In this post, I will show you how cloud consulting services guide companies through digital change.
Cloud transformation is more than just a buzzword. It is a strategic business shift that involves adopting cloud computing to modernize IT processes and foster innovation. It’s more than just moving data. Cloud migration aims to change how technology supports your business goals.
But how are you supposed to do all of this alone? This is where cloud consulting services come in! This brief guide explains how cloud consulting services drive digital transformation and help companies become future-ready. Let’s get in!
Requirement Analysis
First things first, cloud transformation services review a business’s existing IT setup. Their aim is to pinpoint gaps and opportunities.
Let’s say a retail company wants to migrate its e-commerce store to the cloud. Consultants will assess the existing e-commerce platform and understand its architecture. They will also gather feedback and preferences to determine why moving to a cloud-based infrastructure is necessary.
Planning and Strategy Creation
Once cloud consultants have understood unique business needs and requirements, they will create a customized cloud transformation strategy. Think of it as creating a cloud roadmap, crafting the optimal cloud architecture, and selecting appropriate cloud services.
They will also determine a suitable deployment method. This could be public cloud, private cloud, or hybrid cloud.
Strategic Migration
This is where practical cloud transformation begins. A reliable consulting service provider like Sutherland will outline the steps required to move the application and its data to the cloud. Their aim? Ensure minimal downtime, so major operations aren’t jeopardized.
Consultants might take one of the following migration approaches for each app:
Rehost: Moving the app as-is.
Replatform: Making minor tweaks for cloud benefits.
Refactor/Re-architect: Doing a major redesign for cloud-native.
Repurchase: Moving to a SaaS solution.
Retire: Decommissioning unused apps.
Retain: Keeping on-prem for now.
Relocate: Moving with minimal change (like VMware on Cloud).
A cloud consultant will make detailed timelines, allocate responsibilities, and keep tabs on each part of the migration to avoid running into any issues in the long run.
Architecture and Development
Cloud consultants design scalable and resilient cloud infrastructure. For instance, consultants implement Continuous Integration/Continuous Delivery (CI/CD) protocols.
Continuous Integration (CI) involves automatically building, testing, and preparing code for release, making it always releasable. The next step, Continuous Delivery (CD), means fully automating the release to production. For a business transitioning to a cloud infrastructure, this means their new system is ready to launch.
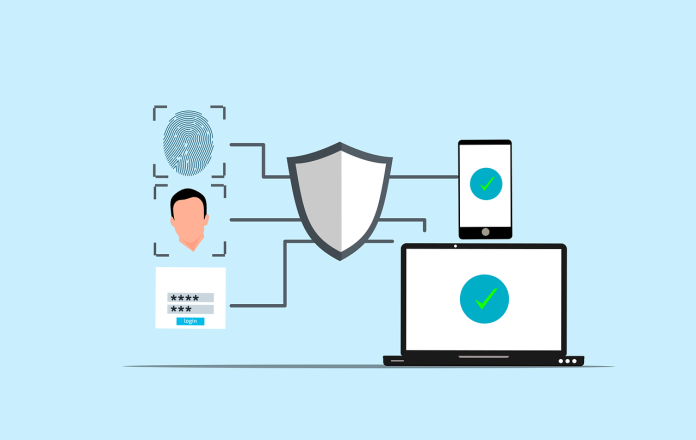
Cloud Security
Cloud consulting isn’t just about migration. Consultants also make your infrastructure risk-free. They set up security protocols, such as:
- Encryption
- Identity and Access Management (IAM)
- Network segmentation
- Automated security threat alerts
The result? Your cloud infrastructure will always meet industry norms and security regulations. State-of-the-art security features will help you anticipate attacks and predict future security breaches.
Regulatory Compliance
Reputable cloud consulting providers ensure your newly launched infrastructure is compliant with industry regulations, including those under GDPR, HIPAA, and PCI DSS.
This is especially true for businesses working in data-sensitive industries, such as healthcare or cybersecurity.
INTERESTING POSTS