Want the best ISP Proxies? Read this post to find out…
ISP proxies have become increasingly popular in today’s digital landscape due to their numerous advantages over datacenter and residential proxies.
Selecting a reliable proxy provider with high-quality and secure services is crucial when choosing the best ISP proxies.
This comprehensive guide will explore the benefits of ISP proxies, review the top proxy providers in the market, and help you make an informed decision.
What Are ISP Proxies and Why Do You Need Them?

ISP proxies, or static residential proxies, utilize IP addresses allocated by Internet Service Providers (ISPs).
These proxies offer the combined benefits of datacenter proxies and residential proxies, providing fast speeds, high anonymity, unlimited bandwidth, and private browsing capabilities.
They are ideal for various use cases such as web scraping, SEO monitoring, social media monitoring, ad verification, brand protection, and price comparison.
By using ISP proxies, you can access geo-restricted content, avoid IP blocking, and ensure the security and privacy of your online activities.
These proxies act as intermediaries between your device and the websites you visit, concealing your actual IP address and protecting your sensitive data.
ISP proxies are especially valuable for businesses, including Fortune 500 companies, as they offer reliable and secure connections for critical operations.
Best Proxies Deals
Best Featured ISP Proxy Service Providers – EDITOR’S CHOICES
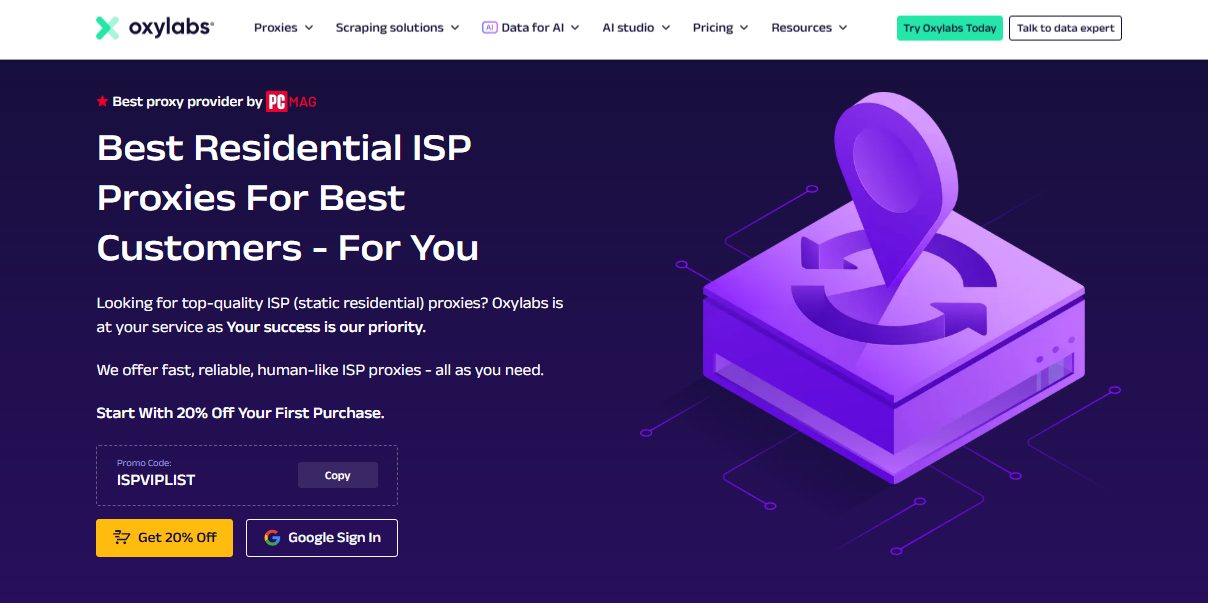
1. Oxylabs – Best for Enterprise-Grade Proxy Solutions
Oxylabs is widely recognized as the leading provider of ISP proxies, offering top-quality dedicated proxies for sneaker copping and other use cases.
Their proxies are renowned for their exceptional speed, reliability, and compatibility with major websites, including Adidas, Foot Locker, Nike, and Shopify.
With millions of IP addresses available in Western Europe and the US, Oxylabs ensures you have a wide range of options to suit your needs.
