Want the best IoT connectivity distributors for system integrators? Read on.
Choosing an IoT SIM distributor can make—or break—your deployment. Pick well and every sensor stays online; pick poorly and field devices rack up fees or fall silent. After stress-testing 12 globally active distributors between 2023 and 2026, interviewing integration engineers, and scoring each vendor across seven weighted criteria, we narrowed the list to six partners that excel in reach, reliability, and integrator-grade support. Use this guide to match the right provider to your project, avoid budget-wrecking surprises, and keep every device talking.
How we selected and scored the six stand-outs
We started with a simple question: Which IoT connectivity distributors keep system integrators out of trouble, on budget, and compliant?
To find out, we pulled data from analyst reports, vendor datasheets, Reddit post-mortems, and field-engineer interviews. Each candidate had to sell multi-country IoT SIMs, publish a usable API, and show momentum between 2023 and 2026. We removed pure satellite providers, single-nation carriers, and “coming soon” startups.
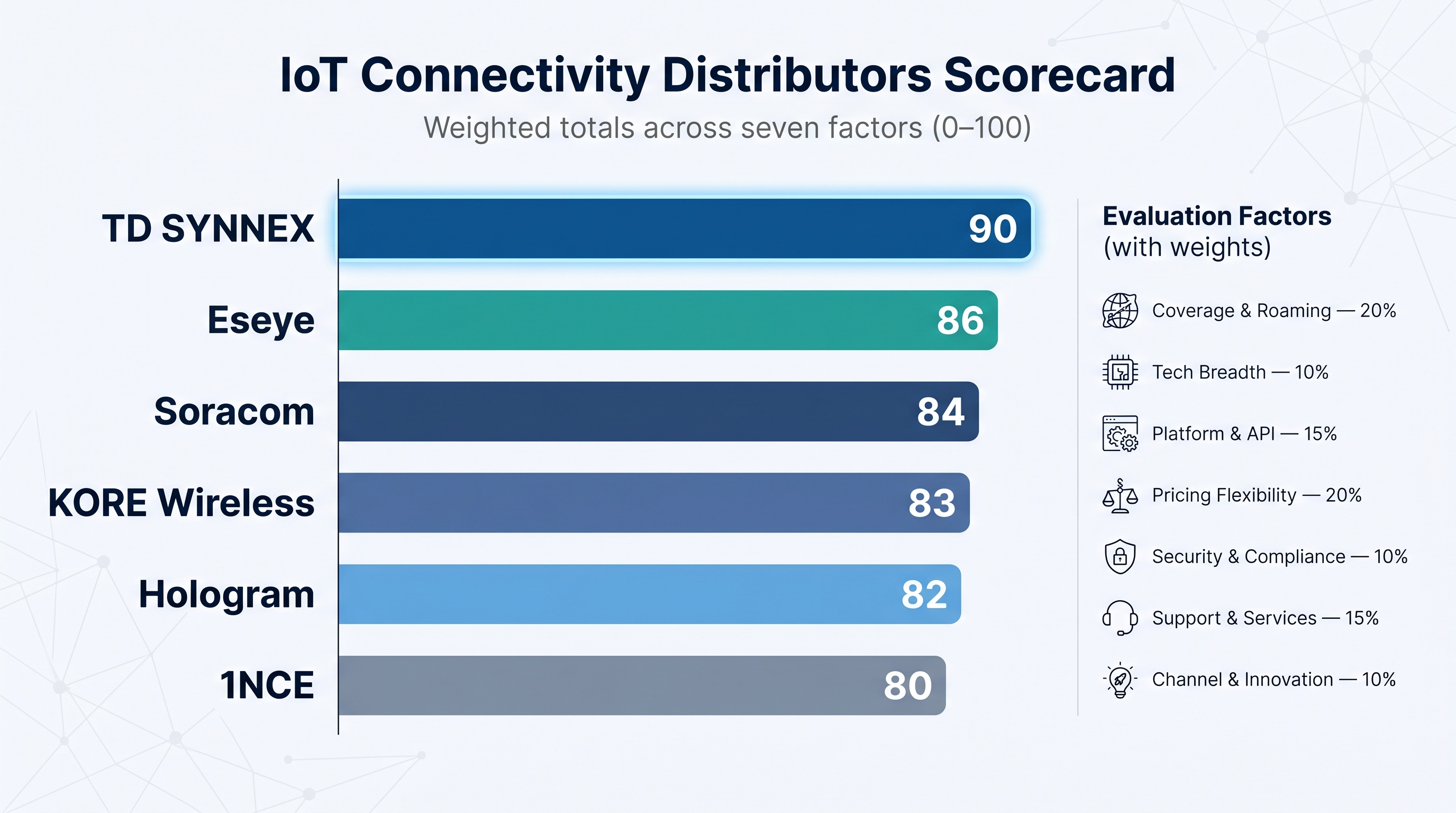
Next, we built a seven-factor scorecard that reflects the pain points integrators mention most often.
