A lot of workers in the IT industry have CompTIA certificates. As a result, many IT professionals consider the certificate entry-level and too basic. Some say the certificate won’t help them as they don’t see the value in a certification that doesn’t set them apart from other IT experts.
However, many others still count on the value of the certificate to help them get jobs and promotions. To be straightforward, a CompTIA certificate is important for any IT professional who wants to build a long-term career.
There are many reasons for this, which are explained below:
Table of Contents
Global Usability
With a CompTIA certificate, your options are endless. The certification is independent of specific software or hardware programs. As a result, you can use it to prepare for a job in any sector of the IT industry.
In the long run, a CompTIA certificate opens doors to in-demand fields like computer networking and cybersecurity. Not to mention the CompTIA A+ certification is recognized around the world because it has ISO/ANSI accreditation.
Currently, the world is leaning more towards remote working. Many workers are not mandated to work from offices or other locations. Instead, they can work from home or other locations they find convenient.
READ ALSO: Difference Between Bitcoin And Bitcoin Cash – Which Is Safer?
With a certificate like CompTIA that companies worldwide recognize, your employment chances will transcend your locality.
Proof Of Experience
Having a CompTIA certification shows that you are up-to-date on the basics of computer systems and applications. You can apply the skills you acquire to fixing any electronic device, from PCs to mobile phones.
Most CompTIA training programs include security plus training. As a result, you can also become a cybersecurity expert who is well-informed on security technologies and policies.
Furthermore, the CompTIA A+ certification was developed and is regularly updated by IT professionals from various fields. If you have a CompTIA certification, you can boast of your IT skills being up to par with what real employers expect from their IT workers today.
Better Salary And Credit
Tech jobs are some of the best-paying jobs we have right now, and there are many of them. Every day, new positions become available. You need to meet different criteria to qualify for a job in IT, but having a CompTIA certificate increases your chances.
Many major tech companies – including Microsoft, Novell, HP, and Cisco – accept CompTIA certifications, such as the A+ and Network+, as equivalent to their own. In addition, some colleges and institutions award college credit to students who have obtained CompTIA certifications.
CompTIA certifications are often listed as criteria for entry-level jobs, and many firms and organizations have declared them necessary for certain professions. In addition, data shows that certified experts earn a higher salary than their non-certified IT professional counterparts.
READ ALSO: Benefits of CompTIA Certifications for IT Careers
Professional Community
People who think CompTIA certificates are not valuable because many people have them are mistaken. On the contrary, having a CompTIA certificate makes you a member of a massive global community of IT professionals.
CompTIA confirms that more than 2.5 million tech professionals from more than 100 countries have a certification.
Undoubtedly, you’ll feel odd if you’re the only person in your workplace who doesn’t have a CompTIA certificate. Also, you will miss out on being a part of this global professional community.
Better Work Confidence
Anyone would agree that getting a CompTIA certificate isn’t an easy feat. You need to study and prepare hard to succeed in the examinations.
Therefore, one of the most significant advantages of CompTIA certifications – especially for newcomers in the IT industry – is the boost in confidence. The certificate is not only a mark of professional distinction but also a symbol of personal success and accomplishment in your field.
