This post will show you essential Squid Game cybersecurity tips to learn.
Netflix’s Squid Game took the world by storm, captivating audiences with its brutal depiction of 456 debt-ridden individuals competing in deadly children’s games for a massive cash prize.
Beyond its gripping storyline, the series offers profound cybersecurity lessons that mirror today’s digital threats. Just as contestants face life-or-death challenges, your sensitive data battles against relentless cybercriminals daily.
CHECK OUT: Web Security Guide: Keeping Your Website Safe
Table of Contents
What Is The Squid Game All About?

The Squid Game’s rules mirror classic childhood games turned deadly. The perimeter drawn in sand represents a squid’s outline, with defenders patrolling the boundaries and attackers attempting to breach them while hopping on one leg. Once past the defenders, attackers can use both legs to reach the “squid head” and win—but one wrong move means elimination (or death, in the show’s context).
This high-stakes game serves as a perfect metaphor for cybersecurity:
- Defenders = Your security systems and IT team
- Attackers = Cybercriminals probing for weaknesses
- Squid Perimeter = Your network’s digital boundaries
Cybersecurity Lessons From Squid Game
| Lesson | Description | Real-World Application |
|---|---|---|
| Don’t Trust Easily (Red Light, Green Light) | The unsuspecting players are eliminated for trusting the deceptive doll’s instructions. | Be cautious of online interactions and information. Verify sources, avoid clicking suspicious links, and be wary of overly generous offers. |
| Information Asymmetry (Honeycomb Game) | Players with prior knowledge of the game (shapes) have a significant advantage. | Attackers often exploit vulnerabilities in software or human error. Stay updated on cybersecurity threats and best practices. |
| Strength in Numbers (Tug-of-War) | The stronger team (more members) wins, highlighting the importance of teamwork. | Utilize multi-factor authentication and implement security measures across your entire network (personal or business). |
| Physical vs. Digital Security (Glass Bridge Game) | The “tempered” glass bridge represents strong security, while the “normal” glass is a security weakness. | Implement strong passwords data encryption, and regularly update software to patch vulnerabilities. |
| Desperation Breeds Risk (Marbles Game) | Players take extreme risks due to desperation in the game. | Financial desperation can make people more susceptible to phishing scams or malware. Be cautious of online financial opportunities, especially those promising quick and easy returns. |
| Beware of Internal Threats (The Hostage Situation) | The game’s mastermind is revealed as one of the participants. | Insider threats can be just as dangerous as external threats. Implement access controls and be mindful of who has access to sensitive information. |
Case Study: The Red Light, Green Light Phishing Lesson
In 2022, Google reported blocking 100 million phishing emails daily. Just like players who moved during “Red Light” were eliminated, employees who click malicious links often compromise entire networks. A 2023 IBM study found that 95% of cybersecurity breaches result from human error—proving why verification is crucial.
What Does The Squid Game TV Series Have In Common With Cybersecurity?
