In this post, we will reveal the signs and effects of adware. Plus, how to remove them from your web browsers.
Adware is malicious software (malware) that prompts up ads on computer screens – usually while surfing the net.
However, there is more to this program than malware. This article provides a concise review, highlighting the signs, effects, common examples, and steps to remove adware.
READ ALSO: Adware Guide for Beginners
Want to learn more about this malicious program? Read on!
Table of Contents
What Is Adware?
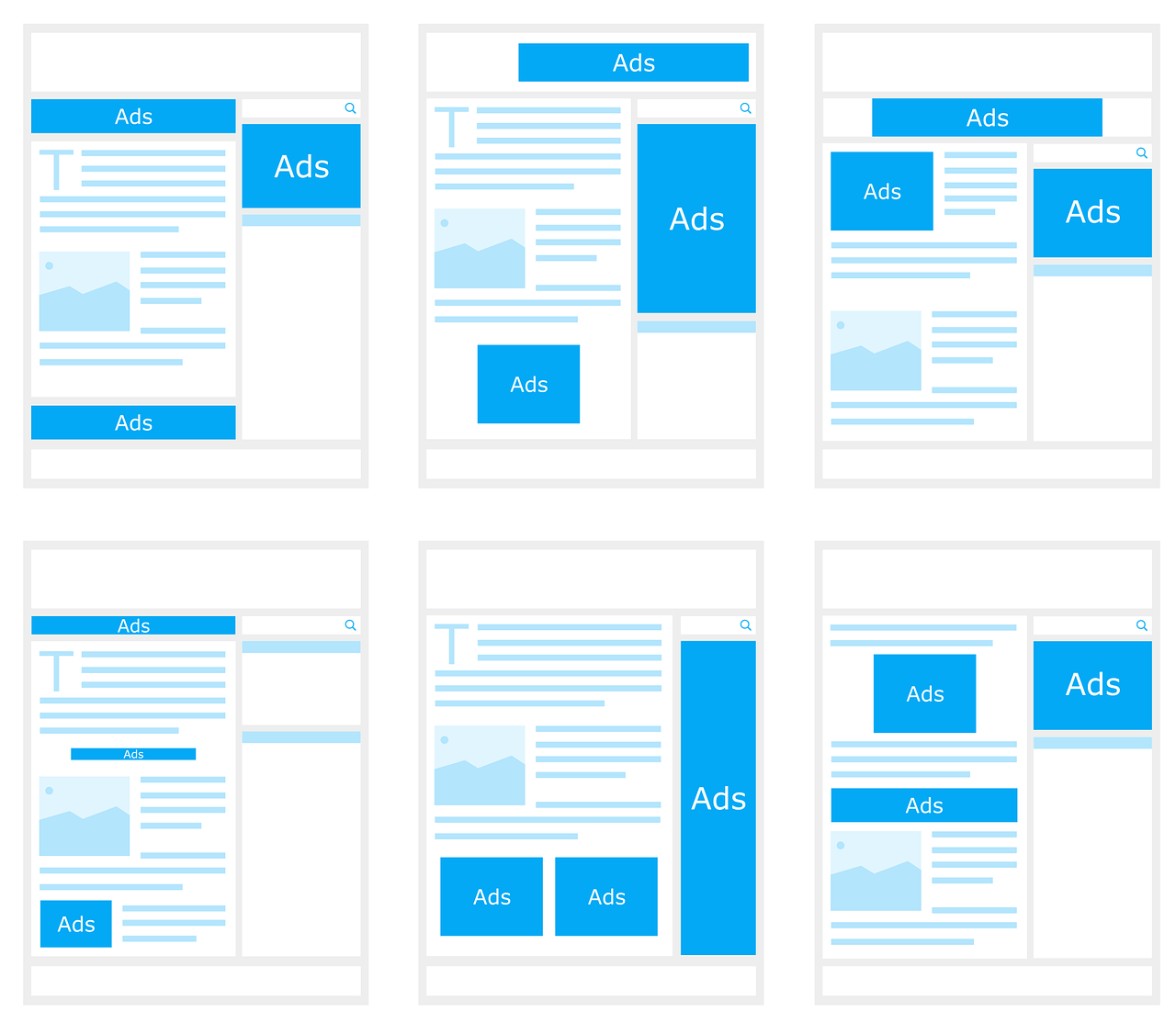
Adware is the shortened form of “advertising malware”; it’s designed to hijack the navigability of web browsers – throwing up unwanted adverts and redirecting web searches to advert pages.