- Global coverage and roaming redundancy — 20 percent
- Supported technologies (2G sunset plans, LTE-M, NB-IoT, early 5G) — 10 percent
- Platform and API maturity — 15 percent
- Pricing transparency and flexibility — 20 percent
- Security and regulatory compliance — 10 percent
- Support and solution assistance — 15 percent
- Channel program and ongoing innovation — 10 percent
We ran each platform through hands-on portal tests, contract reviews, and customer interviews, then multiplied the raw scores by the weights to reach a 100-point composite.
Numbers alone were not enough. We stress-tested the results against real-world fit—an ultra-low-cost SIM without network failover can never satisfy a life-safety deployment. That field reality gave every finalist a clear, actionable role.
The result is a ranked list of six distributors, each mapped to the scenario where it adds the most value. Up next: the full long-list and how the original twelve brands compared before the final cut.
The long-list: twelve contenders, one crowded stage
Before we name any winners, you deserve to see the full slate we vetted. Think of this as the talent pool; every provider on the list met our baseline for multi-country reach, an integrator-ready platform, and clear momentum during the last 24 months.
We cut marketing puffery, pulled hard numbers, and built a side-by-side view that mirrors a first discovery call: headquarters, headline coverage, and one milestone from 2023-2026 that shows fresh investment.
| Provider | HQ | Global Reach* | Recent Highlight |
| TD SYNNEX | USA | 160 countries | Ericsson–M2M alliance bundles routers + SIMs (2026) |
| KORE Wireless | USA | 190 countries | Passed about 20 million active SIMs |
| Aeris | USA | 190 countries | Absorbed Ericsson IoT Accelerator (2023) |
| Hologram | USA | 190 countries | Launched Hyper SIM with outage protection |
| Soracom | Japan | 170 countries | Added satellite messaging + Sigfox resale (2023) |
| 1NCE | Germany | 173 countries | Surpassed 22 million lifetime connections (2024) |
| Eseye | UK | 190 countries | Named Gartner “Visionary” |
| Telnyx IoT | USA | 140 countries | Shifted focus to larger data plans after price hike (2023) |
| Tata MOVE | India | 200 countries | Launched connected vehicle platform for Jaguar Land Rover (2025) |
| BICS – SIM for Things | Belgium | 200 countries | Partnered with GEO sat-com firms for hybrid IoT (2024) |
| Wireless Logic | UK | 165 countries | Crossed 10 million SIMs globally (2023) |
| Transatel / NTT | France | 180 countries | Integrated Ubigi 5G eSIMs into BMW vehicles (2024) |
*Coverage refers to advertised cellular footprint; per-country network count varies.
Scan the grid and you will spot distinct personalities: price disruptors, enterprise stalwarts, and niche innovators. Yet breadth alone never guarantees uptime or sane invoices, which is why only six names advanced.
Next, we will compare those finalists head to head and show the score gap that set leaders apart from the chasing pack.
The scorecard: how the finalists stack up at a glance
Numbers cut through hype, so we converted every interview note and portal test into a weighted score. The grid below highlights where each finalist excels and where it lags. Higher numbers signal stronger real-world performance for that factor.
| Provider | Coverage & Roaming<br>(20 %) | Tech Breadth<br>(10 %) | Platform & API<br>(15 %) | Pricing Flexibility<br>(20 %) | Security & Compliance<br>(10 %) | Support & Services<br>(15 %) | Channel & Innovation<br>(10 %) | Total |
| — | :center: | :center: | :center: | :center: | :center: | :center: | :center: | :center: |
| TD SYNNEX | 9 | 8 | 8 | 9 | 9 | 9 | 10 | 90 |
| Eseye | 9 | 8 | 8 | 7 | 10 | 9 | 8 | 86 |
| KORE Wireless | 10 | 8 | 8 | 7 | 9 | 8 | 7 | 83 |
| Soracom | 8 | 9 | 10 | 8 | 8 | 8 | 8 | 84 |
| Hologram | 9 | 8 | 9 | 8 | 8 | 7 | 9 | 82 |
| 1NCE | 8 | 8 | 7 | 10 | 8 | 7 | 6 | 80 |
A few themes stand out.
TD SYNNEX leads because broad multi-network coverage pairs with a mature channel program. Integrators earn margin and rely on distributor-level support, something pure-play MVNOs rarely match.
Eseye lands a close second thanks to its localisation-friendly eSIM and spotless security track record. When regulatory headaches or deep-zone risk keep you awake, that extra reliability justifies the premium.
KORE commands the enterprise tier on raw footprint (now past 20 million active SIMs) but loses points on price flexibility for smaller fleets.
Soracom and Hologram battle for the developer crowd. Soracom wins on API richness and cloud plug-ins; Hologram gains ground with network redundancy after its Hyper SIM release.
