Read on for the Surfshark Antivirus vs McAfee comparison.
Thousands of new malware roll out each day. Malware, which can completely cripple even the most rigorous systems if there’s any vulnerability. So, you’re at a significant risk if you’re not protecting your devices using a quality antivirus solution.
The question, however, is, what is a quality antivirus solution? You can search the web for answers and come across multiple software programs. Surfshark Antivirus and McAfee will most likely be among the top options.
If you’re reading this, you’re contemplating which of the two antivirus solutions you should use. Making the decision is only possible if you know what they offer and how their features compare.
We’ll discuss that in this Surfshark Antivirus vs McAfee post, so read on.
Table of Contents
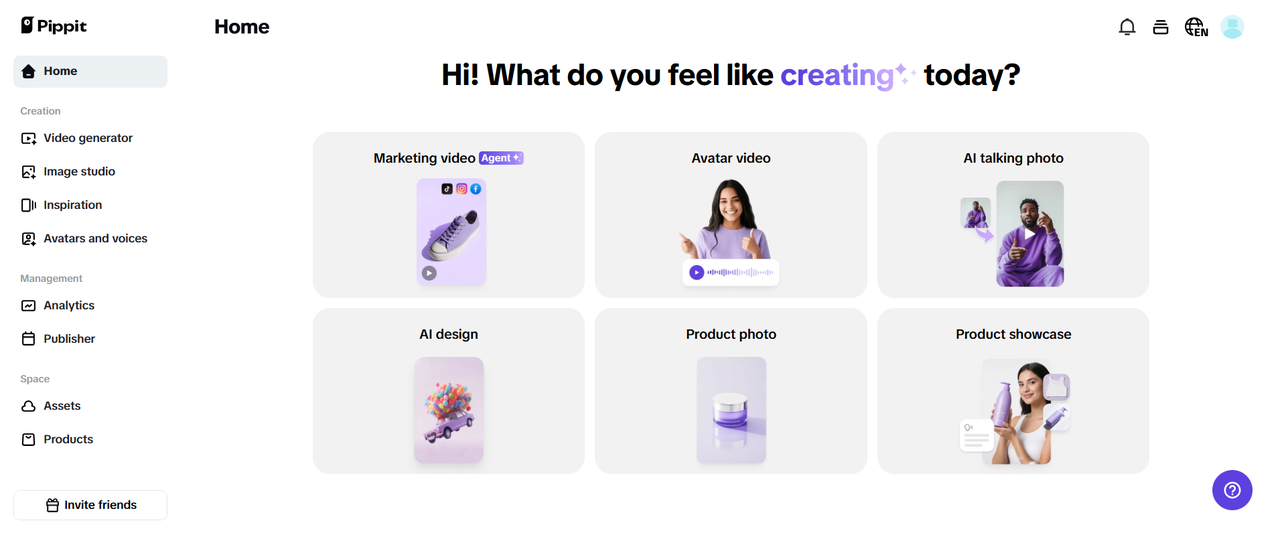
What Is Surfshark Antivirus?
Surfshark Antivirus is a lightweight software from one of the most renowned cybersecurity companies. It’s a relatively new antivirus, but considering the features, it easily qualifies as one of the best options. Notably, the software works to eliminate both known and unknown malware.
You can’t use Surfshark Antivirus for free. The software is premium; you can’t get it as a standalone tool. Instead, the Antivirus is part of the Surfshark One suite.
As a result, purchasing the Surfshark Antivirus means you get the other tools in the suite. The tools include a VPN, search, and breach alert solution. With these, you can amplify your cybersecurity protection.
What Is McAfee Antivirus?
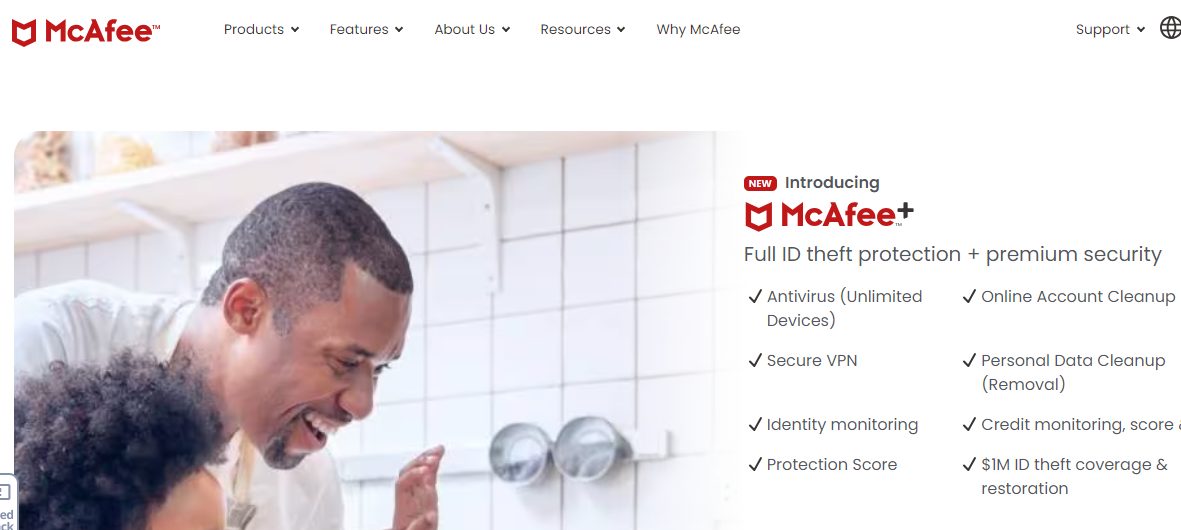
McAfee is a popular antivirus solution that has existed for a long time. For context, the software was released in 1988, making it over 35 years old. It’s not surprising that it’s a multiple-award-winning antivirus.
