In the post, I will show you the best mobile browsers for Android, iOS and Windows phones.
In today’s mobile-first world, a reliable web browser is as essential as your phone. But with many options available, choosing the “best” browser can feel overwhelming. Fear not, fellow web wanderers!
This comprehensive guide will explore the top contenders for Android, iOS, and even the (admittedly niche) Windows Phone market.
We’ll delve into their strengths, weaknesses, and unique features to help you find the perfect browser for your mobile browsing needs.
Table of Contents
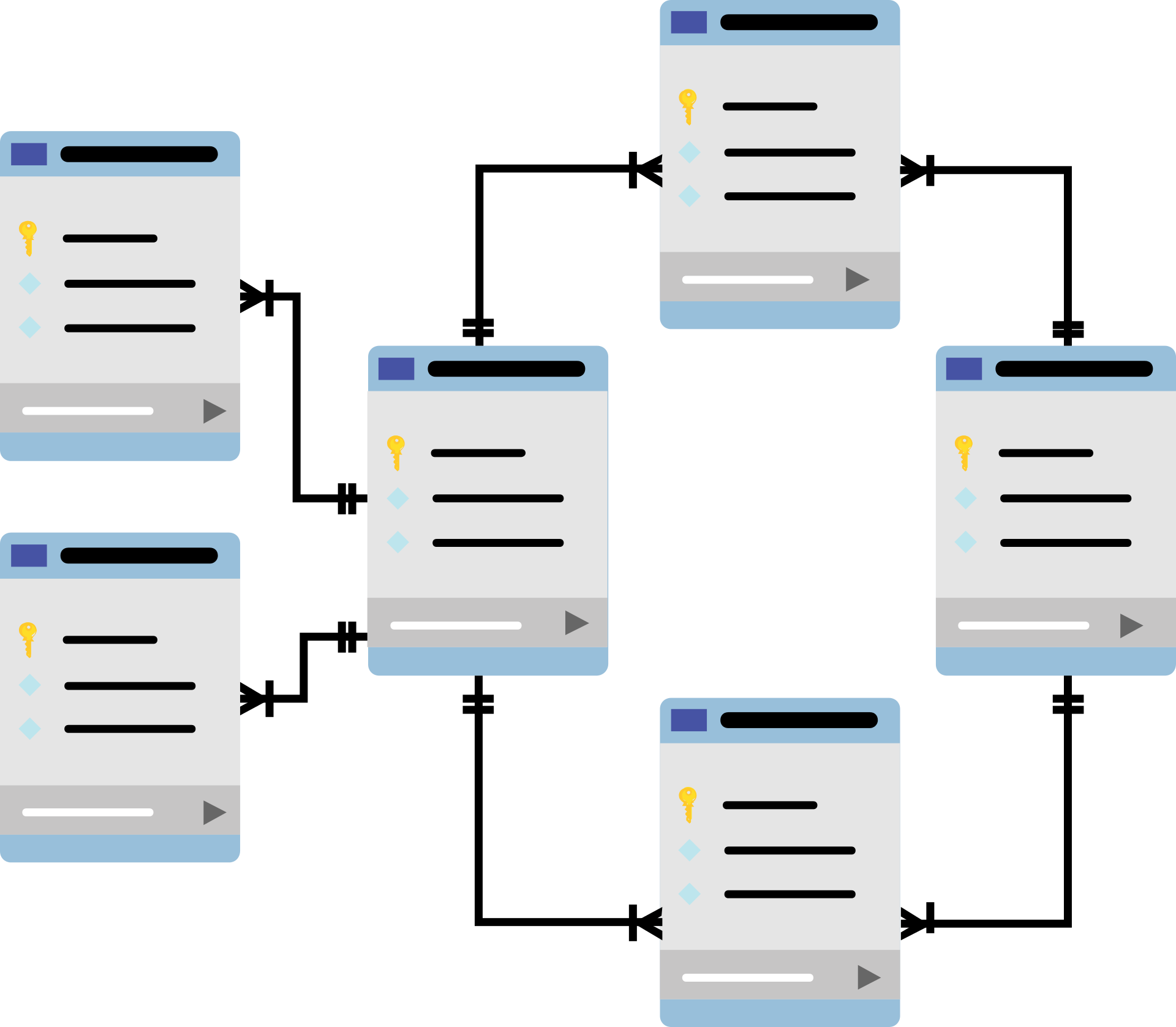
Best Mobile Browser: A Quick Comparison Chart
| Feature | Chrome | Firefox Focus | Samsung Internet | Brave | Opera Mini | Safari | Firefox (iOS) | Chrome (iOS) | Edge (Windows) | DuckDuckGo Go | Dolphin | Kiwi |
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Platform | Android, iOS | Android | Android | Android, iOS | Android, iOS | iOS | iOS | iOS | Windows Phone | Android | Android | Android |
| Focus | Performance, Extensions | Privacy | User Experience | Privacy, Speed | Data Efficiency | Simplicity, Apple Integration | Privacy | Performance (iOS) | Performance (Windows) | Privacy | Customization | Privacy, Background Playback |
| Extensions | Yes | No | Limited | No (Android), Limited (iOS) | No | No | No | No | No | No | Yes | Built-in ad blocking |
| Privacy | Default | Strong | Good | Strong | Very Good | Good | Strong | Default (iOS) | Good | Strong | Optional | Built-in ad blocking |
| Offline Reading | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes |
| Data Saver | Yes | No | Yes | No | Yes | Built-in | No | No | No | No | Optional | No |
The Android Arena: A Symphony of Choices
Google Chrome: The reigning champion, Chrome boasts lightning-fast speed, seamless integration with Google services (Gmail, Drive), and a massive library of extensions. It also syncs seamlessly with Chrome on desktop, offering a unified browsing experience. However, Chrome can be a battery hog and might not be the most privacy-focused option.