Finally, 1NCE shows that low cost does not have to sacrifice security or coverage. Its ten-dollar, ten-year plan earns a perfect score in pricing, even if single-network service holds the overall total at eighty.
With the landscape mapped, the next sections dive into each provider’s strengths, trade-offs, and ideal use cases.
1. TD SYNNEX connectivity – your one-stop IoT backbone
Coverage comes first.
Beyond SIM cards, TD SYNNEX’s IoT connectivity solutions package SD-WAN, private cellular networking, and 5G services into one channel-friendly lineup. That toolset lets a single SIM roam in more than 160 countries and usually find at least two tier-one networks per market, so coverage worries fade into the background.
Lose signal on AT&T in Texas? The same chip re-attaches to T-Mobile in seconds and keeps streaming.
Management feels equally simple. You open the Connectiv portal, toggle a slider, and a batch of SIMs springs to life. Usage dashboards, real-time alerts, and a REST API sit one click away. Need hardware too? Add an Ericsson-grade router pre-configured with your private APN, then ship it to site.
Pricing is quote-based yet integrator-friendly. You buy at wholesale rates and, as evidence of the model’s earning power, TD SYNNEX reports paying partners more than $45 million in carrier commissions over the last two years, giving integrators a tangible recurring margin when they bundle connectivity into their service. No surprise line items for VPN or portal access; the essentials are already included.
Support seals the deal. A named account manager partners with TD SYNNEX’s 24 × 7 NOC. If a deployment in Brazil blinks offline at 2 am, someone who knows your project answers the phone, pulls logs, and coordinates the carrier fix while you sleep.
When to choose it
Roll out hundreds or thousands of devices across regions and want one contract, one invoice, and one point of contact. The model shines for solution providers that resell connectivity under their own brand.
When to pause
Ultra-small pilots—think fewer than ten SIMs—move faster on a self-serve platform like Hologram. If absolute lowest cost per byte is the only goal, 1NCE’s prepaid plan will beat any custom quote.
Bottom line
TD SYNNEX compresses complexity. Hardware, SIMs, logistics, and revenue share sit in one stack, so you spend time building customer value instead of stitching vendors together.
2. Eseye – always-connected eSIM for the hard places
Some IoT projects feel routine. Others place devices in patchy rural grids, strict regulatory zones, or steel cabinets that swallow radio waves. Eseye lives for the second category.
At the heart of its offer is the AnyNet eSIM. Each chip carries several local carrier profiles plus an intelligent applet that swaps between them when signal weakens or roaming limits loom. One device, three networks, zero manual intervention. Gartner called the approach “visionary” in its 2023 Magic Quadrant.
Coverage spans 190 countries, yet the real value lies in localisation. Deploy a fleet in Brazil or Turkey, and the eSIM quietly loads a domestic IMSI to stay compliant—no truck roll required.
Security keeps pace. Private APN, IPSec tunnels, and SIM-based AWS authentication ship as standard options. If a sensor drinks ten times its normal data, Eseye flags it and can auto-suspend the line before the bill spikes.
Pricing is premium and bespoke. Expect a monthly fee per SIM plus pooled data. Projects that judge ROI in uptime—health kiosks, EV chargers, asset trackers—rarely flinch because one outage can cost more than a year of connectivity.
Support stays hands-on. Solution architects join early design reviews, advise on antenna placement, and remain on call after launch. When a South African network degraded last December, Eseye switched thousands of client devices to an alternate carrier within minutes, then sent root-cause notes before customers opened a ticket.
When to choose it
Pick Eseye when failure is not an option and deployments cross regulatory minefields. Think global medical devices, border-hopping logistics tags, or industrial sensors buried behind concrete.
When to pause
If your sensors sip a few kilobytes in one country, Eseye’s sophistication and cost can feel like bringing a satellite phone to a garden party. Simpler, cheaper options suit low-risk scenarios.
Bottom line
Eseye sells peace of mind. Its eSIM hunts for signal, dodges roaming bans, and calls for help before you notice a blip. For integrators chasing five-nines reliability, that insurance often pays for itself on day one.
3. KORE Wireless: heavyweight scale for enterprise fleets
KORE is the company Fortune 500 teams call when a pilot turns into a global rollout. Two decades in machine-to-machine markets have built relationships with more than 400 mobile networks, giving KORE the widest raw footprint in our line-up: over 190 countries and more than 20 million active SIMs in service today.
That reach shows in daily operations. A single KORE SIM usually sees three carriers per country, so a delivery truck crossing Europe keeps data flowing even when one operator hits a maintenance window. Behind the scenes, KORE’s carrier-grade platform, an evolution of the Jasper Control Center, logs every hand-off, flags anomalies, and exposes those events through a well-documented REST API. Enterprise IT teams appreciate the familiarity; it feels like working with a major telco, minus the regional silos.
