Learn how to secure your OPay account in this post…
Mobile banking has revolutionized finances, but navigating the digital world comes with risks. With cyber threats on the rise, securing your OPay account is more important than ever. This is your gateway to financial freedom – sending, receiving, and saving your money with ease. However, true peace of mind requires confidence in the safety of your account.
In this article, we’ll equip you with essential tips and tricks to build an impenetrable wall around your OPay, ensuring your financial transactions remain secure and worry-free.
Take control of your digital wallet and unlock the full potential of OPay, starting today!
Table of Contents
How To Secure Your OPay Account
1. Do Not Share Your PIN With Anyone
Your Personal Identification Number (PIN) is created by you and should be known by only you. No transaction, whether online or offline, is authorized on OPay without you first entering your PIN, and that makes it very important.
It doesn’t matter the level of trust you have for your friends or relatives, do not share your PIN with them or any OPay agent. OPay will never contact you to disclose your PIN.
In instances where you are sent a text message requesting that you send your PIN, or you receive a call and are asked to verbally confirm your PIN to enable a transaction, do not do so; it is likely someone is trying to access your account.
2. Do Not Share Your Username and Password
Your Username and Password are as important as your PIN, do not share them with anyone. They help you log into your account and can be used by fraudsters to gain access if they obtain it. Your Username and Password should be created by you and known by only you.
3. Use Hard to Guess PIN and Password
Avoid using your birth year, the digits of your phone number, or those of your spouse, children, or close relatives as your PIN or Password.
Do not also use a combination of your birthday and month, digits from your debit card, the repetition of one number (for example, 0000), or common digits (for example, 1234) because they can be easily guessed by any fraudster that wants to access your account.
4. Answer Security Questions
When activating your account online, click on Security Questions and answer them. The information you provide is encrypted, meaning it is known only to you.
They are necessary for situations when someone tries to use different passwords to log into your account or attempts to log into your account from another device. OPay will ask security questions to verify the user’s identity, ensure it is the correct person, and detect potential fraudsters based on the answers provided.
5. Disregard Spam Calls, Emails, and Text Messages
Any phone call, email, or text message that seems suspicious or demands that you reveal your PIN, Phone Number, Username, or Password should be disregarded. Such calls, emails, or text messages carry an undertone of urgency, demanding that you take a particular action. This is just a trick.
Do not click on any link contained in them or send back any number or personal information. They are not legitimate. Instead, try to confirm from OPay’s social media handles or website whether they have sent such information before carrying out any action.
6. Carry Out Your Transaction Discreetly
When carrying out transactions, ensure that no one is looking at your phone. Do not relate with suspicious individuals or send money to unknown accounts. During business transactions, avoid involvement in anything confidential; if it can’t be disclosed, then it is wrong.
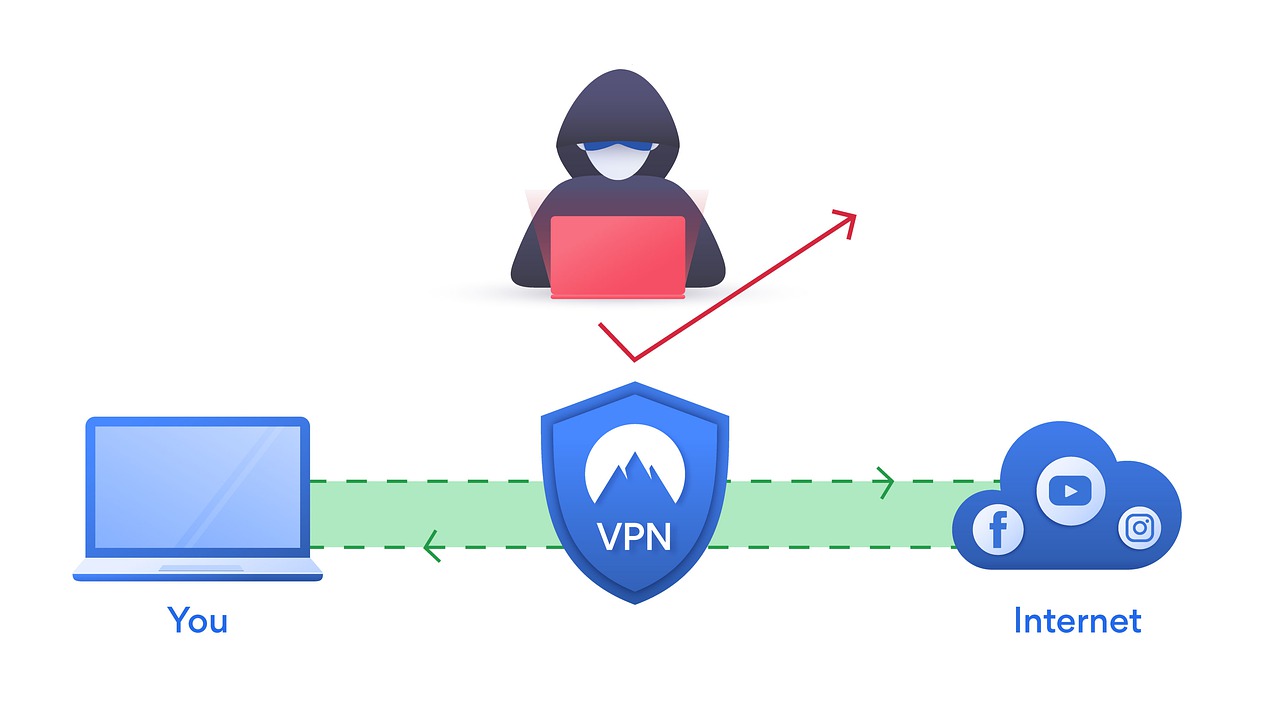
7. Never Use Public Wi-Fi to Carry Out Transactions
When carrying out online transactions, never use public Wi-Fi. Fraudsters can make use of public Wi-Fi to access your account by hacking your phone.