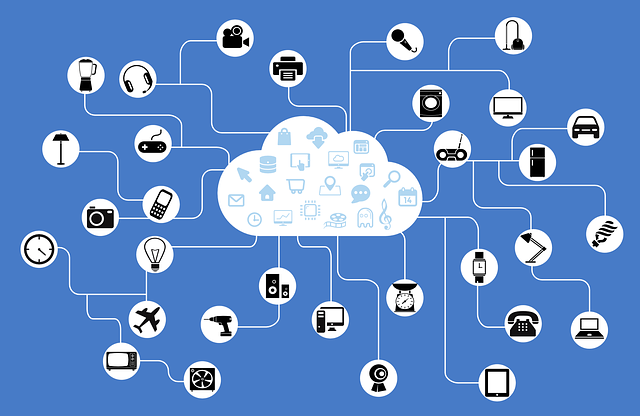
Modern organizations face attacks from multiple vectors—cloud, mobile, IoT devices—just as Squid Game contestants faced unexpected challenges. Here’s the cybersecurity parallel:
- The Squid Perimeter = Your network’s firewall and endpoint security
- Defenders = Your SOC (Security Operations Center) team and tools like SIEM systems
- Attackers = Advanced Persistent Threats (APTs) or ransomware gangs
READ ALSO: 5 Cybersecurity Tips To Protect Your Digital Assets As A Business
Cybersecurity Tips From Squid Game Series To Help You Up Your Game: SEASON 1
1. Build Your Defenses Like The Squid Perimeter
Actionable Steps:
- Conduct a data audit to identify critical assets (customer data, IP, financial records)
- Deploy next-gen firewalls with intrusion prevention (Palo Alto, Fortinet)
- Use endpoint detection and response (EDR) tools like CrowdStrike
- Budget at least 10-15% of IT spending on security (Gartner recommendation)
CHECK OUT: Best Antivirus For 2022
2. Network Segmentation: Isolate Like The Game’s Zones
Why It Matters: The 2023 Verizon DBIR found that 83% of breaches involved external actors jumping between systems.
Implementation Guide:
- Create VLANs for different departments (HR, Finance, R&D)
- Use zero-trust architecture (never trust, always verify)
- Implement micro-segmentation for cloud workloads
- Deploy privileged access management (PAM) solutions
CHECK OUT: Best VPN For 2022
3. Defense-in-Depth: The Glass Bridge Strategy
Like the tempered vs. normal glass in the show, layered security ensures attackers face multiple barriers:
| Layer | Security Measure | Example Tools |
|---|---|---|
| Perimeter | Firewalls, Email Filters | Cisco Firepower, Proofpoint |
| Network | IDS/IPS, Network Segmentation | Darktrace, Splunk |
| Endpoint | Antivirus, EDR | SentinelOne, Microsoft Defender |
| Data | Encryption, DLP | VeraCrypt, Symantec DLP |
CHECK OUT: GlassWire Network Firewall
4. Prepare For Unknown Threats (The VIPs’ Game)
The show’s unpredictable VIPs mirror advanced persistent threats (APTs). 34% of breaches in 2023 involved novel attack vectors (Source: Mandiant M-Trends).
Incident Response Plan Checklist:
- Conduct quarterly tabletop exercises
- Maintain an updated contact list for crisis response
- Store offline backups (3-2-1 rule: 3 copies, 2 media types, 1 offsite)
- Subscribe to threat intelligence feeds (Recorded Future, etc.)
Season 2 Cybersecurity Lessons: The Return of Deception 🎭
1. Advanced Social Engineering (The Recruitments)
In Season 2, returning or new participants are subtly manipulated into joining the deadly games, often through promises or emotional appeals. Just like in real life, attackers exploit trust to gain entry into systems.
Real-World Application:
- Train employees regularly to spot phishing emails, fake calls, and pretexting attempts.
- Simulate attacks through controlled phishing campaigns (tools like KnowBe4 or PhishMe).
- Verify unusual requests for sensitive information, even if they appear to come from leadership.
- Example: An employee receives a convincing “urgent invoice” email from finance. Without verification, clicking it could unleash malware — just as a contestant trusting the recruiter faces elimination.
2. Multi-Layered Monitoring (The Underground Games)
The hidden games in Season 2 feature multiple surveillance points, catching every subtle move, ensuring that mistakes don’t go unnoticed. In cybersecurity, single-layer defenses aren’t enough; threats can bypass one system and exploit another.
Real-World Application:
- Continuous network monitoring using SIEM tools like Splunk or LogRhythm.
- Behavioral analytics to detect unusual user activity or privilege misuse.
- Redundant checks for critical systems: firewall + EDR + endpoint monitoring.
- Example: Just like a contestant is watched by cameras in blind spots, attackers may lurk in systems unnoticed without comprehensive monitoring. Multiple layers make detection faster and containment more effective.
