This post will reveal nine practical tips for protecting your data from phishing attacks. Read on!
One of the biggest cybersecurity concerns that almost every IT professional harbours is: How do I stop cyber-attacks?
Hackers rely heavily on phishing to gain unauthorized access to a business network and steal sensitive data. It is the most common and damaging type of cyber-attack. Due to a lack of awareness of the telltale signs of phishing, hundreds of big and small businesses fall victim to it.
According to findings, “Phishing attacks account for over 80% of reported security incidents.”
It’s no secret that phishing attacks have become increasingly potent. Furthermore, with COVID-19 prompting organizations to transition to remote work, the number of attacks has increased, compromising data privacy.
Fortunately, it is possible to identify and thwart phishing scams.
This post outlines nine IT security measures to help you prevent phishing and protect your business assets and data.
READ ALSO: Data Security Protection Tips That Would Help Save Your Money
Table of Contents
9 Effective Tips For Preventing Phishing Attacks On Your Data
Understand What Phishing Looks Like
Phishing techniques evolve, but they all share a few similarities that can be identified if you know what signs to look for. The techniques range from classic email phishing to more inventive ways, such as cold calling on the phone. They all have the same malicious intent: stealing the user’s details.
If you’re serious about staying on top of the latest phishing tactics and understanding their signs, a wealth of information is available online. You must use these resources to proactively educate yourself about how cybercriminals target and attack their victims.
Furthermore, sharing your learning with employees through a well-planned cybersecurity training program would be beneficial. This will help your employees stay on guard against and thwart such attacks should they be used to steal data.
READ ALSO: How URL Spoofing Makes Benign Applications Deadly
2. Steer Clear of Clicking on Random Links
It is a good idea to avoid clicking on suspicious links embedded in emails and text messages, even if you receive them from a (seemingly) known sender. To stay safe, hover your mouse over the link to see if it has a known link destination, but do not click on it. Please bring this event to the attention of your IT personnel immediately for further action.
Remember, sometimes, the fake URL destination can look identical to a genuine website’s URL. It is set up to record keystrokes or steal sensitive information. So, never lower your guard. If you must douse your curiosity, access the original website directly or via your search engine instead of clicking on the malicious link.
READ ALSO: What Are Phishing Scams And How You Can Avoid Them?
3. Invest in the Latest Anti-Phishing Software
Phishing has been a persistent threat to data security for a considerable time. Emails are the most common means by which attackers deliver malware. So, what’s the solution to it?
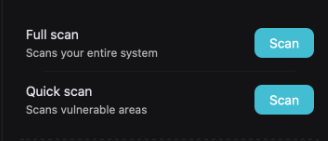
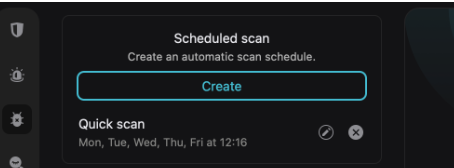
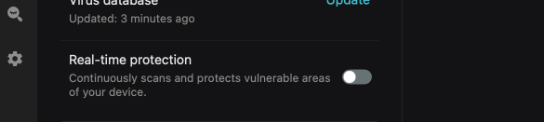
Think advanced anti-phishing software! The influx of various anti-phishing software/services has equipped users and organizations with a cybersecurity solution to prevent phishing attacks. Anti-phishing software is an effective layer of protection that impedes malicious attacks and safeguards your sensitive business data.
4. Avoid Revealing Information on Malicious Websites
Unsecured websites are malicious, so you should never have sensitive information on them or download files from them. If you visit a website and its URL doesn’t start with “HTTPS,” or if you don’t see a closed padlock icon next to it, you should know that the website does not have a security certificate.
READ ALSO: Session Hijacking: Everything You Need To Know
Even a website with a simple “HTTP” URL may be unsecured, allowing it to gather your data for phishing purposes. Even if it isn’t, it’s always better to be safe than sorry and avoid such websites.
5. Update Your Passwords Regularly
It is advisable to regularly change your system passwords to prevent an attacker from gaining access to your emails, payment gateways, and login portals. If you’re on a hacker’s list of potential targets, they may attempt to access your account multiple times. This is why it’s essential to change your password frequently. Doing so reduces the risk of unauthorized access and phishing attacks.
In short, adding an extra layer of protection that is regularly updated prevents ongoing attacks and locks out potential attackers.
6. Never Ignore Security Updates
Receiving numerous updates and system messages frequently can be frustrating. However, you should pay heed to them for your own sake.
Software manufacturers continually fix bugs and make improvements to their products. They regularly release network security updates and patches to keep you ahead of evolving cyber-attacks, protecting your network, systems, and data from potential threats.
