Discover how to protect your business from cyberattacks in this article…
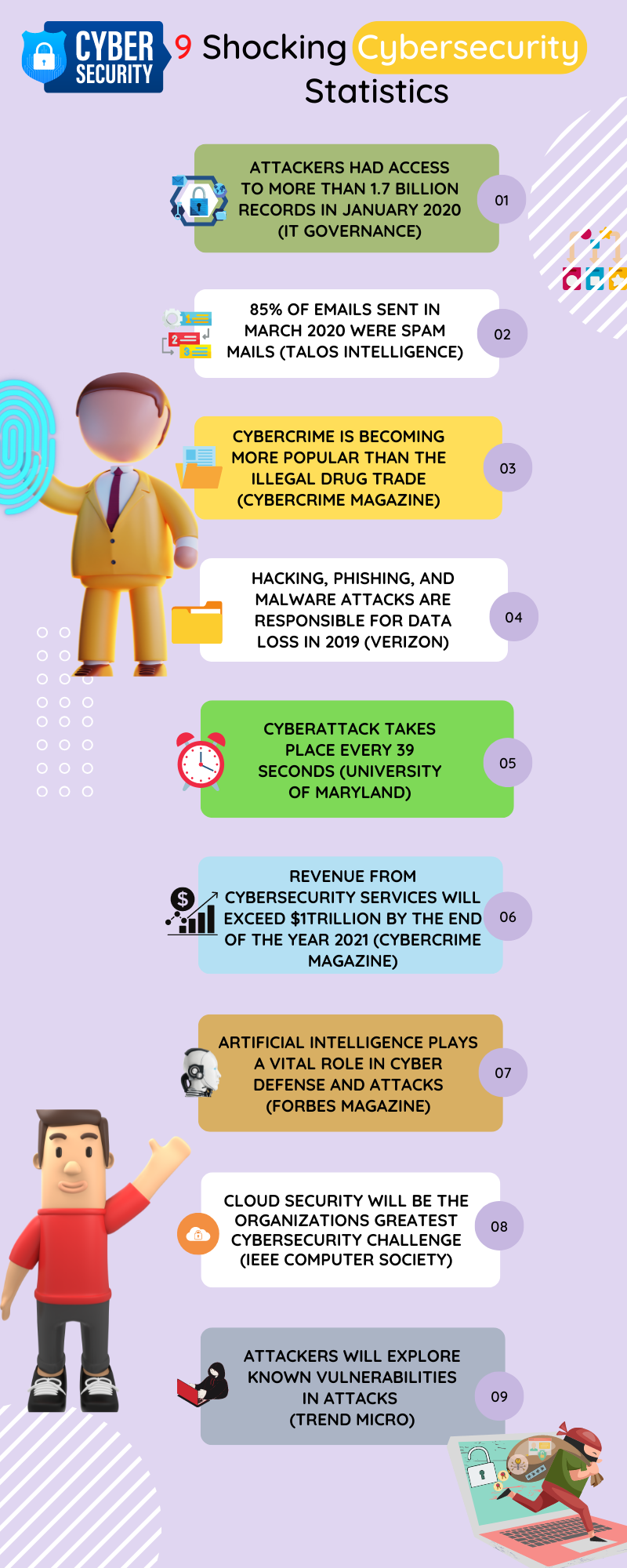
In today’s digital landscape, protecting your business from cyberattacks is paramount. Cybercriminals are constantly evolving their tactics, targeting companies of all sizes.
As a business owner, it is essential to prioritize cybersecurity measures to safeguard your company’s sensitive data, reputation, and customer trust.
This comprehensive guide will explore expert tips and strategies to protect your business from cyber threats.
TOP DEALS
1. Understanding the Importance of Cybersecurity
Cybersecurity should be a top priority for businesses of all sizes. Many small businesses assume they are not at risk, but studies show they are increasingly becoming targets of cyberattacks.
Recognizing that cyber threats can have severe consequences, including financial loss, reputational damage, and legal implications, is crucial. By understanding the importance of cybersecurity, you can take proactive steps to protect your business.
2. Educating Your Employees on Cyber Threats
Your employees play a critical role in maintaining the security of your business. It is essential to educate them on cyber threats and provide training on best cybersecurity practices.
This includes recognizing phishing emails, using strong passwords, and avoiding suspicious websites. By fostering a culture of cybersecurity awareness, you can significantly reduce the risk of a successful cyber attack.
