In this post, I will talk about the ultimate 2026 iGaming free play demo aggregator.
The iGaming industry is poised for a significant transformation. 2026 is only a few moments ahead, and there are some changes to expect. The days of clunky downloads, mandatory sign-ups, and lag-heavy interfaces are fading. The new year is set to usher in the zero-barrier era.
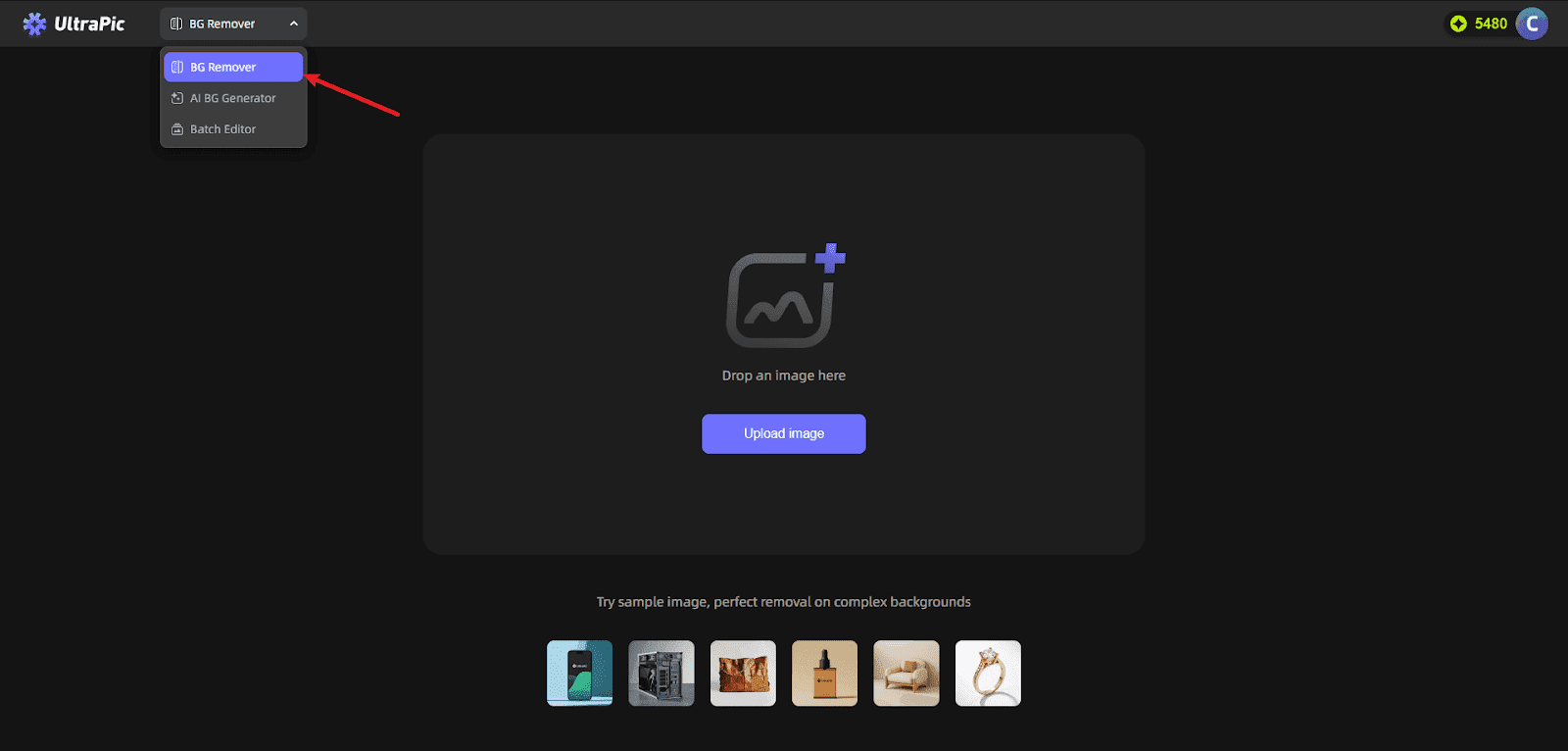
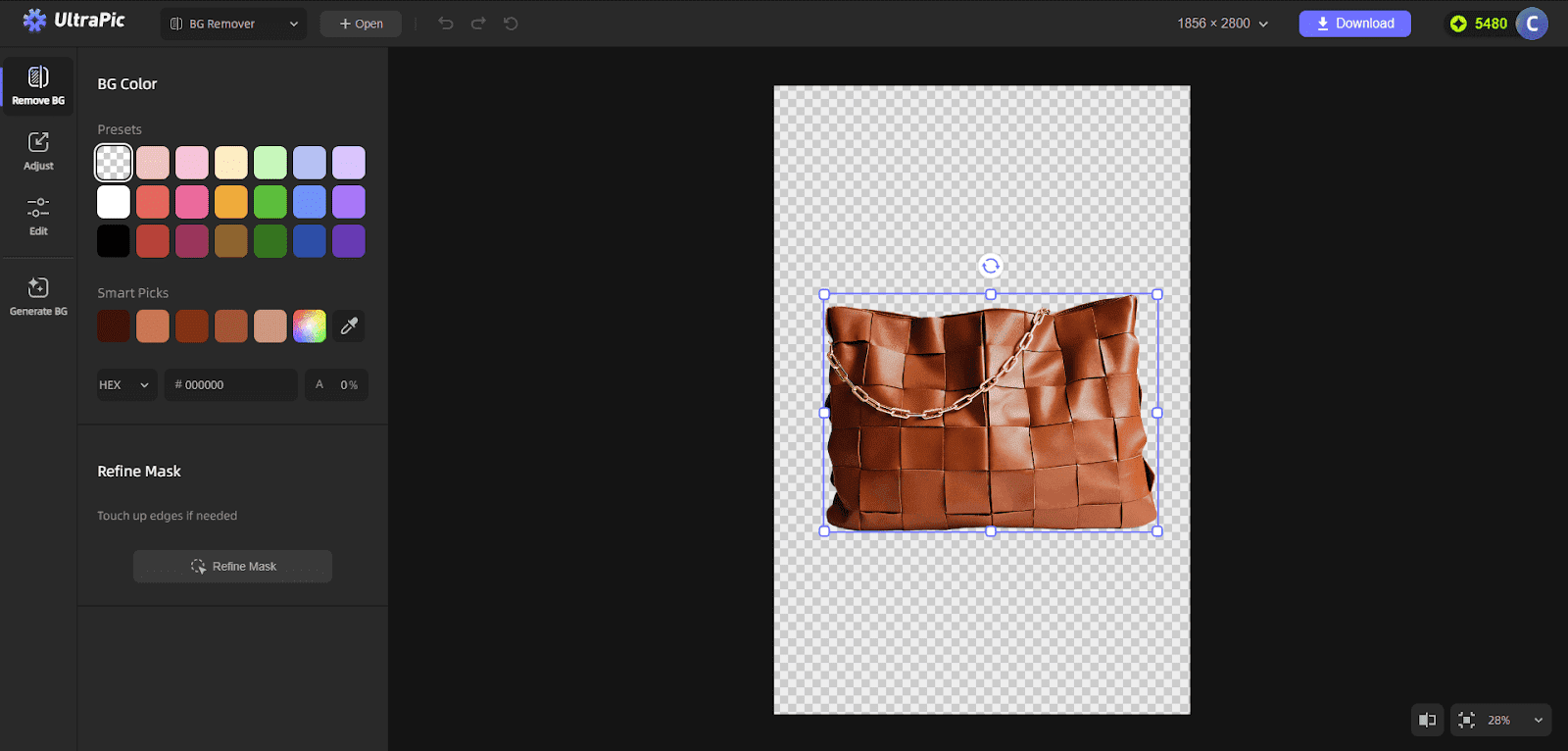
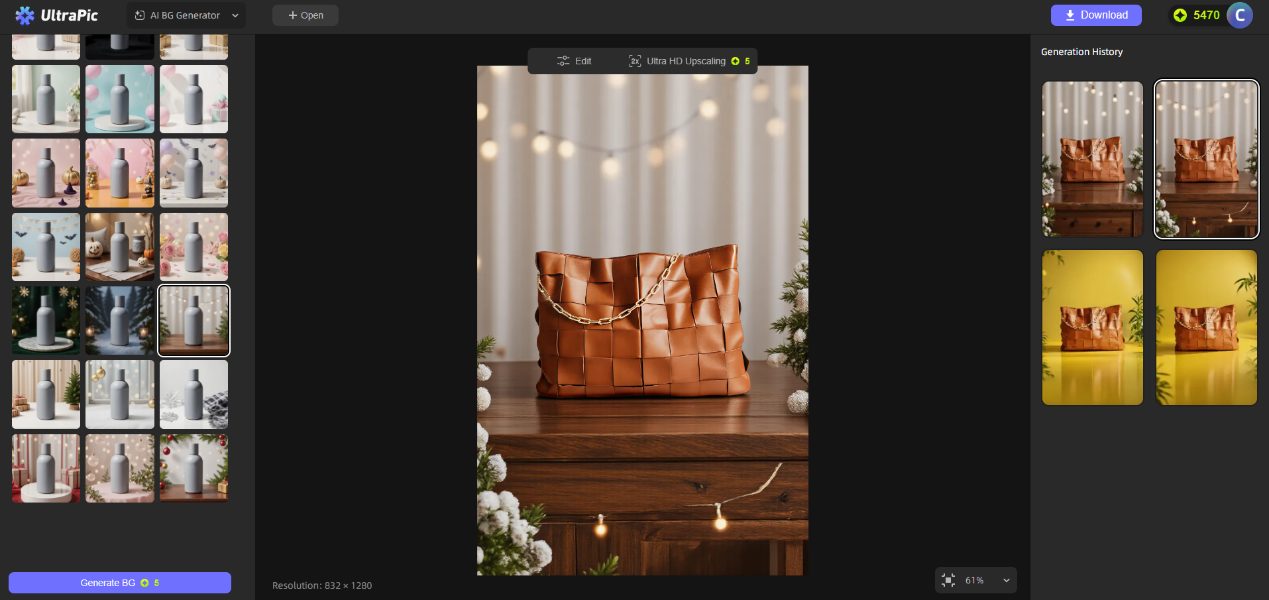
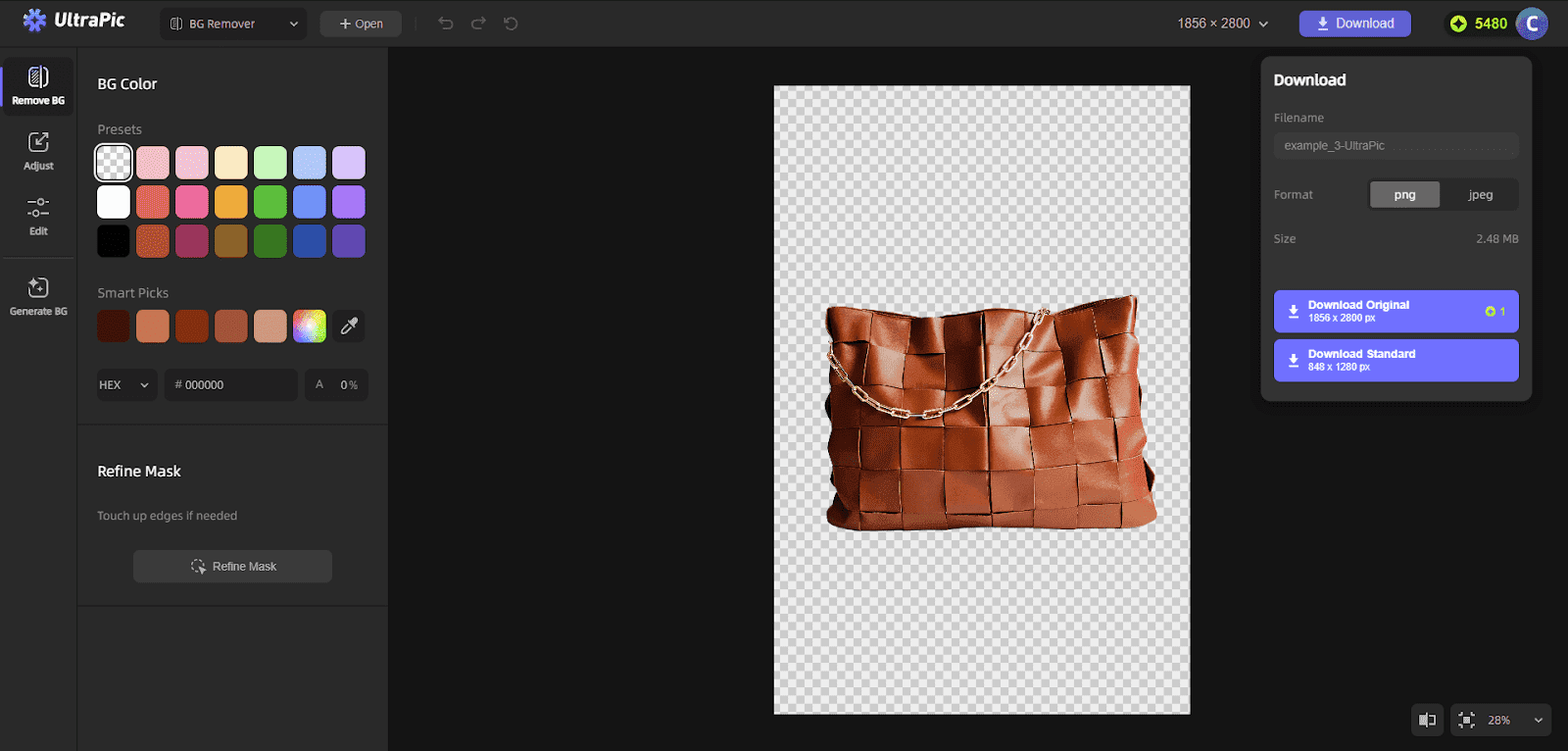
Being accessible is now the primary driver of user engagement. Players need instant access to premium entertainment without the friction. This has led to the rise of the Free Play Demo Aggregator, a centralized hub powered by advanced HTML5 (H5) technology.
