Update your WhatsApp now. Users with the old WhatsApp version are now vulnerable to attacks if they fail to upgrade due to a bug.
WhatsApp, the ubiquitous messaging platform used by billions worldwide, isn’t immune to security threats. While WhatsApp employs encryption to protect your messages, hackers constantly devise new methods to exploit vulnerabilities and gain unauthorized access to accounts.
If you suspect your WhatsApp has been compromised, don’t panic!
This guide will equip you with the knowledge to identify the signs of a hacked account, walk you through the recovery process, and, most importantly, advise you on how to update WhatsApp and secure your account to prevent future breaches.
Warning Signs: How to Tell Your WhatsApp is Hacked
Hackers can infiltrate your WhatsApp account in various ways, often aiming to steal your personal information, intercept messages, or even impersonate you to scam your contacts.
Here are some red flags to watch out for:
- Suspicious Activity: Have you noticed messages being sent from your account that you didn’t write? This is a clear indication that someone else might be accessing your account.
- Unrecognized Linked Devices: WhatsApp lets you view a list of devices currently logged into your account. If you see unfamiliar devices listed, it could be a sign of unauthorized access.
- Missing Messages or Profile Changes: Were important messages deleted without your knowledge? Did your profile picture or name change unexpectedly? These actions could be signs of a hacker tampering with your account.
- Sudden Log Out: If you’re abruptly logged out of your WhatsApp account without explanation, it could be due to the hacker activating their device as the primary one.
Immediate Action: Taking Back Control
If you suspect your WhatsApp account has been hacked, act swiftly to regain control and minimize potential damage. Here’s what you need to do:
- Log Out of All Devices: First, log out of WhatsApp from all devices, including your phone, computer, or any other device where you might be logged in. This will prevent the hacker from further access. To do this, go to “Settings” > “Linked Devices” and tap “Log out from all devices.”
- Verify Your Phone Number: Request a new verification code for your phone number. This will prevent the hacker from using your account even if they have your login credentials. Go to “Settings” > “Account” > “Security” and tap “Two-step verification” (if not already enabled). Then, tap “Change Phone Number” and follow the on-screen instructions to verify your number with a new code.
- Enable Two-Step Verification: This adds an extra layer of security by requiring a six-digit PIN and your phone number to log in. Go to “Settings” > “Account” > “Security” and enable “Two-step verification.” Set a strong PIN that you can remember easily.
- Change Your Password: While WhatsApp doesn’t have a traditional password, you can change your account information. Go to “Settings” > “Tap on your profile picture” > “Edit” and change your name or profile picture if the hacker modified them.
- Report the Incident: Inform WhatsApp about the hacking attempt. While WhatsApp doesn’t have a formal reporting system within the app, you can contact WhatsApp Support through email. Briefly explain the situation and provide any relevant details.
READ ALSO: Cybersecurity Tips For Gambling
Preventative Measures: Keeping Your WhatsApp Secure
By following these practices, you can significantly reduce the risk of your WhatsApp account being compromised:
- Update WhatsApp Regularly: Cybersecurity vulnerabilities are constantly being discovered and patched. Keeping your WhatsApp app updated ensures you have the latest security fixes. Go to your app store and update WhatsApp whenever a new version is available. This is crucial!
- Strong Passwords & PINs: While WhatsApp doesn’t have a traditional password, consider using a solid PIN for two-step verification. Choose a complex combination of numbers and letters that is difficult to guess. Don’t reuse PINs or passwords across different platforms.
- Beware of Phishing Links: Phishing scams are a standard tactic hackers use to steal login credentials. Be cautious of suspicious links received in messages, even from known contacts. If a link seems untrustworthy, don’t click on it.
- Verification Before Sharing: Double-check the recipient before sending sensitive information or financial details through WhatsApp. Verify phone numbers or contact information to prevent sending messages to a compromised account.
- Enable Two-Step Verification: As mentioned earlier, enabling two-step verification adds a crucial layer of security. Don’t skip this critical step.
- Limit App Permissions: Review and adjust WhatsApp’s access permissions within your phone’s settings. Does WhatsApp need access to your location all the time?