Pricing follows the same enterprise logic. You negotiate a contract, then pool data across the fleet. Per-megabyte rates are average, yet KORE rarely charges for inactive inventory, so integrators can stage thousands of SIMs without running up a bill. Watch the fine print: SMS and overage fees sit on a second page of the quote, so set caps where possible.
Security runs deep. Private APNs, MPLS backhaul, and HIPAA workflows cover most regulated sectors. KORE’s engineers also help with tough certifications. If your telemetry unit fails a carrier test in Australia, they tweak firmware and retest, saving months of guesswork.
When to choose it
You manage a multinational fleet where board-level stakeholders demand mature SLAs, strict compliance, and a vendor that answers the phone in six languages.
When to pause
Start-ups running a hundred smart lockers may find KORE’s paperwork and minimum commitments heavy. Developer-first platforms like Soracom or Hologram get you live in minutes and let you pay by card.
Bottom line
KORE delivers telco-grade reliability without forcing you to juggle individual carrier contracts. For integrators scaling past tens of thousands of endpoints, that operational simplicity beats chasing the last penny per megabyte.
4. Soracom – cloud-style connectivity that developers love
If Amazon Web Services built a mobile network, it would look a lot like Soracom. The Japan-born provider treats connectivity as another cloud resource: self-service, pay as you go, and bundled with dozens of drop-in tools that wipe out middleware work.
Getting started is quick. Order a starter kit, pop a SIM into your prototype, and watch usage stats update in real time. Need devices to post straight into AWS IoT, Azure, or Datadog? Turn on Soracom Funnel. Want to translate raw TCP into secure MQTT without writing code? Enable Soracom Beam. Each switch lives inches apart in one console.
Coverage reaches 170 countries on multiple carriers, with LTE-M and NB-IoT already live in key markets. Soracom also allows technology mixing. You can run LoRaWAN sensors on a local gateway, then backhaul through Soracom cellular, all visible in the same dashboard. For assets that drift beyond cell towers, a satellite short-burst add-on fills the gap.
Pricing stays simple: no contract, no device minimum, and per-kilobyte billing that pools across your fleet. Light sensors often cost pennies per month. Heavy data devices can move to fixed buckets, and you decide line by line. A small daily SIM fee applies when active, so remember to suspend spares.
Security arrives baked in. One toggle spins up a VPN tunnel (Soracom Canal) so traffic never touches the public internet. Another locks a SIM to the device’s IMEI to block theft. Every action is also an API call, ideal for CI/CD pipelines that treat hardware like code.
When to choose it
Rapid prototyping, mixed-tech projects, or any rollout where your software team moves faster than telecom procurement. Agriculture, micromobility, and smart-retail deployments thrive because developers can iterate without waiting for a new contract.
When to pause
Large enterprises that need formal SLAs, on-site support, or ultra-low data rates at million-unit scale may outgrow the self-serve model. In that case, KORE or TD SYNNEX’s white-glove approach fits better.
Bottom line
Soracom turns connectivity into a cloud checkbox. For integrators who prefer shipping code over chasing SIM paperwork, that agility is a superpower.
5. Hologram – global reach, developer-first DNA
Hologram started by selling SIM kits to makers. A decade later the company still greets you with an easy dashboard and posted-online pricing, yet now backs that friendliness with a 550-network footprint across 190 countries.
The headline feature is Hyper SIM. Each card holds several IMSI profiles and an outage-protection routine that notices when one carrier stumbles, then hops to another core network without manual help. Latency in the United States and Europe drops about twenty percent because traffic lands on a local core, not a distant roaming gateway.
Pricing remains transparent. Activate a line and pay a one-dollar platform fee plus usage: by the megabyte at forty cents or through ready-made buckets from one to 1 000 MB. You can mix plans in one account, pause unused SIMs to dodge that access fee, and spin new lines up—or down—through API calls that slot into any CI pipeline.
The platform keeps friction low for engineers. Real-time data usage, webhooks, and a REST API appear minutes after sign-up. Need to tunnel into a field device for firmware work? Spacebridge VPN opens a secure door without juggling public IPs.
Support is email-first but quick, with a community forum where staff and peers share modem quirks and AT-command fixes. Enterprise tiers add phone escalation, yet the sweet spot remains agile teams that prefer self-service over formal tickets.
When to choose it
Select Hologram for connected products that ship worldwide under one SKU, mobile assets that crave multi-carrier redundancy, or any project where your developers prize speed and clear pricing.
When to pause
Massive fleets pushing gigabytes per device will hit cost ceilings, and sectors that need signed SLAs or private MPLS links may lean toward KORE’s heavier toolset.
Bottom line
Hologram offers global connectivity that feels as approachable as Stripe or Twilio. For integrators who value clarity, strong APIs, and a safety net against carrier outages, Hyper SIM delivers.
6. 1NCE – the ten-year SIM that rewrites the cost model
Every integrator meets a project where the device budget is single-digit dollars and the data plan must follow. 1NCE exists for those moments.