8. Beware of Fake Apps
Using a fake mobile app can also give fraudsters access to your account and confidential financial information. Download OPay’s app from the official source, such as Google Play or the App Store. To find the right app, follow the link on OPay’s website, which will direct you to the Play Store.
9. Enable Two-Factor Authentication (2FA)
This adds an extra layer of security by requiring a second factor, such as a one-time code sent to your phone, when logging in or making transactions. It’s quick and easy to set up and can make a huge difference in protecting your account.
10. Update your OPay app regularly
Updates often include security patches that fix vulnerabilities hackers could exploit. Staying on the latest version ensures you have the most up-to-date protection.
11. Monitor your account activity
Regularly review your transaction history for any suspicious activity. If you notice anything unusual, report it to OPay immediately. Even small, unauthorized transactions could be a sign of a bigger problem.
12. Be cautious about phishing scams
Phishing scams attempt to deceive you into disclosing your personal information or clicking on malicious links. Be cautious of emails, text messages, or calls claiming to be from OPay that request your PIN, password, or other sensitive information. OPay will never ask for this information directly.
READ ALSO: How To Secure Your WhatsApp Group From Hackers
13. Choose strong security questions and answers
Don’t use easily guessable answers to your security questions, such as your pet’s name or your mother’s maiden name.
Instead, opt for obscure personal details like childhood nicknames, favorite teachers’ names, or the street you grew up on. Consider using a passphrase or a random combination of words instead of actual answers.
14. Beware of social engineering
Social engineering is a type of scam where the attacker tries to gain your trust and then trick you into revealing your personal information. Be cautious about sharing your information with others, even online.
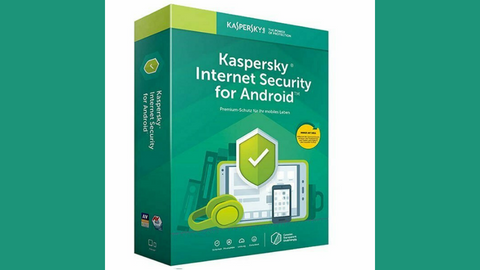
15. Use a strong antivirus and anti-malware software
Choose a reputable brand with real-time protection and scheduled scans to keep your device shielded from malicious software that can steal your OPay information or compromise your phone’s security.
BEST MOBILE SECURITY APPS
16. Keep your phone’s software up to date
Install updates as soon as they become available, as they often include critical security patches that fix vulnerabilities used by hackers to access your data. Set your phone to auto-update for maximum protection.
17. Be mindful of your phone’s physical security
Never leave it unattended in public places, especially near charging stations. Use a strong password or fingerprint lock, and consider a phone case with anti-theft features to deter opportunistic thieves.
READ ALSO: How To Secure Your Gmail Account
18. Consider using a mobile wallet
Store your OPay funds in a secure mobile wallet app instead of keeping them directly linked to your phone number. This adds an extra layer of protection and simplifies financial management.
How To Secure Your OPay Account: Frequently Asked Questions
Here are answers to some of your most common questions about OPay security:
How do I put face ID on my OPay app?
Unfortunately, OPay currently does not offer Face ID as a login option. However, you can secure your account with a strong PIN or password and enable Two-Factor Authentication (2FA) for an extra layer of protection.
