Digital single-lens reflex cameras (DSLRs) have long been the workhorse of professional and serious amateur photographers. Renowned for their image quality and versatility, DSLRs have captured countless iconic moments throughout history.
However, a recent discovery by Israeli cyber experts has shaken the foundation of DSLR security, raising concerns about the vulnerability of millions of cameras worldwide.
The team, affiliated with Claroty, a cybersecurity firm specializing in operational technology (OT), identified critical security flaws within the firmware of several major DSLR brands. If exploited by malicious actors, these vulnerabilities could grant them unauthorized access to a camera’s core functionalities.
A Breach of Focus: The Nature of the Digital Cameras Vulnerabilities
The specific details of the vulnerabilities haven’t been publicly disclosed to prevent attackers from exploiting them. However, Claroty researchers have hinted at several potential entry points.
One possibility involves vulnerabilities in the communication protocols between the camera and its removable storage devices, such as SD cards. A hacker could inject malicious code into a compromised SD card, which the camera would execute upon insertion.
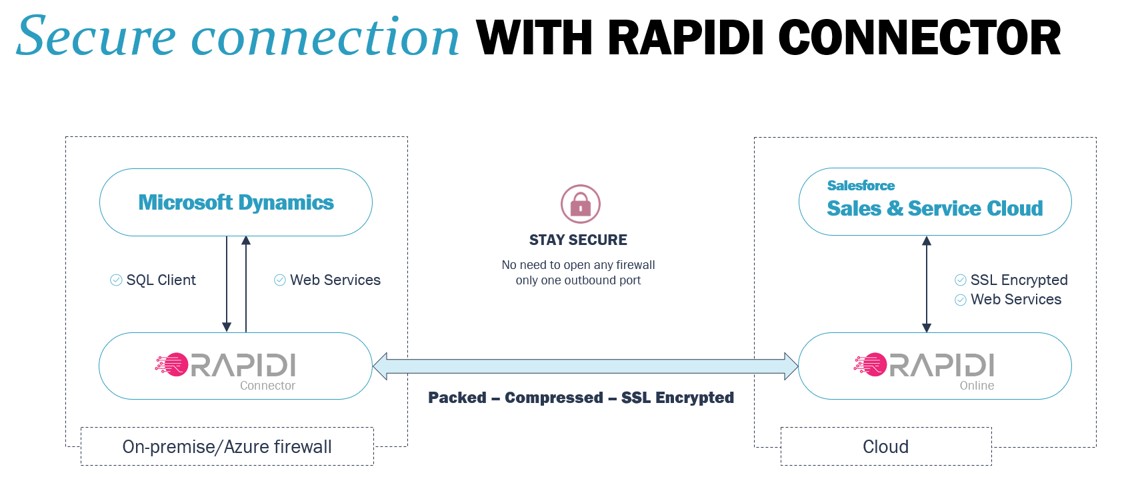
Another area of concern lies in the camera’s Wi-Fi connectivity. If not properly secured, a hacker could gain remote access to the camera by intercepting its wireless communication. This could allow them to steal captured images and videos in real time, alter camera settings remotely, or even use the camera as a vantage point for cyber espionage.
- READ ALSO: Best VPN For 2023
The Bigger Picture: Potential Impact and Ramifications
The ramifications of these vulnerabilities extend far beyond personal photography via digital cameras. Professional photographers who rely on DSLRs for their livelihood could see their sensitive work exposed if their cameras are compromised.
News outlets and journalists covering sensitive events could also be targeted, with attackers potentially accessing incriminating or confidential footage.
Furthermore, the potential for these vulnerabilities to be weaponized for industrial espionage is a significant concern. Attackers could target DSLRs used in research facilities, manufacturing plants, or government buildings to steal sensitive information or disrupt critical operations.
READ ALSO: Phone Photography: Photography Tips On The Phone
A Call to Arms: Mitigating the Risks and Securing the Future of DSLRs
The discovery of these vulnerabilities underscores the growing need for robust cybersecurity measures within photography. Here’s what various stakeholders can do to mitigate the risks:
Camera Manufacturers: DSLR manufacturers must prioritize firmware updates that address the identified vulnerabilities. Additionally, implementing secure coding practices and penetration testing throughout the development lifecycle can help prevent future security flaws.
Photographers: Always ensure your camera’s firmware is up to date. When connecting to Wi-Fi, use strong passwords and avoid public or unsecured networks. Disabling Wi-Fi connectivity when not in use and exercising caution when using third-party accessories or software is also advisable.
Security Researchers: Continued research and collaboration between cybersecurity firms and camera manufacturers are crucial to identify and address emerging threats. Responsible disclosure practices, where vulnerabilities are reported directly to vendors before public disclosure, are essential to minimize the exploitation window.
- READ ALSO: Best Antivirus For 2023
FAQs: DSLR Security Concerns
Are all DSLRs vulnerable to these security flaws?
The specific models identified by the Israeli researchers haven’t been publicly disclosed. However, the research suggests that a lack of proper authentication measures might be present in various DSLR models.
What information could be at risk if a hacker gains control of my DSLR?
The primary concern is unauthorized access to captured images and videos stored on the camera’s memory card. Additionally, depending on the vulnerability, camera settings could be manipulated, potentially ruining photos.
What steps can I take to protect my DSLR from cyberattacks?
- Keep your camera firmware updated with the latest security patches from the manufacturer.
- Avoid connecting your camera to untrusted Wi-Fi networks.
- Use strong passwords and enable two-factor authentication if available on your camera model.
- Consider encrypting images stored on the memory card (if your camera offers this option).
What should I do if I suspect my DSLR has been compromised?
If you suspect unauthorized access, it’s best to assume the worst. Disconnect the camera from any network and remove the memory card. Consider having a security professional examine the camera for any lingering malware.
READ ALSO: Outdoor Security Camera for Your Home
What’s the future of DSLR security?
Continuous vigilance is key. Manufacturers should prioritize security updates and explore bug bounty programs. Collaboration between cybersecurity experts and photographers is crucial for raising awareness and developing best practices.
The Road Ahead: A More Secure Future for Photography?
The discovery of these vulnerabilities is a wake-up call for the photography industry. While DSLRs remain a powerful tool for photographers, their security posture must be addressed.
By working together, camera manufacturers, security researchers, and photographers can ensure a more secure future for photography, where capturing precious moments doesn’t come at the cost of compromising sensitive data.
It’s important to note that this is a developing story. As more details about the vulnerabilities emerge, we can expect further action from camera manufacturers and security researchers.
In the meantime, photographers should remain vigilant and take steps to secure their cameras.
What are your fears about using digital cameras?
INTERESTING POSTS
- Best Antivirus For 2022
- Best VPN For 2022
- 7 Best VPNs for 8 Ball Pool
- Full Virtual Shield VPN Review
- Identity Theft Is Not A Joke, Jim [MUST READ Parody]
- Best Paid Antivirus According To Reddit Users
- 10 Best VPNs According To Quora Users
- Is Windows Defender Enough for 2024?
- Android SLocker Capitalizes on Coronavirus Pandemic to Hijack Android
- How to Detect Email Phishing Attempts
- Interview With Michael Bruemmer, Vice President of Experian Data Breach Resolution Group and Consumer Protection
- Best Home Security Cameras According To Reddit Users