This is a comprehensive review of ClevGuard KidsGuard Pro for Android, a phone monitoring app. As a parent, you oftentimes wonder what your kids are up to when they are out of your sight and control; you’re not alone in this.
For this reason, several parental control/monitoring apps have been developed to help parents keep an eye on their children’s locations and activities.
One such monitoring app that has gained popularity due to its stealth mode is ClevGuard’s KidsGuard Pro for Android. This review will focus on everything you need to know about KidGuard Pro, including how to install and activate KidGuard Pro in stealth mode on your kids’ devices.
ClevGuard Company Overview
ClevGuard is an IT company focused on cybersecurity solutions. We see the knowledge of anti-spyware production being applied in the design and development of KidsGuard Pro, as it has quickly gained ground as a monitoring app that can remain undetected on your target’s phone due to its stealth mode. You can also learn how to hack mobile call history online using KidsGuard Pro.
Hence, their products are designed to protect you from the ills of the internet, which include spyware that monitors your camera and microphone and collects and transmits data from your keyboard.
What Is KidsGuard Pro?
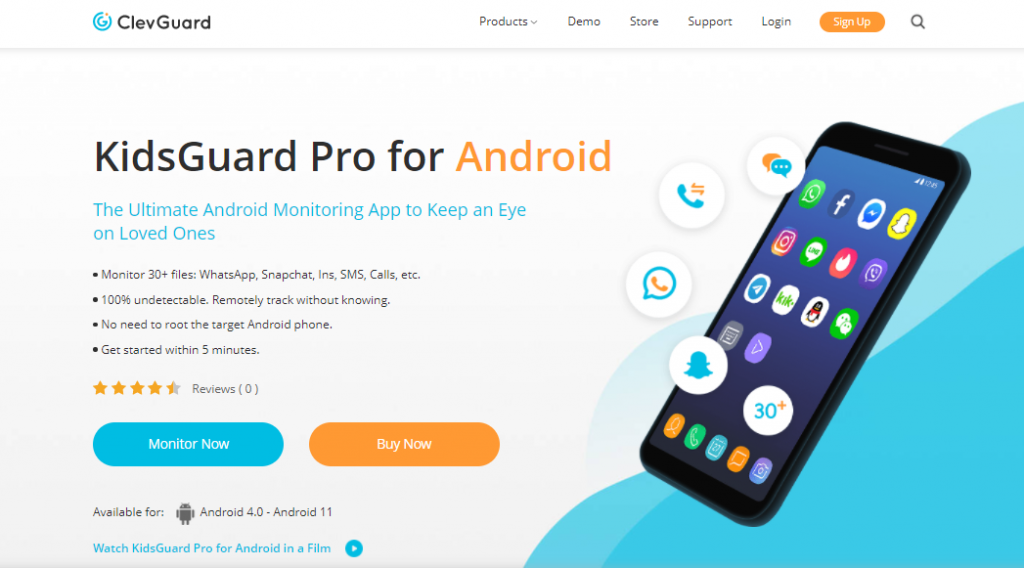
KidsGuard Pro is a kid’s monitoring solution that allows you to track your child’s social media usage, phone calls, location, and more. Additionally, it enables you to remotely control the camera and microphone on your child’s device, allowing you to secretly take snapshots and record conversations.
Overall, KidsGuard grants you remote access to your kids’ smartphones without you leaving any clue that they are being monitored.
Features of KidsGuard Pro
Installation without rooting an Android device
When installing KidsGuard Pro, our team didn’t need to worry about rooting an Android device, which can be quite damaging or possibly result in an irrecoverable phone brick.
So, not worrying about rooting your target’s Android device is a big relief; thus, having access to your kid’s phone once for 5 minutes or less is enough to set up KidsGuard Pro on your kid’s device without raising any suspicion or getting caught.
