Learn what rotating proxies are, how they work, their types, benefits, and top use cases. Compare Decodo, Oxylabs, Webshare, Mars Proxies, and IPRoyal for 2025.
In 2025, data is gold — but the web isn’t always friendly to data collectors. Whether you’re scraping sites, automating accounts, or gathering market intelligence, one problem keeps surfacing:
IP bans.
That’s where rotating proxies come in — your invisible army of constantly changing IPs that keep you anonymous, unblock access, and make your operations look completely human.
This comprehensive guide breaks down:
- What rotating proxies are
- How they work
- The different types available
- Best use cases
- And the top providers for 2025 include Decodo, Oxylabs, Webshare, Mars Proxies, and IPRoyal.
🧭 What Are Rotating Proxies?
Rotating proxies are proxy servers that automatically change your IP address after each request or at a set time interval.
Instead of using one static IP, they switch between millions of IPs, giving you:
- Unlimited anonymity
- Zero bans
- Continuous, stealthy access
🧩 Example:
You’re scraping 10,000 product pages on Amazon.
A normal proxy gets you blocked after a few hundred requests.
But a rotating proxy network switches IPs every few seconds — so to Amazon, every request looks like it’s coming from a new user.
💡 In short: Rotating proxies = your identity shapeshifter on the internet.
⚙️ How Rotating Proxies Work
Rotating proxies rely on proxy pools — massive networks of IPs that automatically rotate via algorithms or user-defined rules.
🔄 Two Main Rotation Methods:
- Time-Based Rotation
- IP changes every few minutes or seconds.
- Example: 1 IP every 60 seconds.
- Request-Based Rotation
- IP changes per request made.
- Example: Each API call uses a new IP.
These rotations are handled by the provider’s gateway, so users just connect once — the provider does all the switching in the background.
🧠 Why IP Rotation Matters
Modern websites use anti-bot technologies (like Cloudflare, Akamai, and PerimeterX). These detect abnormal request patterns from a single IP.
Rotating proxies prevent detection by:
- Disguising your identity
- Randomizing your footprint
- Mimicking human browsing patterns
This is crucial for:
- Web scraping
- Market monitoring
- Ad verification
- Automation
Without rotation, even the best proxies eventually get flagged or banned.
🧩 Types of Rotating Proxies
Let’s break down the five main categories of rotating proxies you’ll encounter in 2025.
1. 🏠 Rotating Residential Proxies
These use IPs from real household devices (assigned by ISPs).
Pros:
- High trust level
- Undetectable by anti-bot systems
- Access to geo-blocked content
Cons:
- More expensive
- Slower than datacenter proxies
Best Providers:
- Decodo – offers dynamic residential rotation across 100+ countries
- Oxylabs – top-tier residential pools with 100M+ IPs
- Mars Proxies – budget-friendly plans with flexible rotations
2. 🏢 Rotating Datacenter Proxies
IPs generated from cloud servers or virtual machines.
Pros:
- Extremely fast
- Scalable and affordable
- Ideal for non-sensitive scraping
Cons:
- Easier to detect by strict websites
Best Providers:
- Decodo Datacenter Suite – advanced rotation control + API support
- Webshare – low-cost, high-speed proxy pools
- IPRoyal – stable and easy for developers
3. 📱 Rotating Mobile Proxies
IPs assigned from 3G/4G/5G mobile carriers.
Pros:
- Nearly undetectable
- Perfect for social media and ad testing
Cons:
- High cost per GB
- Limited availability
Best Providers:
- Oxylabs Mobile Network – powerful carrier-grade IPs
- Decodo Mobile Proxies – auto-rotating mobile gateways for social automation
4. 🌐 Backconnect (Gateway) Proxies
Instead of managing IPs manually, you connect to one gateway endpoint that rotates IPs internally.
Pros:
- Simplifies management
- Best for high-volume scraping
Cons:
- Limited manual control
Best Providers:
- Webshare Backconnect System
5. ⚡ Custom or Rotating Hybrid Proxies
Combine residential + datacenter + mobile IPs dynamically.
Perfect for enterprise-grade stealth.
Pros:
- Adaptive IP switching
- Maximum uptime
- One API for all types
Best Providers:
- Oxylabs Residential Proxies
🧮 Technical Overview: How Rotation Logic Works
A rotating proxy system is powered by:
- Load balancers – distribute requests
- IP pools – millions of live IPs
- Rotation algorithms – manage IP lifespan
Example Process:
- You send a request to Decodo’s gateway.
