In this post, I will talk about securing the IIoT edge.
For decades, the factory floor was a fortress of solitude. Industrial Control Systems (ICS) operated in an “air-gapped” environment, physically disconnected from the corporate IT network and the outside world. Security was defined by physical access; if you couldn’t touch the machine, you couldn’t hack it.
That era is over. Industry 4.0 has dismantled the air gap, replacing isolation with hyper-connectivity. Today’s manufacturing environments are driven by the Industrial Internet of Things (IIoT), where data flows seamlessly from sensors to the cloud.
While this connectivity drives unprecedented efficiency, it also drastically expands the attack surface. Industrial controllers and sensors—once obscure operational technology (OT)—are now frontline security risks. Securing this new landscape requires a “Defense in Depth” strategy, merging robust IT security protocols with rigorous hardware lifecycle management.
The Vanishing Air Gap: IT/OT Convergence Explained
What is the IIoT Edge?
In a manufacturing context, “The Edge” refers to where the physical action happens. It is not just about local servers; it encompasses the operational hardware that drives production. This includes Programmable Logic Controllers (PLCs), Human-Machine Interfaces (HMIs), and distinct robotic actuators.
Unlike standard IT assets, these devices are designed for specific physical tasks. Their operating systems are often proprietary and stripped down to minimize latency. Consequently, they prioritize availability and speed over encryption or user authentication. A delay of milliseconds for a security handshake might be acceptable in an email server, but it can cause a catastrophic failure in a high-speed assembly line.
Why the Merge is Inevitable
Despite the inherent security challenges, the convergence of Information Technology (IT) and Operational Technology (OT) is driven by undeniable business value. Manufacturers are integrating these systems to achieve:
- Predictive Maintenance: Using vibration and heat sensors to predict part failure before it halts production.
- Real-Time Analytics: Adjusting production flows dynamically based on supply chain data.
- Remote Monitoring: Allowing engineers to diagnose machinery issues from off-site locations.
The operational benefits are too significant to ignore. Businesses cannot afford to disconnect; therefore, they must learn to protect the converged environment effectively.