Monitor your kid’s social media usage
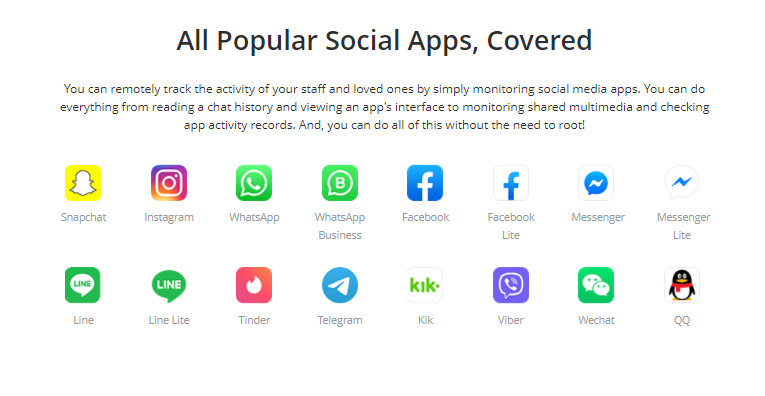
KidsGuard Pro boasts of monitoring more than 16 social media apps. Interestingly, this is a verifiable claim proven by our software testing crew, who have successfully used KidsGuard Pro to monitor popular social media platforms, including WhatsApp, Telegram, Instagram, Facebook, WeChat, Tinder, and Viber.
If you choose to monitor your child’s WhatsApp conversation, you can view their sent and received messages.
Monitor Location
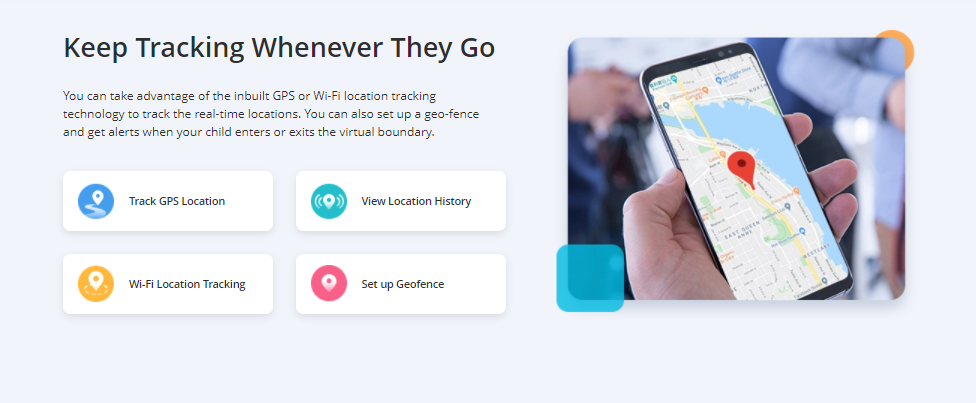
All parental monitoring apps can monitor locations, but what sets KidsGuard Pro apart is its geofence feature. When you set a geofence by circling off areas that are off-limits to your kids, you get an email/SMS notification when your kid crosses the geofence.
Remotely gain access to your kid’s device
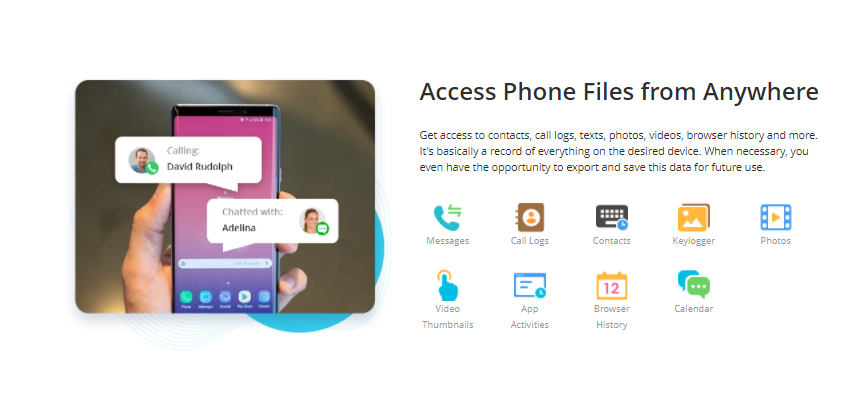
KidsGuard Pro lets you remotely control your kid’s camera, microphone, Phonebook, Message, browsing activities, etc., from your device.