Season 3 Cybersecurity Lessons: Insider Threats Amplified 🕵️♂️
1. Exploiting Familiarity (The Insider Advantage)
Returning players leverage their prior knowledge to exploit vulnerabilities in new contestants. Similarly, insiders in organizations — whether employees, contractors, or partners — have knowledge that external attackers do not.
Real-World Application:
- Role-Based Access Control (RBAC): Only allow access necessary for a user’s role.
- Audit trails & logging: Track every action to identify suspicious behavior.
- Periodic access reviews: Revoke privileges that are no longer needed.
- Example: A former employee retains access to shared folders and exfiltrates data. Proactive monitoring and strict access controls prevent such exploitation.
2. Contingency Planning (The Extreme Twists)
Season 3 throws unexpected twists at players — sudden rule changes, hidden traps, and ambushes. Cybersecurity faces similar uncertainty with zero-day exploits, ransomware, and advanced persistent threats (APTs).
Real-World Application:
- Incident response plan: Keep it updated, test it quarterly, and include clear communication protocols.
- Redundant backups: Apply the 3-2-1 rule (3 copies, 2 media types, 1 offsite).
- Rapid patch management: Ensure critical updates are applied within hours of release.
- Example: A ransomware attack encrypts critical servers. Organizations with tested contingency plans restore systems quickly, just as contestants adapt to survive sudden game changes.
✅ Key Takeaways From Seasons 2 & 3:
- Trust is currency: Never assume trust — verify everything (Zero Trust).
- Knowledge is power: Insider awareness and monitoring prevent exploitation.
- Layer your defenses: One line of defense is never enough.
- Plan for surprises: Cyberattacks evolve; preparation reduces damage.
Squid Game Cybersecurity Lessons Table: Seasons 1–3
| Lesson | Season & Game | Description | Real-World Application / Actionable Tip |
|---|---|---|---|
| Don’t Trust Easily | S1 – Red Light, Green Light | Players eliminated for trusting deceptive instructions. | Verify online sources, avoid suspicious links, double-check offers. Implement zero-trust architecture. |
| Information Asymmetry | S1 – Honeycomb | Players with prior knowledge have advantage. | Keep software patched, educate staff, stay updated on threats, reduce knowledge gaps internally. |
| Strength in Numbers | S1 – Tug-of-War | Teamwork increases survival chances. | Apply multi-factor authentication across all systems; ensure network-wide security policies. |
| Physical vs. Digital Security | S1 – Glass Bridge | Strong glass = strong security; weak glass = vulnerability. | Use strong passwords, encrypt data, patch software regularly. Conduct penetration tests. |
| Desperation Breeds Risk | S1 – Marbles | Desperation leads to risky decisions. | Avoid hasty financial or security decisions. Train staff to recognize scams, phishing, and malware. |
| Beware of Internal Threats | S1 – Hostage Situation | Game mastermind is one of the participants. | Implement RBAC, audit logs, insider threat monitoring, and access reviews. |
| Advanced Social Engineering | S2 – Recruitments | Returning or new participants manipulated psychologically. | Conduct phishing simulations, train staff on social engineering, verify all unusual requests. |
| Multi-Layered Monitoring | S2 – Underground Games | Multiple surveillance systems catch mistakes. | Deploy SIEM, EDR, and behavioral analytics for continuous monitoring. Redundant checks prevent undetected breaches. |
| Exploiting Familiarity | S3 – Insider Advantage | Returning players exploit knowledge to gain edge. | Limit insider risk through RBAC, privilege reviews, logging, and monitoring suspicious behavior. |
| Contingency Planning | S3 – Extreme Twists | Unexpected twists force rapid adaptation. | Maintain and test incident response plans, use 3-2-1 backups, and implement rapid patching for zero-day threats. |
✅ How to Read This Table
- Season & Game: Identifies the Squid Game season and specific in-show game that illustrates the lesson.
