In this post, I will show you the top 7 field service mobile apps.
Most field service teams don’t fail because of technicians. They fall apart due to poor coordination, a job update that never made it back to the dispatcher, a customer who called three times to ask where the crew was, and a schedule that made sense on Monday but collapsed by Wednesday noon.
For a while, spreadsheets and phone calls hold things together. Then job volume increases, and the whole system becomes a liability. Managers lose visibility. Dispatchers chase updates. Technicians arrive unprepared.
That’s the exact gap that field service mobile apps were built to close. It shows up across trades, HVAC companies losing track of technicians mid-route, plumbing crews showing up without job details, roofing and solar teams where the schedule falls apart the moment one job runs over. Cleaning services, electrical contractors, and field repair teams all run into the same wall eventually.
These platforms put scheduling, job tracking, and customer communication in one place, accessible from the office and from the back of a work truck. This guide breaks down seven of the most-discussed field service mobile apps: Arrivy, Jobber, ServiceTitan, FleetSharp, Connecteam, Service Fusion, and Fieldwire.
Quick Summary- Field service mobile apps handle the daily chaos of scheduling, dispatching, job tracking, and crew communication from a phone.
- Both dispatchers in the office and technicians on the road get real-time visibility into what’s happening and what’s next.
- This guide covers seven platforms: Arrivy, Jobber, ServiceTitan, FleetSharp, Connecteam, Service Fusion, and Fieldwire.
- These tools aren’t interchangeable; each one has a different center of gravity, whether that’s fleet monitoring, workforce coordination, customer communication, or construction collaboration.
- Some go further with offline task handling, digital quoting, and deep workflow customization.
|
How We Selected These Field Service Mobile Apps
This list was compiled by considering what field service teams actually complain about, and which platforms kept coming up as solutions in those conversations.
The baseline criteria were straightforward: scheduling, dispatching, technician coordination, and real-time job visibility. From there, we cross-referenced user reviews on G2 and Capterra to understand how efficiently these tools work once the demo is over.
The seven apps here serve different business sizes and industries, from small HVAC and plumbing crews to enterprise-scale operations with technicians across multiple regions.
Comparison of Popular Field Service Mobile Apps
Before getting into each platform individually, here’s a side-by-side look at how they compare on use case, core capabilities, and pricing.
If you already have a rough sense of your budget or team size, use this table to cut the list down to two or three realistic options before reading the full breakdowns below.
Note that pricing is subject to change. Always verify directly with the vendor.
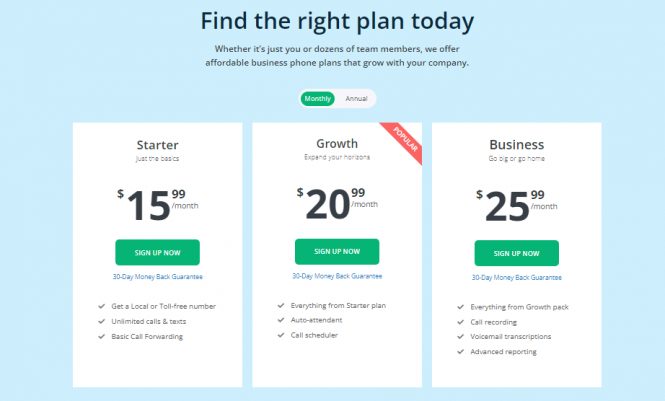
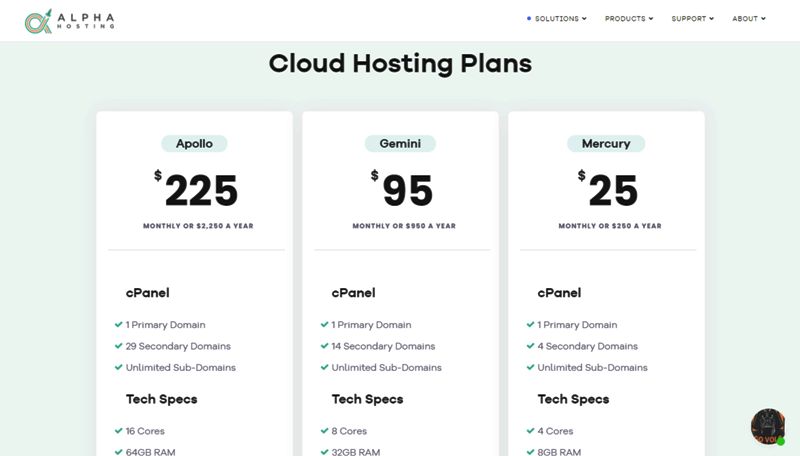
| App | Best For | Key Capabilities | Pricing | Notable Features |
|---|
| Arrivy | Real-time field service coordination | Scheduling, dispatching, and job tracking | Starting at $75/month (includes 3 users; $25 per additional user) | Customer notifications, GPS tracking, quotes, and offline forms |
| Jobber | Small service businesses | Quotes, scheduling, invoicing | Plans start around $39 per user/month | Client portal, automated reminders |