The offer is simple: pay ten dollars once and run a sensor for ten years. That upfront fee buys 500 MB of data and 250 SMS in 173 countries. A soil-moisture probe can check in hourly for a decade. When the bundle runs out, you top up at the same low rates. No monthly line charge, no platform fee, no hidden extras.
Coverage depends on one preferred carrier per country, a trade-off that keeps contracts lean and prices tiny. Urban areas work well, but remote corners with only one bar of the other network may fail. Field-test critical sites before bulk orders.
The portal is bare-bones and fast. Activate SIMs in batches, set usage alerts, and pull CSV reports. A REST API mirrors every function, so you can drop activation into an assembly-line script and skip the UI. Power users can add an IPSec VPN or AWS IoT Core link for a few dollars more.
Support stays email first to protect margin. Documentation is clear, and community forums solve most edge cases. Large enterprise deals unlock an account rep through Deutsche Telekom, yet the sweet spot is still high-volume, low-touch deployments.
When to choose it
Pick 1NCE when devices sip kilobytes, budgets are tight, and maintenance windows are rare. Smart meters, parking sensors, and asset beacons that move slowly or not at all are perfect fits.
When to pause
Mobile assets that roam through patchy coverage need multi-network redundancy. Projects that burn more than 50 MB a year may outgrow the prepaid model and find pooled plans cheaper elsewhere.
Bottom line
1NCE shows that reliable global connectivity can live without recurring invoices. If your device thrives on one network, locking in ten years of predictability for ten dollars is hard to beat.
Feature snapshot: key specs, one table
You have met the players one by one. Here is the cheat sheet you will likely share with the team. It distills practical details—SIM form factor, tech support, and security extras—into a single view, so you can spot the short-list candidate that fits your project in seconds.
| Feature | TD SYNNEX | Eseye | KORE | Soracom | Hologram | 1NCE |
| SIM type | Triple-cut + eSIM (partner branded) | eSIM by default, plastic if needed | SIM & eSIM | SIM & eSIM | SIM & Hyper eSIM | Triple-cut SIM, eSIM beta |
| Networks per country | 2–3 | 2–4 (auto-switch) | 2–3 | 2–3 | 3+ (non-steered) | 1 primary |
| LTE-M / NB-IoT | Yes | Yes | Yes | Yes | LTE-M yes, NB-IoT limited | Yes |
| 5 G roadmap | Partner launches 2026 | Trials live | Pilots live | Early SIM ready | NSA live in US/EU | Not yet |
| Platform/API depth | Mature portal + REST | Advanced policy engine | Carrier-grade CMP | Cloud-style API suite | Polished dashboard + webhooks | Basic portal + REST |
| Pricing model | Custom, margin for resellers | Custom premium | Custom pooled | Pure usage PAYG | Transparent PAYG or buckets | 10 USD / 10-yr prepaid |
| Security add-ons | Private APN, VPN | SIM-based AWS auth | MPLS backhaul, HIPAA packs | Canal VPN, SIM lock | Spacebridge VPN | IPSec “IP Plug” |
| Support style | Dedicated AM + 24 × 7 NOC | Proactive engineers | 24 × 7 enterprise NOC | Email / API first, premium SLA extra | Email + forum, phone for enterprise | Email / docs only |
Use the matrix as a filter:
- Need reseller margin and bundled hardware? TD SYNNEX is the ready answer.
- Chasing nonstop uptime across tricky borders? Eseye’s multi-IMSI eSIM wins.
- Managing a million smart meters under one SLA? KORE brings the telco muscle.
- Building a cloud-native prototype this week? Soracom’s API gets you live today.
- Shipping a consumer gadget worldwide? Hologram balances coverage with clear pricing.
- Deploying cost-sensitive sensors at city scale? 1NCE’s decade plan slashes OPEX.