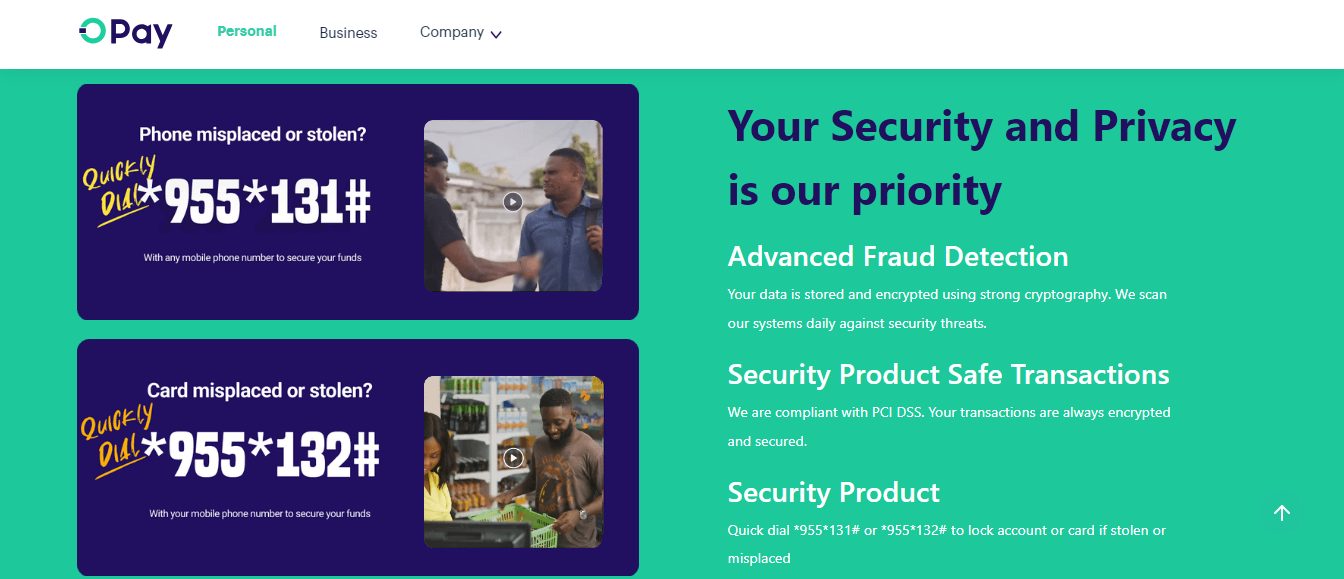
How to block my OPay account?
To block your OPay account immediately, contact OPay customer support through the app or website.
Provide your registered phone number and explain the reason for blocking. They will guide you through the process and temporarily disable your account until you can regain access.
How to lock my OPay account on iPhone?
Lock your OPay app just like you would any other app on your iPhone. Go to Settings > Face ID & Passcode or Touch ID & Passcode, then enable “Require Face ID/Touch ID” for OPay. This will require facial or fingerprint recognition to open the app.
READ ALSO: How to Securely Send Sensitive Information Over the Internet
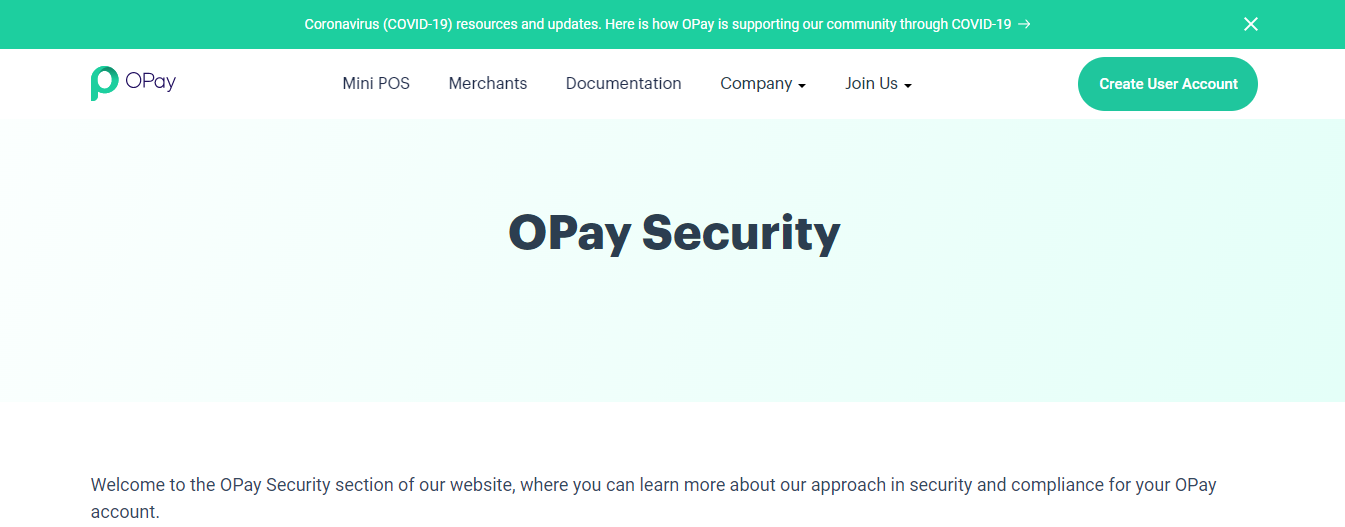
Is OPay safe to keep money?