Our team was able to take screenshots remotely, capture photos, record calls, and remotely monitor browsing history. This implies that you can stay informed about what your child is doing at any time by gaining remote access to their Android device.
Export Data
The downside to this feature is that you can only export data from your dashboard in CSV format. To generate and export data, navigate to the left side of your dashboard and select the required data module. Our team is hopeful that soon, KidsGuard users will be able to export data in PDF, HTML, or Excel format.
How To Set Up KidsGuard Pro On An Android Device
Setting up KidsGuard Pro on a target device is extremely fast and easy, requiring no special IT skills. The following steps will guide you through setting up KidsGuard Pro in just 5 minutes.
- Sign up with KidsGuard Pro and subscribe to a suitable Plan. KidsGuard offers flexible plans and subscription packages, which can sometimes be a bit confusing when choosing a package that suits your needs and budget.
- After signing up and subscribing to a subscription package, you get a device code to activate KidsGuard monitoring on your target device.
- Use your child’s phone browser to access KidsGuard Pro’s official website and download and install KidsGuard Pro on their device.
- Grant permission to install applications from an unknown source when prompted to do so during installation.
- After a successful installation, use your username and code generated in step 2 above to activate KidsGuard Pro on your child’s Android device, enabling you to monitor their device from any device and browser.
- Clear your browsing history, and delete the KidsGuard Pro APK file to erase all traces of your activities and KidsGuard’s presence on your target’s device.
READ ALSO: 6 Online Security Tips for Kids
KidsGuard Pro Plans And Pricing
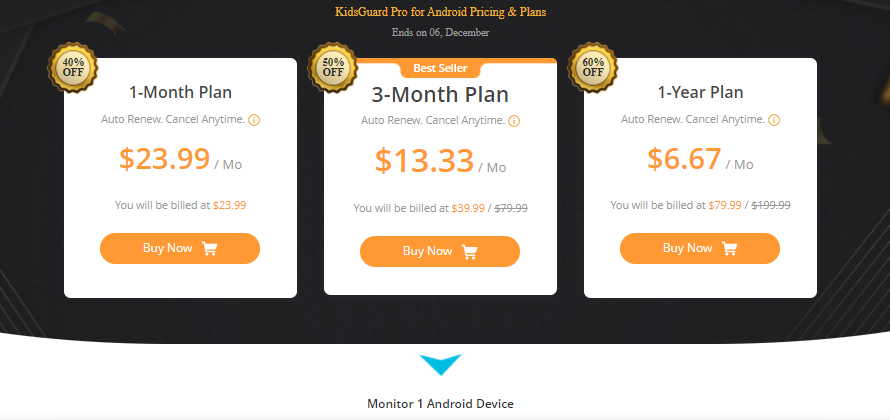
Here are its pricing plans:
- Month Plan: $49.99 per month, gives you access to all premium KidsGuard features
- 3-Month Plan: $75.99 for 3 months, billed at $25.33 per month.
- 1-year Plan: $139.99, billed at $11.66 per month.
At $11.66 per month for a yearly plan, KidsGuard Pro is quite inexpensive. Additionally, you are entitled to a 30-day money-back guarantee, during which you can request a refund if you’re not satisfied with KidsGuard Pro.
Note: The system requirement for this parental control software is Android OS version 4.0 and higher.
Customer Support
24/7 customer support and correspondence are available for all customers and prospective users via email and LiveChat. The Speed and ease of correspondence by email beat my imagination, but the fact remains that you cant get instant technical support offered via dedicated helplines.
KidGuard’s Pro LiveChat feature provides access to customer support personnel for immediate issue resolution, without the benefit of voice communication.
KidsGuard Pro’s FAQ page is a comprehensive collection of issues and solutions that have helped make users’ experiences excellent.
Is KidsGuard Pro Safe To Use?
