Learn how modern data interpretation elevates leadership decisions in this post.
Leadership teams handle continuous streams of information, but most organizations struggle to turn this information into structured guidance. Data interpretation helps leaders read patterns across operations, customers, finances, and internal performance. It turns raw information into a clear direction. Many enterprises work with data analytics consulting teams to develop accurate readings of their data, so decisions stay aligned with real conditions rather than assumptions.
Modern leadership responsibilities require a deeper view of what drives outcomes. Data interpretation gives that view. It supports planning, priority setting, and internal alignment. When data is examined in a structured way, leaders gain a practical understanding of what is happening, what needs attention, and how different business functions move together.
Table of Contents
What problems arise when decisions are made without structured analytics?
Without structured analytics, organizations often experience blind spots. These blind spots grow slowly and affect major decisions. Leaders may think they understand performance, but the details behind that performance stay hidden.
Common issues include:
- Reports that do not match operational realities
- Delayed or inconsistent data updates
- Confusion about which metrics matter most
- Decisions influenced by incomplete or outdated numbers
- Difficulty linking outcomes to actions across departments
These issues do not stay isolated. They affect hiring, budgeting, growth planning, risk management, and customer outcomes. Teams spend time fixing recurring problems instead of preventing them. The absence of a structured analytical foundation reduces the accuracy of leadership decisions.
How does an analytics assessment reveal organizational issues and opportunities?
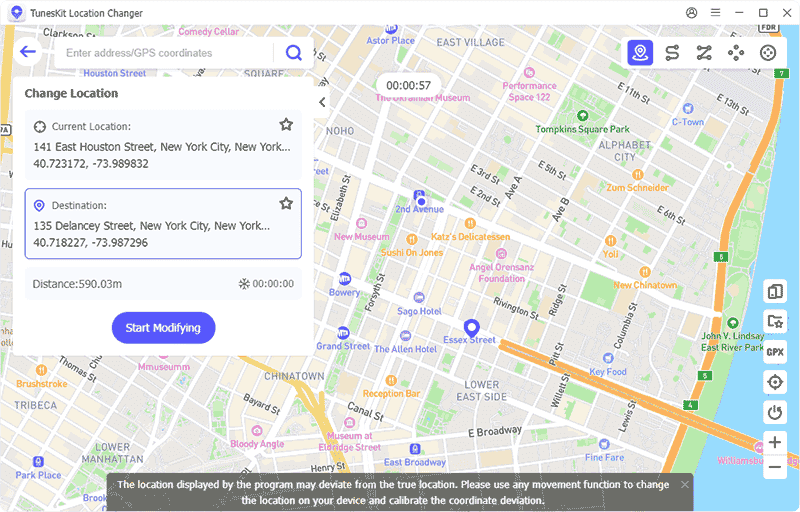
Enterprises often use an analytics assessment framework, supported by Data Analytics services, to understand the condition of their data systems.. This framework helps locate technical issues, process gaps, and reporting limitations. It guides the review of data sources, quality standards, operational workflows, reporting dashboards, and alignment with strategic objectives.
A typical assessment covers the following areas:
| Assessment Area | What It Examines | How It Helps Leadership |
| Data quality | Missing data, outdated values, inconsistent entries | Reduces errors in strategic planning |
| Data structure | Naming rules, definitions, categorization | Avoids misinterpretation of metrics |
| System integration | Flow between tools and departments | Supports unified reporting |
| Dashboard and reporting reliability | Timeliness, clarity, accuracy | Helps leaders make decisions quickly |
| Governance maturity | Ownership, protocols, audit history | Protects long-term data trust |
Leaders use these findings to decide whether they need cleanup efforts, new reporting models, updated systems, or stronger governance. The clarity from an assessment prevents random changes and directs attention to the areas that matter.
READ ALSO: How Cloud Consulting Services Guide Companies Through Digital Change
How does consulting-led insight design support leadership decisions?
Many organizations partner with data analytics consulting specialists to build structured insight processes. One of the core tasks is developing an executive insight design model. This design approach organizes how information reaches leadership teams, how dashboards are shaped, and how recurring reporting cycles function.
A consulting-led insight design normally includes:
- Defining each leadership question that needs a reliable answer
- Selecting the correct data sources to support those questions
- Building dashboards that show precise metrics instead of broad summaries
- Establishing fixed reporting cadences
- Creating protocols for reviewing results and assigning accountability
This structure helps leadership view the same metrics consistently across quarters. It removes noise from reporting and keeps attention on results that tie directly to strategic planning.
During this process, consulting teams often reference external findings to reinforce decision patterns. For example, a study referenced by Harvard Business School Online reports that organizations using structured data processes make 3 times faster and more confident decisions. This aligns with what many leaders observe when insight design becomes systematic and predictable.
How do real decision scenarios change when analytics guide them?
Analytics-based interpretation changes outcomes in very direct ways. Below are examples that match common enterprise situations.
Scenario: Budget planning for marketing teams
Leadership faces multiple requests from different marketing channels. Without analytics, decisions depend on personal judgment or incomplete reporting. With a structured process built through data analytics consulting, leadership can review channel-level cost trends, lead quality, customer value scores, and conversion reliability. This leads to a budget distribution that matches real performance.
Scenario: Workforce and capacity allocation
Many operations teams record workload, cycle times, and error rates, but these numbers stay unused. When leaders apply structured analytics, they can see shortages, rising workloads, or areas with unused capacity. This supports informed decisions about hiring, workflow adjustments, or internal reorganization.
Scenario: Product performance visibility
Leadership can view usage frequency, customer satisfaction, churn triggers, and feature performance. These metrics guide decisions about product roadmaps, engineering allocations, and customer support plans.
Scenario: Risk assessment for lending or financial services
Historical repayment patterns, demographic segmentation, and behavioral signals allow companies to define credit policies with more precision. Leadership decisions about approval criteria and pricing become grounded in consistent patterns rather than opinions.
Here is a short checklist that helps readers understand decision improvements:
- Confirm which metrics directly influence the decision
- Validate that the data behind these metrics is complete
- Ask whether the reporting format supports clear interpretation
- Check whether the decision aligns with long-term objectives
- Review how outcomes will be tracked after the decision
This checklist helps maintain clarity and structure before leadership finalizes high-impact choices.
What guidance helps organizations begin a consulting engagement?
Before starting a consulting project, leaders benefit from a clear preparation stage. The following points help streamline the engagement:
- Document core business questions that leadership needs answered
- Prepare a list of all current data sources across departments
- Identify inconsistent reporting or unclear metrics
- Make sure each department assigns a point of contact for data clarification
- Confirm dashboard access, tool permissions, and existing reports
- Define success metrics for the consulting project
- Decide how insights will be used after the engagement ends
These steps prepare the internal environment for consulting efficiency. They also ensure that data analytics consulting teams understand organizational goals without delay.
Key takeaways for starting a consulting engagement
- A structured analytical environment reduces uncertainty
- An analytics assessment framework reveals the real state of data systems
- A strong executive insight design process gives leadership consistent clarity
- Relevant, decision-oriented metrics support accurate actions
- Clear reporting cycles and governance rules maintain long-term reliability
- Engagements work best when leadership prepares goals, data sources, and internal responsibilities
INTERESTING POSTS