| ServiceTitan | Large service companies | Dispatching, job management, analytics | Pricing available on request | Advanced reporting, membership management |
| FleetSharp | Fleet tracking and vehicle monitoring | GPS tracking, route monitoring | Pricing available on request | Driver behavior monitoring, vehicle activity reports |
| Connecteam | Workforce and employee management | Scheduling, time tracking, and communication | Paid plans from about $29/month | Shift management, internal chat |
| Service Fusion | Customer communication and job management | Estimates, dispatching, messaging | Starting around $245/month for unlimited users | Built-in texting and call tracking |
| Fieldwire | Construction field collaboration | Task tracking, project coordination | Paid plans from about $39 per user/month | Blueprint access, project documentation |
Here’s how each one actually works in practice.
1. Arrivy
“The most helpful team with a very intuitive and dynamic platform.” — Nate M., VP of Innovation and Data Operations (G2)
Arrivy sits in an interesting spot among field service tools, genuinely flexible in a way most platforms aren’t, and particularly strong on the customer-facing communication side.
Teams that have tried to force their workflow into a rigid system and failed tend to find Arrivy a better fit. The platform connects dispatchers, technicians, and customers without making any of the three feel like an afterthought.
Scheduling & Dispatch
Dispatchers can build out job schedules, assign crews, and watch progress updates in real time without refreshing anything manually. Job statuses like “on the way,” “started,” and “completed” are customizable, so the board reflects how your operation actually runs rather than how the software assumes it does.
What Technicians Get in the Field
The mobile app, available on both iOS and Android, gives technicians their full job picture before they arrive on site. Instructions, customer details, and any attached forms are right there. Updates, photos, and notes go back to the office the same way, which cuts the check-in calls that eat up everyone’s time.
Live Location Visibility
GPS tracking feeds into a central dashboard so dispatchers always know where crews are. When a job runs long or a route needs adjusting mid-day, having that map view makes the difference between a smooth recovery and a frustrated customer.
Keeping Customers in the Loop
Arrivy handles customer notifications automatically when a crew is heading over, when work kicks off, and when the job is wrapped. It happens without anyone in the office having to remember to send an update.
Quoting & Workflow Configuration
Digital quotes go out to customers for online approval before work begins, and because the quote lives inside the same system as scheduling, an approved job moves straight to the calendar without anyone re-entering information on the back end. No printing, no back-and-forth over email, no copy-pasting details from one tool into another.
Beyond quoting, the platform is built to be configured. Templates, workflows, and job structures can all be adjusted to match what your team already does rather than the other way around.
2. Jobber
“Organized layout with unique features, though it could benefit from more flexibility.” — Ryan B., Validated Reviewer (G2)
It’s the go-to starting point for small service businesses that want a clean, low-friction setup. There’s no steep learning curve, no bloated feature set that takes months to configure. You set it up, your team learns it in a day, and jobs start moving through a cleaner process than before.