- Lesson: The cybersecurity principle inspired by the show.
- Description: Explains the in-show analogy for easier understanding.
- Real-World Application: Concrete, actionable cybersecurity steps you can implement immediately.
Cybersecurity Lessons From Squid Game: FAQs
The show highlights distrust as a key cybersecurity principle. Isn’t that a bit extreme?
While absolute distrust isn’t practical, zero-trust architecture is now industry standard. Google’s BeyondCorp model proves that verifying every access request reduces breaches by 50%+.
How can small businesses implement Squid Game-level security affordably?
Start with these low-cost measures:
- Enable free MFA (Microsoft Authenticator, Google Authenticator)
- Use built-in security tools (Windows Defender, macOS Gatekeeper)
- Train staff with phishing simulation tools (KnowBe4 has free tiers)
How does the “information asymmetry” in the Honeycomb Game apply to real-world cybersecurity?
Just like players with shape knowledge had an advantage, cybercriminals exploit unpatched vulnerabilities. The CISA KEV Catalog shows 60% of breaches use vulnerabilities where patches existed but weren’t applied. Always update systems within 72 hours of patch releases.
The Marbles Game shows desperation leading to bad decisions. How does this translate to cyber risks?
Financial stress makes people 3x more likely to fall for “get rich quick” scams (FBI Internet Crime Report 2023). During economic downturns, fake investment scams increase by 200%. Always verify opportunities through official channels before acting.
What’s the cybersecurity equivalent of the Glass Bridge’s “testing each step”?
This mirrors penetration testing:
- Conduct annual red team exercises
- Use automated vulnerability scanners weekly
- Test backup restoration quarterly (40% of backups fail when needed)
How can teams collaborate securely like the Tug-of-War game winners?
Implement team-based security:
- Shared password managers (Bitwarden, 1Password)
- Role-based access controls (RBAC)
- Security champion programs in each department
Microsoft found this approach reduces incidents by 58%.
The show features disguised threats. What’s the cybersecurity parallel?
This represents fileless malware and living-off-the-land attacks:
- 31% of attacks now use legitimate tools like PowerShell
- Deploy behavioral analysis tools (CrowdStrike, SentinelOne)
- Monitor for unusual system tool usage patterns
How does the “elimination” concept apply to cybersecurity?
This mirrors automated threat containment:
- Set SIEM rules to isolate compromised devices
- Automatically revoke credentials after 3 failed logins
- Quarantine suspicious emails with sandboxing
Gartner shows this reduces breach impact by 72%.
Conclusion – Squid Game Cybersecurity Tips
Just as Squid Game contestants faced escalating challenges, cyber threats grow more sophisticated yearly. A 2023 CyberArk study found attacks increased by 38% YoY. By implementing these layered defenses—network segmentation, EDR, employee training—you create a security posture as resilient as the show’s tempered glass.
For further protection, explore our guide on protection tools against hackers and learn how to secure your systems against emerging threats.
INTERESTING POSTS
- 25 Best Hacking Movies For Cybersecurity Enthusiasts [2025 List]
- 8 Beginner Tips To Elevate Your Gaming Skills [From A Game Addict]
- Top 5 DDoS Attack Challenges For Telecom Companies
- Optimize Your PC With IOLO System Mechanic Ultimate Defense
- Software and Tips To Restrict Children To Adult Content Websites
- Xbox Exclusive Games You Should Try
- Best Black Friday Antivirus Deals 2024 – Up To 90% OFF
About the Author:
Gina Lynch is a VPN expert and online privacy advocate who stands for the right to online freedom. She is highly knowledgeable in the field of cybersecurity, with years of experience in researching and writing about the topic. Gina is a strong advocate of digital privacy and strives to educate the public on the importance of keeping their data secure and private. She has become a trusted expert in the field and continues to share her knowledge and advice to help others protect their online identities.