Here, we will show how a Nigerian Fraud ring hijacked the Washington unemployment system in one of the most significant business email compromise (BEC) scams.
It is no longer news that Washington and about six other US states have been victims of fraud attacks by the Scattered Canary. According to an ongoing investigation from the Federal Department of Justice, hundreds of millions of dollars were siphoned from the endless unemployment benefits payout due to the economic and financial effects caused by the coronavirus pandemic.
In what appears to be the largest COVID-19 unemployment fraud to have ever emerged from Africa, the world was awakened to scattered reports from multiple sources involving millions of dollars fraudulently stolen by hackers.
A West African-based cybercrime group allegedly spearheaded these named the “Scattered Canary,” as revealed by Agari, a security research firm. The group used stolen identities from a previous data breach involving consumer information.
Seattle Times and other local media outlets reported the COVID-19 unemployment fraud. However, Agari’s Cyber Intelligence Division (ACID) has been trailing and investigating the cybercriminal group of hackers involved and has managed to penetrate the group’s activities.
When the news broke out about Washington State losing millions of dollars to cyber-criminals, the security research firm intensified its investigation to expose the criminal masterminds behind the group.
Table of Contents
Scattered Canary And The 35 Cybercriminals
This West African-based cybercrime group did not start big, but it was founded in 2008, so they’ve had enough time to hit big while remaining unidentified until now. From a “one-man gang” known as Alpha, whose operation was centered on Craigslist, eBay, checks, and romance scams, to a full-blown cartel of criminals strengthened by 35 members engaged in various kinds of fraud running concurrently.
Previously, Alpha, who had a mentor named Omega (under whose guidance he refined his nefarious activities), carried out profitable scams by exchanging approximately 1,950 emails. According to reports, he reportedly earned up to $23,500 per month.
Presently, the “Scattered Canary” group has evolved to include sensitive data phishing, romance scams, tax fraud, employment scams, social security fraud, W-2 scams, credit card fraud, fake job listings, payroll diversion, business email compromise (BEC), and other forms of fraud, as outlined by ACID.
According to ACID, “one common fallacy is that crime rings run within set steeps; believing that cybercrime groups only run business email compromise (BEC) scams and concentrate only on such is a misconception. They are like entrepreneurs in any industry; cybercriminal gangs operate to achieve growth by designing and evaluating extensible business models through various sets of revenue streams.”
The security research firm continued, “During the research into Scattered Canary, records of how the main cybercrime leaders encountered situations where opportunities for diversification came calling saw them delve into them like genuine entrepreneurs.”
Read Also: 1,000 Chinese Nationals Suspected In Massive Online Scam
Based on their agile working methods, they expanded by recruiting more “skilled” cybercriminals through material and financial enticement by displaying their wealth on social media and other possible platforms.
“With trust, a biased approach to candidate selection can be achieved, and many relationships were built while still in the tertiary institutions within West Africa where talent is effortlessly noticed, and recruitment is easily done.” The research firm alluded.
Scattered Canary’s Operations
Since 2008, when the group became active, they have been linked to several significant attacks:
Covid-19 Unemployment Benefit scams (2019-2020)
This, without argument, overshadows their previous engagements, not because it is the most recent and currently trending, but because it is the biggest so far and happened due to the ongoing coronavirus pandemic.
According to The Seattle Times, the group filed approximately 174 unemployment and insurance claims using stolen identities in Washington alone, which are estimated to be worth about $1,339 per week per claim. Experts estimate that about 1 out of 4 claims are said to be from cyber criminals, of whom Scattered Canary remains a top suspect.
Most of their proceeds end up in Asia, Nigeria, and other parts of West Africa after being converted to Green Dot prepaid cards and cryptocurrencies.
READ ALSO: How To Secure Your WhatsApp Group From Hackers
Targeting of top CEOs (2018)
It was reported in 2018 that a group called London Blues (suspected to be in collaboration with Scattered Canary) attacked top business executives and chief financial officers around the world through business email compromise (BEC), requesting vast sums of money to be paid to an external account while posing as insiders in these companies.
Businesses worldwide lost an estimated $12 million between 2013 and 2018, according to the FBI. Although the scam appears common, approximately 50,000 top CEOs were targeted by the group.
READ ALSO: E-Commerce Fraud: Navigating the Challenges in Online Retail
Active Toolkits Used By Scattered Canary
Members of the Scattered Canary group deploy various tools to help them WORK faster and easier. This includes phishing message templates and multiple VPNs to mask their location as they exchange scam emails with their victims.
VOIP phone numbers were also obtained from online service providers such as Hushed, Google Voice, and TextMe, while operating from Nigeria or any part of West Africa. An ACID investigation revealed that the group used the same callback number for previous cyberattacks, making it easy for the research firm to delve deeply into their activities.
The cybercriminal gang also utilizes a variety of model text documents, known as “formats,” which expedite their phishing process. ACID revealed that “the group gathered their potential victim’s leads by signing up with Lead411 lead generation service and using 7-day trial accounts totaling twenty times within three years.” “We could identify a format containing 26 different message templates that could be used to target corporations in various BEC scams, including W-2 fraud and direct deposit”, ACID concluded.
