This post will answer the question – what should security awareness training include?
According to statistics, employees are the weakest link in an organization regarding cybersecurity and are often considered the prime cause of data breaches. However, at the same time, employees can be a cybersecurity asset for an organization – provided they have the proper knowledge and training to identify and handle the threats.
So, what should practical security awareness training include? When designing a training program, covering all potential threats your organization faces is imperative.
This article will outline five essential aspects that must be included in a security awareness program.
Table of Contents
5 Components Of Security Awareness Training
Phishing Scams
Phishing scams are the most common method cyber criminals use to target an organization. Employees regularly get emails, and many of them open them without giving a second thought.
Hackers take advantage of this vulnerability and target employees by promising them some fake incentives such as a business opportunity, prize, or free travel, along with creating a sense of urgency.
Hence, every security awareness training must emphasize identifying and dealing with phishing emails. Examples should be given about standard methods used in phishing scams, including the following tips:
- Don’t trust unsolicited emails
- Always filter spam
- Don’t send personal or financial information to people who request it via email.
- Securely configure your email client
- Don’t click suspicious links in an email from an unknown person
- Be wary of email attachments
- Besides email, take precautions while handling SMS, social media messages, and enterprise collaboration platforms.
READ ALSO: 2024 Cybersecurity: The Rise of CyberAttacks
Malware
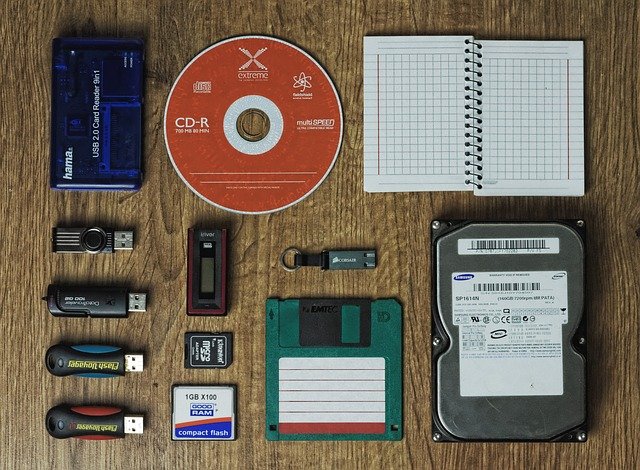
Malware or malicious software is used very commonly by cybercriminals for stealing sensitive user information, such as cardholder data or bank account details, or damage your organization’s system, resulting in substantial financial losses (ransomware). Malware is delivered in numerous ways, including phishing emails, removable media or drive-by downloads.
Security awareness training should cover the malware aspect and include common ways of delivery, threat potential and impact on your data. Along with other detailed information, it must consist of tips such as:
- Do not install unauthorized software program
- Always keep your antivirus up and running
- Use a firewall at all times
- Don’t download any unknown files through email or websites
- Immediately contact your security team if you suspect a malware infection
READ ALSO: Most Effective Cybersecurity Strategy For A Small Business [We Asked 45+ Experts]
Password Security
Passwords are the most common method of authenticating a user. Many employees create dozens of accounts online that they can access through a username and password.
If password security practices are not followed, they can risk the entire organization’s network. Hence, your training content should include some critical password management tips, such as:
- Use a different password for every online account.
- Use a password manager that generates and stores unique, strong passwords for every account.
- Generate passwords randomly
- Use multi-factor authentication where possible to lessen the impact of a compromised password.
Removable Media
Removable storage media is an easy tool for hackers to help them enable malware and bypass network-based security checks of an organization. The malware gets installed through removable media if executed automatically via Autorun or by keeping catchy filenames and tricking employees into clicking the file.
This removable media can install ransomware, steal your data or even destroy the computer it is inserted into. Malware-infected removable media can come into your employees’ possession at conferences or public events. Hence, they must be trained to manage any second-hand removable device. You should train your employees to:
- Never plug an untrusted device into their computer
- Get all untrusted removable devices scanned from the IT or security department
- Disable the Autorun option on all computers.
Privacy and Data Management
Most organizations, especially those dealing with customer data, collect, store and process sensitive information. It includes customer information, business plans, employee data, and other forms relevant to the organization.
If this data gets exposed to the public, cybercriminals, or a competitor, your organization can face penalties and suffer huge losses to consumer relationships.
Employees should be trained to manage confidential business data and protect their customers privacy and data security. This critical training content should include:
- Data classification strategy of the organization and how data can be classified at each information level
- Regulatory requirements affecting the routine operations of an employee
- Approved and unapproved locations for storing sensitive data on an enterprise’s network
- Using strong security practices for accounts that hold sensitive data
Key Takeaways
Employees are an essential asset of every organization and play a vital role in the success of a business.
Untrained and unknowledgeable personnel can put an organization at risk of potential data breaches. Hence, organizations must implement a security program that encompasses all aspects of securing and preventing security incidents resulting from human error.
Besides annual or biannual training, it’s also vital to give reminders frequently through emails, office posters, or flyers. Make training material readily available and incentivize employees who take proactive measures to ensure security within the organization.
INTERESTING POSTS
- Shut Cybercrime Door With Cybersecurity Training For Employees
- Integrating Security Awareness Training Into Employee Onboarding
- Breachers Gonna Breach: Protect Your Organization From Internal Threats
- How To Secure Devices Against Phishing Emails
- Why Is Data Backup And Recovery So Important?
- CyberVista Review: Reliable Cybersecurity Awareness Training
About the Author:
Daniel Segun is the Founder and CEO of SecureBlitz Cybersecurity Media, with a background in Computer Science and Digital Marketing. When not writing, he's probably busy designing graphics or developing websites.
Meet Angela Daniel, an esteemed cybersecurity expert and the Associate Editor at SecureBlitz. With a profound understanding of the digital security landscape, Angela is dedicated to sharing her wealth of knowledge with readers. Her insightful articles delve into the intricacies of cybersecurity, offering a beacon of understanding in the ever-evolving realm of online safety.
Angela's expertise is grounded in a passion for staying at the forefront of emerging threats and protective measures. Her commitment to empowering individuals and organizations with the tools and insights to safeguard their digital presence is unwavering.