The program is widely known in the cyber world as a modern-day PUP – Potentially Unwanted Program.
Typically, the unwanted pop-ups that suddenly appear on your screen while surfing the net are mainly associated with adware. However, these pop-ups are sometimes standard components of a website.
 Furthermore, this program differs slightly from other forms of malware in that it causes little to no harm to the host computer or its inherent files.
Furthermore, this program differs slightly from other forms of malware in that it causes little to no harm to the host computer or its inherent files.
Nonetheless, some adware is notorious for information theft. This category of adware is similar to “trojan spyware”, which is highly notorious for data theft and cyber-espionage.
Essentially, adware is used by advertising agencies, albeit illegally, to gather information about potential clients/customers or promote a particular product.
READ ALSO: Tor+VPN Guide: How to Combine Tor Browser With VPN
Adware Signs And Effects
As pointed out earlier, “advertising malware” differs from other forms of malware. Usually, an adware invasion provides less cause for worry, compared to the invasion of spyware or Trojans.
In most cases (if not all), this program does not impede the smooth running of infected computers, except, of course, the nuisance created by the pop-up ads, as well as the web redirects.
Similarly, a typical adware reveals itself to the victim. Most of the time, it requests permission (usually in disguise) before accessing privileged information.
However, its revelation is in its effects – the pop-up ads, as there is usually zero indication or traceable record of adware installation on your device.
- READ ALSO: Best VPN For 2023
- READ ALSO: Best Antivirus For 2023
Common Sources Of Adware Infection
Adware lurks in various corners of the digital world, waiting to infiltrate your devices and bombard you with unwanted ads.
Here are some of the most common sources to be aware of:
1. Freeware and Shareware
While free software can be tempting, it often comes bundled with adware. During installation, some programs may sneakily install adware alongside themselves, often hidden within the fine print of agreements that you may skip reading.
2. Infected Websites
Clicking on malicious links or visiting compromised websites can expose your device to adware. These websites might contain hidden scripts or exploit vulnerabilities to inject adware onto your device.
3. Malicious Email Attachments
Opening infected attachments in emails, especially from unknown senders, can be a gateway for adware. These attachments might disguise themselves as legitimate documents but actually contain adware hidden within.
4. Peer-to-Peer (P2P) File Sharing
Sharing files through P2P networks can be risky. Downloaded files, especially from unreliable sources, may be laced with adware that is waiting to be unleashed on your device.
5. Fake Software Updates
Phishing tactics can be used to trick users into installing fake software updates that are actually disguised as adware. Always verify the legitimacy of updates before installing them.
6. Mobile Apps
Even app stores, although typically safer, can harbor malicious apps containing adware. Be cautious when downloading apps, read reviews, and only download from reputable sources.
7. Deceptive Ads
Clicking on pop-up ads that promise free items or claim to detect “viruses” on your device can lead to an adware infection. Always exercise caution when interacting with online advertisements.
By recognizing these potential threats and practicing safe browsing habits, you can significantly reduce your risk of encountering adware and protect yourself from its intrusive and potentially harmful effects.
READ ALSO: 7 Strange Tips for Selecting an Antivirus Program
How To Remove Adware
Adware can be a nuisance, but don’t panic! Here’s a comprehensive guide on removing it from your device:
1. Scan with your Antivirus
Most antivirus software offers adware protection in addition to virus protection. Run a full system scan to detect and remove any adware it might find.
2. Check Browser Extensions
Open your browser settings and review the list of installed extensions. Look for any unfamiliar or suspicious entries, especially those that have been recently added. Remove any extensions you don’t recognize or use.
READ ALSO: Comprehensive Malware Guide: Safeguarding Your Digital World
3. Manage Installed Programs
Go to your device’s control panel or settings (depending on your operating system) and access the list of installed programs.
Look for programs you don’t remember installing or that seem suspicious. Research them online to verify their legitimacy. If confirmed as adware, uninstall them immediately.