At least 600 million devices worldwide use the McAfee Antivirus software. It’s reliable for real-time protection and can eliminate various malware threats. Notably, you can install it on almost all top device platforms.
McAfee has extra features like VPN, identity monitoring, and parental controls. It’ll even work as an online data cleanup and password manager, to name a few. However, what you can do with the software depends on your subscription plan.
Surfshark Antivirus vs McAfee: Features Comparison
Let’s look at how Surfshark Antivirus and McAfee compare in terms of features. You can identify the best antivirus software for each category from the verdicts.
Getting Started
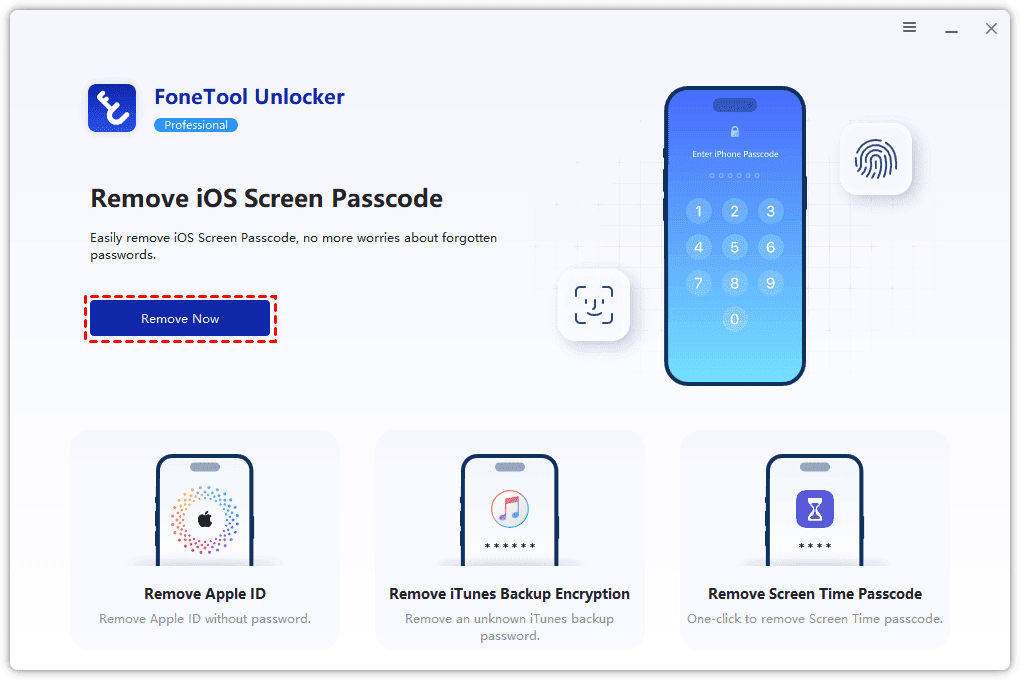
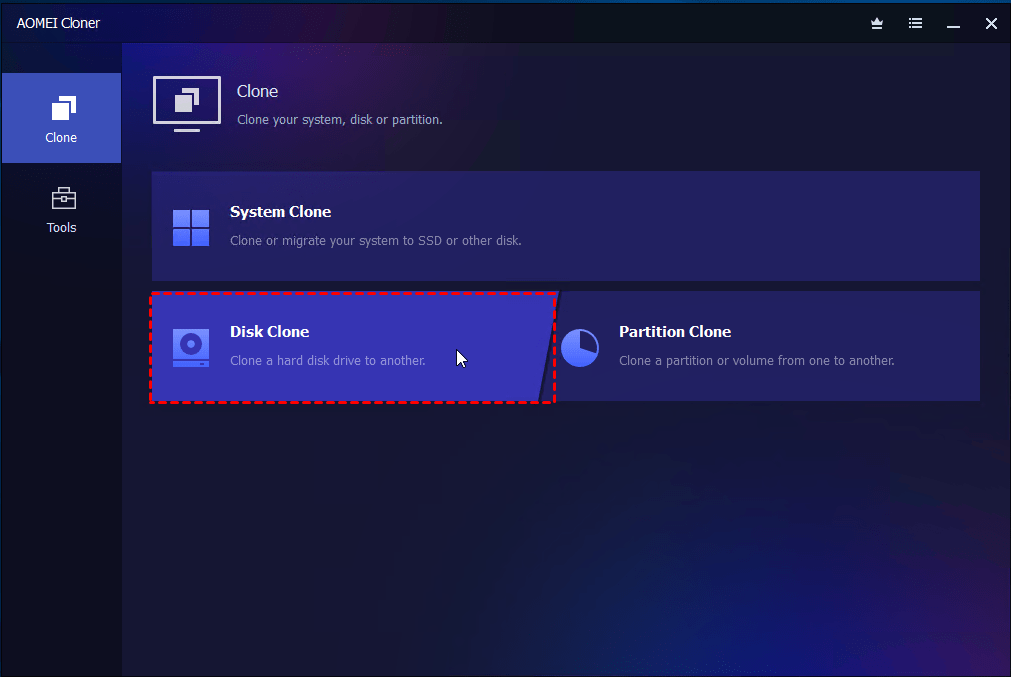
Surfshark Antivirus
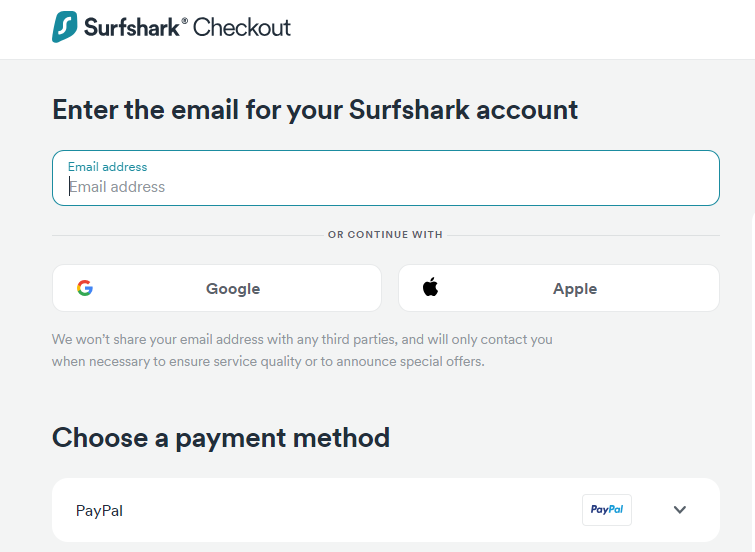
You first need to make a payment to use Surfshark Antivirus. The software offers no free version or trial — mainly because it’s not standalone. Also, you’ll be paying for Surfshark One.