- The gateway assigns a random residential IP.
- Once the request completes, the IP is rotated.
- A new IP is assigned for the next request.
This makes detection nearly impossible — you appear as 10,000 unique users from around the world.
🌐 Key Benefits of Rotating Proxies
Let’s unpack the major advantages in 2025:
🧱 1. Enhanced Anonymity
Each request comes from a new IP → tracking becomes impossible.
⚡ 2. Unlimited Scalability
You can send thousands of simultaneous requests without throttling.
🧠 3. Higher Success Rates
Automatic IP rotation prevents bans on sensitive targets like Amazon, Google, or LinkedIn.
💸 4. Cost Efficiency
Instead of buying thousands of static IPs, one rotating plan gives you millions.
🕵️ 5. Geo-Targeting Freedom
Change location automatically between countries or cities for localized data.
💻 6. Plug-and-Play Integration
Providers like Decodo, Oxylabs, and Webshare offer single-endpoint systems compatible with tools like:
- Scrapy
- Puppeteer
- Selenium
- BeautifulSoup
- Apify
🧰 Common Use Cases for Rotating Proxies
🛒 1. E-Commerce Price Monitoring
Track prices across Amazon, Walmart, or AliExpress without bans.
- Best: Decodo Residential or Oxylabs Proxies
📈 2. SEO & SERP Tracking
Collect global search results for hundreds of keywords safely.
- Best: Webshare or IPRoyal Datacenter Rotators
🧠 3. Data Mining & Market Research
Gather market intelligence from public websites.
- Best: Decodo or Mars Proxies for affordability
📲 4. Social Media Automation
Run multiple accounts safely across Facebook, Instagram, and X (Twitter).
- Best: Decodo Mobile or IPRoyal Rotating Residential
🔍 5. Ad Verification
Verify global ad placements in different regions.
- Best: Oxylabs or Decodo Residential Rotation
🎮 6. Gaming and Ticket Bots
Avoid IP bans on limited-release websites.
- Best: Mars Proxies for sneaker bots and event monitoring
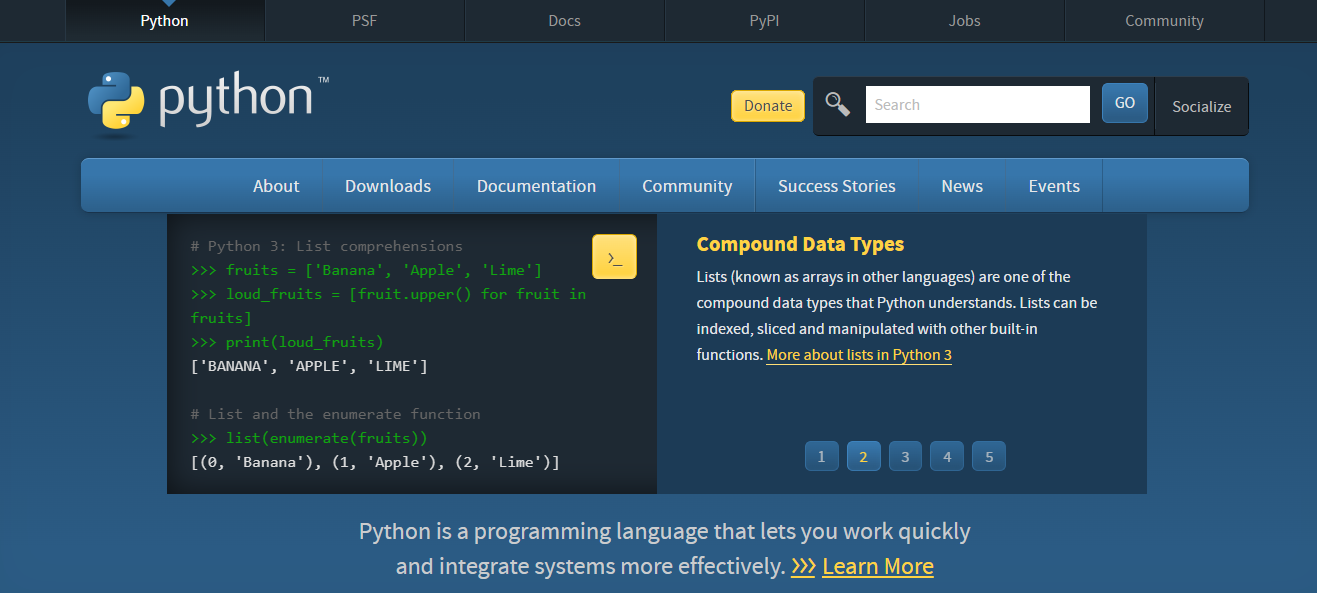
⚙️ Setup Example: Using Rotating Proxies in Python
Here’s a quick code snippet using Decodo’s rotating gateway:
import requests
proxies = {
"http": "http://username:password@gw.decodo.net:8000",
"https": "http://username:password@gw.decodo.net:8000"
}
for i in range(5):
response = requests.get("https://httpbin.org/ip", proxies=proxies)
print(response.json())
Each loop prints a new IP address, showing live rotation in action.