OPay is a licensed financial institution regulated by the Central Bank of Nigeria (CBN) and employs multiple security measures to protect your money. However, no system is foolproof, so it’s crucial to follow best practices for account security.
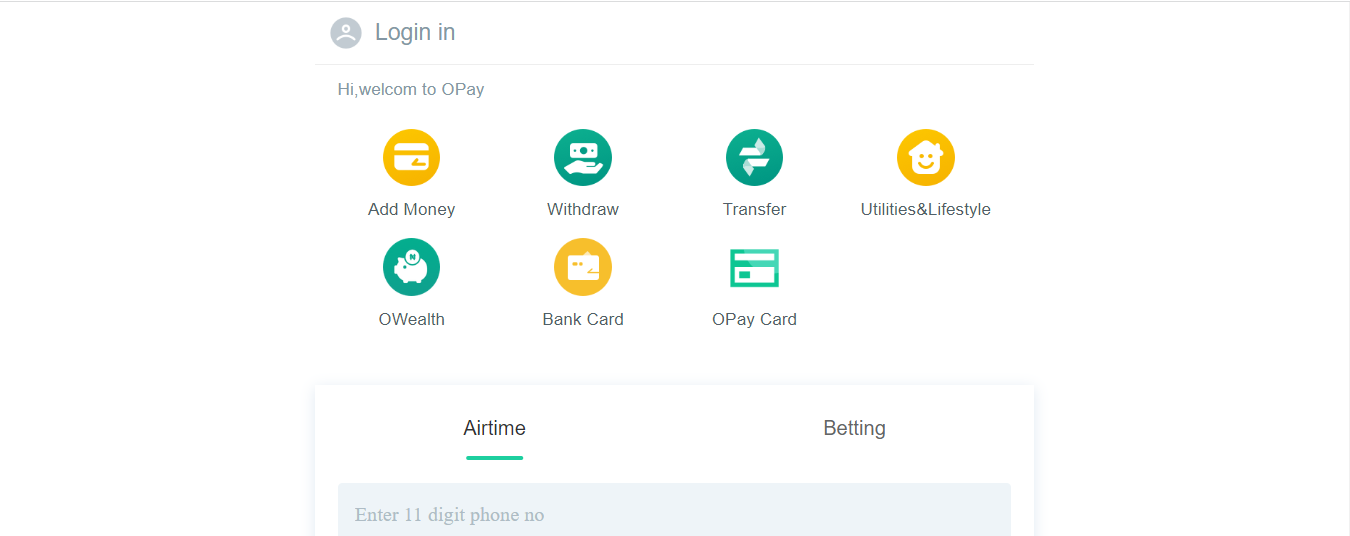
How can I lock money in my OPay account?
OPay currently doesn’t offer a specific feature to “lock” money in your account. However, you can consider these options:
- Transfer funds to OWealth: This investment feature offers daily interest on your balance, essentially “locking” your money for a specific period while generating returns.
- Withdraw cash: If you prefer physical security, consider withdrawing your funds and keeping them safely secured.
- Use a mobile wallet: Consider a mobile wallet like Google Pay or Apple Pay, linked to your OPay account, for secure storage and smaller daily transactions.
Is OPay a safe option for storing money in Nigeria?
Yes, OPay is generally considered a safe option for storing money in Nigeria. They are a CBN-licensed institution with robust security measures in place. However, always exercise caution and follow security tips to minimize risks.
READ ALSO: A Look at Fraud: 5 Things Your Business Should Look Out For
Can someone send money to my OPay account?
Yes, anyone can send money to your OPay account as long as they know your phone number or your OPay account number. Remember only to share this information with trusted individuals.
What is the highest amount OPay can receive?