III. Key Vulnerabilities in Industrial Hardware
The “Legacy” Problem
One of the most significant risks in OT security is the age of the infrastructure. It is not uncommon to find critical infrastructure running on hardware that is 10 to 20 years old—technology designed long before modern cyber threats like ransomware existed.
In the IT world, an outdated server is simply replaced or patched. In the OT world, “patching” a physical motor controller is often impossible. The hardware may not support modern firmware, or the vendor may no longer exist. Yet, replacing the entire system could require millions in downtime and re-engineering.
To maintain operational stability, facility managers often need to source specific industrial automation components that match their existing infrastructure, ensuring that legacy systems remain reliable even as network defenses are upgraded. This strategy allows for continuity while the broader security architecture is modernized around the vulnerable hardware.
Insecure Endpoints and Default Passwords
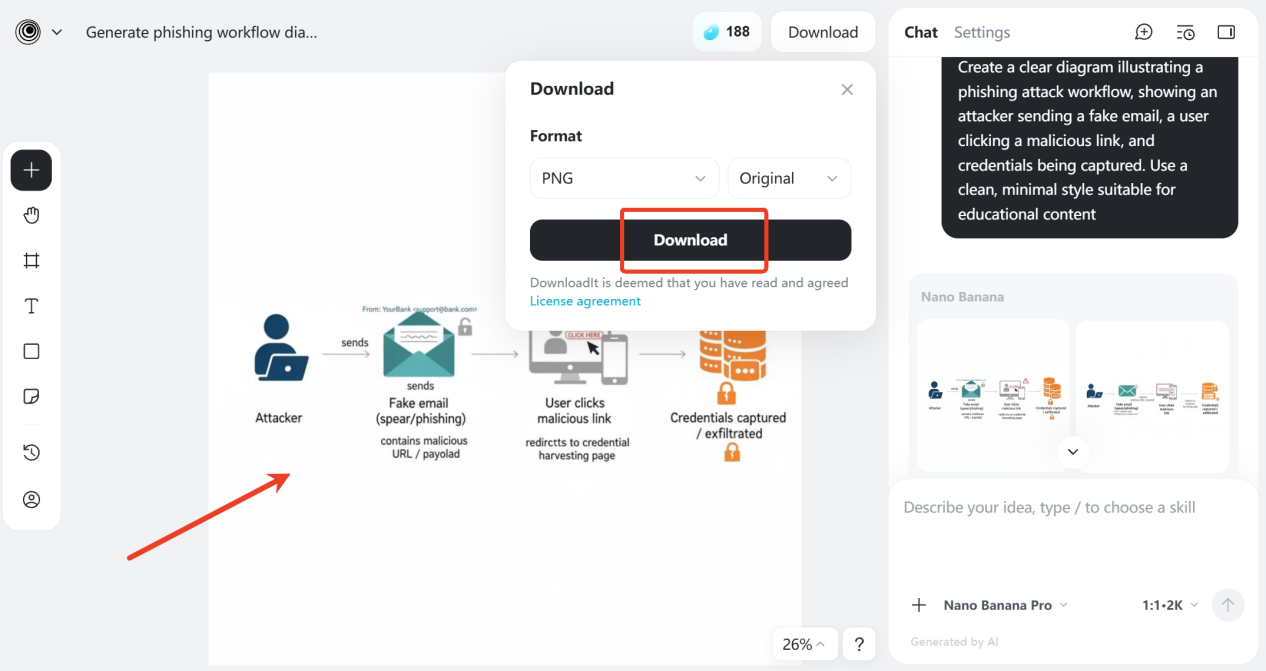
A surprising number of breaches originate from basic oversight. It is tragically common to find sophisticated perimeter firewalls protecting devices that still utilize factory-default credentials (e.g., “admin/1234”).
Hackers utilize specialized search engines, such as Shodan, to scan the internet for exposed industrial ports (like Modbus or TCP/IP ports used by PLCs). If these endpoints are left on default settings, they become open doors for attackers to manipulate machinery, alter temperature setpoints, or simply shut down production.
The Hardware Supply Chain Risk
Software is not the only vector for attack. The physical supply chain presents a growing threat in the form of “Hardware Trojans” or counterfeit modules. A compromised chip embedded within a controller can be designed to bypass software firewalls entirely, acting as a physical backdoor.
Counterfeit components may also lack the rigorous quality control of genuine parts, leading to unpredictable failures that can be exploited to cause physical damage to the plant.
Strategic Defense: Securing the Factory Floor
Network Segmentation and Zoning
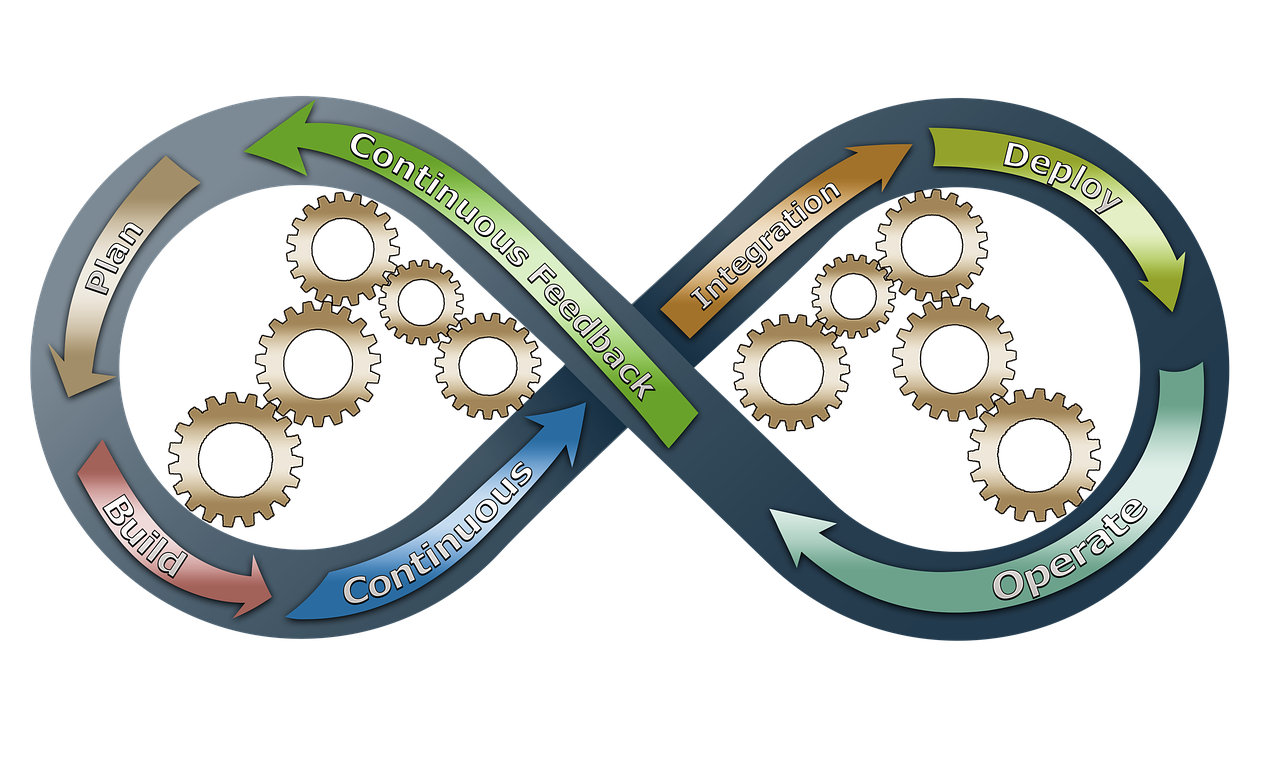
The most effective defense against lateral movement in a converged network is segmentation. Following standards like IEC 62443 or the Purdue Model, organizations should architect their networks into distinct zones.