3. Implementing Robust Network Security Measures
Securing your business network is paramount to protecting against cyber threats. Start by implementing firewalls to monitor and control incoming and outgoing network traffic.
Additionally, consider using intrusion detection systems (IDS) and intrusion prevention systems (IPS) to identify and block potential threats. Regularly update and patch network devices, routers, and switches to address known vulnerabilities.
4. Strengthening Password and Access Controls
Weak passwords are one of the leading causes of successful cyberattacks. Encourage employees to use strong, unique passwords for all accounts and systems.
Implement multi-factor authentication (MFA) to add an extra layer of security. Limit administrative access to critical systems and regularly review user access privileges to ensure they align with job responsibilities.
5. Regularly Updating Software and Security Patches
Outdated software can create security vulnerabilities that cybercriminals can exploit. Regularly update and patch all software, including operating systems, web browsers, and applications.
Enable automatic updates whenever possible to ensure the timely installation of security patches. By keeping your software up to date, you can mitigate the risk of known vulnerabilities being exploited.
READ ALSO: AI in Breach Detection Threat or Safeguard (or Both)
6. Embracing Encryption and Secure Data Storage
Encrypting sensitive data is essential to protect it from unauthorized access. Utilize encryption tools and technologies to secure data in transit and at rest.
Consider storing sensitive data in secure, encrypted databases or utilizing cloud storage services with robust encryption protocols. Implement access controls to limit data exposure to authorized individuals only.
7. Employing Multi-factor Authentication
Multi-factor authentication (MFA) adds an extra layer of security by requiring users to provide multiple forms of identification to access systems or data.
This could include a combination of passwords, biometrics, smart cards, or mobile device authentication. Implementing MFA significantly reduces the risk of unauthorized access, even if passwords are compromised.
8. Conducting Regular Security Audits and Risk Assessments
Regularly assessing your cybersecurity posture is crucial to identify vulnerabilities and areas for improvement. Conduct comprehensive security audits to evaluate your network infrastructure, systems, and policies.
Perform risk assessments to identify potential threats and assess their impact on your business. Use the findings to develop and implement a robust cybersecurity strategy.
9. Establishing Incident Response and Recovery Plans
No organization is immune to cyberattacks, and having an incident response plan is essential for minimizing damage and facilitating a swift recovery. Establish a clear protocol for reporting and responding to security incidents.
Define roles and responsibilities, establish communication channels, and regularly test the effectiveness of your response plan through simulated exercises. Implement backup and recovery strategies to ensure business continuity in the event of a cyber incident.
10. Investing in Cybersecurity Insurance
Cybersecurity insurance can provide an added layer of protection for your business. It helps cover financial losses, legal expenses, and recovery costs in a cyberattack or data breach.
Work with insurance providers specializing in cybersecurity to assess your risks and determine the appropriate coverage for your business. Review and update your policy regularly to meet evolving threats and business needs.
Use Cybersecurity Tools To Protect Your Business
HOT CYBERSECURITY DEALS
In addition to the strategies mentioned above, leveraging cybersecurity tools can significantly enhance your business’s protection against cyber threats.
Utilize advanced antivirus and anti-malware software to detect and mitigate potential threats.
Implement real-time network monitoring and intrusion detection systems to identify suspicious activities.
Consider utilizing threat intelligence platforms to stay updated on emerging threats and vulnerabilities. Regularly review and upgrade your cybersecurity tools to stay ahead of evolving threats.
Conclusion
Protecting your business from cyberattacks requires a comprehensive and proactive approach. By understanding the importance of cybersecurity, educating your employees, implementing robust security measures, and investing in insurance, you can significantly reduce the risk of falling victim to cyber threats.
Stay vigilant, regularly update your security practices, and adapt to emerging threats to ensure your business’s long-term security and resilience.
Now, you should know how to safeguard your business from cyberattacks. Remember, cybersecurity is an ongoing process that requires continuous monitoring, adaptation, and improvement to stay ahead of cybercriminals.
You can effectively safeguard your business from cyberattacks by prioritizing cybersecurity and staying informed about the latest trends and best practices.
INTERESTING POSTS
- Identity Theft: How To Safeguard Your Personal Information
- Great Tools To Help Protect Yourself And Your Devices
- Can VPNs Help Prevent Cyberattacks? [We Have The Answer]
- How To Secure Your Business In The Times Of All-pervasive Hackers
- Hot Black Friday Deals 2023 [Exciting Offers]
- 4 Cybersecurity Best Practices To Prevent Cyber Attacks
- Is Carbonite Safe To Use? [Unbiased ANSWER]
- How To Safeguard Your Business From Cyberattacks
- How to Safely Remove Viruses from Your Computer: A Comprehensive Guide
- StatesCard Review: Is This Card Worth Your Wallet?