Scheduling & Work Orders
Assigning jobs, managing a service calendar, and organizing work orders all happen from one place. For businesses running a handful of crews across a busy week, having that in a single screen beats juggling texts and spreadsheets by a wide margin.
The Mobile Side for Technicians
Technicians open the app and see exactly what they need. The job, the customer details, and any notes from the office. They can log progress and add their own notes from the field without calling anyone.
Tracking What’s Actually Happening
Managers can see where the day stands across all active jobs without chasing down updates. That alone saves real time.
Client Communication
Appointment reminders go out automatically. Follow-up messages after a job can be scheduled. Customers stay informed without someone on your team having to remember to send anything.
From Quote to Invoice
Jobber handles the full billing cycle, creates a quote, gets it approved, schedules the job, and generates the invoice once it’s done. For small businesses where the owner is often handling admin alongside everything else, having that flow in one place removes a lot of manual work.
3. ServiceTitan
“Deep, customizable platform backed by a team that stands behind it.” — Leon W., Service Manager (G2)
It’s built for larger operations, the ones where a lightweight tool stopped being enough a while ago. The depth is designed for companies running multiple crews, tracking performance across teams, and managing customer relationships at scale, and the implementation effort reflects that.
Dispatching at Scale
ServiceTitan’s dispatching system handles complex scheduling across large technician pools. Service calls get assigned and tracked through a centralized board, and nothing falls through the cracks.
Technician Experience in the Field
The mobile app gives technicians what they need on-site: job details, service history, status updates, and documentation. They’re not calling the office to ask basic questions because the answers are already in the app.
Reporting That Actually Means Something
This is where ServiceTitan separates itself from lighter tools. The analytics go beyond job counts. You can track performance by technician, monitor trends over time, and identify where jobs are getting delayed or where revenue is being left on the table.
Customer Communication
The platform manages customer interactions through the full service lifecycle. Appointment confirmations, service reminders, follow-ups, it’s all handled without manual intervention at each step.
Estimates & Service Agreements
Technicians can build estimates in the field. Membership and maintenance agreements are tracked at the platform level, which matters a lot for businesses that run recurring service programs and need visibility into renewals and upcoming visits.
4. FleetSharp
“It’s been a useful tool for managing our fleet, and their customer support has been really helpful when we run into any issues.” — Paul J., Office Coordinator (Capterra)
Best for businesses where vehicle management and driver accountability are the primary operational concerns. FleetSharp is a narrower tool than the others on this list. It’s not trying to manage your entire field service operation. What it does is give businesses real, detailed visibility into their vehicles, and it does that well. For companies where fleet costs and keeping tabs on driver behavior directly affect the bottom line, that narrow focus is actually an advantage.
Fleet Monitoring & Route Tracking
Vehicle locations, route history, and travel patterns are all tracked and viewable from a central dashboard. If a driver is taking inefficient routes or racking up unnecessary mileage, it shows up here, and managers can act on it with actual data instead of gut feeling.
Mobile Access for Managers
Fleet data isn’t locked to a desktop. Managers can check vehicle locations and activity from their phones, which is useful when something goes sideways in the field and you need to know quickly where your nearest truck is.
Driver Behavior Reporting
FleetSharp generates reports on driving patterns, not just where vehicles went but how they were driven. For companies managing insurance costs or trying to reduce wear on their fleet, that data adds up to real savings over time.
5. Connecteam
“Reliable, powerful, and built for real-world teams.” — Spencer M., Manager (Capterra)
Most field service platforms are built around the job. Connecteam is built around the people doing the jobs, which makes it a different kind of tool.
If your biggest operational headache is coordinating a large frontline workforce, tracking hours accurately, or keeping employees informed across shifts, Connecteam addresses that more directly than most scheduling-first platforms do.