4. Consider Dedicated Anti-Adware
In some cases, more robust solutions might be needed. Dedicated anti-adware programs specialize in detecting and removing adware that might escape traditional antivirus software.
Consider using a reputable anti-adware program to eliminate stubborn adware infections.
5. Manual Removal (Advanced Users)
This approach is only recommended for advanced users as it involves modifying system settings and potentially deleting critical files.
If comfortable, research specific instructions for your operating system and the identified adware to manually remove its files and registry entries. Proceed with caution and back up your data beforehand.
Additional Tips
- Clear your browser cache and cookies: These can sometimes harbor traces of adware.
- Change your browser homepage and default search engine: Adware might have altered these settings.
- Reset your browser settings: This can be a drastic option, but it can also be effective in removing adware that has deeply embedded itself in your browser settings. Be aware that resetting your browser will erase all your saved data, bookmarks, and passwords.
- Be cautious with future downloads: Only download software from trusted sources and pay attention to the installation process to avoid accidentally installing adware.
To remove this program from your computer, you can use a standard malware scanner or a versatile antivirus program, such as AVG. Check our Deal page for some of the best malware remover tools.
READ ALSO: 5 of the Best Secure Web Browsers
Protecting Yourself from Adware
In addition to the removal methods mentioned above, it’s crucial to take proactive steps to protect yourself from future adware infections.
Here are some essential practices:
- Download software only from trusted sources: Avoid downloading applications from untrustworthy websites or clicking on pop-up ads that promise free software. Opt for official app stores or a reputable gaming blog.
- Be cautious with free software: While free software can be tempting, consider the potential risks associated with it. Read reviews from trusted sources before installing, and opt for premium versions if they offer enhanced security features.
- Use a reputable antivirus with built-in anti-adware protection. Consider security solutions like those offered by the AntivirusWithVPN blog, which protect against viruses and include adware detection and removal capabilities.
- Stay informed: Keep yourself updated on the latest adware threats and trends. Resources can provide valuable information and guides on staying safe online.
READ ALSO: Difference Between A Virus, Malware, Adware, Trojans, And Ransomware
Adware: Frequently Asked Questions
What is adware?
Adware is software that displays unwanted advertisements on your computer, phone, or other devices. These ads can appear in various forms, including pop-ups, banners, and even video ads. They can be disruptive and interfere with your browsing experience, and in some cases, they may even be malicious.
What are the signs and effects of adware?
Some common signs that your device might be infected with adware include:
- A sudden increase in pop-up ads, even on websites you normally trust.
- New toolbars or browser extensions appear without your knowledge.
- Your browser’s homepage or search engine has been changed unexpectedly.
- Your device is running slower than usual.
- Difficulty closing browser windows or programs.
How can I get infected with adware?
Adware can enter your device in several ways, including:
- Downloading free software or games from untrusted sources.
- Clicking on suspicious links or ads.
- Installing browser extensions from unknown developers.
- Opening infected email attachments.
READ ALSO: How To Clean An Infected Computer
How can I remove adware?
There are several methods for removing adware, depending on the severity of the infection. Here are some steps you can take:
- Run a scan with your antivirus software: Most antivirus programs offer protection against adware as well as viruses.
- Check your browser extensions and remove any you don’t recognize.
- Manually remove suspicious programs from your computer’s control panel.
- Consider using a dedicated anti-adware program: These programs can be more effective in detecting and removing stubborn adware infections.
Bottom Line
As we said earlier, adware is one of the many forms of malware that infest your web browsers. Hence, you should take the necessary precautions when surfing the net.
If you’re unsure about how to remove adware safely, it’s always best to consult a trusted computer technician or refer to reputable online resources for detailed guides.
Additionally, it is best that you read the terms and conditions of freeware/shareware apps before installing them on your computer.
Share your adware experience with us by commenting below.
RELATED POSTS
- Browser Compartmentalization: How to Compartmentalize Your Web Browsers
- How to Configure Popular Web Browsers with Proxy Information
- How to uninstall a Program on various Windows OS
- Cryptojacking Across Europe: Multiple Supercomputers Get Hit
- 5 Certified Benefits of Identity Theft Protection
- Understanding Ad Blocker: The Ultimate Guide to Blocking Ads Online
- Adware Vs Ransomware Showdown: Decoding the Threat