It is designed to deliver a casino-grade experience directly to your browser, instantly. In this guest post, delve deeper into the Free Play Demo Aggregator, DSTGAMING, and its crucial role.
Detailed Game Reviews (The Expert View)
Here is a look at what the games from the iGaming Free Play Demo Aggregator looks like:
High-Fidelity Slots Without the Lag
The modern slot machine is a beast. It blends cinematic 3D visuals with intricate mathematical models. Usually, high fidelity meant high latency. The new standard for 2026 focuses on H5 optimisation, prioritising asset loading. This ensures that even graphically intense games launch instantly. The aggregator maintains crisp textures and fluid animations without bogging down the player’s device.
The Rise of Instant-Win Mini Games
There is a surge in “micro-session” gaming. More players are leaning towards quick mini-game sessions, which has led to instant-win titles, like crash games. Our reviews place a strong emphasis on session length and intuitive design.
These games prioritize distilled mechanics over complex pay tables. With this version, players jump in, understand the objective, and complete a round in under 30 seconds.
The Community Voice: Simulated Player Insights
While technical specifications are essential, a platform’s accurate measure is user sentiment. DSTPLAY and the 2026 aggregator strategy have a tangible impact in the real world. To illustrate this, check out these feedbacks from three distinct player personas. These simulated insights reveal what different segments of the community value most.
1. The Strategy Hunter (Alex): the Analytical Grinder
Alex views the demo as a place to try different strategies like a laboratory. He uses free play to reverse-engineer a game’s behaviour before committing real money. His priority is the transparency of the math model. Here is what he has to say:
“I spent 2 hours on the demo to understand the volatility. The way the DSTPLAY engine handles multipliers is a game-changer for my strategy. It’s rare to find a demo that feels this ‘honest’ regarding the hit rate.”
2. The Mobile-First Casual (Maya): the Commuter
Maya represents the majority of modern traffic. She is one of the many players who engage in short bursts on mobile devices. She doesn’t care about RTP variance. What picks her interest is the game’s UI. If a game forces her to rotate her screen, it is a no for her.
“Finally, every game fits my phone screen perfectly. I can spin with one hand while commuting. It is a relief that no landscape rotation is needed. The UI is clean, and the buttons are big enough to tap without looking.”
3. The Tech Enthusiast (Chen): the Performance Junkie
Chen needs perfection. He has zero tolerance for lag or stuttering when using the high-end device and a 5G connection. He validates the technical backbone of the aggregator.
“Most aggregators lag, but this H5 tech is incredibly smooth. The transitions between the lobby and the game are seamless. It feels less like a webpage and more like a native app.”
The Technical Backbone: Trust Through Transparency
The feedback from Alex, Maya, and Chen highlights a critical truth: players are becoming more sophisticated. They can tell when a demo is “rigged” to be too generous. Additionally, they recognise that a platform must be well-optimised to support the Zero-Barrier era; DSTPLAY relies on a foundation of certified fairness. All titles displayed are compliant with GLI 19. This ensures that the RNG used in the demo is identical to the one used in the real-money version.
Check out the displayed real-time data on RTP and volatility. DSTPLAY combines complex data with the qualitative simulated insights to enable players to make informed choices. Whether you want a low volatility game for a long session or a high volatility game for a quick thrill, you’ll know at the get-go.
Conclusion
In 2026, the iGaming Free Play Demo Aggregator would be more than a repository of games. It is a glimpse into the future of the iGaming industry. DSTPLAY has incorporated several tips from technical reviews and community feedback to ensure seamless aggregation of demo games, resulting in reduced friction.
There is no need for large downloads and chunky sign-ups. Once players visit your site, they can access your favourite demo right away.
Experience the community favourites: Launch your first free demo now.
INTERESTING POSTS
- Complete DeleteMe Review [100% WORKING]
- What Is GLI 19 Certification and Why It Matters for iGaming Platforms
- How To Get Started On Forex Trading
- Best Way to Play Slot Machines and Maximize Your Chances
- Exclusive Interview With Alex Ruiz, COO Of 3GO Security
- Soft2Bet: Driving Innovation in the iGaming and Casino Technology Industry