Scattered Canary And The Present Reality: 4 Years After
ACID relayed all evidence and reports gathered from their investigation to the FBI and Interpol. This helped the security agencies in the recent raid that led to the arrest of some members of the Scattered Canary gang, including Woodberry (Mr. Woodbery) and Hushpuppi (Raymond Igbalodeyl), in Dubai, with their properties allegedly seized.
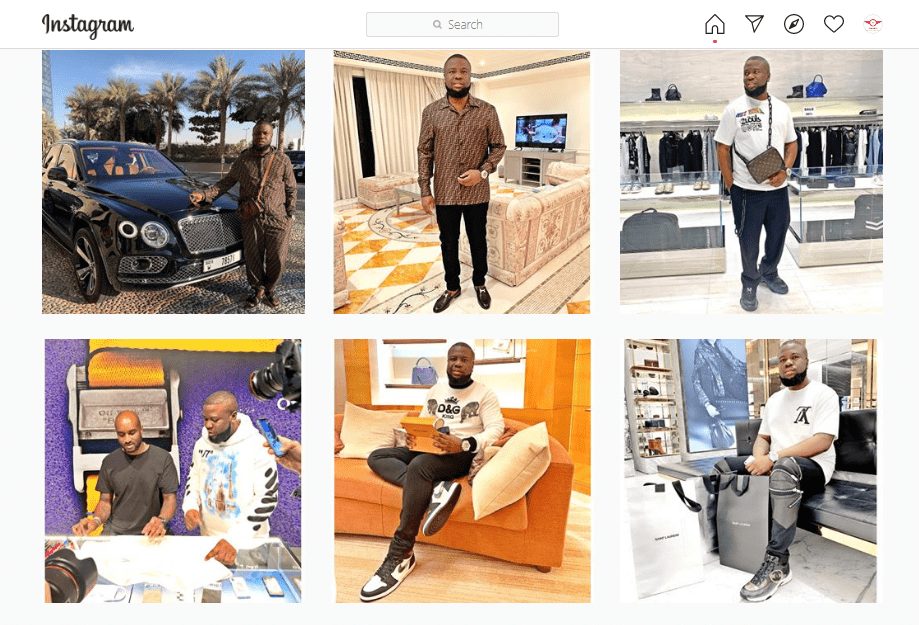
In Nigeria, their arrest trended on popular social media sites like Instagram, Facebook, and Twitter. The duo is known to display their luxurious lifestyles, with the “in your face” show of expensive cars, houses, clothes, and even drinks on these platforms.
Many Nigerians, including KCee, an influential Nigerian musician, have often questioned their sources of wealth to afford such a lifestyle.
With this new development, it appears that more cybercriminal gangs will undoubtedly end up in the net of law enforcement agencies.
The group’s present reality revolves around sophisticated cybercrime operations. Business Email Compromise (BEC) scams have become their weapon, infiltrating company email systems to divert funds to their accounts.
During the COVID-19 pandemic, Scattered Canary capitalized on vulnerable unemployment systems, stealing millions of dollars in government aid. Their reach extends beyond BEC, encompassing tax return fraud and credit card scams, demonstrating a diverse and adaptable criminal repertoire.
A Persistent Threat
Scattered Canary’s continued success highlights the ever-present threat of cybercrime. Their longevity highlights the importance of robust cybersecurity measures at both the individual and organizational levels. Businesses must prioritize employee training to identify phishing attempts and secure email systems.
Looking Forward
As technology continues to evolve, so will the tactics of cybercriminals like Scattered Canary. Staying informed about the latest threats, implementing robust online security practices, and remaining vigilant are essential steps toward a safer digital future.
By understanding the present reality of cybercrime groups like Scattered Canary, we can proactively protect ourselves and mitigate their potential impact.
RELATED POSTS
- Cyber Threats: How To Secure Your Computer Against Cyber Threats
- Most Effective Cybersecurity Strategy For A Small Business [We Asked 45+ Experts]
- Exposed: Italian Company Fronting for Guloader Malware Operations
- Notorious hackers infect authentic 2FA apps with malware
- 5 Common Online Scam Tactics
- 5 Top Apple Mail Alternatives For iPhone And Mac
- What Should You Expect From The Best Washington DC IT Support?
- Gift Cards Are Increasingly Popular Among BEC Scammers
- How to Protect Yourself from Online Fraud [6 Surefire Internet Safety Tips]
- 5 Cybersecurity Tips To Protect Your Digital Assets As A Business
About the Author:
Gina Lynch is a VPN expert and online privacy advocate who stands for the right to online freedom. She is highly knowledgeable in the field of cybersecurity, with years of experience in researching and writing about the topic. Gina is a strong advocate of digital privacy and strives to educate the public on the importance of keeping their data secure and private. She has become a trusted expert in the field and continues to share her knowledge and advice to help others protect their online identities.