Key Features:
- Fast and reliable connections for seamless browsing and data collection
- Wide coverage with millions of IP addresses in Western Europe and the US
- Compatible with major sneaker websites for successful copping
- User-friendly dashboard for easy proxy management
- Excellent customer support and 24/7 technical assistance
Best For:
- Large-scale data extraction
- Market research and competitor analysis
- Ad verification and brand protection
Why Choose Oxylabs?
For businesses seeking enterprise-grade reliability, massive scalability, and ethical proxy sourcing, Oxylabs provides a premium experience. Try Oxylabs today for a seamless proxy solution!
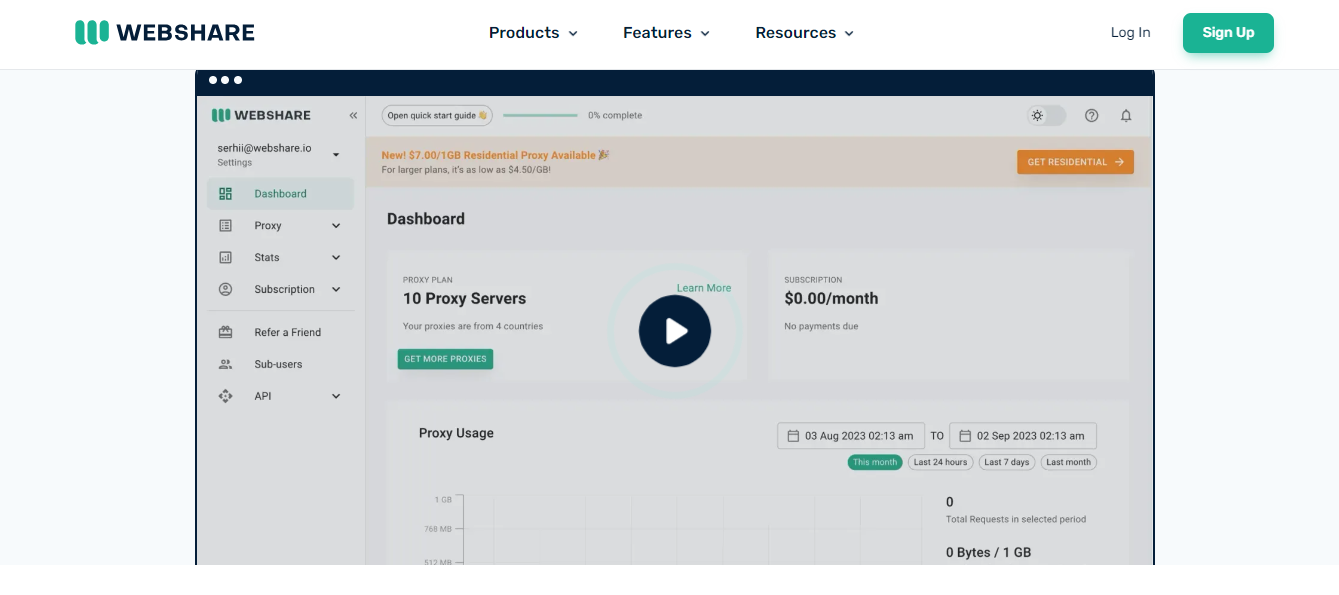
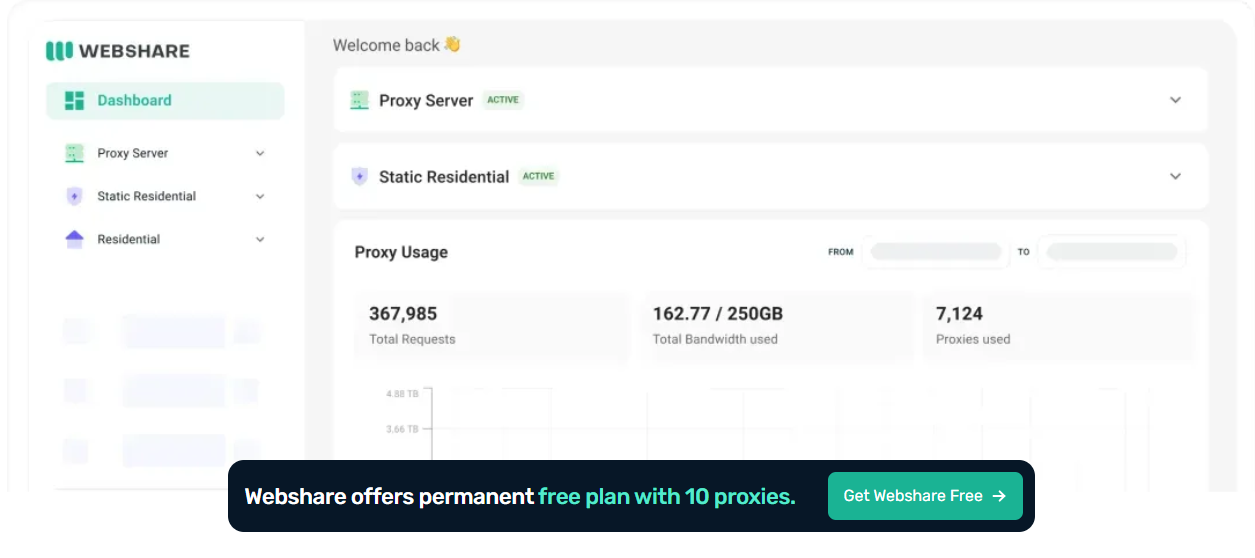
2. Webshare – The Most Affordable ISP Proxies Service Provider
Webshare provides high-quality ISP proxies sourced from residential IP addresses. This makes them more anonymous than datacenter proxies and better suited for use cases that require precise location targeting.