Find your fit: a quick decision flow
Choosing a provider gets easier once you pin down your top priority. Walk through the questions below, answer honestly, and land on a short-list in under a minute.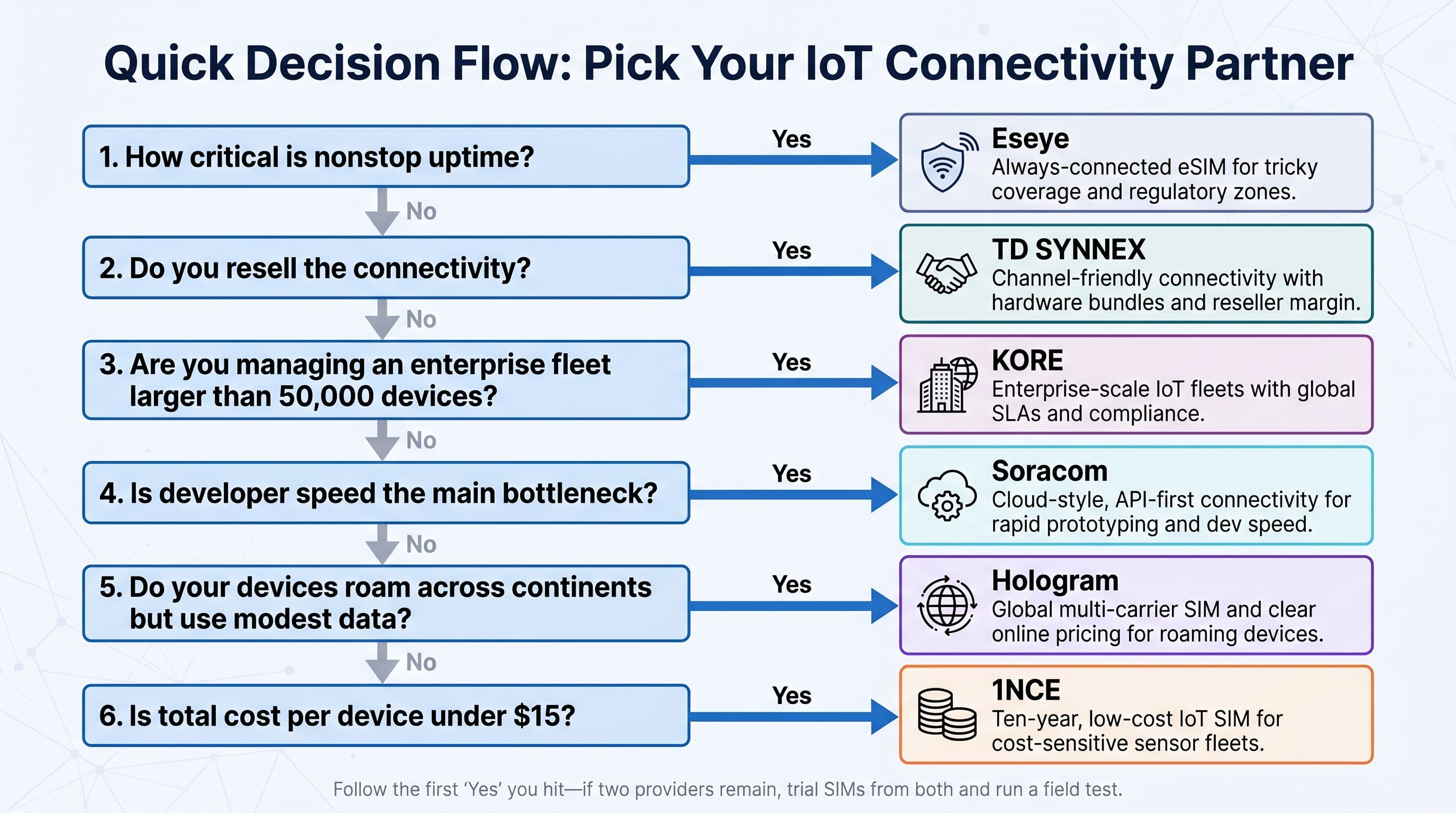
- How critical is nonstop uptime?
If a single drop hurts revenue or safety, jump straight to Eseye. Its multi-IMSI eSIM and proactive support serve life-or-death deployments.
- Do you resell the connectivity?
Need wholesale rates, margin, and bundled hardware? TD SYNNEX’s distributor model gives you all three without extra vendors.
- Are you managing an enterprise fleet larger than 50,000 devices?
Scale and compliance point to KORE. The carrier-grade platform and global SLAs keep board members calm.
- Is developer speed the main bottleneck?
For rapid prototyping and cloud-native builds, Soracom’s pay-as-you-go API suite gets you live by lunchtime.
- Do your devices roam across continents but use modest data?
Hologram balances multi-network redundancy with clear online pricing, perfect for connected products that ship worldwide under one SKU.
- Is total cost per device under $15?
If yes, end the search at 1NCE. Its ten-year, ten-dollar plan suits penny-pinching sensor fleets.
Treat these questions as gates. The first “yes” usually reveals the best match. If two providers remain, order trial SIMs from both and run a one-week field test; that small step often saves months of second-guessing.