READ ALSO: Kaspersky Security Flaw Exposes Millions to Hacks
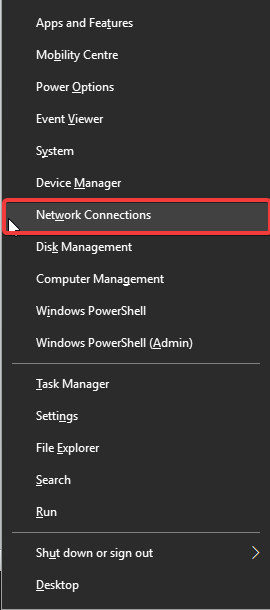
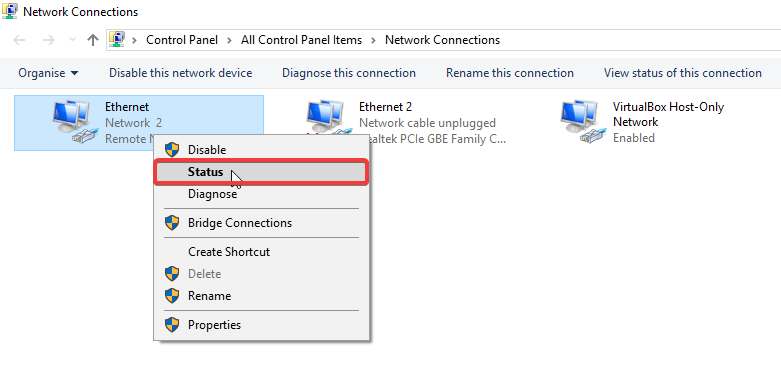
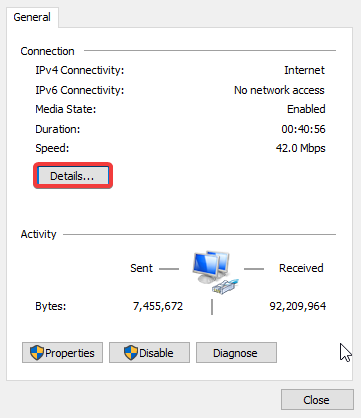
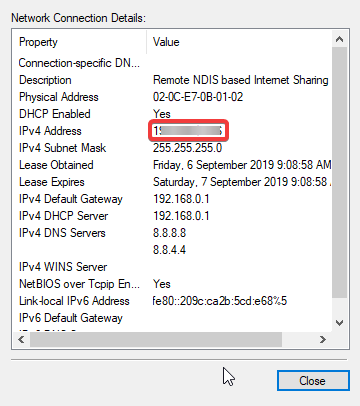
- Manage Linked Devices: Watch the devices linked to your WhatsApp account. Go to “Settings” > “Linked Devices” and review the list periodically. If you see any unfamiliar devices, log out of all devices immediately and follow the recovery steps mentioned earlier.
- Beware of Unwanted Group Invites: Malicious actors might use group invites to spread spam or malware. Be cautious of joining groups from unknown senders, especially if the group name or description seems suspicious.
- Scrutinize Third-Party Apps: Be wary of granting access to third-party apps that integrate with WhatsApp. These apps might request unnecessary permissions or contain vulnerabilities that could expose your account information. Only connect trusted third-party apps with a clear purpose.
- Regular Backups: Backing up your chat history is a good practice even if your account isn’t hacked. This allows you to restore essential messages in case of accidental deletion or phone loss. WhatsApp offers a built-in backup option to Google Drive or iCloud. Go to “Settings” > “Chats” > “Chat Backup” to configure backups.
- Report Suspicious Activity: If you encounter any suspicious activity on WhatsApp, such as spam messages or impersonation attempts, report them to WhatsApp. This helps them identify and address potential security threats.
Remember: Security is an ongoing process. By staying vigilant and following these best practices, you can significantly reduce the risk of your WhatsApp account being compromised.
Update your WhatsApp app regularly, avoid clicking on suspicious links, and enable two-step verification to create a robust defence against hacking attempts.
READ ALSO: How To Stop Calls On iPhone Without Blocking Them
Spreading Awareness: Educating Your Contacts
Social engineering tactics are a significant weapon in a hacker’s arsenal. By educating your contacts about common scams and security best practices, you can create a network of informed users who are less susceptible to falling victim to hacking attempts.
Share information about phishing scams, the importance of solid PINs, and how to identify suspicious activity on WhatsApp.
The Importance of a Layered Security Approach
Securing your WhatsApp account goes beyond just the app itself. Consider using a mobile security app on your phone that can provide additional protection against malware and phishing attempts.
Additionally, practising good internet hygiene – being cautious about the websites you visit and the information you share online – contributes to a layered security posture that safeguards your digital life.
By taking these steps and staying informed about evolving cybersecurity threats, you can ensure your WhatsApp experience remains secure and enjoyable.
Remember, a little vigilance goes a long way in protecting your privacy and maintaining control over your digital communication.
Note: This was initially published in October, 2019 but has been updated for freshness and accuracy.
RELATED POSTS
- 4 Top Music Streaming Services In The World
- How to Use Windows 7 Forever
- Full Review of VyprVPN VPN Service Provider
- How to Set Up a New Computer
- How To Secure Your WhatsApp Group From Hackers
- Hackers Target WhatsApp with Verification Scam
- How To Migrate From Windows 7 To Windows 10
- Android releases Patches for Critical Vulnerabilities