Not to mention, Webshare gives you unlimited bandwidth for all static residential plans, unlike other proxy service providers.
Webshare offers a variety of plans to suit different needs, including shared, private, and dedicated proxies. They also have a good reputation for customer support.
Key features:
- Webshare’s high-speed static residential network of up to 1 GBps
- 99.7% uptime
- High-quality residential proxies
- Worldwide coverage
- Fast speeds
- Reliable connections
- Good customer support
- Variety of plans to choose from
Best For:
- Budget-conscious businesses and startups
- SEO monitoring and web scraping
- Automated data collection and social media management
Why Choose Webshare?
If you need cost-effective, high-performance proxies with full control over your plan, Webshare is an excellent choice. Get started with Webshare today and experience reliable proxies at an unbeatable value!
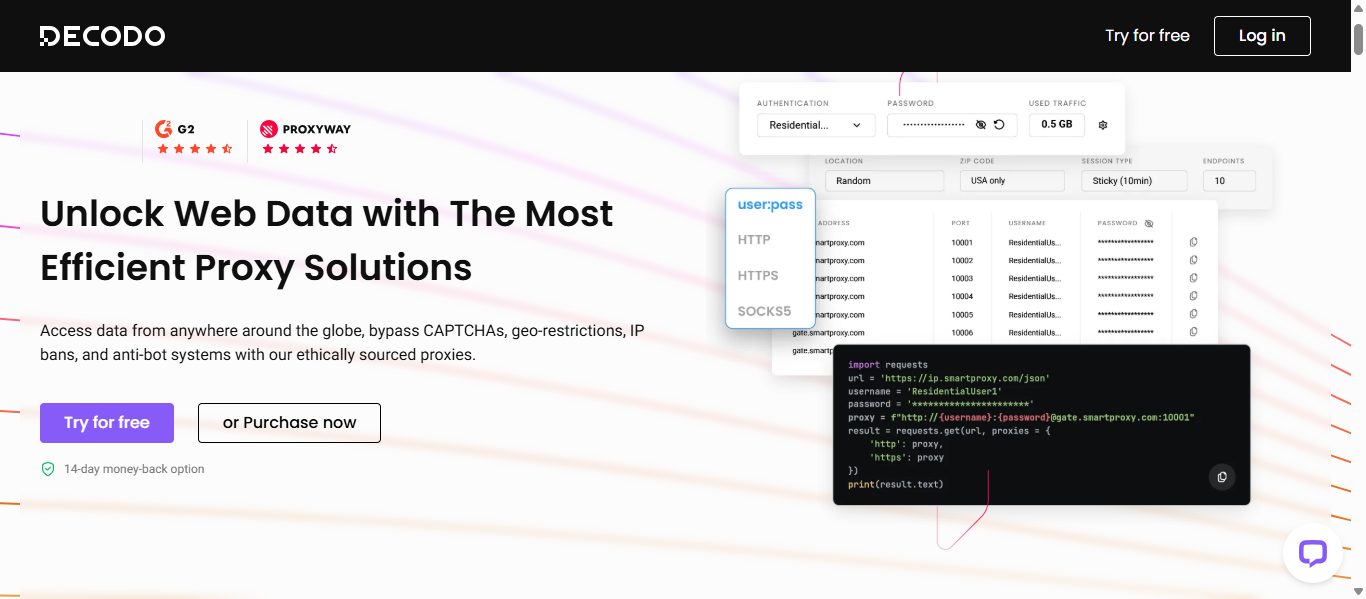
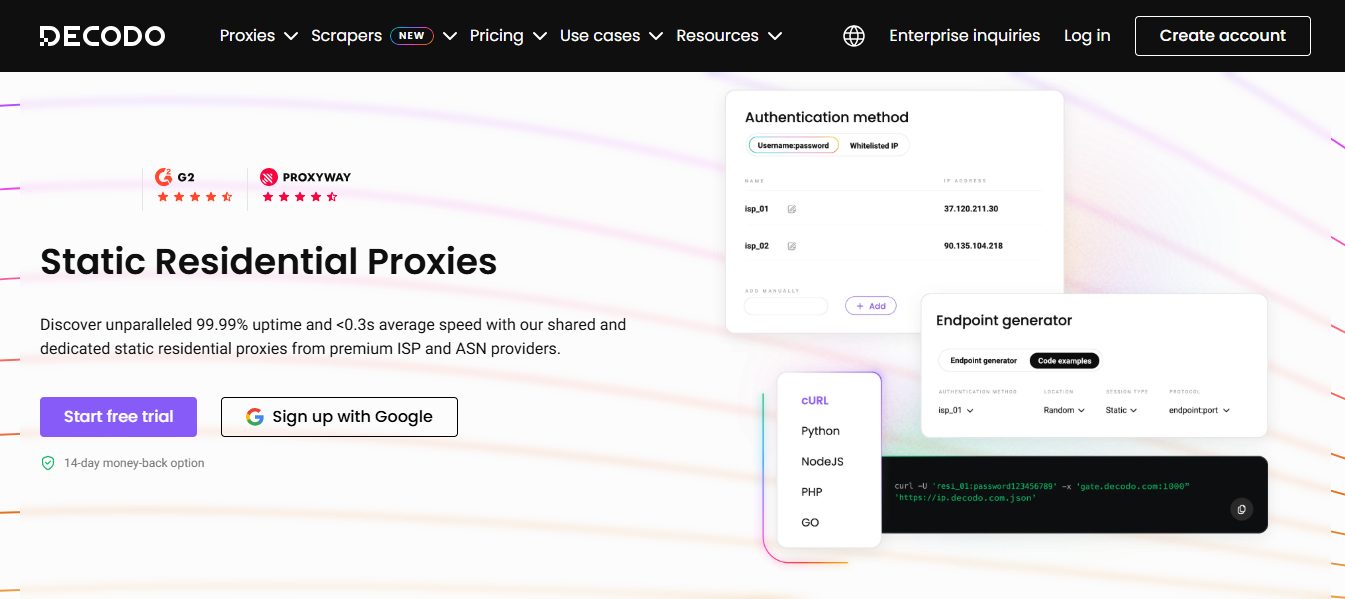
3. Decodo – High-Quality ISP Proxies with Affordable Pricing
Decodo (formerly Smartproxy) is a leading private proxy provider, known for its balance of performance, affordability, and ease of use. Whether you’re a beginner or a professional, Decodo’s plug-and-play proxy solutions simplify web scraping, automation, and online security.
With over 115 million+ IPs across 195+ locations, Decodo ensures fast, reliable connections with an average speed of <0.3s and a 99.99% uptime. Their ISP proxies are especially popular for sneaker copping on websites like Finish Line, Footsites, Yeezy Supply, and Shopify.
Smartproxy, for those interested in residential proxies, offers a free trial that allows users to test the service before committing.
Key Features:
- 195+ locations for global access
- 115M+ residential proxies and 65M+ total IPs
- <0.3s average speed with 99.99% uptime
- HTTPs and SOCKS5 support
- Customer support responds within 40 seconds
- Free trials available on all products
Best For:
- E-commerce monitoring and sneaker botting
- Social media automation and ad verification
- General-purpose web scraping and research
Why Choose Decodo?
Decodo makes proxy management easy with a user-friendly dashboard, affordable pricing, and excellent customer support. Whether you’re looking for ISP, residential, or datacenter proxies, Decodo provides reliable, high-performance solutions to meet your needs.