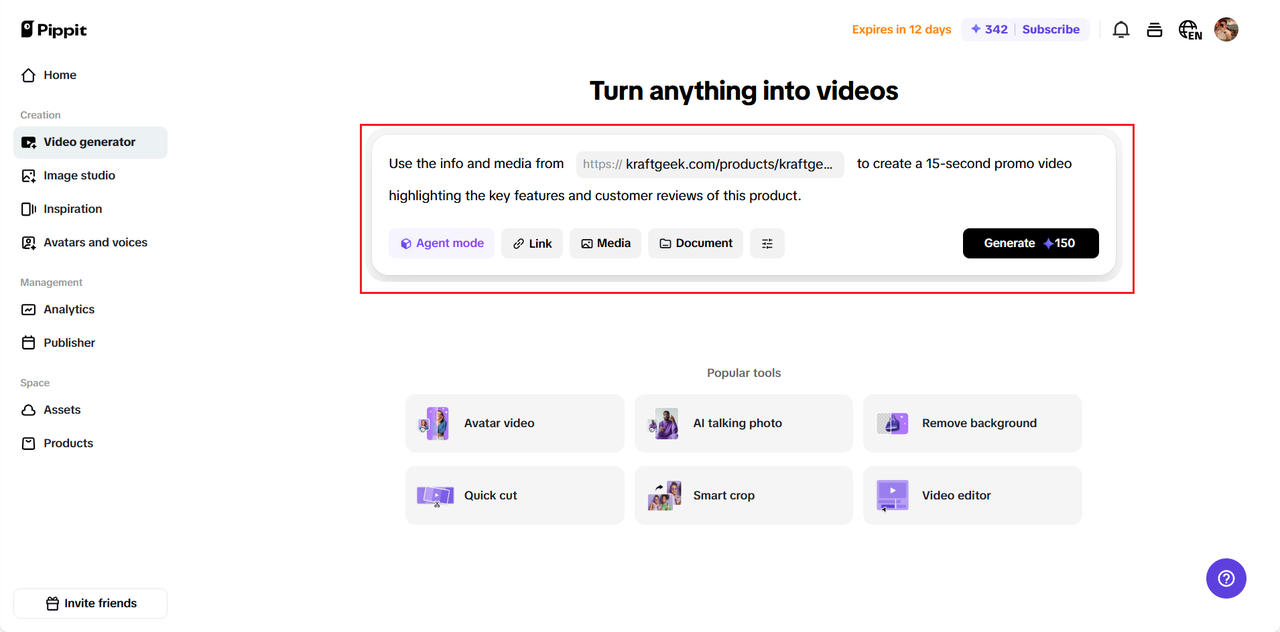
On the Surfshark website, select the Antivirus among the products in the menu. Then, click the “Get Surfshark” button and choose your preferred subscription plan. Continue to checkout.
You’ll enter your email address on the checkout page and pick a payment method. Surfshark supports crypto, PayPal, Google Pay, Amazon Pay, and Apple Pay, so you have many options.
Once your payment is successful, you can download and start using the antivirus app for your device.