Scheduling & Shift Management
Managers build out schedules, handle shift swaps, and push changes out to the team from one place. When someone calls out or a shift needs coverage, adjustments happen fast without a phone chain.
Employee Mobile Experience
Workers clock in, check their schedules, submit updates, and communicate with managers entirely through the mobile app.
Time Tracking & Hours Visibility
Digital timesheets replace paper logs and manual entries. Managers can see hours in real time, catch discrepancies before payroll, and keep a clean record without chasing anyone down at the end of the week.
Internal Communication
Built-in chat and company-wide announcements mean important updates don’t get lost in a group text or missed entirely. For larger teams, that kind of structured communication channel is worth more than it looks on a feature list.
Task Management & Checklists
Beyond scheduling, Connecteam includes task assignment and checklist tools, useful for onboarding new employees, running recurring safety checks, or standardizing how specific jobs get completed across different crew members.
6. Service Fusion
“We are pretty happy that we’ve upgraded our dispatch and estimating to Service Fusion.” — Sruli G., President (G2)
Service Fusion is a strong fit for growing teams where headcount is increasing and per-seat pricing becomes a real budget concern. It makes a compelling case on pricing alone, a flat monthly rate, unlimited users, and no per-seat cost increases as your team grows.
The platform covers the core field service workflow without unnecessary complexity, and the built-in customer communication tools are a genuine differentiator.
Scheduling & Dispatching
Jobs get scheduled, technicians get assigned, and work orders move through the system from a clean dispatching dashboard. Nothing groundbreaking here, but it’s well-organized and reliable, which is honestly what dispatchers need most.
Field Technician Tools
The mobile app gives technicians access to job details and lets them update status and log service notes from the field. Straightforward, functional, and doesn’t require a training day to figure out.
Customer Texting & Call Tracking
This is where Service Fusion stands out. Built-in texting lets businesses communicate with customers directly through the platform, including appointment confirmations, on-the-way messages, and follow-ups. Call tracking adds another layer of accountability for customer interactions.
Estimates & Job Workflow
Estimates go out, customers approve them, jobs get scheduled, work gets done. The flow from first contact to completed invoice is handled inside one system without jumping between tools.
7. Fieldwire
“A centralized all-in-one app for construction.” — Krystler F., Project Manager / Senior Estimator (G2)
Fieldwire works well in construction, not traditional field service, and that context shapes everything about how it works. If you’re managing multi-phase projects, coordinating subcontractors across active job sites, and dealing with blueprints and project documentation as daily realities, it’s built for that environment in a way that general FSM tools simply aren’t.
Task Management Across Job Sites
Tasks get assigned, tracked, and updated across multiple active projects simultaneously. Project managers can see what’s completed, what’s behind, and what needs attention without walking the site or calling every foreman.
Blueprint & Plan Access from the Field
Workers pull up current plans directly on their phones or tablets at the job site. No printed drawings, no version confusion, no waiting until they’re back at the office to check something. That alone saves significant time on a busy site.
Real-Time Project Visibility
Progress updates feed back into shared dashboards that keep everyone, site workers, project managers, and office teams, looking at the same picture. When work gets done, or something changes, it’s reflected immediately rather than at the end-of-day report.
Team Collaboration Tools
Notes, updates, and project documentation can be shared across the team inside the platform, keeping subcontractors and site supervisors working from the same information.
Site Documentation & Photo Logging
Photos, reports, and documents attach directly to project tasks, building a running record of job site activity. For projects where documentation matters, inspections, sign-offs, and punch lists, having it all tied to specific tasks rather than sitting in someone’s email is a practical advantage.
What to Look for in a Field Service Mobile App
Most platforms claim to do everything. These three questions cut through that quickly:
Does the mobile app actually work for technicians?
Start here, not with the desktop version. If your crew won’t open the app between jobs, the back-end doesn’t matter. Always pull up the mobile interface before you commit. That’s the version your team will live in every day.
Where does your dispatching actually break down?