Other Best ISP Proxies Provider
When selecting the best ISP proxy provider, several factors should be considered, including network size, performance, reliability, pricing, and customer support.
To help you make an informed decision, we have thoroughly researched the top proxy providers in the market. Here are our recommendations for the best ISP Proxies providers:
1. Bright Data – Unmatched Proxy Infrastructure
Bright Data, formerly known as Luminati, is a reputable proxy provider that offers a wide range of proxy services, including high-quality ISP proxies.
Their ISP proxies are sourced directly from Internet Service Providers, ensuring the fastest response times and 99.99% network uptime.
With an extensive pool of over 72 million residential IPs from 195 countries, Bright Data provides unmatched global coverage for all your proxy needs.
Key Features:
- Extensive pool of over 72 million residential IPs from 195 countries
- Superior network uptime and fastest response times in the industry
- Dedicated ISP proxies for reliable and secure browsing
- Easy integration with popular tools and platforms
- Customizable solutions to meet your specific requirements
2. NodeMaven – Scalable ISP Proxies

NodeMaven is a relatively new proxy provider, but they have quickly gained a reputation for offering high-quality ISP proxies.
Their proxies are known for their fast speeds, global coverage, and affordability.
NodeMaven also offers a variety of features that make it a suitable choice for various use cases, including rotating proxies, dedicated IP addresses, and sub-user management.
Key Features:
- Fresh IPs: NodeMaven regularly rotates their IPs. This helps prevent your IP addresses from being blocked by websites and services.
- Secure: NodeMaven ISP proxies use SSL encryption to protect your data. This ensures that your traffic is secure and private.
- Scalable: NodeMaven ISP proxies are designed to be scalable, allowing you to easily add or remove proxies as needed. This makes them a good choice for businesses and organizations that must manage many.
==>> Get Nodemaven
3. MarsProxies – Dependable ISP Proxies for sneaker copping
MarsProxies are a good choice for users who need proxies specifically designed for sneaker copping.
They offer various plans tailored to this use case, including dedicated proxies and proxies that are rotated every 5 minutes.
MarsProxies also has a good reputation for customer support.
Key features:
- ISP proxies specifically designed for sneaker copping
- Variety of plans tailored to this use case
- Good customer support
==>> Get MarsProxies
4. IPRoyal – High-Speed ISP Proxies
IPRoyal is a popular proxy provider that offers a variety of proxy types, including ISP proxies.
Their ISP proxies are known for their high uptime, fast speeds, and global coverage. IPRoyal also offers a free trial, allowing you to test their proxies before making a purchase.
Key Features:
- Undetectable: IPRoyal ISP proxies are designed to be undetectable by most websites and services. This makes them a good choice for sneaker copping, web scraping, and other tasks that require anonymity.
- Secure: IPRoyal ISP proxies use SSL encryption to protect your data. This ensures that your traffic is secure and private.
- Scalable: IPRoyal ISP proxies are scalable, so you can easily add or remove proxies as needed. This makes them a suitable choice for businesses and organizations that require managing multiple proxies.
==>> Get IPRoyal
5. Proxy-Cheap – Budget-Friendly ISP Proxies for Everyday Tasks
Proxy-Cheap is a well-known proxy provider especially popular among users who want reliable ISP proxies without spending too much. Despite its affordable pricing, Proxy-Cheap maintains strong performance across multiple use cases, including automation, data gathering, and sneaker copping.
Their ISP proxies offer good speeds, decent uptime, and support for various geo-locations. You can buy static residential proxy from Proxy-cheap. Besides, Proxy-Cheap also offers flexible billing, making it an appealing option for both beginners and mid-level users who require scalable proxy solutions.
Key Features:
- Affordable Pricing: Proxy-Cheap stays true to its name by offering some of the most budget-friendly ISP proxies on the market. This is ideal for users who want quality without high costs.
- Multiple GEO Options: They offer ISP proxies from various locations, providing users with flexibility depending on their target websites and tasks.
- Reliable Performance: Proxy-Cheap ISP proxies provide stable speeds and uptime, making them suitable for general automation, research, and lightweight scraping tasks.
==>> Get Proxy-Cheap
6. NetNut – Long-Term ISP Proxies
NetNut is another reputable proxy provider that offers ISP proxies. Their proxies are known for their affordability and reliability.
NetNut also offers a variety of features that make it a suitable choice for various use cases, including rotating proxies, dedicated IP addresses, and sub-user management.