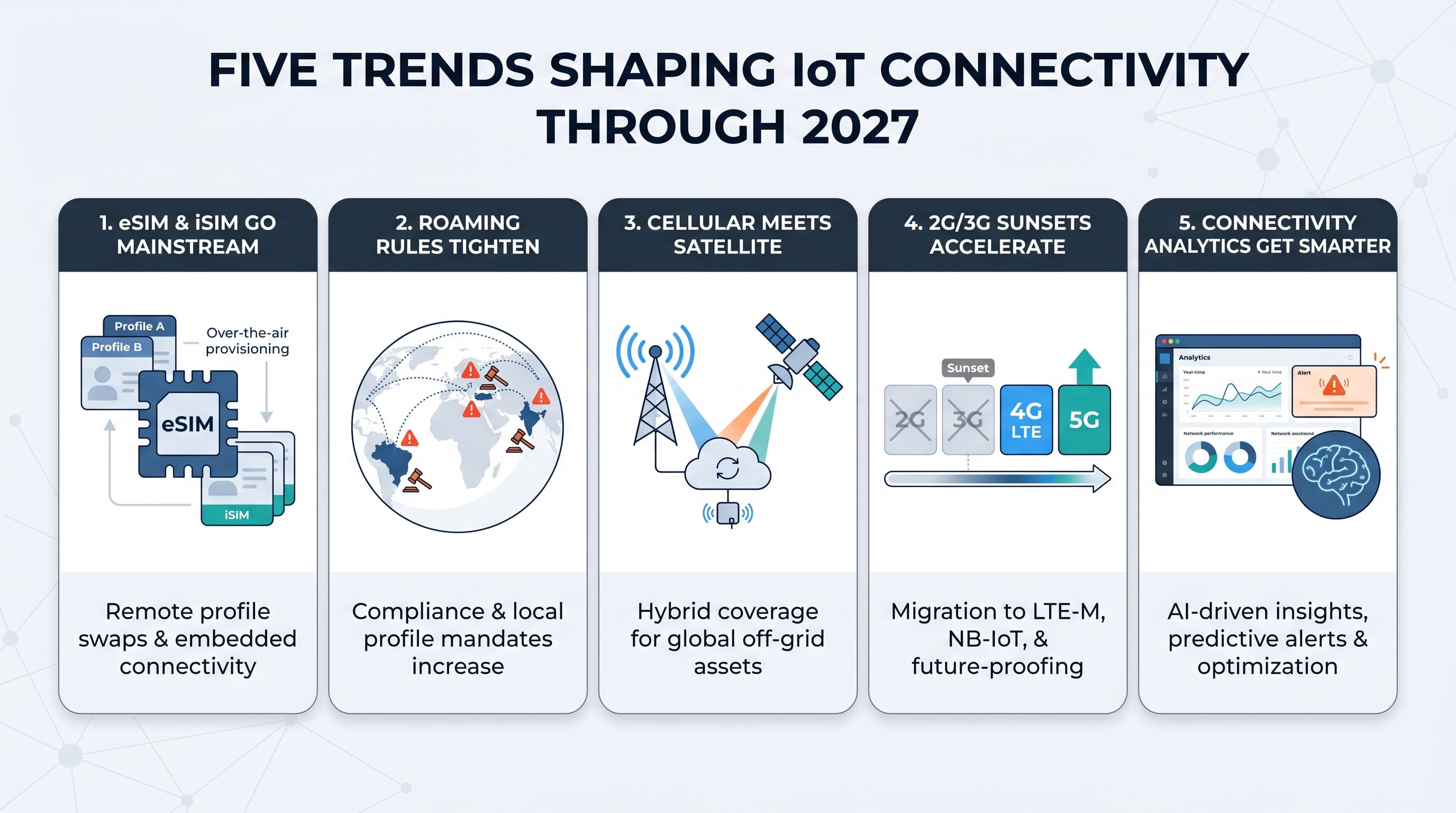
Five trends shaping IoT connectivity through 2027
New GSMA SGP.32 profiles let you swap carriers over the air with zero truck rolls. Hologram’s Hyper SIM rollout and Eseye’s localisation work prove the standard is production-ready, not theory. Chip-level iSIM variants will follow, baking connectivity into the modem and trimming BOM cost.
Permanent-roaming crackdowns tighten.
Regulators in Brazil, Turkey, and parts of India now fine or block devices that linger on a foreign IMSI. Eseye solves this with local profiles, while TD SYNNEX and KORE ship country-specific SIMs when needed. Plan for compliance early or budget for mid-deployment swaps.
Cellular meets satellite.
Low Earth Orbit networks, from Iridium’s short-burst service to OneWeb’s broadband backhaul, are sliding into the same dashboard as your LTE fleet. Soracom already lets a sensor fall back to satellite SMS when it drifts off-grid, a preview of smooth terrestrial-plus-space plans on the horizon.
2G/3G sunsets accelerate migration.
In the United States, 3G shut down in 2022; Europe follows by 2025. LTE-M and NB-IoT fill the low-power gap, while 5G RedCap modules promise similar efficiency with wider spectrum support. KORE and TD SYNNEX have 5G pilot tariffs live, but check module firmware because older hardware may need an update before it talks to new bands.
Connectivity analytics get smarter.
AI now spots a failing antenna or a stolen SIM before humans notice. Hologram’s outage protection and Eseye’s SMARTconnect stream real-time network data into optimisation engines that reroute devices to stronger or cheaper carriers. Tomorrow, your NOC may receive predictive alerts such as “Signal degradation expected in Nairobi tomorrow; rerouting 312 devices.”
Six hidden risks to flag before you deploy
Silent SIM shutdowns catch teams off guard.