Some platforms are built to cut phone tag between the office and the field. Others focus on route optimization or giving managers a live map view. Know which problem you’re solving before you start comparing features because every platform looks equally good in a demo.
Does customer communication happen automatically?
This is underrated during the buying process and critical once you’re live. Manual notification workflows fall apart under volume. Look specifically for platforms where updates go out on their own, without a dispatcher having to remember to trigger them every single time.
Conclusion
No single platform here is the obvious winner for every business. Anyone telling you otherwise is probably selling something.
A small cleaning crew and a regional HVAC operation with 40 technicians have almost nothing in common operationally, even though they’re searching for the same thing. What works for one is overkill or underpowered for the other.
The more useful exercise than reading comparison tables is writing down the two or three moments in your current workflow where things actually go wrong, and then evaluating platforms against those moments specifically.
Most of these tools offer trials. Use them. The right field service management app brings scheduling, job tracking, and customer communication into one place, and makes the difference between a day that runs and a day that unravels.
FAQs
What is a field service mobile app?
It’s software that keeps technicians, dispatchers, and office teams connected during live field operations. Instead of relying on phone calls and printed job sheets, technicians get everything they need pushed to their phones, job details, customer info, instructions, forms, and send progress back the same way.
Which field service app is best for small businesses?
Jobber and Arrivy come up most often for smaller teams. Jobber is straightforward: quote, schedule, invoice, done. Arrivy works well for small businesses that need more flexibility, particularly around customer notifications and customizable job workflows.