Key Features:
- Long-term IPs: NetNut offers long-term IPs that are not rotated. This is a good choice for tasks that require consistency, such as social media marketing and SEO.
- High availability: NetNut offers a 99.9% high availability guarantee. This means you can be confident that your proxies will be available when you need them.
- Friendly support: NetNut offers friendly and helpful support. You can contact their support team for assistance if you have any questions or problems.
==>> Get NetNut
7. Infatica – High-quality ISP proxies

Infatica is a proxy provider offering a range of proxy solutions, including residential, mobile, and data center proxies.
They are a good choice for users who need to bypass geo-restrictions, scrape data, or maintain online anonymity.
Some of the key features of Infatica include:
- A large pool of proxies: Infatica maintains a substantial pool of proxies, encompassing residential, mobile, and data center proxies. This provides users with a wide range of options to choose from.
- Worldwide coverage: Infatica proxies are available in over 195 countries, allowing users to access content from anywhere.
- Fast speeds: Infatica proxies provide fast speeds, allowing users to browse the web and download files without any lag.
- Reliable connections: Infatica proxies have a high uptime, ensuring users can connect to the internet with confidence when needed.
- Rotating proxies: Infatica offers rotating proxies, meaning the IP address changes frequently. This helps to protect user anonymity and prevent IP bans.
- Anonymous proxies: Infatica offers anonymous proxies, meaning the user’s IP address is hidden from the websites they visit. This helps to protect user privacy.
- Support for popular platforms: Infatica supports various platforms, including Windows, macOS, Linux, Android, and iOS. This makes it easy for users to use Infatica proxies with their favorite devices and applications.
==>> Get Infatica
8. Geonode – Unlimited Bandwidth ISP Proxies
Geonode is a relatively new proxy provider, but they have quickly gained a reputation for offering high-quality ISP proxies.
Their proxies are known for their fast speeds, global coverage, and affordability.
Geonode also offers a variety of features that make it a suitable choice for various use cases, including rotating proxies, dedicated IP addresses, and sub-user management.
Key Features:
- Unlimited bandwidth: Geonode offers unlimited bandwidth with all of its plans. This means you can use as much data as you need without worrying about incurring overage charges.
- No throttling: Geonode does not throttle its proxies. This means you can achieve the fastest possible speeds using their proxies.
- No logs: Geonode does not log any of your activity. This ensures that your privacy is protected.
9. Ninja Proxy – Anonymous ISP Proxies
Ninja Proxy is a well-known proxy provider that offers a variety of proxy types, including ISP proxies. Their ISP proxies are known for their high uptime, fast speeds, and global coverage.
Ninja Proxy also offers a variety of features that make it a suitable choice for various use cases, including rotating proxies, dedicated IP addresses, and sub-user management.
Key Features:
- Anonymous Browsing: Ninja Proxy ISP proxies allow you to browse the web anonymously. This is a suitable option for users who want to safeguard their privacy.
- Geo-spoofing: Ninja Proxy ISP proxies allow you to spoof your location. This is a suitable option for users seeking to access geo-restricted content.
- Easy to use: Ninja Proxy ISP proxies are easy to use. You can add them to your proxy list and start browsing.
READ ALSO: The Role Of Proxies For SEO And SMM Professionals
10. ProxyEmpire – Web Data Extraction Specialists
ProxyEmpire is a renowned proxy provider known for its expertise in web data extraction. While their main focus is residential proxies, they also offer ISP proxies specifically designed for data collection.
With an extensive pool of over 25 million IP addresses from Internet Service Providers worldwide, ProxyEmpire ensures high-speed and reliable connections for all your scraping needs. Their rotating ISP proxies provide added flexibility and anonymity.
Key Features:
- A large pool of over 25 million ISP IP addresses from global Internet Service Providers
- High-speed connections for efficient web data extraction
- Rotating ISP proxies for enhanced anonymity
- Comprehensive location coverage for geo-targeting
- Dedicated customer support to assist you with any inquiries
11. Proxyrack – Expanding Proxy Service Provider
Proxyrack is a fast-growing proxy service provider that offers high-quality ISP proxies at affordable prices.
With servers worldwide and over 2.5 million proxies in their pool, Proxyrack provides comprehensive location coverage and ensures reliable connections for various use cases.
Their clean IP pool, regularly updated to remove bad proxies, guarantees the highest quality and performance for browsing and data collection needs.
