Here, I will talk about student cybersecurity. Additionally, I will share four simple safety tips.
In the modern world, cybersecurity has become a crucial aspect of everyday life. Students, in particular, need to be aware of the potential risks they face online and how to protect themselves. Term paper help is often sought online, and in the process, sensitive data can be exposed if not adequately protected.
This article offers five straightforward tips for students to protect their online activities.
5 Simple Tips For Students Safety
1. Creating Strong and Unique Passwords
One of the most basic yet effective ways to protect online accounts is to create strong and unique passwords. A robust password acts as a first line of defense against potential hackers and cybercriminals.
It’s surprising how many people still use easily guessable passwords, such as “123456” or “password”. These are easy targets for hackers who use automated software to guess thousands of passwords per second.
Creating a strong and unique password involves using a combination of uppercase and lowercase letters, numbers, and special characters.
The longer the password, the harder it is for hackers to crack. It’s also important to avoid using personal information such as birthdays or names that can be easily guessed or found online.
However, creating and remembering strong and unique passwords for each account can be challenging. This is where password managers come in handy.
Password managers generate and securely store complex passwords, relieving the burden of remembering each one. They also offer additional security features, such as two-factor authentication, that provide an extra layer of protection.
READ ALSO: Ultimate Digital Privacy Guide: Protect Your Data Today
2. Recognizing Phishing Attempts
Phishing is a common cyber attack where hackers impersonate a trustworthy entity to trick individuals into revealing sensitive information, such as usernames, passwords, and credit card numbers.
Students often fall victim to phishing scams as they may not be fully aware of the signs to look out for.
Phishing attempts typically take the form of deceptive emails, messages, or websites. They often create a sense of urgency, pushing the recipient to react quickly without thinking. For example, an email claiming to be from the university administration may request that the student confirm their login credentials due to a suspected security breach.
To combat phishing, students need to be skeptical of unexpected or suspicious emails or messages. They should avoid clicking on links or downloading attachments from unknown sources.
Instead, they can verify the information by contacting the supposed sender directly through a verified means of communication.
If a message seems suspicious, it probably is. Students should trust their instincts and take the time to verify any request for personal information. It’s better to err on the side of caution than to risk falling victim to a phishing scam.
READ ALSO: The Power of Student Networks: How to Leverage University Connections for Your Startup
3. Protecting Your Personal Data Online
The internet is a treasure trove of information, but it can also be a minefield when it comes to protecting personal data. Every time students use the internet for term paper help or to access online resources, they expose their personal information to potential threats.
One of the most effective ways to protect personal data online is to limit the amount of information shared on social media and other online platforms.
Students should adjust their privacy settings to control who can see their posts and personal information. They should also be mindful of the information they share in online forms and surveys.
Another crucial step in protecting personal data is to use a secure and private internet connection. Public Wi-Fi networks are often unsecured, making it easy for hackers to intercept data.
If students must use public Wi-Fi, they should use a Virtual Private Network (VPN) to encrypt their online activities.
Lastly, students should regularly update their devices and applications. Updates often include security patches that fix vulnerabilities that hackers could exploit. Delaying updates could leave devices vulnerable to attacks.
READ ALSO: 20 Essential Cybersecurity Tips For Students
4. Be Cautious About Public Wi-Fi
While tempting for a quick online fix, public Wi-Fi networks are breeding grounds for hackers. Their lack of security leaves your data exposed, making them unsuitable for accessing:
- Financial accounts: Banking, online payments, or any transactions involving your credit card are strictly off-limits.
- Personal Information: Don’t log in to accounts with sensitive details, such as social security numbers or health records.
- Private communications: Avoid sending confidential emails or messages on insecure networks.
For situations where public Wi-Fi is your only option, consider using a Virtual Private Network (VPN).
A VPN creates a secure tunnel, encrypting your data and making it unreadable to prying eyes. Think of the best VPN services as a protective shield for your online activities.
5. Be Aware of Online Scams
Scammers are clever! They often target students with tempting offers of quick money, scholarships, or exclusive deals that sound too good to be true. Don’t let them fool you!
Here’s how to stay safe:
- Always be skeptical: If something seems too good to be true, it probably is. Don’t let the promise of fast results cloud your judgment.
- Do your research: Before committing to anything, take the time to thoroughly investigate the offer. Verify the company’s legitimacy by checking its reputation, reading reviews, and confirming the information through trusted sources.
- Never share personal or financial information: Scammers often attempt to extract sensitive information, such as passwords, credit card numbers, or Social Security numbers. Unless you’re 100% sure the website or organization is legitimate, never share personal details online.
- Look for red flags: Be wary of urgency tactics, pressure to act quickly, or offers that require upfront payments. These are often hallmarks of scams.
- Trust your gut: If something feels suspicious, it probably is. Don’t be afraid to walk away from an offer that makes you uncomfortable.
- Talk to someone you trust: If you’re unsure about an offer, discuss it with a trusted adult, such as a parent, guardian, teacher, or counselor. They can help you assess the situation and make informed decisions.