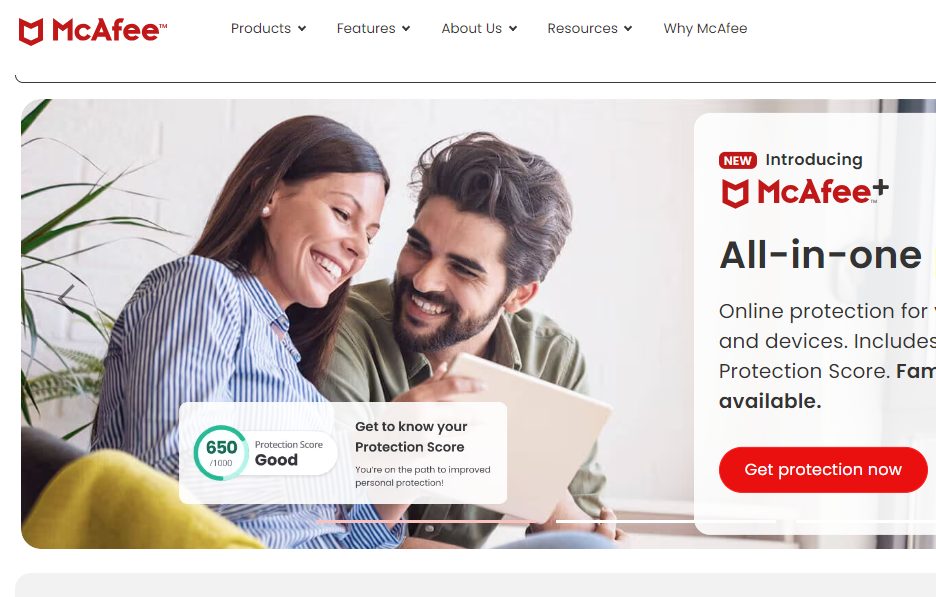
McAfee
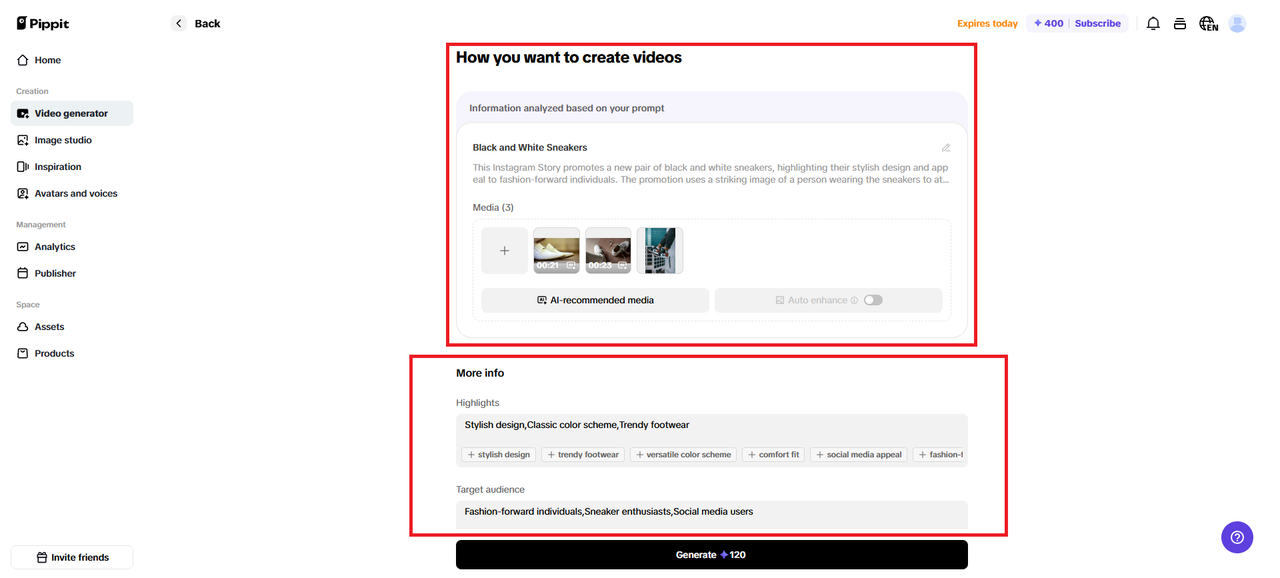
McAfee offers different cybersecurity solutions, and some packages include antivirus software. However, you’ll select the option for just the Antivirus from the menu. Then, pick a suitable plan depending on the number of devices you want to protect.
Before you subscribe, you can download the free trial and try out the software. It’s helpful, but only limited features are accessible. Click the “Get Protection Now” button to continue with the payment.
Enter your email address on the checkout page and pick a preferred payment option. You can pay for McAfee antivirus using your debit card or PayPal. You get full access to the antivirus software if the transaction completes successfully.
Verdict
McAfee’s free trial makes things easy for new users. However, you ultimately have to subscribe, like with Surfshark. Surfshark wins here as you get more payment methods, making registration more convenient.
Virus And Malware Protection
Surfshark Antivirus
With Surfshark Antivirus, you can protect your devices from various types of malware. These include viruses, spyware, Trojan horses, bots, rootkits, adware, and ransomware, to name a few. In addition, Surfshark will also protect against zero-day threats.
Zero-day threats here refer to newly released malware, which, usually, should not be within the detection capability of the antivirus tool. Yet, Surfshark can stop such threats thanks to a Cloud Protect System. The tool scans the internet 24/7 to identify the newest viruses the minute they’re out.
It’s worth noting that Surfshark Antivirus protects your webcam. This is a vital feature that many antivirus solutions skip. It’ll prevent any malicious party from accessing your camera without authorization.
READ ALSO: Surfshark One vs Surfshark VPN Comparison
McAfee
You can use McAfee Antivirus to keep your devices free from viruses and malware. However, the software mainly focuses on malware that aims to hack or steal information via phishing. Hence, it’s effective in eliminating spyware.
McAfee virus protection capabilities aren’t limited to known threats. The software can block off brand-new threats using behavioral detection and machine learning. It spots and isolates any file showing malware-like behavior and eliminates it if confirmed to be malware.
Note that McAfee makes a 100% pledge to all users to completely rid their devices of malware. Hence, if the software fails to keep your device free from malware, you can contact the company and get a refund. That’s how confident McAfee is of the antivirus software performance.
Verdict
There’s no winner here. Surfshark Antivirus and McAfee stand equal in terms of virus and malware protection. Each can fight off existing, new, and emerging threats.
