For many people, the differences between residential and datacenter proxies might seem unclear, and that’s understandable. They have many similarities, but they also have key differences that separate them and make them unique.
In this article, you will learn about the 4 key differences between residential proxies and datacenter proxies.
CHECK OUT: Top Proxy Service Providers in 2024: Unlocking Internet Freedom
Without further ado, let’s get started.
Table of Contents
What Are Residential and Datacenter Proxies?
As you probably know, there are two main types of proxies: residential and datacenter proxies. But, before learning about their differences, you should first learn them individually.
Residential proxies are one of the most common types of proxies on the market, and they are often offered by your Internet Service Provider (ISP), or residential proxies can also obtain through a third party depending on which proxy server provider you choose; they might also offer free residential proxies.
They enable you to select a location (country, city, and cell carrier) to access the internet. Essentially, they operate as a buffer between your actual IP address and the website you’re visiting by giving you unique mobile and desktop IPs.
Physical data centers around the world provide datacenter proxies. They frequently have greater technology, are more stable, and are less expensive. They do, however, have drawbacks.
For starters, datacenter proxies have a limited number of locations, making it difficult to hide your true IP address without being banned, which leads to the second point: datacenter proxies perform poorer when compared to residential proxies who have thousands of unique mobile and desktop IPs.
This is because datacenter proxies have such a restricted number of locations; this leads to them not having the capacity to act like real people.
Best Proxy Services
What’s The Difference?
Now that you know what residential and datacenter proxies are, it’s time to learn the differences and determine which is better for you.
1. Speed and Stability
Datacenter proxies have superior speed compared to residential proxies. This is because datacenter proxies are located in physical data centers worldwide, and these data centers often have a better internet connection and better technology.
This makes datacenter proxies better for people prioritizing speed over anything else. This means that if you’re using one of the best datacenter proxies, you are guaranteed ultrasonic speed for your web surfing. And as mentioned, data centers also have better technology, which makes them a much more stable choice compared to residential proxies.
2. Price
If you’re tight on budget and looking to buy in bulk. Datacenter proxies are the way to go since they are much easier to get in terms of pricing availability. And if you get them from a good provider, you’ll experience good security, stability, and speed.
On the other hand, residential proxies are much more expensive because you usually have to go through an ISP, and the IP is unique only to you and your device.
3. Locations and Performance
One of the biggest concerns when you’re looking to buy a proxy server, is the number of locations you’ll have and the performance of the IP address. These two components are the bread and butter of proxies.
Residential proxies have better locations and performance than datacenter proxies, and the reason is simple; datacenter proxies can’t act like humans. Because data centers are so limited around the world, the number of IP addresses you’ll have is also limited, which means restricted websites will recognize your IP address more often, leading to poorer performance.
However, with residential proxies, you get to experience a unique IP address for each device, making it impossible to have poor performance.
4. Ease of Use
If you’re just starting or have little to no experience with technology. Residential proxies might be your best option.
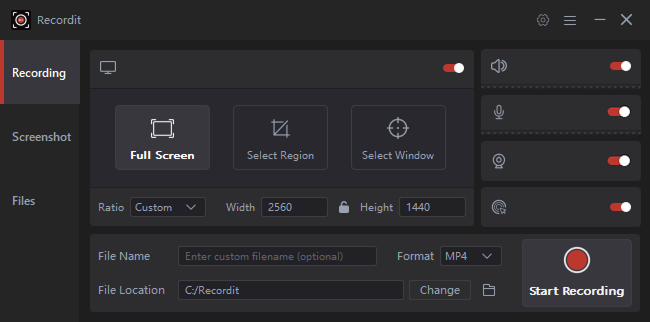
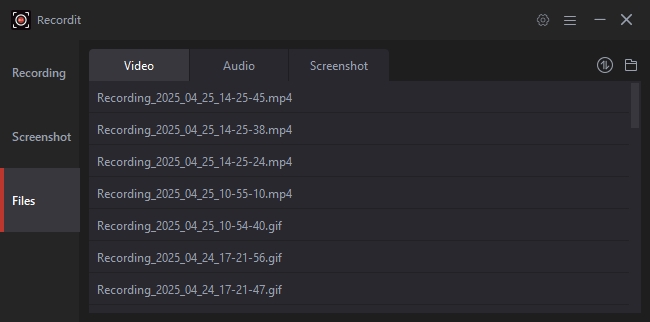
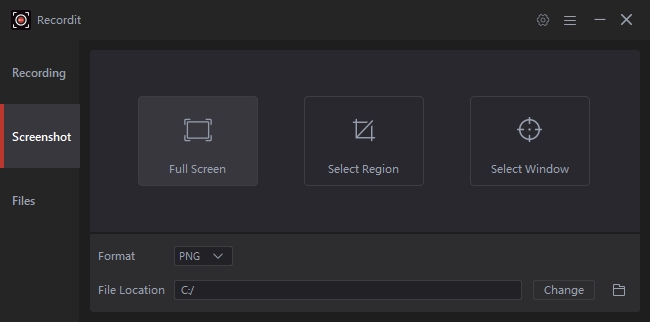
Since ISPs or third-party companies usually provide residential proxies, they put more effort into providing you with the best experience possible. And one of the ways they do that is through an easy-to-follow user interface.
This is usually done by giving you software to control your proxy servers, location, speed, bandwidth, etc. This is great news for beginners just starting to realize the power of proxy servers and those without much technology experience.
READ ALSO:
- The Best ISP Proxies
- The Best Antivirus Software
- The Best VPN Services
- The Best Datacenter Proxies
- The Advantages Of Mobile Proxies
Frequently Asked Questions (FAQs) About Residential and Datacenter Proxies
Which proxy is better: residential or datacenter?
It depends on your needs. Residential proxies are ideal for tasks requiring high anonymity (web scraping, social media management), while datacenter proxies are better suited for speed-critical tasks (data downloads, streaming content).
Are residential proxies legal?
Using residential proxies is generally legal, but it’s crucial to comply with the terms of service the proxy vendor provides and avoid any illegal activities.
Can I use free proxies?
Free proxies can be risky. They might be unreliable, slow, or even infect your device. Opting for reputable paid proxy services is recommended.
How do I know which proxy provider to choose?
Before choosing a provider, consider factors like proxy type (residential or datacenter), server locations, speed, pricing, and features (like static IPs or bandwidth caps).
READ ALSO: Best Residential Proxies In 2024: A Comprehensive Guide
What are some common uses for proxies?
Proxies can be used for web scraping, data collection, bypassing geo-restrictions, social media management, and enhancing online privacy.
Is a VPN a replacement for a proxy?
VPNs (Virtual Private Networks) encrypt your entire internet traffic, while proxies only route specific traffic through the proxy server. VPNs offer broader privacy protection, but proxies can be more targeted for specific tasks.
Conclusion
In conclusion, you now know what residential and datacenter proxies are and what the differences between the two are.
By understanding these core differences and FAQs, you can make an informed decision when choosing between residential and datacenter proxies to fulfill your specific online needs.
INTERESTING POSTS
- Exclusive Interview With Vladimir Fomenko, Founder Infatica
- Proxy Optimization: 4 Things You Didn’t Know A Proxy Could Do
- What Are The VPN Features And Benefits?
- How To Rent A Cheap Car In Various Countries
- Google Chromecast Vs Amazon FireStick – Which Is Better?
- Full Review of VyprVPN VPN Service Provider
- Best Mobile Proxies: Unlocking Faster and More Secure Mobile Browsing