Cybersecurity Tools Every Student Should Know About
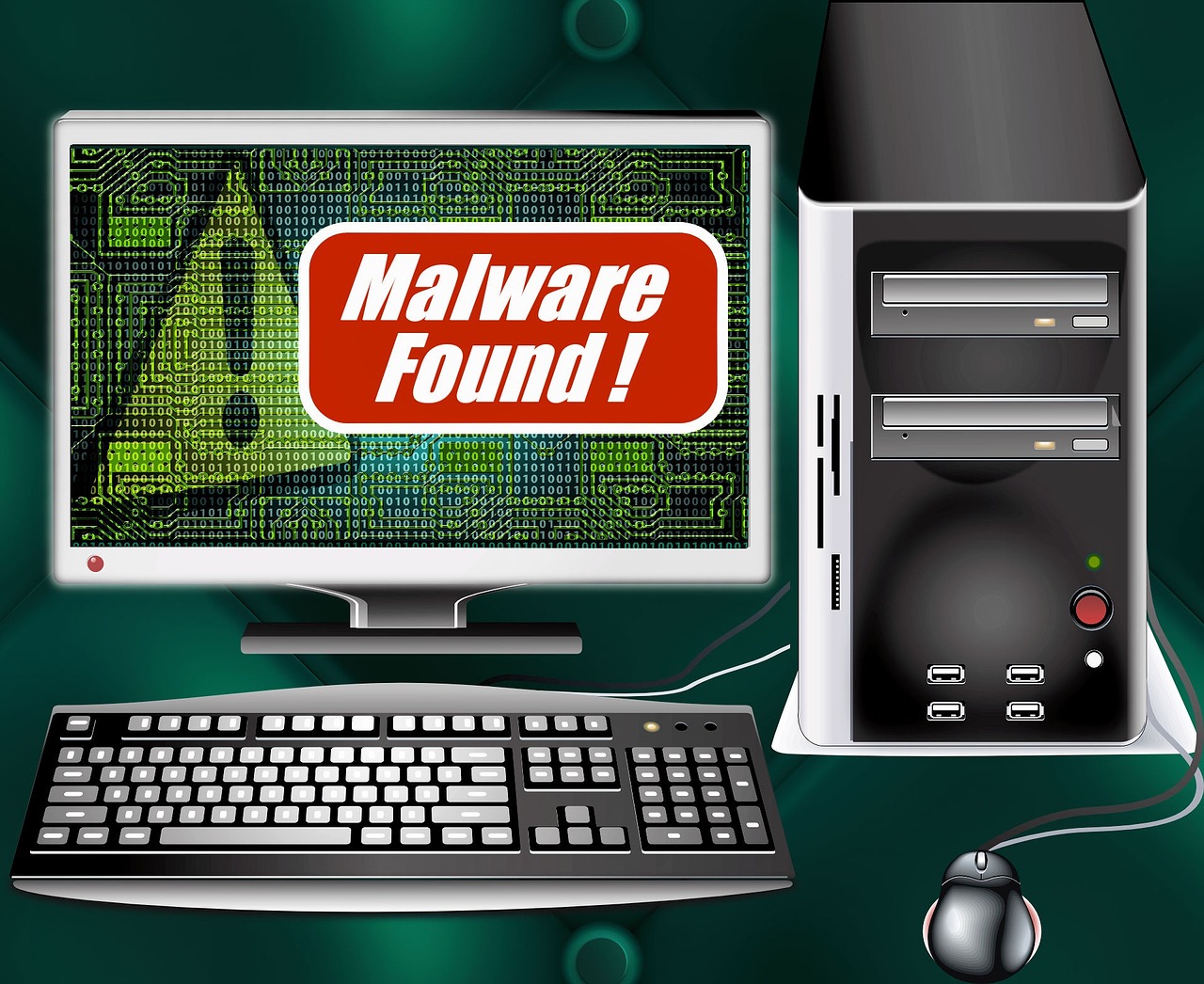
While good online habits form the foundation of cybersecurity, several tools are available to enhance protection. These tools can help students protect their devices and data from cyber threats.
Antivirus software is a must-have for every student. It provides real-time protection against malware, ransomware, and other types of cyber attacks. Students should ensure that their antivirus software is always up to date to protect against the latest threats.
As mentioned earlier, a password manager is an invaluable tool for managing and protecting passwords. It not only helps generate strong passwords but also stores them securely. Most password managers also alert users about weak or duplicated passwords.
A VPN is another essential tool for online security. It encrypts internet traffic, making it unreadable to anyone who might intercept it. This is especially useful when using public Wi-Fi networks.
Finally, students should consider using a secure browser that prioritizes privacy and security. These browsers often include features like tracking protection and automatic HTTPS redirection, which ensures a secure connection to websites.
Conclusion
In conclusion, student cybersecurity is a topic that should not be taken lightly. With an increasing amount of study resources and term paper help available online, students need to take proactive measures to ensure their online safety.
By creating strong passwords, recognizing phishing attempts, protecting personal data, and utilizing cybersecurity tools, they can significantly reduce their risk of falling victim to cyber threats.
Remember, cybersecurity is not a one-time task, but a continuous process of staying vigilant and adapting to ever-evolving threats.
INTERESTING POSTS
- The Must Dos And Don’ts For Protecting Your Password And Personal Data
- How To Detect Email Phishing Attempts (Like A Geek!)
- Great Tools To Help Protect Yourself And Your Devices
- The Intersection of Cybersecurity and AI: Exploring Challenges and Opportunities in Student Writings
- Most Helpful Apps For Students
- Top 10 Cybersecurity Tips For Students
- Cybersecurity Tips for Students Studying Online