Supported Scans
Surfshark Antivirus
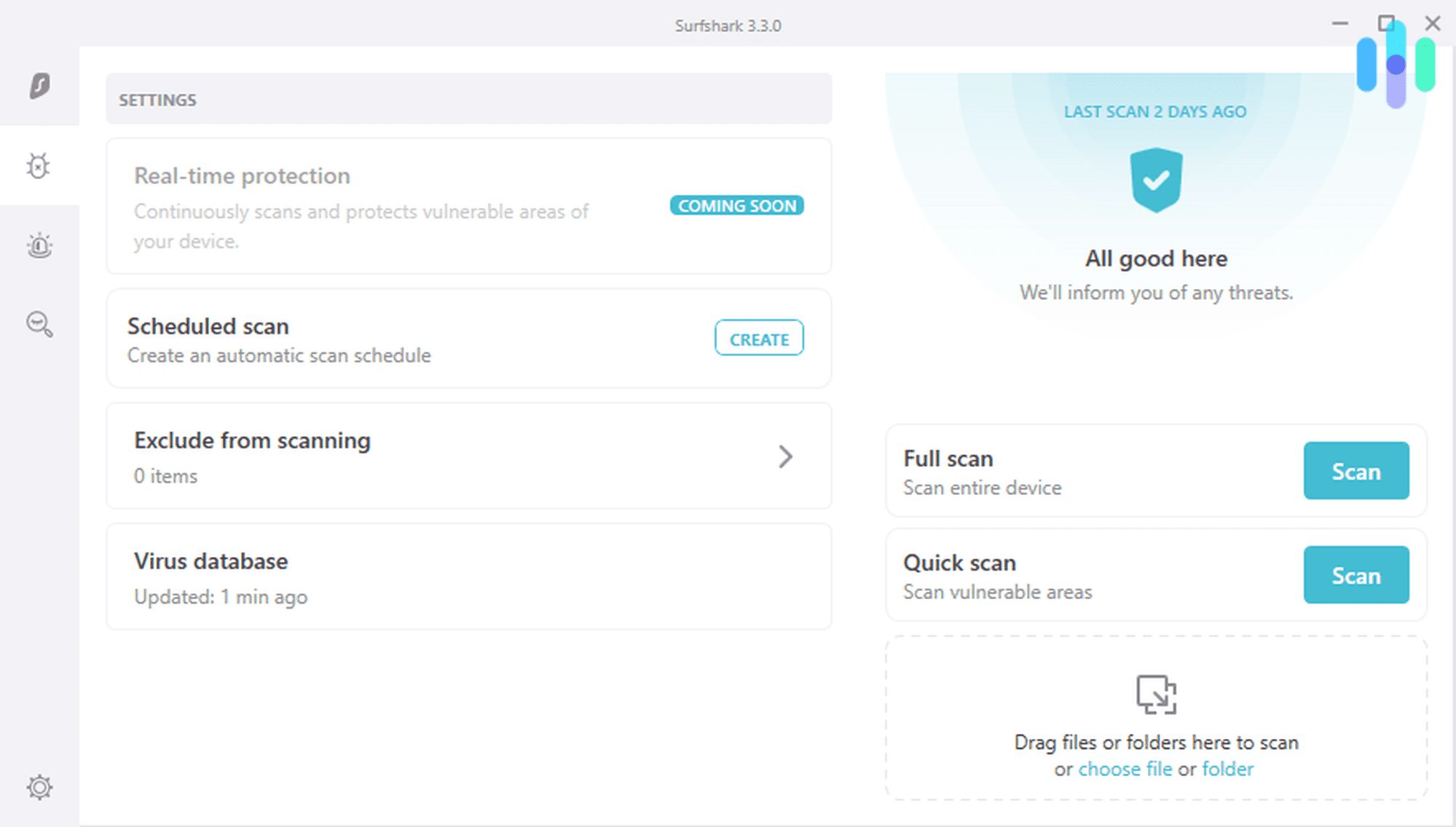
Surfshark Antivirus supports manual, scheduled, and real-time scanning. In addition, the 24/7 Cloud Protect System was mentioned earlier for zero-day threats. With these, the software offers all-round malware protection.
You can launch the app on your device and run a scan anytime. From the options, it’s possible to narrow your scan location. Also, you can either perform a full manual scan that’ll take a long time or a quick one that takes seconds.
Scheduled scans are helpful if you want the Antivirus to work automatically. You can set the software to scan your device for malware every day at a specific time or on particular days. It’s also possible to schedule a single future scan.