In other words, updating your software is crucial to enhancing the security and integrity of your systems and data.
READ ALSO: Preventing Cyber Attacks with Domain Protection and Threat Takedown Solutions
7. Install Firewall
Among our tips for preventing phishing attacks is to install a Firewall.
When you use the internet, several data packets get exchanged between your device and various servers. Between these two points, there is a space that scammers utilize to infiltrate your devices. A firewall monitors this space to ensure it is safe.
READ ALSO: How to Securely Send Sensitive Information Over the Internet
Firewalls are an effective means of preventing external cyberattacks. They act as shields between your computers and malware. You can enhance your cybersecurity and reduce the likelihood of unauthorized access to your data by installing both a desktop firewall and a network firewall.
8. Block Pop-ups
Pop-ups are not only annoying but also dangerous. They can be linked to malware as a part of a phishing attack.
Typically, a pop-up has a “Close” or “Cancel” button in the top right-hand corner. While you may click on this button to remove the pop-up, please note that doing so does not guarantee its dismissal. The link embedded in this button can redirect you to a malicious website or lead to the download of ransomware on your system.
The only way to stop them from “popping up” is by installing a robust pop-up blocker or availing professional services from an expert MSP who can fortify your data security measures.
9. Use a Robust Data Security Platform
Data security platforms alert IT authorities about unusual behaviour and downloading suspicious files. This platform enables a faster response to these situations, thereby preventing potential attacks or data breaches.
READ ALSO: How To Detect Email Phishing Attempts (Like A Geek!)
Even if cybercriminals give unauthorized access to sensitive information, data security platforms can help you identify the compromised system. This, in turn, will empower you to take preventive action to minimize further damage.
Wrapping Up
So, those are the tips for preventing phishing attacks.
While phishing tactics are becoming increasingly potent, you can protect yourself by taking timely preventive measures to safeguard your digital assets and data. Understanding the risks associated with phishing attacks and identifying the typical signs can go a long way in keeping you protected from them.
Follow the above tips to maximize your security measures, thereby protecting your data and overall IT infrastructure from phishers and other cybercriminals.
SUGGESTED READINGS
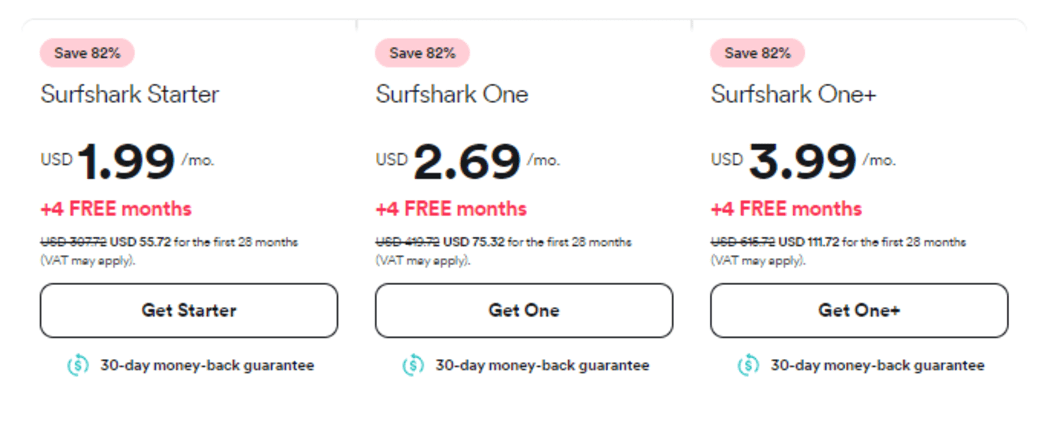
- Should I Use A Free VPN or a Premium VPN in 2021?
- WordPress Hardening: 7 Ways to Harden Your Website Security
- 7 Top Cyber Security Plans for Small Businesses
- Top 5 Pro Tips About Providing Cybersecurity For Business
- How To Secure Devices Against Phishing Emails
- 10 Most Common Cyber Threats [MUST READ]
- 5 Secure Online Payment Services to Consider
- 6 Ways To Protect Your Business From Phishing Attacks












![Is Surfshark Antivirus For Mac Worth It? [Here’s the ANSWER] Is Surfshark Antivirus For Mac Worth It? [Here’s the ANSWER]](https://secureblitz.com/wp-content/uploads/2024/01/Is-Surfshark-Antivirus-For-Mac-Worth-It-Heres-the-ANSWER-768x402.jpg)