Here is the CCleaner Kamo Review, read on.
In the world of digital technology, it is imperative to protect your online privacy, secure your online activities, and optimize your device’s performance to maintain online privacy.
Kamo software from Piriform is a privacy protection tool designed to protect you from advanced tracking and data collection techniques; should you entrust Kamo with your privacy, and what is Kamo’s role in safeguarding your online activities?
Read on to learn more about the Privacy app in this Kamo review.
What Is Kamo?
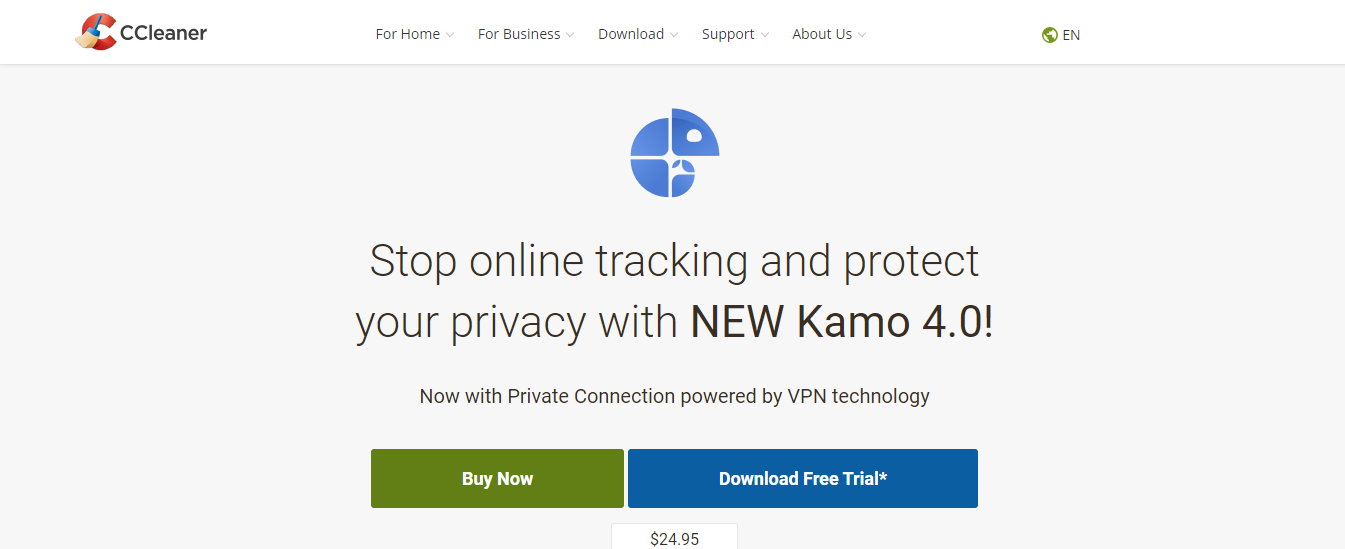
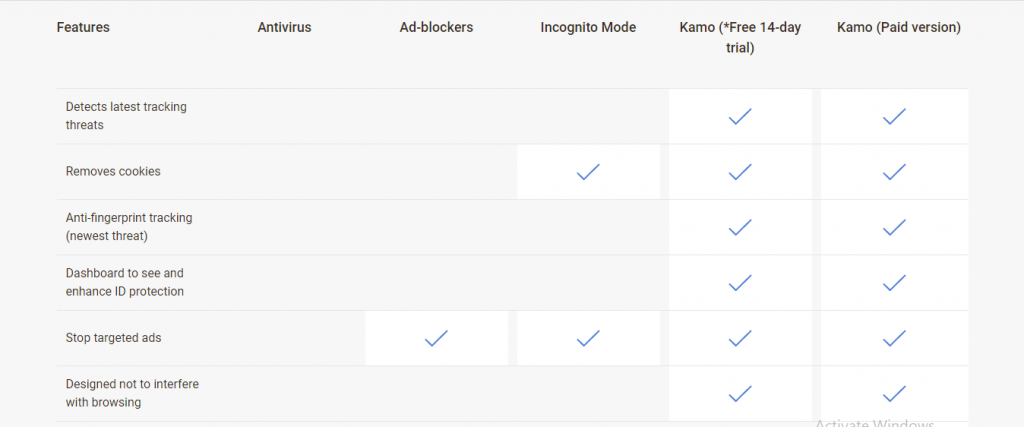
Kamo is a privacy app designed to protect your identity from advanced tracking techniques, such as fingerprinting and tracking, by utilizing a range of tools, including a basic VPN and anti-fingerprinting technology integrated into a single application.