The maximum amount you can receive in a single transaction on OPay is ₦5 million. However, daily transaction limits and cumulative monthly limits may apply depending on your account verification level.
Conclusion
Be it OPay or any other mobile-based platform that offers financial solutions, the security of your account should be taken seriously.
The mobile money system is getting popular, and hackers are always devising new means to exploit people. Do not fall victim before you take caution. Follow the above-mentioned tips to secure your OPay account today.
Leave a comment below on how to secure your OPay account.
INTERESTING POSTS
- Are Magento Websites Secure?
- What is ATM Skimming?
- How to Secure Your WordPress Website from Hackers
- How To Read Someone’s Text Messages Without Their Phone
- 11 Password Management Mistakes You Should Avoid
- The Role of an Elementary Math Tutor in Building Strong Foundations
- Casino Etiquette And Proper Behavior
- 2023 Cybersecurity Maturity Report Released: Why Detecting Cyber Attacks Is Not Enough
- Top 8 Cybersecurity Companies In Dubai
- LastPass Password Manager Review: Is It Still Safe In 2023?
- mSpy Review: Is It An Effective Parental Control App?
- Crypto Tips For Beginners: Why You Should Use An Exchange Instead Of A Wallet
- How To Choose The Ideal Cryptocurrency To Invest In
- Traveling Abroad: 5 Safety Tips When Connecting To Wi-Fi Overseas




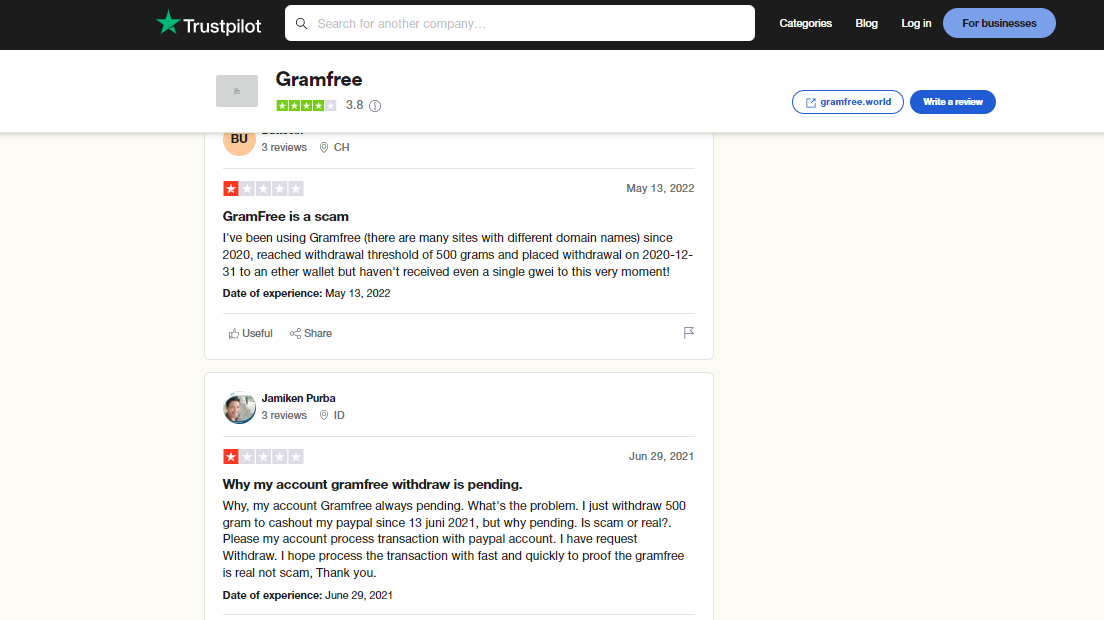
![Africgold Review: Is Africgold Legit Or A Scam? [EXPOSED] Africgold Review: Is Africgold Legit Or A Scam? [EXPOSED]](https://secureblitz.com/wp-content/uploads/2022/04/Is-Africgold-Legit-or-a-Scam-768x345.png)


![Is GramFree Legit Or A Scam? [Unbiased Answer] Is GramFree Legit Or A Scam? [Unbiased Answer]](https://secureblitz.com/wp-content/uploads/2022/04/Is-GramFree-Legit-Or-A-Scam-Unbiased-Answer-768x345.webp)

























![Mozilla Firefox Set to Launch a New VPN [OLD NEWS] Mozilla Firefox Set to Launch a New VPN [OLD NEWS]](https://secureblitz.com/wp-content/uploads/2019/12/firefox-new-vpn-768x512.jpg)