torrenting fan, you will surely enjoy high-speed torrenting from any of its optimized servers worldwide.
Key Features of Hotspot Shield
- Supports five simultaneous VPN connections from a Single account
- Unlimited bandwidth connection
- Uses the Catapult Hydra VPN protocol for high-speed connectivity
- DNS leak protection to protect your real IP and location from exposure
- Support a ‘no logging’ policy
- Compatible with primary OS like Windows, Android, iOS, and Mac OS
READ ALSO: VPN Chaining: Can You Use Multiple VPNs at Once?
Why Should You Use A VPN Service During the Coronavirus Quarantine Period?
By using a VPN service during the coronavirus quarantine period, you can gain the following benefits:
- A VPN masks your IP address and location, making you appear anonymous online. It also prevents online trackers from tracking your activities and serving you with tailor-made adverts.
- You enjoy data protection when you connect to unprotected public networks, e.g., WiFi networks in coffee shops, parks, and other public places.
- With a VPN service, you can bypass internet censorship imposed in some countries by connecting to a VPN server outside of such a country.
- Using a VPN service during this Coronavirus quarantine season gives you unlimited streaming access to stream geo-restricted content from Netflix US, BBC iPlayer, Hulu, and other streaming service providers.
- Although torrenting is not illegal, torrenting copyright content is considered illegal. But with a VPN, you can torrent any content anonymously.
- Also, when you use a VPN service, you bypass your ISP speed throttling. Hence, you can download or stream videos at a much faster speed.
RELATED: 8 Best VPNs For China And Hong Kong (+5 Reliable Ones)
Can I Use A Free VPN During This Coronavirus Quarantine Period?
For the following reasons, a free VPN is not ideal for use during the coronavirus quarantine period.
- Several free VPNs offer a limited bandwidth of less than 500MB daily.
- Some free VPNs log your details, which they sell to the highest bidders or ad providers.
- Some free VPN software is adware-infested. Hence, they serve you consistently with annoying ads.
Final Thoughts
There you go! Our top picks of the best VPN for coronavirus quarantine holiday.
While the lockdown persists, using a VPN becomes imperative due to the rising level of cybersecurity threats to ensure data safety and security while working from home.
Another major issue experienced during the lockdown period is boredom due to limited content from local TV and radio stations.
However, subscribing to any of the best VPNs for coronavirus quarantine gives you access to highly entertaining movies, TV shows, music, books, etc., either from torrenting sites or from geo-restricted streaming sites such as NBC, Hulu, Netflix US, Spotify, BBC iPlayer, etc.
Editor’s Note: This post was initially published in April 2020 but has been updated for accuracy and freshness.
RELATED POSTS
- Coronavirus: Online Security Tips for Remote Workers
- 10 Tips to Secure Your Smartphones (iOS and Android)
- Is VPN4Test VPN Service safe to use?
- Online Security Tips for Kids
- Tor+VPN Guide: How to Combine Tor Browser With VPN
- Beat Quarantine Boredom With Free Online Games [MUST READ]
- Android SLocker Coronavirus Malware: Scammers Exploit Pandemic Fears
About the Author:
Daniel Segun is the Founder and CEO of SecureBlitz Cybersecurity Media, with a background in Computer Science and Digital Marketing. When not writing, he's probably busy designing graphics or developing websites.








![When Is Hacking Illegal And Legal? [Honest Answer] when is hacking illegal and legal](https://secureblitz.com/wp-content/uploads/2020/07/when-is-hacking-illegal-and-legal.jpg)


![Cybersecurity Tips From Squid Game TV Series [MUST READ] Cybersecurity Tips From Squid Game TV Series](https://secureblitz.com/wp-content/uploads/2021/10/Cybersecurity-Tips-From-Squid-Game-TV-Series.png)
hi, all of information is great and nice information
Thank you for your comment.
You can subscribe to our newsletter for the latest blog posts, and free eBooks from us.