In essence, Kamo employs VPN technology, often referred to as Kamo VPN, to encrypt your data traffic, mask your IP address, and obscure your exact geographic location. Along with its patented anti-fingerprinting technology to thwart digital fingerprinting, Kamo creates fake fingerprints by injecting fake data into your browser, which throws off trackers and third-party cookie collectors, offering robust tracking protection and tracker blocking.
📝Editor’s Note: We highly recommend that you remove your personal information from data broker sites and search engines. Get Incogni: Best Internet Scrubbing Service
How To Get Started With Kamo
- Go to the official Kamo website to download and install it
- Click ‘Yes’ in the User Account Control
- Set your language option to English or choose a preferred language
- Click ‘Next’ in the Kamo installation wizard
- Confirm you have read the End User License Agreement by clicking on ‘I agree.’
- Kamo automatically launches after installation is completed
- Click ‘Next’ to review the tutorial on how to use Kamo
- Type or paste in the activation code when prompted to do so.
==>> Get Kamo
Features
Intuitive User Interface
Kamo features a user-friendly dashboard that allows you to check your progress, monitor tracking activities, enhance ID protection with browser security features, and adjust other settings to maintain your digital safety.
The interface is navigation-friendly, making it an easy-to-use tool for privacy protection.
IP address and location masking
Kamo uses VPN technology to encrypt and protect your data traffic, and hide your IP address and location, providing a private connection that keeps you an anonymous user safe from hackers, government spies, and cookie trackers, while helping to hide sensitive data.
A privacy tool like a VPN protects your connection, but a mobile antidetect browser with Multilogin adds device-level defenses by emulating real mobile environments and isolating browser profiles to prevent fingerprint linking.
Anti-Fingerprint technology
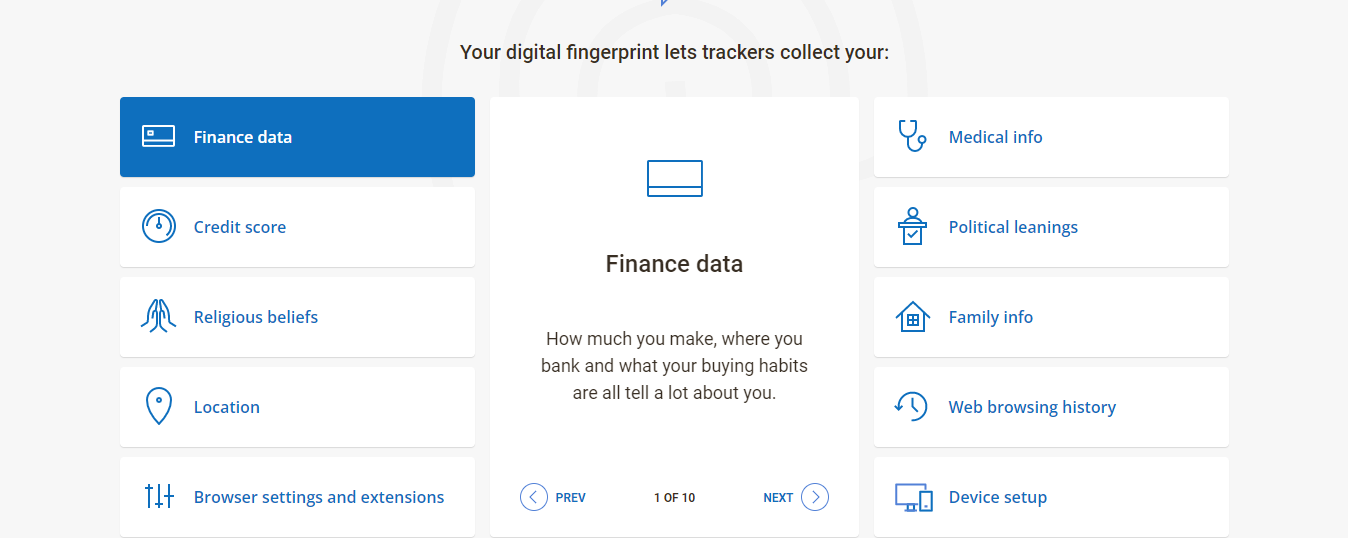
Kamo’s anti-fingerprint technology protects you from fingerprint tracking by generating random and false fingerprints that block trackers from harvesting your digital fingerprint data.