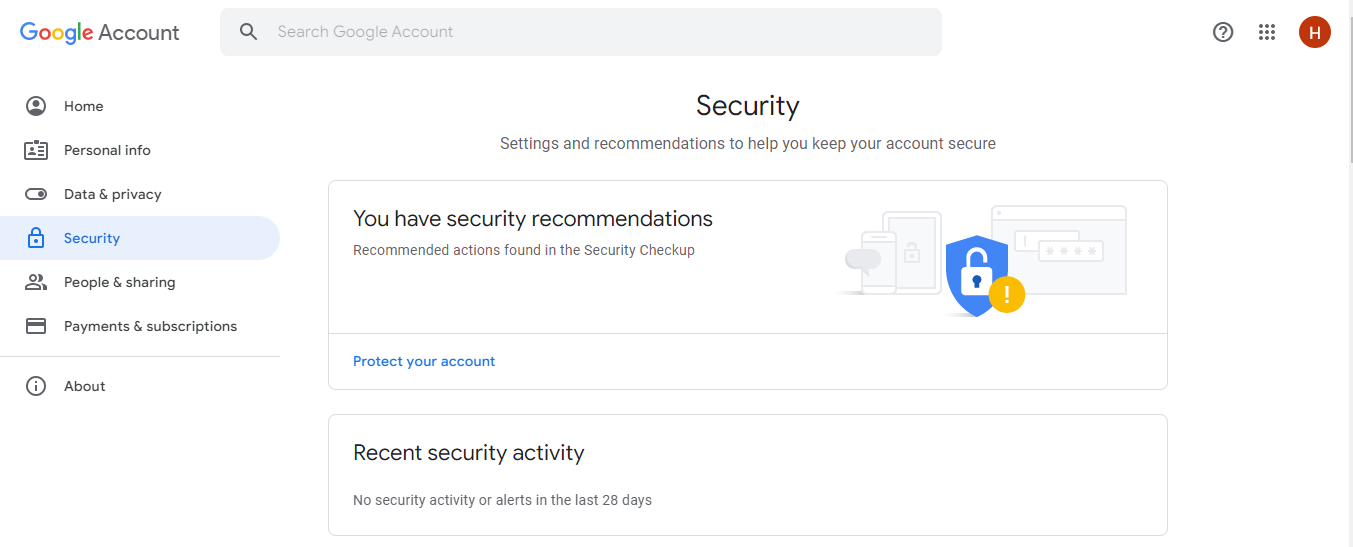
READ ALSO: 20 Online Security Tips For Remote Workers
Why Is A CompTIA Certificate Important?: 5 FAQs
CompTIA certifications are valued credentials in the IT industry. Here are some answers to frequently asked questions about their importance:
Why get a CompTIA certificate?
There are several reasons why a CompTIA certificate can be important for your IT career:
- Validation of Skills: Earning a CompTIA certification demonstrates you have the foundational knowledge and skills necessary for various IT roles.
- Career Advancement: Many IT employers look for CompTIA certifications when hiring for entry-level and some mid-level positions. A certification can give you a competitive edge in the job market.
- Increased Earning Potential: Studies have shown that IT professionals with CompTIA certifications tend to earn higher salaries compared to those without.
- Industry Recognition: CompTIA certifications are well-respected within the IT industry, showcasing your commitment to professional development.
- Stepping Stone: Earning a CompTIA certification can be a stepping stone towards more specialized IT certifications.
Which CompTIA certification is right for me?
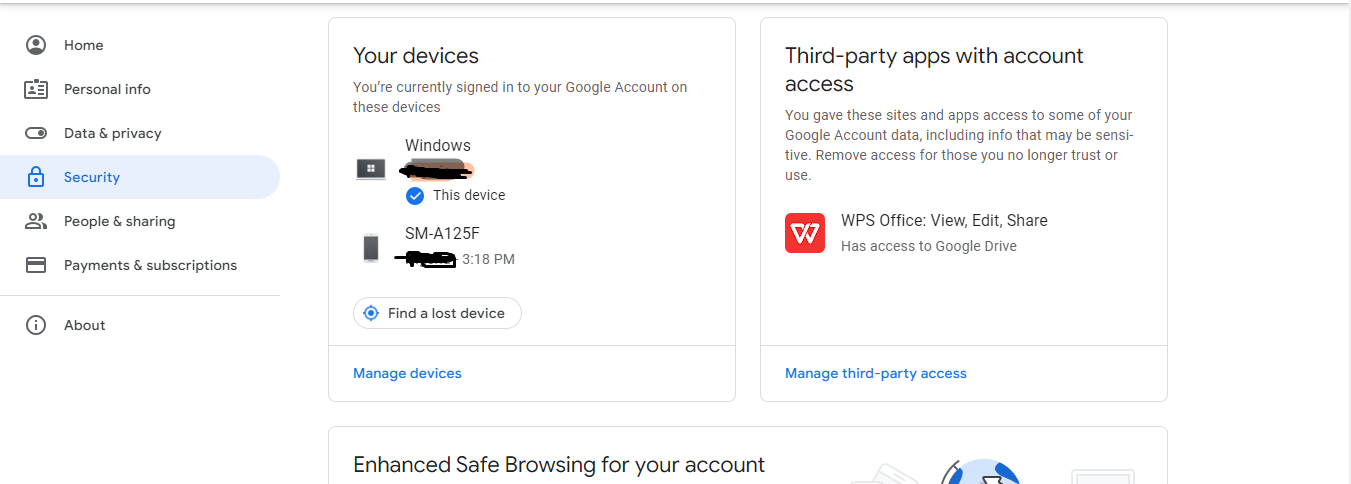
CompTIA offers a range of certifications catering to different career paths. Popular options include:
- A+: The foundation for many IT careers, focusing on core hardware and software troubleshooting skills.