Mozilla Firefox Focus: This privacy powerhouse prioritizes security and user control. It blocks trackers by default, offers private browsing options, and doesn’t collect user data. However, it lacks some advanced features found in Chrome, like extensions and desktop syncing.
Samsung Internet Browser: Pre-installed on Samsung devices, this browser offers a clean interface, built-in ad blocking, and video assistant features for a smooth streaming experience. While feature-rich, it might not be as customizable as some other options.
Brave: This privacy-focused browser focuses on speed and security. It blocks ads and trackers by default, improving page load times and user privacy. It even rewards users with BAT tokens for viewing certain ads. However, its extension library is still under development.
Opera Mini: This lightweight browser shines on slower connections. Its data compression technology saves bandwidth and enables faster browsing, even on limited data plans. However, it may not be ideal for users who need high-fidelity multimedia experiences.
READ ALSO: How To Uninstall Programs On Various Windows OS [Windows 11, 10, 8, 7, Vista, & XP]
The iOS Island: A Walled Garden with Trusted Options
Apple’s iOS ecosystem offers a more curated selection of browsers, but with top-notch quality:
Safari: The default browser for iOS devices, Safari is fast, integrates seamlessly with iCloud and other Apple services, and offers a minimalist interface. However, it lacks the extension support found in Chrome and Firefox.
Firefox for iOS: This mobile version prioritizes privacy like its desktop counterpart. It offers built-in tracking protection and has a clean user interface. However, it might not be as feature-rich as Safari regarding Apple device integration.
Chrome for iOS: While not as feature-rich as its Android counterpart due to Apple’s restrictions, Chrome for iOS still offers a familiar interface and good performance. However, it lacks extension support and might not feel as “native” as Safari on iOS devices.
READ ALSO: Do I Need Antivirus App On Android Phone?
The (Almost) Forgotten Frontier: Windows Phones
While not as widely used as Android or iOS, Windows Phones still have a dedicated browser:
- Microsoft Edge: The default browser for Windows Phones, Edge delivers a clean interface and good performance. It also syncs seamlessly with Edge on a desktop for a unified experience. However, the lack of third-party app support on Windows Phone makes options like extensions scarce.
READ ALSO: How To Avoid Malicious Chrome Extensions [8 PROVEN Methods]
Beyond the Big Names: Hidden Gems in the Mobile Browsing World
Looking for something different? Here are some alternative browsers worth checking out:
DuckDuckGo Go App: This browser from the privacy-focused search engine prioritizes user anonymity with built-in tracking protection and a focus on secure connections.
Dolphin Browser: This veteran browser offers a high degree of customization, allowing users to personalize the interface and add features through extensions.
Kiwi Browser: A Chromium-based browser that prioritizes user privacy and offers features like built-in ad blocking and background playback.
Choosing the Right Browser: It’s All About You!
There’s no single “best” mobile browser. It depends on your individual needs and priorities. Consider the following factors:
- Performance: Do you need a blazing-fast browser for video streaming and heavy browsing?
- Privacy: Are security and user control paramount?
- Features: Do you need access to a vast library of extensions?
- Integration: How important is seamless integration with other apps and services you use?
- Data Usage: Concerned about using up your data plan quickly?
The Future of Mobile Browsing: A Glimpse Ahead
The mobile browser landscape is constantly evolving. Here are some trends to keep an eye on:
- Progressive Web Apps (PWAs): PWAs offer app-like experiences within a browser, blurring the lines between traditional apps and websites.
- Enhanced Security Features: Expect even greater focus on user privacy and security, with built-in features such as data breach notifications and malware protection.
- AI-Powered Browsing: Expect AI to play a bigger role in personalized browsing experiences, content curation, and voice search capabilities.
READ ALSO: Do I Need Antivirus App On iPad? [Here’s The ANSWER]
Conclusion: Charting Your Course in the Mobile Web
The perfect mobile browser is out there waiting for you. By considering your individual needs and exploring the diverse options available, you can find the ideal tool to navigate the vast ocean of the mobile web.
Remember, the best browser is the one that empowers you to browse securely, efficiently, and, most importantly, enjoyably!
We hope this comprehensive guide has helped you navigate the exciting world of mobile browsers! Happy browsing!
INTERESTING POSTS
- 5G Networks Likely to be Hacked Soon
- Browser Compartmentalization: How To Compartmentalize Your Web Browsers
- How to secure your digital devices
- How to Remove Apps on Android and iOS Devices
- 5 Best Browsers for Online Gaming
- Your Guide For Dealing With MacBook Malware
- 10 Best Lightweight Browsers For PC: Speed and Efficiency
- VPN Extension For Google Chrome – Benefits And Useful Tricks