In this post, I will show you why your business needs a results-driven SEO strategy.
Owning a business in Western New York requires a specific kind of resilience. You know the market, you know the people, and you know the value of hard work. But in the current digital landscape, hard work alone isn’t enough to guarantee visibility. You could offer the best service in Erie County, but if your customers can’t find you on the first page of Google, you might as well be invisible.
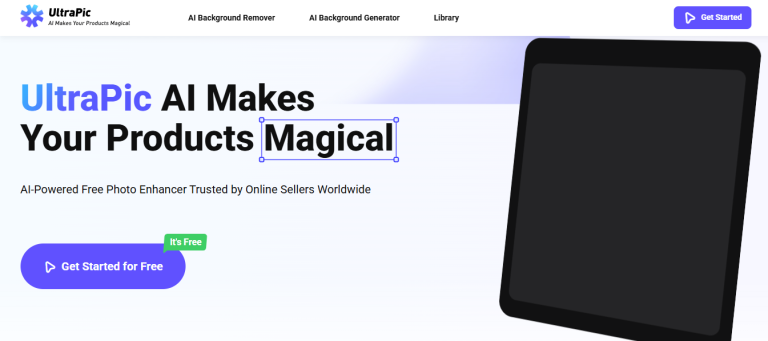
This is where the distinction between a generic marketing agency and a specialized partner becomes critical. You don’t just need a website; you need a machine that generates leads. You need a results-driven Buffalo, NY SEO company that understands the local landscape and knows exactly how to put your brand in front of the right eyes.
We aren’t here to offer vague promises or confusing jargon. We are here to talk about tangible growth, measurable ROI, and the kind of digital dominance that turns small local businesses into industry leaders.
Table of Contents
The Problem with “Set It and Forget It” Websites
Many business owners fall into the trap of thinking that launching a website is the finish line. In reality, it’s just the starting block. A beautiful website that sits on page four of search results is like a billboard in the middle of a dense forest—it looks great, but nobody sees it.
Search Engine Optimization (SEO) is the fuel that drives traffic to that billboard. However, the algorithms that power Google and Bing are constantly shifting. What worked five years ago could actually penalize your site today.
We approach SEO as an ongoing, dynamic campaign rather than a one-time checklist. Our team constantly monitors algorithm updates, shifts in consumer search behavior, and competitive movements within the Buffalo market. This proactive stance ensures that your business doesn’t just climb the rankings but stays there.
What Does “Results-Driven” Actually Mean?
In the marketing world, it is easy to hide behind “vanity metrics.” An agency might show you a report saying your impressions are up by 200%. That sounds fantastic, but can you pay your staff with impressions? Can you reinvest “likes” into new equipment?
As a results-driven Buffalo, NY SEO company, we focus on the metrics that actually impact your bottom line. We look beyond the surface level to track:
- Qualified Leads: Are the people visiting your site actually interested in buying your product or service?
- Conversion Rates: How many visitors are picking up the phone or filling out a contact form?
- Cost Per Acquisition: How efficiently are we turning marketing dollars into new revenue?
- Local Visibility: Are you showing up in the “Map Pack” when someone in Amherst, Cheektowaga, or downtown Buffalo searches for your services?
Our strategy is reverse-engineered from your business goals. If you need to sell more of a specific product or fill a specific service schedule, our SEO efforts are tailored to drive traffic to those exact pages.
The Buffalo Advantage: Winning the Local Market
National SEO agencies often treat every client the same, applying a cookie-cutter strategy whether the business is in Miami, Seattle, or Buffalo. This is a mistake. Western New York is a unique market with specific search patterns and consumer behaviors.
When you partner with a local team, you get the advantage of geographic expertise. We understand the seasonality of the region—how search intent changes from the snowy winters to the bustling summers. We know the local neighborhoods and how people in WNY refer to things (it’s “pop,” not “soda,” after all).
Mastering Local SEO
Local SEO is about more than just keywords; it’s about proximity and relevance. When a potential customer pulls out their phone and searches for “best contractor near me” or “emergency plumber Buffalo,” Google uses specific signals to decide who to recommend.
We optimize your Google Business Profile (formerly Google My Business) to ensure you are the most trustworthy and relevant option. We manage your local citations to ensure your name, address, and phone number are consistent across the web. We also help you implement a strategy for gathering and managing reviews, which is a massive ranking factor for local businesses.
By dominating the local search results, you effectively block out competitors who are relying on outdated or national strategies.
Our Three-Pillar Approach to SEO Success
Being a results-driven Buffalo, NY SEO company means having a comprehensive strategy that covers all bases. We break our service down into three core pillars that support sustainable growth.
1. Technical SEO Foundation
Think of this as the foundation of a house. If the foundation is cracked, it doesn’t matter how nice the paint is. We perform deep-dive audits into your website’s code and structure. We look for:
- Site Speed: Does your site load instantly? If not, users (and Google) will leave.
- Mobile Responsiveness: Is the experience seamless on a smartphone?
- Crawlability: Can search engine bots easily read and index your pages?
- Security: Is your site using HTTPS protocols to protect user data?
We fix the technical errors that are silently killing your rankings, ensuring your site is a high-performance vehicle ready for traffic.