This protects you from advertisers and cookie trackers that collect browser data and cookies to serve you with personalized ads, while also helping to remove cookies that could compromise your privacy.
Anti-data theft and browser protection
Kamo safeguards your online privacy by performing a thorough browser cleanup, including the ability to clear browsing history and delete browser data. This ensures that third-party cookie trackers and advertisers can’t access your browsing activities, as Kamo leaves no trace behind.
Moreover, Kamo is designed to remove cookies, including zombie cookies and other persistent tracking elements, ensuring your browser remains clean and your personal information secure.
Uncovers trackers
Kamo enhances your digital security by pinpointing and blocking analytics from malicious websites. These sites often attempt to collect sensitive information, such as personal, medical, family history, and financial data; however, Kamo ensures that you only interact with trusted websites.
The tracking protection feature in Kamo provides a robust shield for your privacy, actively screening and blocking harmful data traffic from infiltrating your device.
- Read Also: Surfshark Antivirus Review
Auto-data syncing and clearing
For me, Kamo significantly improves the browsing experience by eliminating the need for manual intervention. Without the hassle of installing plug-ins, you simply purchase and install Kamo, and it seamlessly syncs with your browsers.
Kamo takes care of browser cleanup automatically, wiping out all browser history and cookies, thus relieving you from the burden of manually deleting browser data from each browser individually.
Ad blocker
While Kamo isn’t strictly an ad-blocker, it effectively blocks social media tracking by erasing your browser histories and cookies. Additionally, it injects fake fingerprints into your browser, disrupting the ability of trackers and advertisers to compile a complete profile for targeted ads.
Strict Privacy policy
Kamo is committed to enhance privacy with a strict data policy that ensures your personal data is not logged, nor is it sold to advertisers or third-party data collectors.
Kamo Compatibility
At the time of writing this Kamo review, which focuses on Windows privacy tools, I noted that Kamo supports only the Windows OS. It is, however, promising that future app versions may extend support to additional operating systems and devices, including Mac, Linux, Android, iOS, and others.
Kamo Customer Support And Resources
Kamo does not offer helplines for support agents to contact or email support; however, there is a detailed and organized FAQ page that addresses every issue you’re likely to encounter and provides answers to common inquiries.
Piriform reviews often highlight the helpful video tutorials available to guide users on how to utilize Piriform products. Additionally, there’s a fast-response online form for direct communication with Kamo’s customer care, a vibrant online community, and an intelligent live chatbot ready to handle your requests.
Below is a summary of Kamo’s support channels
- LiveChat bot
- Online form
- Video tutorials
- FAQs
- A vibrant community of experts
Kamo System Requirements
Kamo supports only Windows OS 7 and above with X86-64 processors; however, it does not support ARM processors, Mac, iOS, and Android OS, which may be a consideration for those looking into subscription options.
Kamo Pros And Cons
Pros
- Lifetime subscription
- Blocks advanced trackers
- Removes stubborn cookies
- Protects you from fingerprinting
- Intuitive user interface and dashboard
- Robust ad blocker
- Masks your IP and location
Cons
- Compatible only with Windows OS
- 14-day trial period
- Auto-server selection.
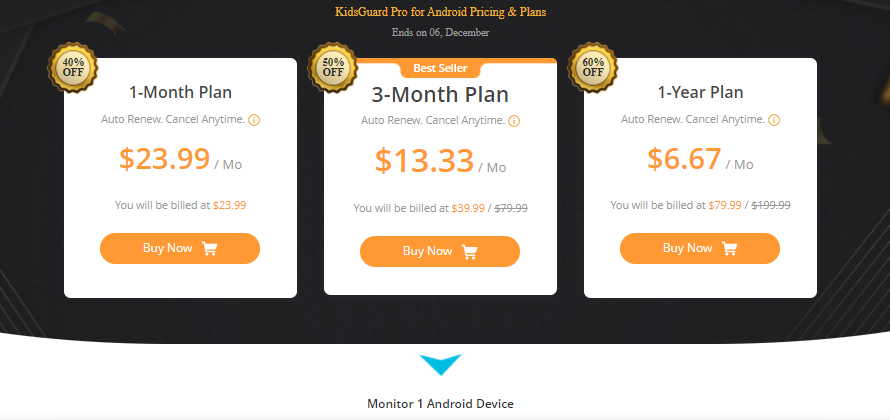
Kamo Pricing
A yearly subscription of $24.95 makes Kamo one of the most affordable privacy protection tools, thanks to its affordability and robust privacy protection features.