- VeePN Review: The Ultimate VPN Solution for Security and Privacy














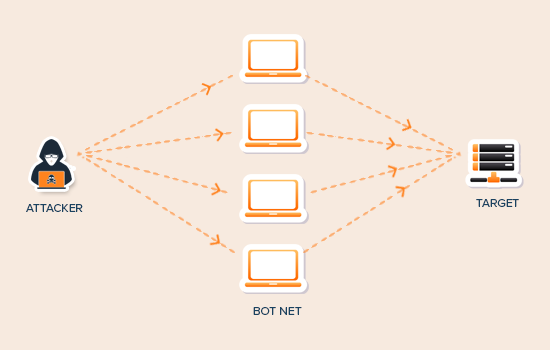
 Furthermore, this program differs slightly from other forms of malware in that it causes little to no harm to the host computer or its inherent files.
Furthermore, this program differs slightly from other forms of malware in that it causes little to no harm to the host computer or its inherent files.


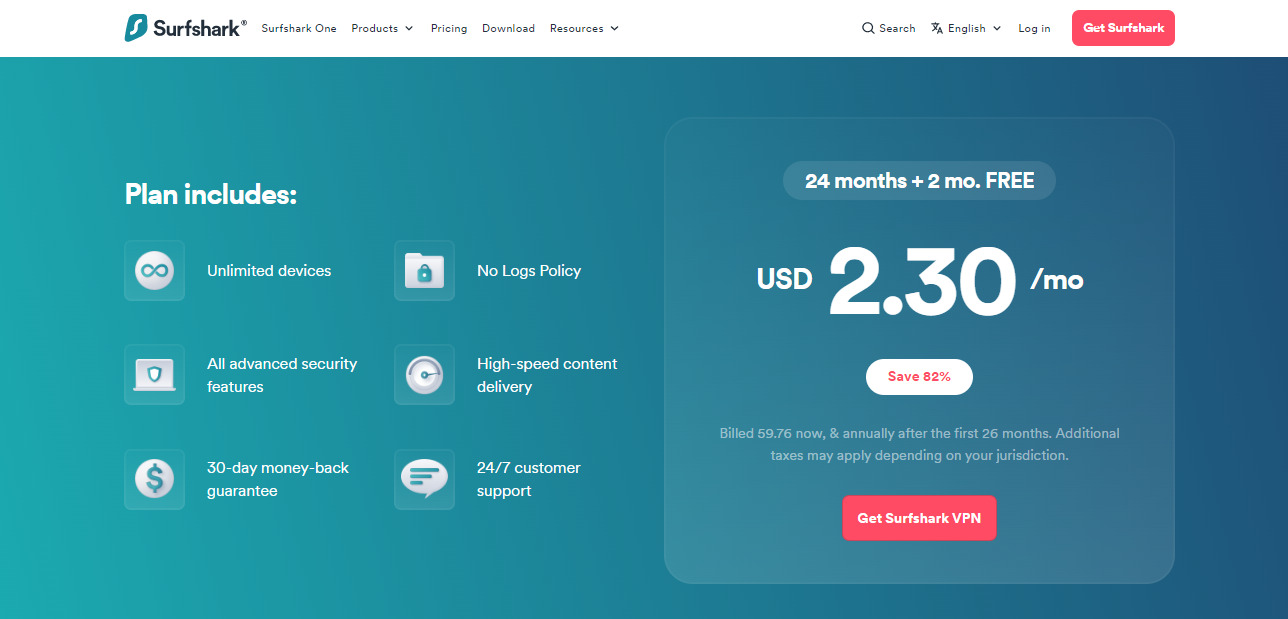