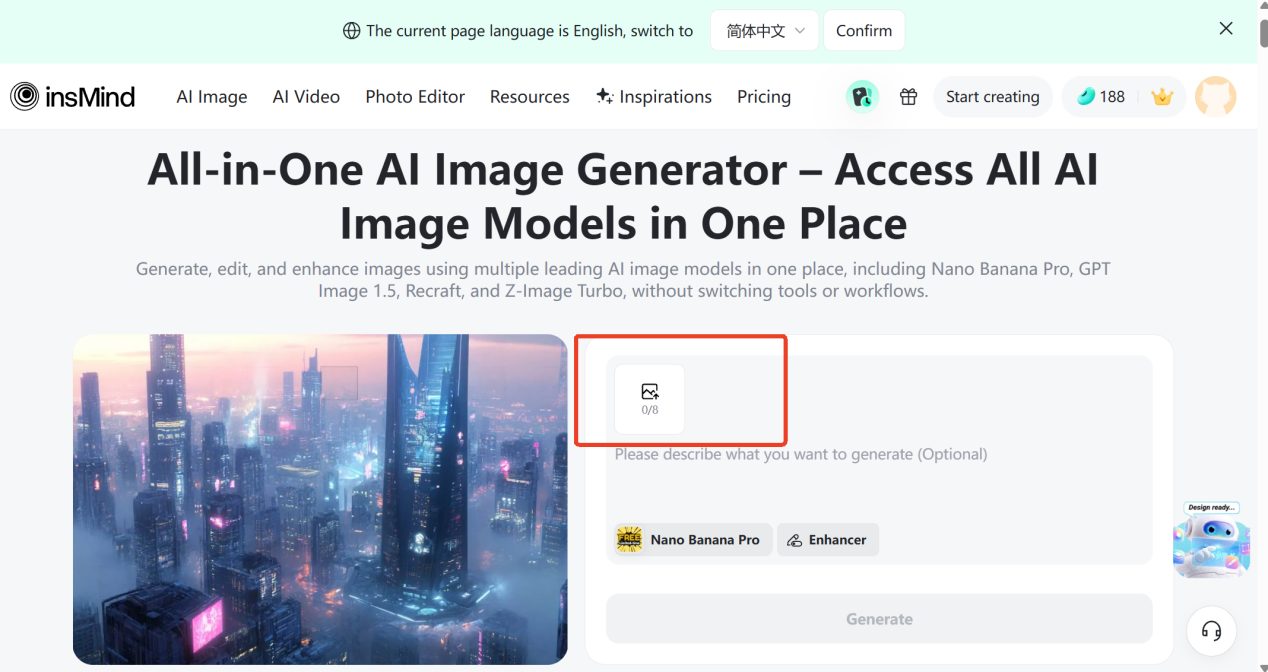
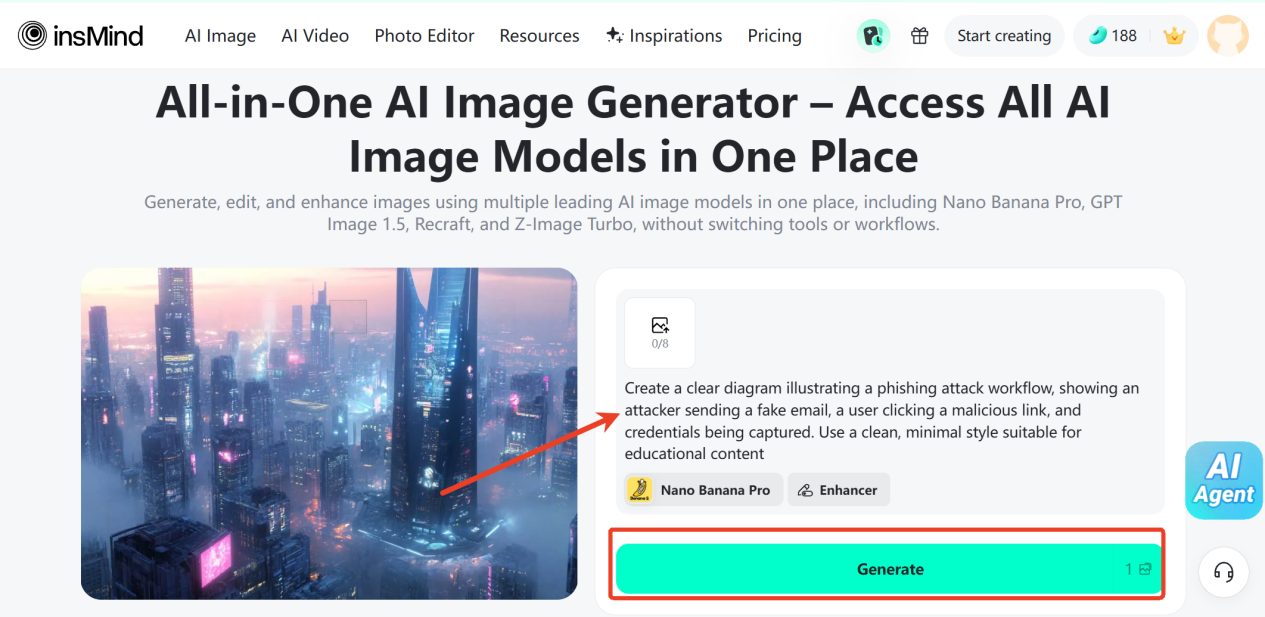
Actionable Tip: Establish a Demilitarized Zone (DMZ) between the enterprise office network (IT) and the plant floor (OT). This ensures that a malware infection from a phishing email in the HR department cannot propagate directly to the assembly line controllers.
Vetting Your Supply Chain
Security starts at procurement. In an effort to cut costs or find obsolete parts quickly, procurement managers may turn to unverified gray markets. This significantly increases the risk of acquiring tampered, refurbished, or counterfeit goods sold as new.
Procurement teams must prioritize vendors who guarantee authenticity and quality, which is why platforms like ChipsGate focus on vetting the integrity of automation modules before they ever reach the factory floor. By establishing a chain of trust that extends to the physical component level, organizations can mitigate the risk of hardware-based attacks.
Continuous Monitoring and “Zero Trust”
The perimeter is dead; trust nothing. A Zero Trust architecture assumes that a breach has already occurred or will occur. This mindset requires continuous verification of every user and device, even those already inside the network.
For OT environments, active scanning can sometimes crash sensitive equipment. Instead, use passive monitoring tools. These tools analyze traffic patterns to establish a baseline of “normal” behavior and alert security teams to anomalies—such as a PLC attempting to reprogram another PLC or communicating with an unknown external IP address.
Conclusion
The Smart Factory represents a massive competitive advantage, but it demands a paradigm shift in how we view security. We can no longer treat physical hardware and digital security as separate domains; they are a single, interconnected ecosystem.
Security in the IIoT era is not a “set it and forget it” product. It is a continuous process of rigorous monitoring, intelligent network segmentation, and securely sourcing the critical infrastructure that powers the modern world.
INTERESTING POSTS
- The Future of Manufacturing: Cutting-Edge Tech
- Energy Sector: Top MDR Companies to Protect Critical Infrastructure in 2025
- Power System Cybersecurity: More Important Than Ever
- Ways To Prevent Supply Chain Attacks
- Securing B2B Payment Systems: Protecting Electronic Transactions from Cyber Threats
- The Convergence of AI, Automation, and Risk Management
- 5 Benefits of Custom Fit Toyota Floor Mats Over Universal Mats