🧩 Combining Rotating and Static Proxies
Many professionals use hybrid proxy workflows:
- Static IPs for login sessions
- Rotating IPs for data extraction
Example Setup:
- Login to Instagram → static residential proxy
- Scrape user data → rotating residential proxy
Platforms like Decodo, Oxylabs, and IPRoyal allow you to mix these seamlessly.
⚖️ Legal & Ethical Use of Rotating Proxies
Remember:
- Only scrape publicly available data
- Respect robots.txt policies
- Never use proxies for illegal or malicious activities
- Keep rotation within reasonable intervals
Providers like Oxylabs and Decodo comply with GDPR, CCPA, and international data privacy standards.
📚 Case Study: How a Marketing Agency Scaled Data Collection with Decodo
A marketing analytics firm needed to collect ad data from 500 websites daily.
Their static proxies kept getting blocked.
Solution:
They switched to Decodo Rotating Residential Proxies with AI-based rotation.
Result:
✅ 99.8% uptime
✅ 3× faster scraping speed
✅ 0 bans after 60 days
💎 Lesson: Smart rotation and hybrid routing are the future of sustainable data operations.
🧭 Best Practices When Using Rotating Proxies
- Use realistic request intervals – don’t overload targets.
- Switch user agents frequently.
- Combine proxies with CAPTCHA solvers for smoother runs.
- Rotate headers and cookies to mimic human patterns.
- Monitor proxy health using dashboards from Decodo or Webshare.
🏁 Conclusion: Rotating Proxies = Your Key to a Boundless Web
In 2025, rotating proxies are not optional — they’re essential for scaling data operations, marketing research, and web automation without interruptions.
Summary:
- Residential rotating = stealth
- Datacenter rotating = speed
- Hybrid rotating (Decodo / Oxylabs) = best of both worlds
When choosing a provider:
- Pick Decodo for hybrid, smart automation
- Choose Oxylabs for enterprise-scale reliability
- Try Webshare or Mars Proxies for budget projects
- Use IPRoyal for developer-friendly APIs
Together, these platforms form the new ecosystem of dynamic, AI-driven web access.
✅ Quick Comparison Recap
| Use Case | Recommended Provider | Rotation Type |
|---|---|---|
| E-commerce Scraping | Decodo, Oxylabs | Residential Rotating |
| SEO Monitoring | Webshare, IPRoyal | Datacenter Rotating |
| Social Automation | Decodo, Mars | Mobile / Hybrid Rotating |
| Ad Verification | Oxylabs, Decodo | Residential Rotating |
| General Data Mining | Decodo | Hybrid Smart Rotation |
INTERESTING POSTS
- The Best Datacenter Proxies
- Top Proxy Service Providers in 2025: Unlocking Internet Freedom
- Best Residential Proxies In 2025: A Comprehensive Guide
- Day Trading Crypto For Beginners Using Trading Bots
- 4 Differences Between Residential Proxies and Datacenter Proxies
- Top Proxy Service Providers in 2025: Unlocking Internet Freedom
- The Best Proxy Services for Legitimate Business Purposes
- How to Set Up an MCP Server (2025 Guide)
- How to Train a GPT Model — Methods, Tools, and Practical Steps
- Residential vs Datacenter Proxies — Which Should You Choose?
- Proxy for Scraping Amazon: The Ultimate Guide (2025 Edition)