Key Features:
- Comprehensive location coverage with servers worldwide
- Large proxy pool with over 2.5 million proxies for reliable connections
- Clean IP pool for the highest quality and performance
- Affordable pricing plans suitable for individuals and businesses
- Dedicated customer support to assist you with any inquiries
READ ALSO: 8 Best Residential Proxy Providers
12. Rayobyte
Rayobyte ISP Proxies are another great option for high-quality ISP proxies.
They offer a range of features, including global coverage, high speeds, and dependable connections. Rayobyte also has a good reputation for customer support.
Key features:
- High-quality residential proxies
- Worldwide coverage
- Fast speeds
- Reliable connections
- Good customer support
- Wide range of features
13. SOAX

SOAX ISP Proxies are a good choice for users who need a large pool of proxies. They offer over 30 million residential IP addresses in over 195 countries.
SOAX also has a good reputation for uptime and customer support.
Key features:
- A large pool of residential IP addresses
- Worldwide coverage
- Fast speeds
- Reliable connections
- Good uptime
- Good customer support
Best ISP Proxies: Frequently Asked Questions
What is an ISP proxy?
An ISP proxy is a proxy server that uses IP addresses from residential ISPs. This means that ISP proxies are more difficult to block than data center proxies, as they appear to originate from real home users. ISP proxies are also typically faster than data center proxies, as they are not located in data centers.
What are the benefits of using ISP proxies?

There are many benefits to using ISP proxies, including:
- Increased anonymity: ISP proxies make it more difficult to track your online activity, as your IP address is constantly changing. This can be useful for online banking, file sharing, and browsing social media.
- Improved performance: ISP proxies can improve the performance of your online activities by caching frequently accessed websites and resources. This can be especially helpful for streaming videos and downloading large files.
- Greater availability: ISP proxies are typically more available than data center proxies, as they are not located in data centers. You are less likely to experience downtime when using ISP proxies.
What are the drawbacks of using ISP proxies?
There are a few drawbacks to using ISP proxies, including:
- Cost: ISP proxies can be more expensive than datacenter proxies.
- Consistency: ISP proxies may not be as consistent as datacenter proxies, as they depend on the underlying ISPs’ performance.
- Risk of abuse: ISP proxies are often used for malicious activities such as spam and phishing. This can result in your ISP’s proxy being blocked by websites and services.
How do I choose the best ISP proxy?

When choosing an ISP proxy, there are a few factors to consider, including:
- Price: ISP proxies can range in price from a few dollars to hundreds of dollars per month. Choosing a provider that offers a price point that fits your budget is important.
- Location: ISP proxies are available in various locations worldwide. Choosing a provider that offers proxies in the locations you need is important.
- Features: ISP proxies offer various features, including rotating IP addresses, sticky sessions, and unlimited bandwidth. Choosing a provider that offers the features you need is important.
- Reputation: Selecting an ISP proxy provider with a strong reputation is crucial. This will help to ensure that you get a reliable and high-quality service.
Where can I buy ISP proxies?
Several providers sell ISP proxies. Some of the most popular providers include:
Conducting thorough research before selecting a provider is crucial, as the quality of ISP proxies can vary significantly.
Final Thoughts On The Best ISP Proxies
Selecting the best ISP proxies is crucial for ensuring fast, reliable, and secure browsing and data collection.
By choosing a reputable proxy provider like Nodemaven, IPRoyal, MarsProxies, NetNut, and Infatica, you can enjoy the benefits of ISP proxies and unlock unlimited possibilities for your online activities.
Whether you need proxies for sneaker copping, web scraping, or other use cases, these top providers offer high-quality services and excellent customer support.
Take the time to evaluate your needs and choose the best ISP proxy provider that meets your requirements for a seamless online experience.
INTERESTING POSTS


![The Best ISP Proxies [Tested, Reviewed & Ranked] The Best ISP Proxies [Tested, Reviewed & Ranked]](https://secureblitz.com/wp-content/uploads/2023/09/Best-ISP-Proxies-768x402.jpg)








![15+ Best Proxy Service For 2026 [Tested, Reviewed & Ranked] 15+ Best Proxy Service For 2026 [Tested, Reviewed & Ranked]](https://secureblitz.com/wp-content/uploads/2023/07/Best-Proxy-Service-768x402.jpg)