- Network+: Covers essential networking concepts like network design, configuration, and troubleshooting.
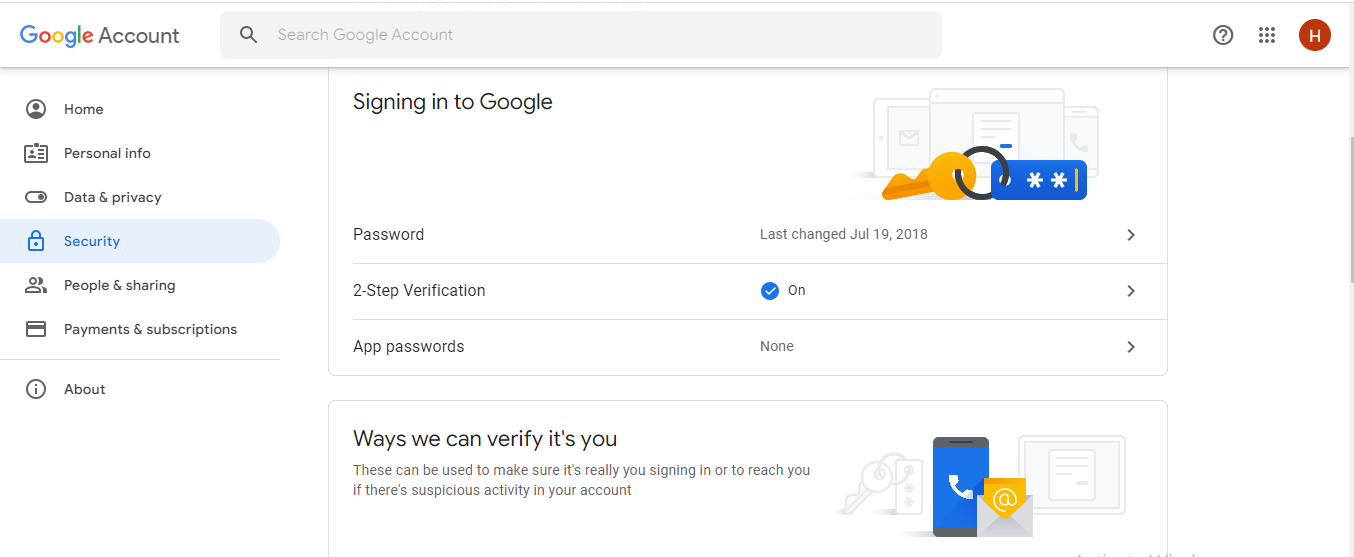
- Security+: Provides a solid understanding of cybersecurity fundamentals and best practices.
