In this post, we will show how to check your IP address by using three quick and easy methods.
In today’s interconnected world, your IP address is your unique online identifier. It’s a numerical label assigned to your device whenever you connect to a network, allowing communication and data exchange.
Understanding your IP address and how to check it is crucial for various reasons, including troubleshooting network issues, accessing geo-restricted content, or simply being aware of your online footprint.
This comprehensive guide explores various methods for uncovering your IP address, catering to different devices and operating systems.
IP (Internet Protocol) Address is the unique set of numbers that links your computer with all your online activities.
It is like an address for return delivery. For example, without an IP address, you can’t have access to any website you may be trying to access.
Table of Contents
What You Should Know About IP Address?
- Your PC is connected to the internet whenever you go online for any activity—your request to access a site.
- Your PC network is configured with a set of networking standards and rules called ‘Protocols.’ One of your PC’s protocols is the Internet protocol, which is responsible for attaching an IP address to your PC. Internet protocol also addresses, delivers, and channels your requests to the website and back to your PC.
- Every request you send online is attached with your IP (return address) for a perfect delivery.
- Your IP address changes each time you connect to a different network. The IP address is assigned to your PC by your network provider or the network you’re connected to at home, office, and other public places.
- It can also be used to protect your online privacy. For instance, a VPN can provide you with a different IP address for anonymity.
READ ALSO: Dos And Don’ts Of Using A Public Wi-Fi [Ultimate Guide]
Understanding IP Addresses: A Primer
There are two main types of IP addresses:
- IPv4 (Internet Protocol Version 4): The most common type, consisting of four sets of numbers separated by periods (e.g., 192.168.1.1). However, the pool of available IPv4 addresses is nearing exhaustion.
- IPv6 (Internet Protocol Version 6): The next-generation IP address format, offering a significantly larger address space represented by eight groups of hexadecimal digits separated by colons (e.g., 2001:0db8:85a3:0000:0000:8a2e:0370:7334).
Throughout this guide, we’ll focus on uncovering IPv4 and IPv6 addresses depending on the method used.
How To Check Your IP Address On Windows 10 & 11
Method 1: Check your IP address Using Network Connections
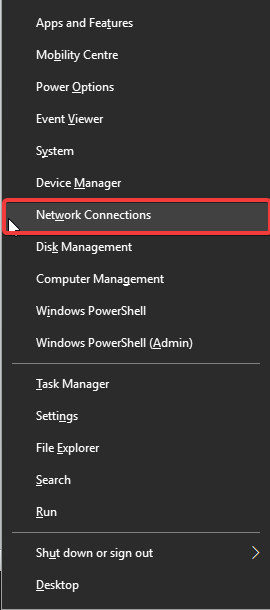
- Press the Windows key + X and select ‘Network connections’ from the options displayed.

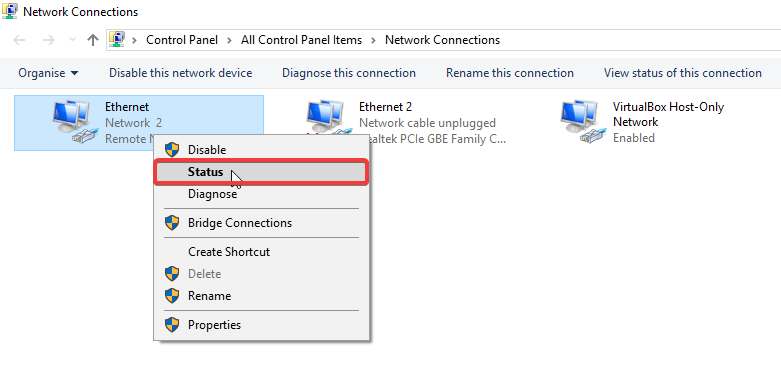
- Select the network you’re connected to
- Right-click and select status.

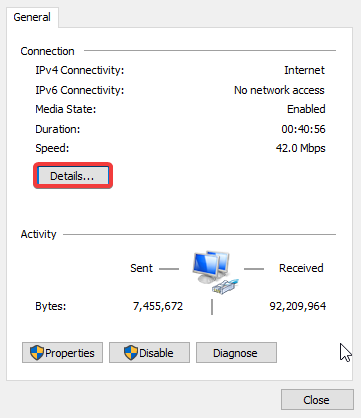
- Click on ‘Details’

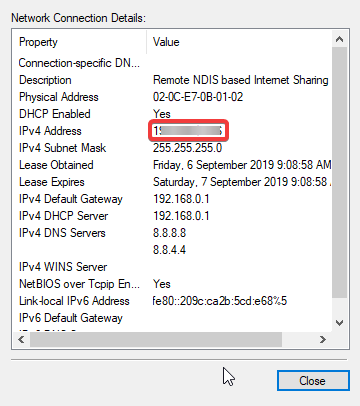
- Details of your IP and address will be displayed.