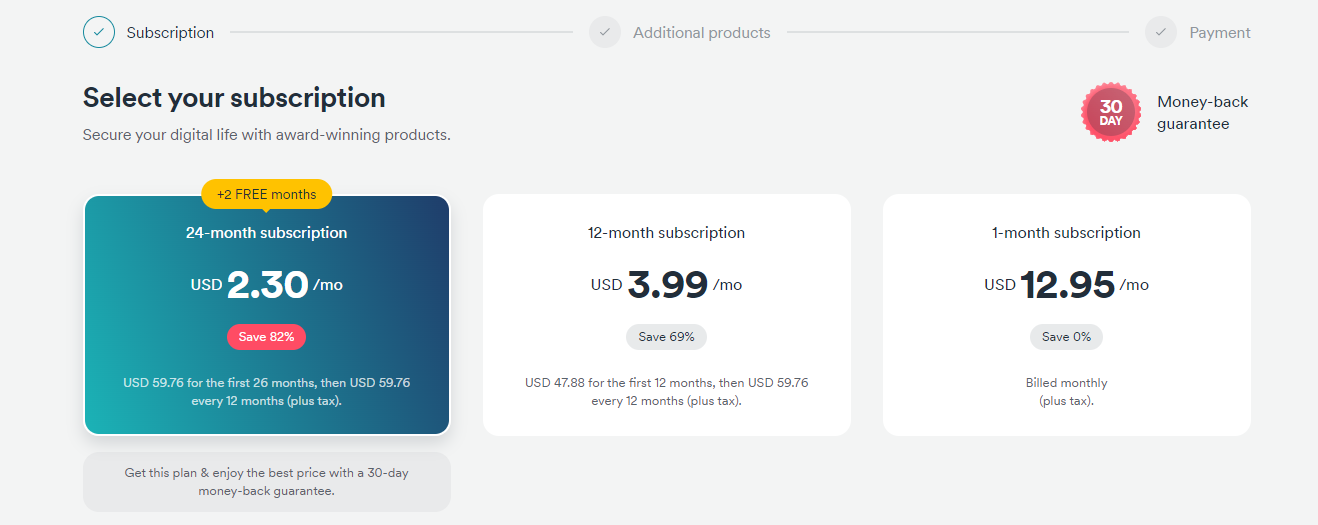
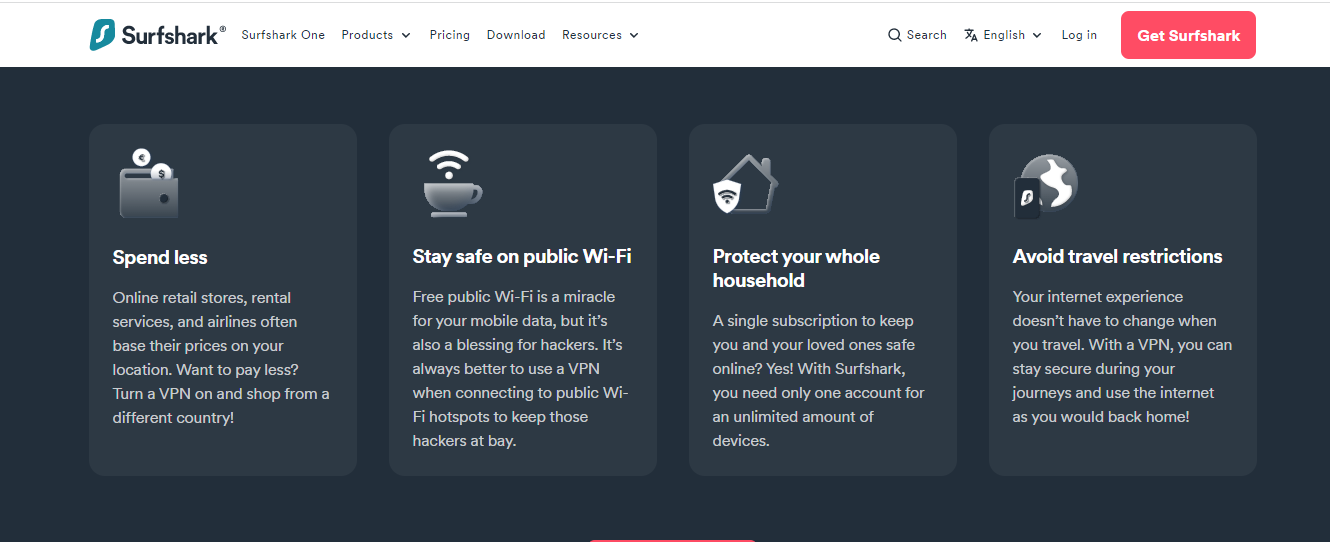 Surfshark works by re-routing incoming and outgoing data pathways from your device through a secure virtual encryption tunnel to any of its secure VPN servers in any country of your choice.
Surfshark works by re-routing incoming and outgoing data pathways from your device through a secure virtual encryption tunnel to any of its secure VPN servers in any country of your choice.