I will show you everything you need to know about session hijacking here.
When a visitor lands on a site, the first thing between the user and the site is the creation of a session. The website authenticates the user, and the session is created. Sessions are an essential part of communication between two parties.
Session IDs are usually stored in the form of cookies. If the hackers can obtain these cookies, they can hijack the user’s session and use the session ID on that website to cause significant damage without being detected.
Table of Contents
What Is Session Hijacking?
Session hijacking occurs when a scammer steals session information from HTTP cookies, URLs, page headers, or active session bodies.
In this way, the attacker steals the web user’s session, pretending to be the real user and gaining access to all the privileges the user has on the network.
During a single connection, the series of interactions between two communicating parties is referred to as a session. When you log into an application, a session is generated on the web server to manage subsequent requests from the same user, facilitating current interactions.
Sessions are used by these applications to keep the client’s appropriate information. For the time the user stays active on a network, the session remains alive.
The session is destroyed once the user has logged out or has not performed any activity for a specified period. A session ID consists of a long, random mixture of letters and numbers.
These are preserved in cookies, web pages, and other digital media. The intruder typically attacks the session cookie, a type of cookie hijacking.
READ ALSO: Surfshark Alternative ID Review 2024
How Does Session Hijacking Work?
Session hijacking is almost similar to plane hijacking. In an airplane hijacking, the attackers launch a systematic attack on the plane and take control of it. The same happens in session hijacking.
There are different ways of session hijacking, as mentioned below:
- Session Sniffing
- Cross-site Scripting (XSS)
- Session Fixation
- Man in the Browser
- Predictable Session ID
1. Session Sniffing
When the communication between the user and the webserver is insecure, and the session ID is being sent in unencrypted form, the intruder can take advantage of this and steal the session ID that they can use for malicious.
Hackers can use tools like Wireshark and OWASP Zed to monitor information flow containing session IDs between the client and the server. Once they get the session ID, they can access it without authorization.
READ ALSO: Best Proxies for Scrapebox: Enhancing Your Web Scraping Efforts
2. Cross-site Scripting (XSS)
Cross-site scripting is one of the most dangerous techniques used for session hijacking. The attacker adds malicious code to a real website or application to inject the user’s web browser with malicious scripts.
When the user visits the site or opens the application, they are attacked by scammers. The malicious code can be in the form of messages, forums, links, etc., on a legitimate server.
READ ALSO: How To Secure PHP Web Apps And Prevent Attacks
3. Session Fixation
To deceive the users, the hackers may send them a known session ID. It can be done by sending a link via email.
Users are directed to a legal login form when clicking the link. The user confirms the connection and becomes a victim of session hijacking by the scammers’ session key.
4. Man in the Browser
A man-in-the-browser attack infects the users’ computers with a Trojan (a virus often assumed to be genuine software). The attacker hijacks the session when the user installs the software and visits a target site.
The user in the browser can perform any transaction that the man can do. They can make new transactions, but the web server cannot identify the invalid access because it comes from the user’s computer.
5. Predictable Session ID
Many websites use easy algorithms to create a session ID. If the hacker monitors various session IDs, he may be able to predict valid ones.
READ ALSO: What Is An SSL Certificate?[MUST READ]
Protection Against Session Hijacking
Here are the tips that are used to prevent session hijacking:
1. Install an SSL Certificate
Data transmission happens between the user and the server during a session. If the website does not have an SSL certificate, the information is not secure, and hackers can easily read it. Therefore, the attacker can compromise the login information shared through this insecure connection.
If you install an SSL (Secure Sockets Layer) on your website, the data transmission is encrypted and beyond scammers’ reach. Even if someone gains access to the encrypted data being exchanged, they will be unable to read and understand it, as they cannot decrypt the information.
You can buy an SSL certificate from any popular SSL certificate provider like Comodo, DigiCert, Symantec, GeoTrust, etc. However, you should consider buying an SSL certificate if your site has a single domain and multiple subdomains.
2. Security Plugins
Installing security plugins can help protect you from hacking. Whenever a hacker sends malware or spiteful code to your site, the plugin’s firewall will alert you about this activity, and you can block it before falling prey to it.
3. Update and Harden your Website
Keep updating your website whenever a new update is available. If you are running outdated server software, the hacker may exploit any vulnerabilities in it and cause harm to you. You should use strong usernames and passwords, block PHP execution, and take other security measures to harden your website.
How Can Users Safeguard Themselves from Cookie Stealing?
As a user, you must take the security precautions that are mentioned below while visiting a website:
1. Antivirus Installation
You should install antivirus software on your computer. This software monitors all downloads from the internet and transfers through flash drives. When you visit a suspicious website, it informs you of the alarming content present on that site.
2. Avoid Clicking Suspicious Links
Hackers can send you links through emails or comment sections on websites. Do not click on untrusted links, especially those that promise prizes and rewards.
3. Do not Store Sensitive Information
It is a convenient way to save your browser passwords and automatically log in to websites. Likewise, you can save your credit card/banking details on shopping websites for faster checkouts.
It will surely save you time, but it can also put you in danger. There is a huge risk of your data being stolen. So, it is strongly recommended that you not save your sensitive information in your browser.
4. Clear Cookies
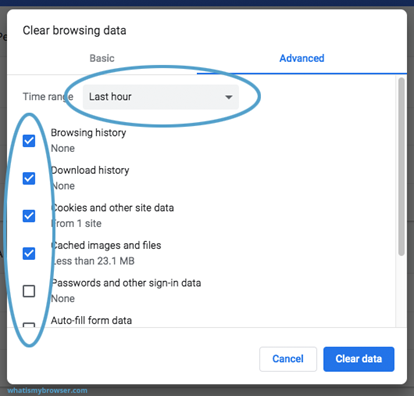
If you are using Google Chrome, go to history, select “Clear browsing history,” and tick the checkbox “Clear cookies and other site data.”
Select the time range of your choice and click ‘clear data’; all the cookies in the selected period will be removed. This will remove any sensitive information stored on the browser.
Rounding Up
Managing an online business is a challenging task. You need to manage hundreds of tasks while running an online business.
It is best to take all necessary security precautions to protect your website, business, clients, and customers from potential attacks. You cannot ignore the security aspects, as it will ruin your business.
As an internet user, you need to protect your site/computer from session hijacking risks while being online. Do not forget the important tips mentioned above to stay safe while browsing.
RELATED POSTS
- 6 Best Secure Web Hosting for Web Designers
- 9 Proven Cybersecurity Tips For Startups
- Is WikiLeaks Still Active? [We Have The Answer]
- How To Overcome Remote Work Security Threats
- Browser Hijacking: Signs And The Easiest Way To Remove It
- 11 Most Common WordPress Attacks [MUST READ]
About the Author:
Gina Lynch is a VPN expert and online privacy advocate who stands for the right to online freedom. She is highly knowledgeable in the field of cybersecurity, with years of experience in researching and writing about the topic. Gina is a strong advocate of digital privacy and strives to educate the public on the importance of keeping their data secure and private. She has become a trusted expert in the field and continues to share her knowledge and advice to help others protect their online identities.
Daniel Segun is the Founder and CEO of SecureBlitz Cybersecurity Media, with a background in Computer Science and Digital Marketing. When not writing, he's probably busy designing graphics or developing websites.












I have questions
Feel free to ask…