McAfee
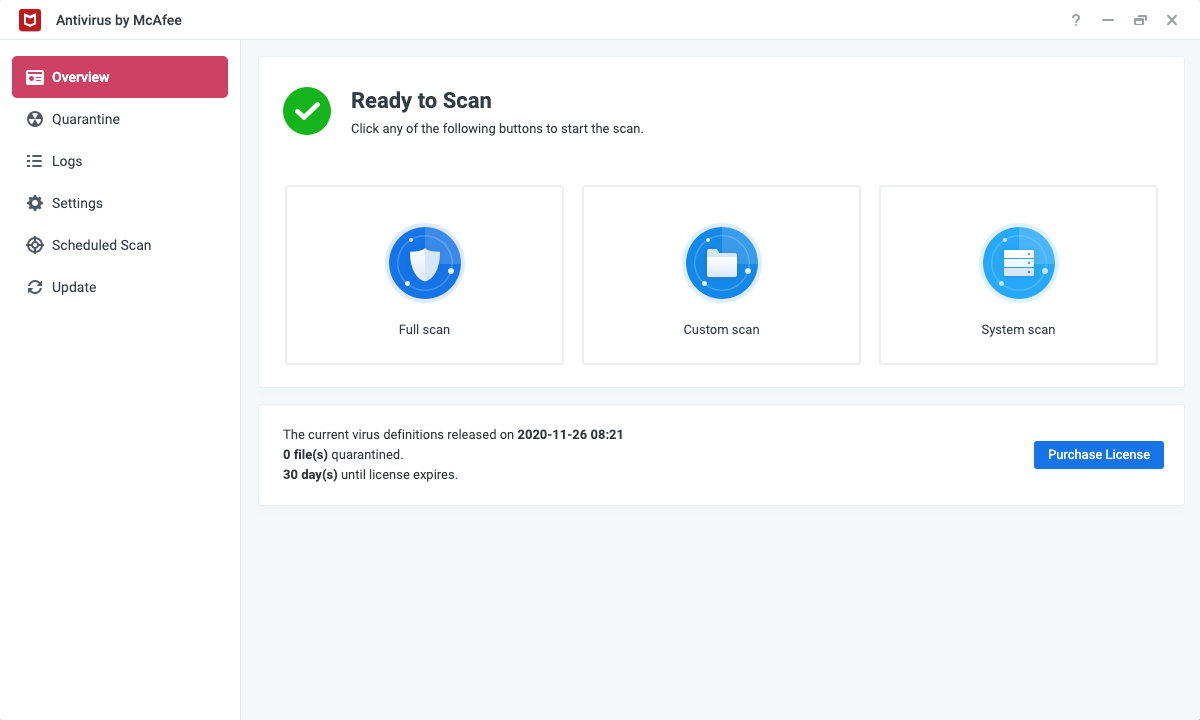
When you load the McAfee software, the scan options include scheduled, on-demand, and real-time scans. Each one is easy to access from the dashboard. However, they have different usage protocols.
If you run an on-demand scan, it’s best when you’re not working with your device. That’s because McAfee’s manual scans are usually in-depth. So, if you’re working on the system concurrently, you may experience lag.
For scheduled scans, your device has to be on for the software to work. This is standard for almost every Antivirus that supports the feature. McAfee can perform scheduled scans in sleep mode if your device supports it.
Verdict
McAfee and Surfshark Antivirus support real-time, scheduled, and manual/on-demand scans. So, it’s a close call. However, Surfshark takes a slight lead due to the 24/67 Cloud Protect System.
Ad Blocking
Surfshark Antivirus
You can’t directly access an ad blocker as part of the Surfshark Antivirus software. However, you get one from the VPN tool with the Surfshark One suite. The feature in question is CleanWeb.
Currently, in its 2.0 version, Surfshark CleanWeb stops ads and malware before they load. These also include pop-ups and cookies, and the latest upgrade also works for data breach alerts.
Besides accessing it via the VPN, CleanWeb is a standalone browser tool. You can install it on Google Chrome, Mozilla Firefox, and Microsoft Edge.
McAfee
You won’t find a specific ad blocker tool when you install the McAfee antivirus. The software blocks adware as part of its malware-blocking functionality. However, it would be best to still deal with “safe” ads and pop-ups as you browse.
If you’re more particular about blocking malicious ads, you can install the McAfee WebAdvisor browser extension. It focuses on the web, keeping you free from not only harmful ads but also harmful websites.
Notably, the extension supports a pop-up blocker. As a result, you can completely prevent ads that block access to web pages.
Verdict
The winner here is Surfshark, as it offers a particular ad blocker with CleanWeb, although you can only access it via the VPN. McAfee works, in a way, but not for all ads.
Identity Protection
Surfshark Antivirus
ID protection is one of Surfshark’s latest features. Like the previous ad blocker option, it’s not a tool native to the antivirus software.
Instead, it forms part of Surfshark Alert. You get access to it since the Alert and Antivirus solutions both come with Surfshark One.
How the feature works is straightforward. You supply your details — email, ID numbers, password, credit cards, etc — and Surfshark scans the web for potential breaches. If there are any, you get prompts on how to stay safe.
McAfee
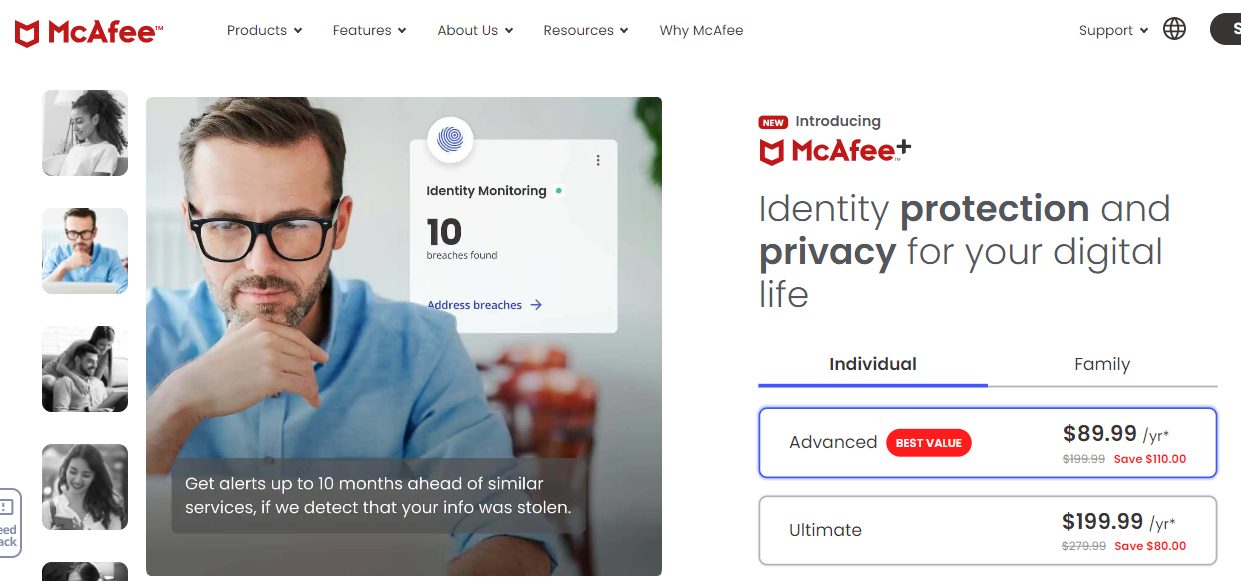
McAfee offers top-notch identity protection with 24/7 monitoring. In particular, the Antivirus supports ID theft protection, with coverage up to $2 million. And you can access this feature whether on an individual or family plan.