Carriers can kill a line without warning if a device breaks fair-use rules, such as parking a roaming SIM in Brazil past the legal limit. Eseye’s local-profile option and KORE’s country-specific IMSIs reduce the danger, but you still need deployment data on file. Keep a spreadsheet of where every unit lives and share it with your provider before rollout.
Roaming contracts change overnight.
Your devices may cling to Carrier A until a roaming deal expires, then fall back to Carrier B—or to no carrier at all. Multi-network SIMs from Hologram or TD SYNNEX soften the blow, yet firmware should retry alternate APNs and log failures for remote diagnosis.
Data spikes wreck budgets fast.
A firmware loop or security breach can burn through a month’s allowance in hours. All six providers let you set per-SIM caps; turn them on during the pilot. For extra safety, build an alert that pings Slack when usage jumps five times the rolling average.
SMS gets pricey in bulk.
Developers love SMS as a wake-up trigger, then forget every ping costs fifteen cents. Multiply that by 10,000 devices texting twice a day and you face a five-figure surprise. Where possible, switch to data commands or free inbound SMS if your provider offers it.
2G/3G sunsets strand legacy hardware.
The United States ended 3G in 2022, and many EU networks will follow by 2025. If your modem cannot speak LTE-M or NB-IoT, you are on borrowed time. Audit module part numbers now and plan a swap before field units become bricks.
SIM inventory leaks money.
Inactive but still-active lines hide in warehouses, demo cases, or retired units. Run a quarterly script that compares the provider’s active-SIM list with your asset database, then suspend anything without a matching serial number. Those one-dollar platform fees add up.
Nine deployment tips every integrator should steal
Run a multi-carrier site survey.
Before you commit, drop SIMs from at least two finalists into test devices and log RSSI for 24 hours at each site. The winner often changes once a steel door closes or a forklift drives past.
Automate SIM lifecycle events.
Connect your backend to the provider’s API on day one. When an installer scans a device QR code, your script should activate the SIM, tag its location, and set a 200 MB monthly cap. Nobody should manage the portal by hand at scale.
Use staged rollouts for firmware updates.
Push code to five percent of the fleet, wait twelve hours, then widen the blast radius. If a bad build kills cellular registration, you lose a handful of units, not thousands.
Cache then forward data.
Write sensor readings to local storage first, then transmit in bursts. This cushions brief outages and cuts connect overhead on LTE-M or NB-IoT.
Set dual alerts for data spikes.
Create a per-SIM cap in the carrier portal and a parallel alert in your monitoring stack. Belt and suspenders stop runaway bills and surface root-cause clues faster.
Lock SIMs to IMEI in high-theft assets.
A single API call prevents a stolen card from fueling someone’s hotspot. For rented e-bikes and smart lockers, that move pays for itself the first time a thief tries.
Log cell IDs for remote triage.
Store the serving cell and signal metrics with each payload. When a customer reports an offline unit, you know immediately whether the tower disappeared or the device needs a reboot.
Schedule bulk traffic off-peak.
Most networks charge the same rate all day, but congestion still hurts latency. Non-urgent files—daily logs, for example—should upload at 3 am local time.
Audit inventory every quarter.
Pull the active-SIM list, compare it with your asset register, and suspend or terminate any orphaned lines. A five-minute script can save thousands in unused platform fees.
Quick answers to five common questions
Is a global SIM legal everywhere?
Mostly, yes. Problems arise when a country limits permanent roaming. Brazil, Turkey, and parts of India enforce local-profile rules. Choose a provider that can load a domestic IMSI remotely or ship country-specific cards before customs intervenes.
How hard is it to switch providers later?
Start with an eSIM that follows the SGP.32 standard and a profile swap is an API call. With plastic SIMs you need a site visit. Plan for flexibility from day one; request eSIM samples even if you launch on plastic.
What is the real difference between LTE-M and NB-IoT?
Both sip power. LTE-M supports mobility and voice, while NB-IoT reaches deeper indoors and uses cheaper silicon. If your device moves or needs over-air firmware updates, choose LTE-M. If it sleeps in a manhole and reports once a day, NB-IoT saves batteries.
Do I need a private APN?
For basic sensor data, NATed public IPs work. If you need inbound access, fixed IPs, or regulatory segregation (healthcare, for example), a private APN with VPN backhaul is worth the cost.
How long should a pilot run?
Two weeks catches most SIM and modem bugs, while thirty days reveal billing quirks across cycles. Ship at least ten units to three varied coverage zones and push a firmware update midway; that single step surfaces hidden edge cases.
Conclusion
Use this guide to match the right provider to your project, avoid budget-wrecking surprises, and keep every device talking.
INTERESTING POSTS
- How to Increase Delivery Speed by 30% with Real-Time Tracking
- Exploring Singapore with Ease: How to Set Up Your Tourist eSIM in Minutes
- Taming the IoT in the Wild: How To Secure Your IoT Devices
- IoT Technologies and Trends: What You Should Know About Them
- The Best Cyber Security Technology Trends You Must Know