Read on to learn about Android SLocker Coronavirus malware.
In 2020, an Android malware variant disguised as a Coronavirus information app exploited anxieties surrounding the pandemic to lock users out of their phones and demand ransom payments.
While the threat is no longer actively circulating, it serves as a stark reminder of the evolving landscape of mobile security and the importance of vigilance.
Table of Contents
Android Malware Played on COVID-19 Fears, Demanding Ransom: A Reminder of Mobile Security
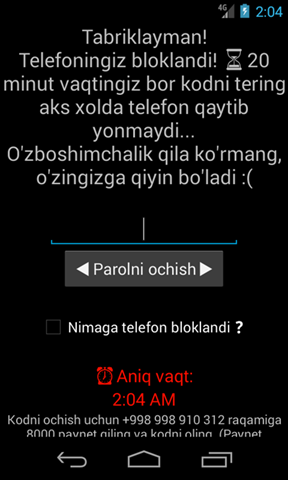
The malware, posing as an app named “Koronavirus haqida” (meaning “About Coronavirus” in Uzbek), targeted Android devices.
Upon installation, it locked the phone and displayed a message demanding a ransom payment to regain access. Although the data remained unencrypted, the malware effectively rendered the phone unusable, causing significant distress for unsuspecting users.
Fortunately, tech-savvy individuals discovered methods to remove the malware without paying the ransom, highlighting the importance of community knowledge and support in combating cyber threats. This incident underscores the need for users to:
- Download apps only from the official Google Play Store: Apps downloaded from unofficial sources often lack proper security vetting and may harbor malicious code.
- Remain skeptical of unsolicited apps: Be cautious of apps claiming to offer exclusive information or exploiting current events, especially if they appear outside the official app store.
- Keep software and apps updated: Regularly updating your phone’s operating system and apps ensures you have the latest security patches and bug fixes.
- Consider a reputable security app: Antivirus and security apps can provide additional protection against malware and other threats.
- Exercise caution with links and attachments: Be wary of clicking on suspicious links or opening attachments, even if they appear to come from trusted sources. Phishing scams often use current events to lure victims.
By adopting these practices, users can significantly reduce the risk of falling victim to mobile malware and protect their valuable data and devices. While the specific “Koronavirus haqida” threat is no longer active, it serves as a valuable lesson in the ever-changing world of cyber threats and the importance of proactive security measures.
READ ALSO: Your Essential Ransomware Guide: Prevention, Detection, and Recovery
Android SLocker Coronavirus Malware: Facts
| Feature | Description |
|---|---|
| Type | Ransomware disguised as a Coronavirus information app |
| Target | Android devices |
| Modus Operandi | An app called “Koronavirus haqida” (Meaning “About Coronavirus” in Uzbek) locked the phone and displayed a ransom message. |
| Impact | The phone is unusable, but data remained unencrypted |
| Resolution | Malware is removed via Safe Mode or ADB (Android Debug Bridge) without paying a ransom. |
| Current Status | No longer actively circulating but serves as a reminder of security threats. |
| Year Emerged | 2020 |
| Distribution Method | Downloaded outside of Google Play Store |
| Technical Details | Used AES encryption to lock the phone screen |
| Ransom Demand | Unknown |
| Similar Threats | Other malware variants may exploit current events or user anxieties. |
Android SLocker Coronavirus Malware: FAQs
Is this malware still a threat?
No, the specific “Koronavirus haqida” variant is no longer actively circulating. However, new malware campaigns emerge constantly, so it’s crucial to stay vigilant about mobile security practices.
READ ALSO: 15 Best VPN For Coronavirus Quarantine Holiday [100% WORKING]
What happened to users who downloaded this malware?
Though their data remained unencrypted, the malware locked users out of their phones, causing significant inconvenience and stress. Fortunately, tech-savvy individuals discovered methods to remove the malware without paying the ransom.
What are some key steps to protect myself from similar threats?
- Download apps only from the official Play Store.
- Stay skeptical of unsolicited apps, especially those exploiting current events.
- Keep your phone’s software and apps updated.
- Consider using a reputable security app.
- Be cautious with links and attachments, even from seemingly trusted sources.
What do you think about the Android Slocker Coronavirus malware?
RELATED POSTS
- How to Remove Apps on Android and iOS Devices
- Utimate List of Dangerous Apps
- 4 Best Mobile Browser for Android, iOS and Windows
- Urgent: Android users warned to delete these Vicious Apps from their devices
About the Author:
Mikkelsen Holm is an M.Sc. Cybersecurity graduate with over six years of experience in writing cybersecurity news, reviews, and tutorials. He is passionate about helping individuals and organizations protect their digital assets, and is a regular contributor to various cybersecurity publications. He is an advocate for the adoption of best practices in the field of cybersecurity and has a deep understanding of the industry.