One option you get with McAfee ID monitoring is the Online Account Cleanup. It scans for your information from broker sites and eliminates any found. McAfee also checks for your data on the dark web with instructions on removing them.
You can rely on McAfee’s identity restoration experts if you suffer any identity theft attack. These are licensed professionals that’ll work with you to resolve the issue.
Verdict
McAfee is the superior tool when it comes to ID monitoring. The coverage value and support for the dark web give it the edge.
VPN
Surfshark Antivirus
When you purchase the Surfshark One suite for the Antivirus, you also get a VPN. Notably, the Surfshark VPN is one of the most popular in the industry. You’ll appreciate it if you prefer lightweight applications.
The Surfshark VPN will work on all major devices. It has over 3,200 servers in 100 countries, which is super fast. Furthermore, you get exclusive features like Kill Switch, MultiHop, Split tunneling, no-logs policy, and more.
Notably, you can get the VPN as a standalone software. It works on unlimited devices with one subscription.
McAfee
As part of its quest to ensure online protection, McAfee includes a staunch VPN with bank-grade encryption.
You can install it if you use Windows, iOS, or Android. However, it’s a standalone tool you’ll purchase alongside the Antivirus in a higher plan.
The McAfee VPN has relatively fast servers. At least 2,000 servers are available in around 23 countries.
Verdict
Surfshark VPN wins since it supports more servers in more countries. In addition, you can use Surfshark VPN on unlimited devices and more supported platforms.
Surfshark Antivirus vs McAfee: Pricing
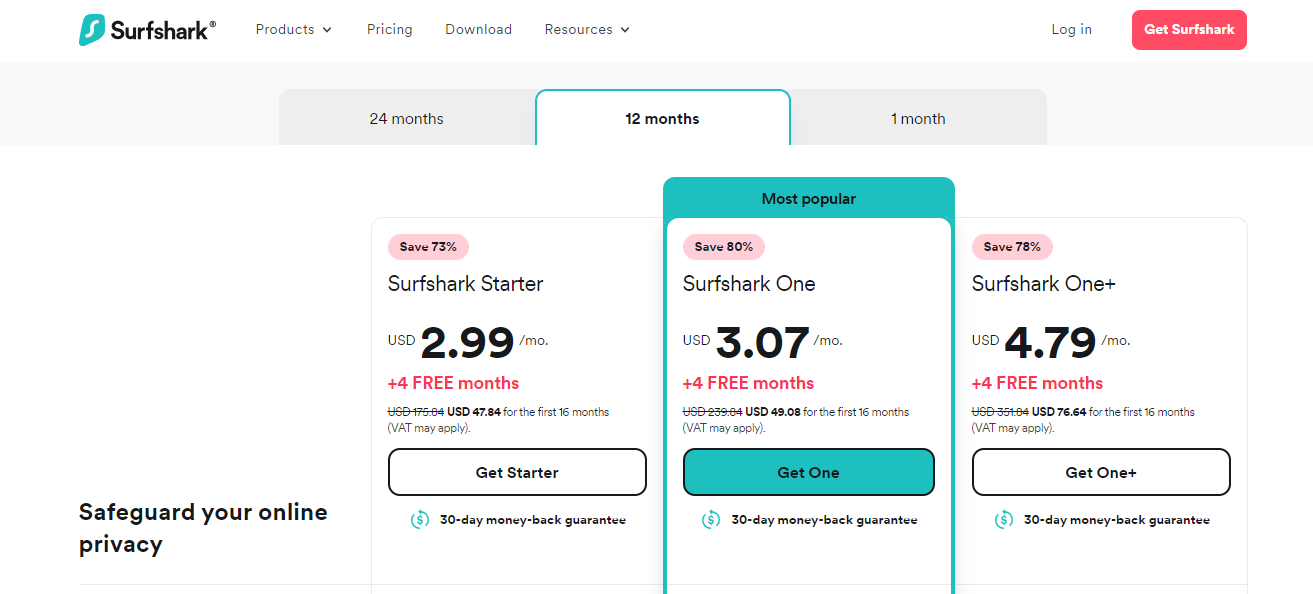
Surfshark Antivirus
Surfshark Antivirus sells for the Surfshark One pricing plans. Check them out below:
Surfshark One
- 1-month Plan: $14.99 per month
- 1-year Plan (plus two free months): $3.49 per month
- Two years plan (plus four free months): $2.69 per month
Surfshark One+
- 1-month Plan: $21.99 per month
- 1-year Plan (plus two free months): $5.49 per month
- Two years plan (plus four free months): $3.99 per month
McAfee
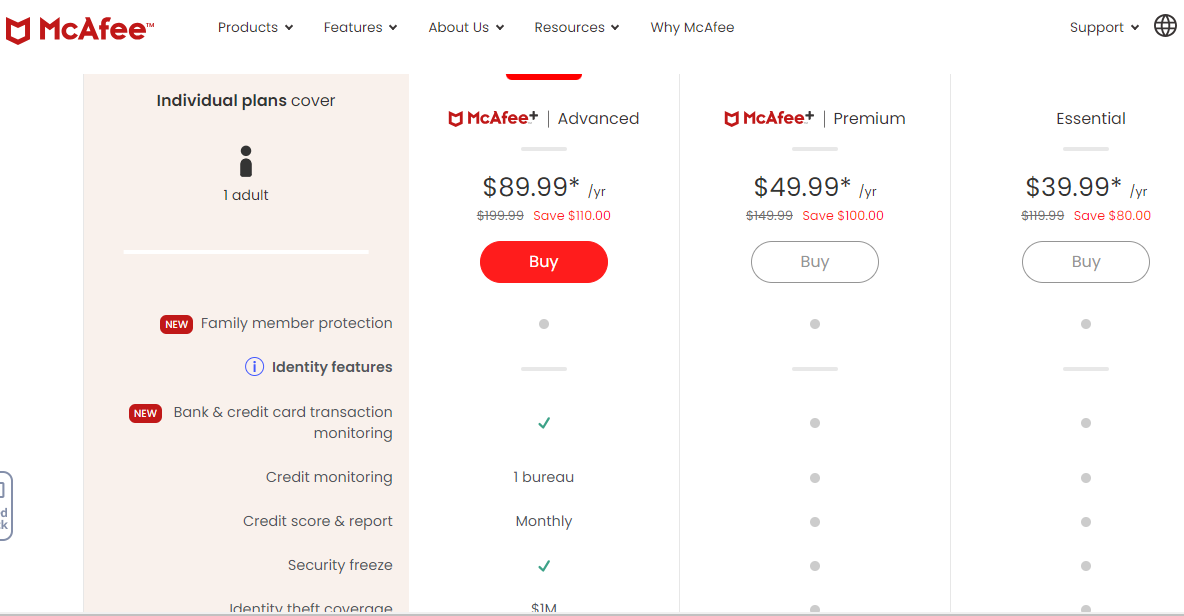
McAfee has several pricing packages that include the Antivirus. However, here are the primary options:
- Basic Plan: $29.99 per year for the first year ($89.99 subsequently)
- Essential Plan: $39.99 per year for the first year ($119.99 subsequently)
- Premium Plan: $49.99 per year for the first year ($149.99 subsequently)
- Advanced Plan: $89.99 per year for the first year ($199.99 subsequently)
Verdict
McAfee has affordable first-time prices, but the regular rates are expensive. On the contrary, Surfshark maintains stable and affordable plans, so it takes the crown.
Surfshark Antivirus vs McAfee: Pros And Cons
Surfshark Antivirus Pros
- Easy to use
- Affordable pricing
- Stops all viruses and malware
- CleanWeb ad blocker