READ ALSO: How To Prepare Your Business For Data Loss
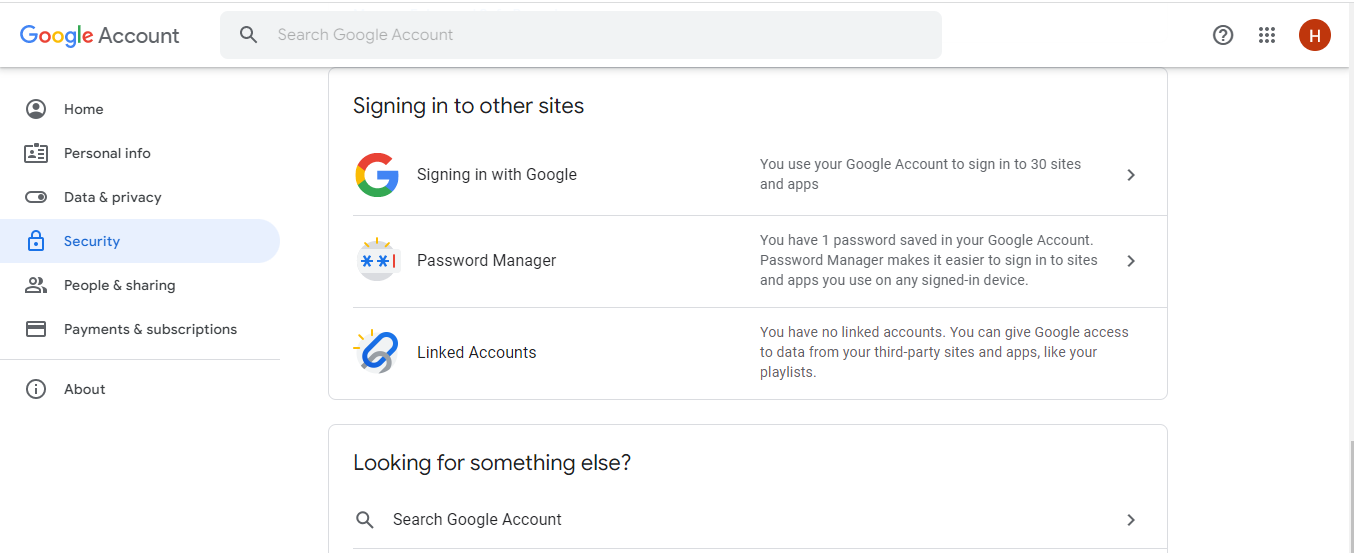
How can I prepare for a CompTIA exam?
There are various resources available to help you prepare for a CompTIA exam:
- CompTIA Official Study Guides: These guides are developed by CompTIA and offer comprehensive exam coverage.
- Online Courses and Training: Many online platforms offer video lectures, practice tests, and other resources.
- Bootcamps: Intensive training programs designed to get you exam-ready in a short period.
How much does a CompTIA certification cost?
The cost of a CompTIA certification exam varies depending on the specific exam. Generally, they range from $200 to $400 USD per exam.
Do CompTIA certifications expire?
Yes, most CompTIA certifications have a three-year validity period. To maintain your certification, you need to retest or pursue continuing education options offered by CompTIA.
Earning a CompTIA certification is an investment in your IT career. By demonstrating your foundational knowledge and commitment to professional development, you can increase your job prospects and earning potential.
Bottom Line
You can’t go wrong with a CompTIA certificate if you’re looking to break into the IT industry. This certification will get your foot in the door and put you on the right track.
Having a CompTIA certificate makes you part of a supportive professional network where members may share knowledge and expertise and receive and offer assistance to others.
Finally, you have to renew your CompTIA certificate from time to time. Hence, it’s a continuous track. Staying on this track shows dedication to your profession and an interest in staying current with changes in the IT field.
INTERESTING POSTS
- Macropay Scam Alert: Fake E-Commerce Sites
- What is Magento? Everything You Need To Know
- How A PDF Can Contain Malware
- 6 Ways To Optimize Your DevOps Team Productivity
- Ways Manufacturers Can Benefit from Going Online
- How To Start A Cybersecurity Company
- What Is An SSL Certificate?[MUST READ]
- The Best Kubernetes Certification Program
- What Is A Certificate Authority (CA) And What Do They Do?
- Why SSL Certificate Is An Essential Cybersecurity Tool?