Method 2: Use the Command Prompt
- Open the Command Prompt by searching for “cmd” in the Start menu and pressing Enter.
- In the black command window, type
ipconfigand press Enter. - Locate the lines labeled “IPv4 Address” and “IPv6 Address” to find your respective IP addresses.
Method 3: Use the Taskbar Network Icon
- Right-click on the network icon on the taskbar in your screen’s bottom right corner.
- Select “Open Network & Internet settings.”
- Follow steps 3 and 4 from the “Settings App” method above.
READ ALSO: How To Run Command Prompt On Windows 11, 10, 8, 7, etc.
How To Check Your IP Address On A Mac
Here’s how to find your IP address on a Mac computer:
Method 1: Use System Preferences
- Click on the Apple icon in the top left corner of your screen and select “System Preferences.”
- Navigate to “Network.”
- Select the network connection you currently use (e.g., Wi-Fi or Ethernet) from the list on the left side.
- Click on the “Advanced” button.
- Under the “TCP/IP” tab, locate “IPv4 Address” and “IPv6 Address” to find your respective IP addresses.
Method 2: Use Terminal App:
- Open the Terminal app by searching for “Terminal” in Spotlight (press Command + Spacebar) and selecting it.
- In the Terminal window, type
ifconfigand press Enter. - Locate the lines labelled “inet addr” (for IPv4) and “inet6” (for IPv6) to find your respective IP addresses.
How To Check Your IP Address on a Smartphone or Tablet (Android & iOS)
Here’s how to find your IP address on your mobile device:
Android
The method for checking your IP address on Android devices can vary slightly depending on the specific device model and operating system version. Here’s a general guideline:
- Open the Settings app on your Android device.
- Navigate to “Network & internet” or “Wi-Fi” settings.
- Tap on the network you’re currently connected to (e.g., Wi-Fi network name).
- Look for options like “Advanced settings,” “Network details,” or similar wording.
- Your IP address (both IPv4 and IPv6, if available) should be displayed within these settings.
iOS
- Open the Settings app on your iPhone or iPad.
- Tap on “Wi-Fi.”
- Click on the information icon (i) next to the Wi-Fi network you’re connected to.
- Scroll down to find “IP Address” listed to view your IPv4 address. Unfortunately, iOS settings don’t natively display the IPv6 address. However, you can leverage a third-party app like “Network Analyzer” or a web-based tool to uncover your device’s IPv6 address.
READ ALSO: What Is Automated IP Address Management?
How To Check Your IP Address on Gaming Consoles and Smart TVs
Gaming consoles and smart TVs often connect to the internet, and you might need to know their IP addresses for network configuration or troubleshooting purposes. Here’s a general approach, but consult your device’s specific user manual for detailed instructions:
Gaming Consoles (PlayStation, Xbox): Navigate to the network settings section on your console. The location might vary depending on the model, but it’s typically found under “Settings” or “Network.” Look for options displaying “Connection Status,” “IP Address,” or similar wording within the network settings.
Smart TVs: Similar to consoles, access the network settings on your smart TV. This option is usually found under “Settings” or “Network.” Locate menus displaying “Network Information,” “IP Address,” or similar terms to find your device’s IP address.
How To Check Your IP Address Using Online Tools
There are a lot of sites where you can check your IP address. These websites work by accessing your device’s connection and identifying the IP address assigned by your internet service provider (ISP).
These websites not only show you your IP address, but they also show you other information like:
- Hostname
- ASN
- ISP
- Organization
- Type
- Continent
- Country
- State/region
- City
- Latitude
- Longitude
Here are some popular online tools for checking your IP address:
- WhatIsMyIP.com
- IPify.org
- MyIP.io
While convenient, remember that these websites only reveal your public IP address. This address identifies your entire network and not necessarily your specific device on the network.
Alternatively, you can type “what is my IP address” on Google from your web browser to get an accurate result.
READ ALSO: Best DNS, IP, and WebRTC Leaks Test Sites
Bottom Line
By understanding these methods and the different types of IP addresses, you’ll be well-equipped to check your IP address whenever necessary.
This knowledge can empower you to troubleshoot network issues, manage your online presence, or better understand how your device interacts with the vast internet landscape.
Note: This was initially published in September 2019 but has been updated for freshness and accuracy.
RELATED POSTS
- 8 Best VPNs For China And Hong Kong (+5 Reliable Ones)
- Best System Optimization Tools
- Most Dangerous Websites You Should Avoid
- The Ultimate List Of Geo-restricted Streaming Services
- Tor+VPN Guide: How to Combine Tor Browser With VPN
- What Is My IP Address? Understanding IP Address Basics
- 35 Confidential Command Prompt Tricks You Should Know


![How To Check Your IP Address [Quick Methods] How To Check Your IP Address [Quick Methods]](https://secureblitz.com/wp-content/uploads/2019/09/check-your-ip-address-768x512.jpg)