- VPN with a high server count
Surfshark Antivirus Cons
- Not a standalone tool
- No free trial
McAfee Antivirus Pros
- Free trial
- Affordable first-time prices
- Supports different scans
- First-rate identity protections
- Quality VPN
McAfee Antivirus Cons
- No particular ad blocker
- Expensive regular pricing
McAfee vs Surfshark Antivirus: Similarities And Differences
Similarities
- Core Functionality: McAfee and Surfshark Antivirus are software programs designed to protect your devices from malware, viruses, and other online threats.
- Real-time Protection: Both offer real-time protection that continuously scans your files and system for suspicious activity.
- Malware Detection: Both use advanced technologies to detect and block known and emerging malware threats.
- Phishing Protection: Both help protect you from phishing attacks by identifying and blocking malicious websites and emails.
- Multi-Device Support: Both offer protection for multiple devices, including Windows, macOS, Android, and iOS.
McAfee vs Surfshark Antivirus: Key Differences
| Feature | McAfee Antivirus | Surfshark Antivirus |
|---|---|---|
| Additional Features | Often includes a firewall, password manager, parental controls | Primarily focuses on Antivirus, data breach monitoring in higher tiers |
| Pricing | More comprehensive range, lower starting price for basic plans, potentially higher for complete packages | Single Plan with occasional discounts |
| System Performance | Can impact performance more noticeably | Generally lightweight and resource-friendly |
| Customer Support | Phone, email, live chat | Primarily email and tickets, live chat limited hours |
| Free Trial | Yes | No |
Choosing The Right Option Between McAfee Antivirus and Surfshark Antivirus
The best choice for you depends on your specific needs and preferences. Here’s a quick guide:
Choose McAfee if:
- You want a wide range of features beyond essential antivirus protection.
- You are comfortable with potentially lower system performance.
- You prefer access to multiple customer support channels.
Choose Surfshark if:
- You prioritize lightweight software with minimal impact on performance.
- You prefer transparent pricing and limited-time discounts.
- You are comfortable with primarily email and ticket support.
Ultimately, McAfee and Surfshark Antivirus are reputable options for protecting your devices. Consider your priorities and research specific features and user reviews before deciding.
Conclusion
Picking either Surfshark Antivirus or McAfee isn’t a wrong decision, as you can see from this Surfshark Antivirus vs McAfee comparison. However, if you want to use the best of the two, you should use the Surfshark Antivirus.
Surfshark offers adequate protection against viruses and malware and has the upper hand in ad blocking, VPN, ease of use, and pricing. You can sign up for the software in no time.
INTERESTING POSTS