Nearshore software development has become a popular outsourcing option in recent years for companies seeking to enhance their software development capabilities while maintaining proximity to their home country.
Due to its thriving tech sector and skilled labor pool, Mexico has become a favored choice for nearshore software development.
This book offers valuable insights into nearshore software development in Mexico, its advantages, factors to consider, and how it can be a wise decision for companies wishing to scale their software projects successfully.
Table of Contents
How Does Nearshore Software Development Work?
It is referred to as “nearshore software development in Mexico” when software development work is outsourced to nearby or adjacent countries, often in the same or similar time zones.
It is a tactical alternative to conventional offshore outsourcing, offering several benefits, including reduced linguistic and cultural barriers, enhanced teamwork, and faster response times.
Benefits of Nearshore Software Development in Mexico
Proximity and Time Zone Alignment
One of the critical benefits of nearshore software development in Mexico is its proximity to the United States and Canada. The proximity ensures greater cultural familiarity and facilitates in-the-moment communication. Being in the Central or Pacific Time Zones makes agile development techniques possible.
Skilled and Educated Workforce
Mexico’s IT sector has experienced substantial expansion, creating a pool of highly qualified software developers and IT specialists. Since many Mexican programmers hold advanced degrees, possess solid technical backgrounds, and are fluent in English, communication is straightforward.
Cost-Effectiveness
In the field of nearshore software development, Mexico provides a cost-competitive edge. Although the rates may be higher than those in some offshore locations, they are often less expensive than those in the US, allowing businesses to save costs without compromising quality.
Cultural Affinity
Mexico, the United States, and Canada share cultural affinities, which makes it simpler for enterprises to match their project objectives and collaborate successfully with Mexican development teams. Collaboration and teamwork can be facilitated by having the same cultural values.
Intellectual Property Protection
Mexico has strengthened its intellectual property protection laws, providing greater assurance to businesses concerned about protecting their sensitive information and proprietary software.
Considerations for Nearshore Software Development in Mexico
Communication
Even though there are many English speakers in Mexico, evaluating the development team’s language skills is crucial to ensure efficient communication. Choose a partner who values open and honest communication.
Time Zone Management
Although Mexico is in the same or a nearby time zone as the United States and Canada, ensure a time difference exists so that real-time collaboration can occur, especially if your project requires a quick turnaround and immediate response.
Cultural Fit
Analyze how well the nearshore development team fits with your company’s culture. Shared business ethics and cultural norms can foster productive collaboration and reduce the likelihood of miscommunication.
Legal and Security Considerations
Know the legal and regulatory requirements, such as those relating to intellectual property rights and data protection legislation, before engaging in nearshore software development in Mexico.
Quality Assurance
Find a Mexican nearshore partner with a history of producing high-caliber software solutions. Request case studies, client endorsements, and references to verify their expertise.
READ ALSO: 12 Companies For Outsourcing Web Development [MUST READ]
Nearshore Software Development: Frequently Asked Questions
What are the advantages of nearshore development compared to other options?
- Time zone overlap: Shared time zones facilitate smoother communication and collaboration, minimizing delays and misunderstandings.
- Cultural similarity: Sharing cultural norms and business practices can improve project understanding and alignment.
- Reduced language barriers: Communication is often more accessible due to shared or similar languages, leading to faster problem-solving.
- Cost-effectiveness: Nearshore locations often offer competitive rates while maintaining high-quality talent, making them a viable alternative to outsourcing destinations.
- Travel convenience: Closer proximity allows for more accessible in-person meetings and team building, fostering stronger relationships.
What are the potential challenges of nearshore development?
- Talent pool size: Depending on the specific location and technology stack, the talent pool may be smaller than that of some offshore destinations.
- Vendor selection: Identifying and vetting qualified nearshore providers requires careful research and due diligence.
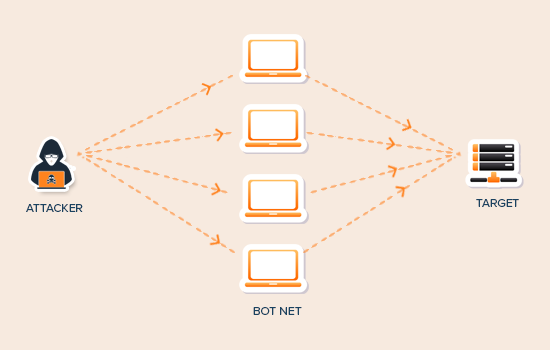
- Data security and privacy: Ensuring data security and compliance with border regulations requires careful planning and implementation.
- Cultural differences: While proximity can minimize some cultural differences, understanding and navigating them require sensitivity.
- Project management complexity: Managing a team in a different country requires effective communication and collaboration tools.
READ ALSO: What Are the Benefits of Outsourcing to an IT Support Company?
How do I find a reliable nearshore development partner?
- Research the nearshore region, considering factors such as talent availability, cost structure, and cultural compatibility.
- Review provider portfolios and references: Look for experience in your industry and similar projects.
- Evaluate communication and project management practices: Ensure clear communication channels and established methodologies.
- Understand security and data privacy protocols: Verify compliance with relevant regulations and robust security measures.
- Conduct pilot projects or proof-of-concept engagements: Assess the provider’s capabilities and team fit before committing to larger projects.
How much can I expect to save compared to other options?
Cost savings can vary depending on the project, technology stack, and chosen nearshore location.
Generally, nearshore development offers savings between 15% and 30% compared to onshore development, but might be slightly more expensive than some offshore options.
However, the benefits of time zone overlap, cultural proximity, and potentially more accessible travel can outweigh the cost difference for some businesses.
Conclusion
Nearshore software development in Mexico offers an attractive option for businesses seeking to scale their coding projects while maintaining proximity, cultural affinity, and cost-effectiveness.
Businesses can leverage Mexico’s educated and skilled population to access a talent pool with the necessary abilities and technical expertise to develop exceptional software solutions.
As you embark on your nearshore software development journey, select a reliable and knowledgeable partner in Mexico that aligns with your project objectives, communication needs, and cultural fit to ensure a successful and profitable engagement.
INTERESTING POSTS
- How To Rent A Cheap Car In Various Countries
- Quality Assurance: Definition And Explanation
- Property Maintenance Essentials: Keeping Your Rental in Top Shape
- Top 8 Considerations To Choose The Right VPN Service
- 4 Essential Tips to Improve Home Security
- The Top 5 Benefits Of Using Outsourcing Services
- Managing Remote Teams: Best Practices for Team Extension and Outsourcing