Kamo also offers a free trial valid for 14 days, after which you’ll need to purchase a yearly subscription to continue enjoying Kamo’s robust privacy protection services.
==>> Get Kamo
Digital Privacy Product Deals
CCleaner Kamo Review: Frequently Asked Questions
Is Kamo Safe?
If you are wondering whether Kamo by CCleaner is safe or not, then you should know that Kamo is a privacy app that is safe to use. In fact, it uses privacy protection tools like VPN, anti-fingerprint technology, ad blocker, and the likes for privacy protection and data security.
Is Kamo Different From CCleaner?
Both Kamo and CCleaner are from Piriform; however, they work differently and serve distinct functions. Kamo protects your identity by injecting fake digital fingerprints into your browser data to throw trackers and advertisers off track.
CCleaner is a system cleaner and optimizer that frees up space by clearing your system of junk and optimizing it to perform optimally.
Is Kamo An Antivirus?
No, Kamo is not an antivirus; however, it can protect your PC from malware and adware infections by blocking malicious data traffic, effectively preventing analytics that compromise your privacy.
Kamo enhances your online experience by establishing a private connection through a secure, virtual, encrypted tunnel, ensuring data transmission between your PC and the internet is private and shielded from government spies, hackers, and ISPs who might monitor your activities.
Therefore, to further enhance privacy, it is advisable to use a recommended antivirus in conjunction with Kamo and CCleaner for comprehensive system protection.
Is Kamo By CCleaner Free?
No, Kamo by CCleaner is not free. The pricing for the software starts at $24.95 per year, depending on the plan you choose.
Kamo excels in safeguarding your online privacy, making it a highly effective tool for protecting your private data and ensuring the security of your devices. It offers robust tracking protection by detecting and blocking malicious websites and tracking cookies, while also safeguarding your online identity.
CCleaner emerges as an excellent option for those seeking a comprehensive security and privacy solution.
Kamo boasts an array of features designed to safeguard your devices, data, and identity, all available at a competitive subscription cost compared to similar offerings on the market.
What is CCleaner Kamo?
CCleaner Kamo is a privacy-focused tool designed to protect your online identity and prevent tracking while browsing the internet. It helps mask your digital footprint by blocking tracking cookies, preventing websites from collecting your personal information, and offering features like automatic clearing of browsing data.
How does CCleaner Kamo work?
CCleaner Kamo works by masking your online activity and blocking cookies and trackers that collect data about your browsing habits. It also helps clear sensitive data, such as your browsing history, cached files, and passwords, ensuring better privacy.
Does CCleaner Kamo slow down my computer?
No, CCleaner Kamo is lightweight and designed to run in the background without affecting your system’s performance. It operates efficiently, so you should not notice any significant slowdowns while using it.
Does CCleaner Kamo work with all browsers?
CCleaner Kamo is compatible with most major browsers, including Google Chrome, Microsoft Edge, and Mozilla Firefox. Although it may not be fully compatible with all lesser-known or niche browsers, it supports the most commonly used ones.
How much does CCleaner Kamo cost?
CCleaner Kamo operates on a subscription model, charging a monthly or annual fee; however, it often offers a free trial for new users. Pricing details can vary depending on promotional offers and your subscription plan.
Can CCleaner Kamo be used on mobile devices?
Currently, CCleaner Kamo is primarily designed for desktop usage (Windows and Mac). It doesn’t have a dedicated app for mobile devices, but users can still achieve some privacy benefits through other mobile privacy tools.
A Final Word On The CCleaner Kamo Review
The integration of Kamo Piriform’s patent anti-fingerprint technology with VPN capabilities is a compelling reason to recommend Kamo as a formidable tool for privacy and data protection.
Kamo’s unique ability to generate random and false digital footprints to protect your personal data, thereby thwarting advertising companies from compiling a matching profile of you, distinguishes it from other privacy-protection tools.
Overall, Kamo does not come in as a substitute for premium VPN services since it is lacking in essential features like Kill Switch, Split tunneling, robust VPN protocols, Multihop, etc.; it does serve as a good substitute for users who may not be able to afford pricey VPN services, but desire to enjoy online anonymity and data protection.
==>> Get Kamo
INTERESTING POSTS
- The Ultimate Surfshark Incogni Review For Internet Users
- Full CCleaner Business Edition Review
- 8 Best Antivirus with VPN
- CCleaner: Hackers break into Avast Antivirus through an unsafe VPN
- LastPass’ Android Version Uses Seven Built-In Trackers
- Best System Optimization Tools for 2023
- 5 of the Best Secure Web Browsers