What’s the difference between field service software and fleet tracking software?
Fleet tracking tools like FleetSharp focus on the vehicles, GPS location, route history, driver behavior, and mileage. Field service platforms manage the broader picture: scheduling jobs, dispatching technicians, tracking work progress, and communicating with customers. They solve different problems. Some businesses run both side by side.
Do field service mobile apps work without an internet connection?
It depends on the platform. Arrivy supports offline task updates and form completion that sync automatically once the connection is restored, which matters for technicians working in basements, rural areas, or anywhere cell coverage is unreliable. Offline capability varies across platforms, so test this specifically if your crews work in low-signal areas.
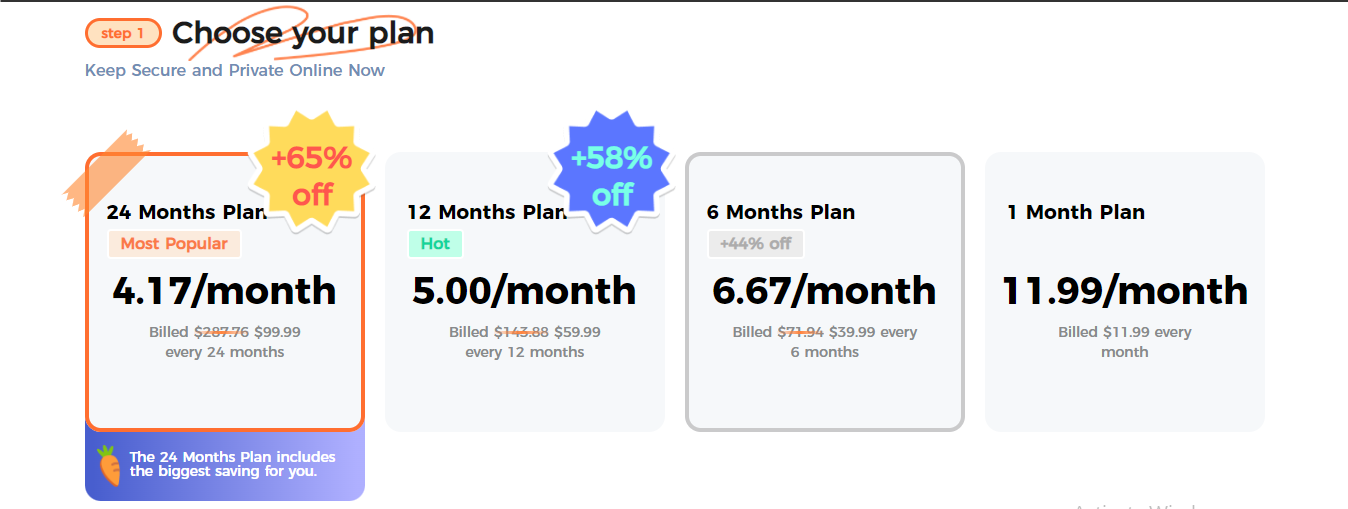
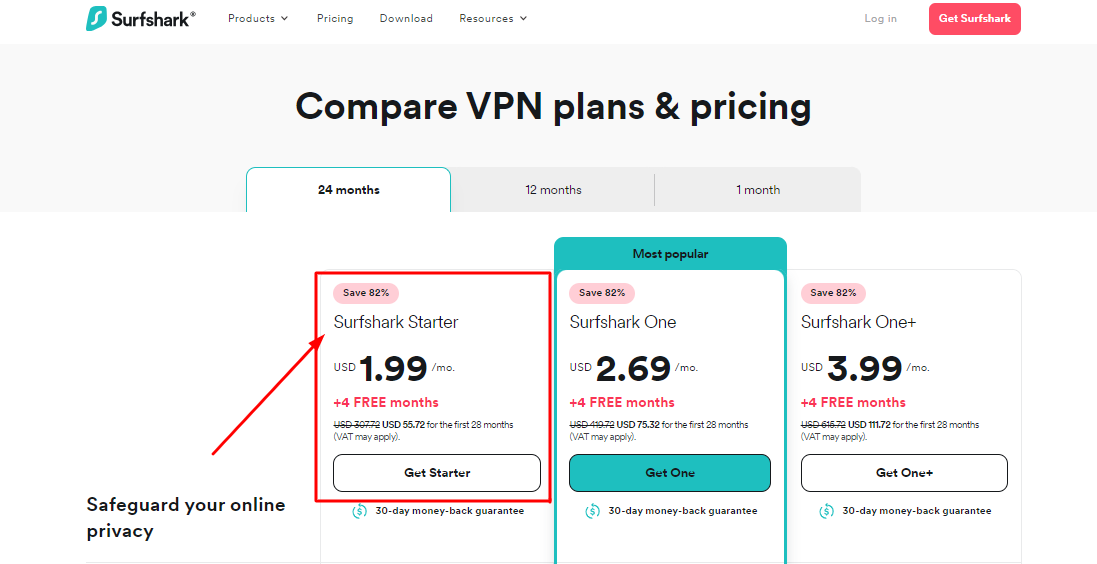
How much do field service mobile apps cost?
Entry-level plans start around $29–$75 per month for small teams. Mid-market platforms like Service Fusion run around $245 per month with unlimited users, which becomes good value as headcount grows. Enterprise platforms like ServiceTitan are custom-priced based on team size and don’t publish rates publicly. Most platforms offer a trial period, which is worth using before signing anything.
INTERESTING POSTS




![5 Best VPN For Zap Surveys [Tested, Reviewed & Ranked] 5 Best VPN For Zap Surveys [Tested, Reviewed & Ranked]](https://secureblitz.com/wp-content/uploads/2021/10/5-Best-VPN-For-Zap-Surveys-768x402.png)

![5 Best VPN for Zepeto [2026 LIST] 5 Best VPN for Zepeto [2026 LIST]](https://secureblitz.com/wp-content/uploads/2021/10/5-Best-VPN-for-Zepeto-2022-LIST-768x345.png)












![Turbo VPN Review: Is Turbo VPN Safe? [+Best Alternatives] Turbo VPN Review: Is Turbo VPN Safe? [+Best Alternatives]](https://secureblitz.com/wp-content/uploads/2022/03/Is-Daily-VPN-Safe-2-768x345.png)