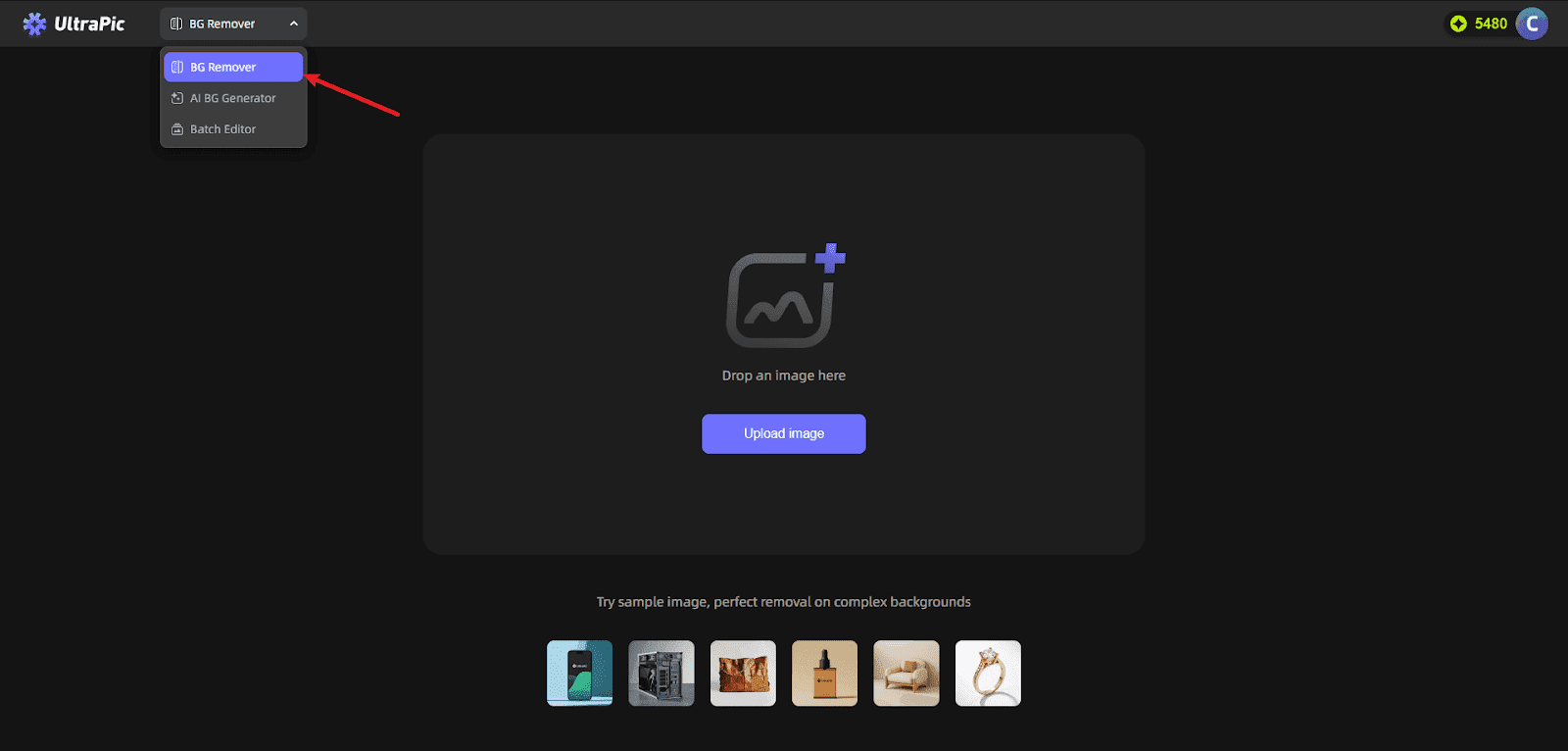
2. On-Page Optimization and Content Strategy
Content is still king, but it has to be the right content. We don’t just stuff keywords into paragraphs. We create valuable, authoritative content that answers the specific questions your customers are asking.
We optimize your existing pages to ensure headlines, meta descriptions, and image tags are all aligned with high-value search terms. Then, we build a content calendar designed to establish your brand as the local authority in your industry. When Google sees that you provide the best answers, it rewards you with the top spot.
3. Off-Page Authority Building
This is how the internet “votes” for your website. When other reputable websites link back to yours, it tells search engines that you are a trusted resource.
However, not all links are created equal. One link from a high-authority local news site or an industry-specific association is worth a thousand links from low-quality directories. We use white-hat, ethical link-building strategies to grow your site’s authority naturally and safely. We protect your domain’s reputation while aggressively expanding your digital footprint.
Transparency You Can Trust
The SEO industry, unfortunately, has a reputation for being a “black box.” You pay a monthly fee, and you aren’t quite sure what is happening behind the scenes.
We operate differently. We believe that an informed client is our best partner. You will receive detailed, easy-to-understand reporting that shows exactly what we did, how your rankings have improved, and most importantly, how much traffic and revenue have been generated.
We meet with you regularly to review the data and adjust the strategy. If a particular keyword is performing exceptionally well, we double down. If a page isn’t converting as expected, we tweak the design or copy. We remain agile and transparent every step of the way.
Ready to Outpace the Competition?
Results-driven Buffalo NY SEO company helps your business seize the digital opportunities in Western New York’s competitive market. While your competitors may already be investing in search marketing, partnering with a company focused on measurable results ensures your SEO strategy outperforms the competition and drives real growth.
Don’t let another month go by where potential customers are clicking on your competitor’s website simply because they appeared first. It is time to reclaim your market share.
Partner with a team that cares about your growth as much as you do. Choose the results-driven Buffalo, NY SEO company that puts revenue over vanity metrics. Let’s discuss how we can build a custom strategy to take your business to the top of the search results—and keep it there.
INTERESTING POSTS
- How To Measure SEO Success: KPIs You Need To Track
- What Is A Certificate Authority (CA) And What Do They Do?
- Best SEO Agency in Dubai Rise Powering Rankings, Traffic, and Digital Success
- SEO Companies: Red Flags That You Are In The Wrong Company
- How to Build a Strong Cybersecurity Foundation
- How To Get Money Back From A Scammer On Western Union