Based on this ClevGuard KidsGuard Pro For Android review, I assure you that the app is safe to use. It doesn’t have any adverse effect on the device on which it is installed, and you can uninstall Kidsgard Pro completely whenever you change your mind. Also, KidsGuard is a virus-free app that encrypts and protects users’ data.
KidsGuard Pro Review: Frequently Asked Questions
What is ClevGuard KidsGuard Pro for Android?
ClevGuard KidsGuard Pro for Android is a parental monitoring app designed to help parents track their kids’ smartphone activities. It lets you monitor calls, messages, social media usage, location, and even remotely control the camera and microphone — all in stealth mode, meaning your child won’t know it’s running.
Is KidsGuard Pro safe to use on Android devices?
Yes, KidsGuard Pro is completely safe to use. It’s a virus-free app that doesn’t harm your child’s Android device. All user data is encrypted and protected, and you can uninstall it at any time without leaving any traces.
READ ALSO: Tips For Keeping Children Safe Online [Detailed Guide For Parents]
Does KidsGuard Pro require rooting the Android device?
No, KidsGuard Pro doesn’t require rooting. You can easily install it within 5 minutes, without any technical expertise or risk of damaging your device. This makes it a safe and hassle-free choice for parents.
What features does KidsGuard Pro offer?
KidsGuard Pro offers powerful features such as:
- Monitoring calls, messages, and 16+ social media apps (e.g., WhatsApp, Facebook, Instagram).
- GPS location tracking and geofencing alerts.
- Remote access to the camera, microphone, and screenshots.
- Data export (CSV format).
These features provide parents with full visibility into their child’s smartphone use.
How do I install KidsGuard Pro on my child’s device?
- Sign up on the official KidsGuard Pro website.
- Choose a subscription plan and get your device activation code.
- Download and install the app on your child’s phone via their browser.
- Grant permission to install from unknown sources.
- Log in and activate the app using the code provided.
- Clear browsing history and delete the APK file to stay discreet.
What devices are compatible with KidsGuard Pro?
KidsGuard Pro works with Android OS version 4.0 and above. It supports most Android smartphones and tablets commonly used by children.
Can I monitor my child’s location in real-time?
Yes, KidsGuard Pro includes real-time GPS tracking and a geofencing feature. You’ll receive instant alerts when your child enters or leaves specific areas you’ve marked as safe or restricted zones.
How can I contact KidsGuard Pro customer support?
ClevGuard provides 24/7 customer support through LiveChat and email. The response time via email is impressively fast, although a phone hotline is not currently available. LiveChat connects you instantly with support staff for quick issue resolution.
Is KidsGuard Pro worth it?
Absolutely. Based on hands-on testing, KidsGuard Pro provides exceptional value for parents seeking peace of mind. It’s affordable, easy to use, and operates in stealth mode, making it one of the most effective parental control apps available today.
Conclusion
The above ClevGuard KidsGuard Pro for Android review demonstrates that it is an exceptional parental monitoring app that offers more for less.
With KidsGuard Pro, you can monitor your kid’s outdoor and indoor activities and whereabouts without raising any suspicion. You can record calls remotely, read SMS, monitor social media activities, and more.
Based on this, I will recommend KidsGuard Pro as one of the best parental monitoring apps that allows you to monitor all your child’s activities in stealth mode.
- Get KidsGuard Pro
INTERESTING POSTS
- The Ultimate Revelation Of Best Apps For Parental Control
- Best Parental Control Software
- iMyFone Video Editor Review
- How IT Professionals Can Monitor Remote Employees’ PCs Without Violating Privacy Laws
- 4 Essential Cybersecurity Tips To Implement When Working Remotely
- Kytephone Parental Control Review
- What Is The Best Country For VPN Anonymity?


![What Is The Aim Of An ARP Spoofing Attack? [Here’s The Answer] What Is The Aim Of An ARP Spoofing Attack? [Here’s The Answer]](https://secureblitz.com/wp-content/uploads/2022/07/What-is-the-aim-of-an-ARP-spoofing-attack-768x345.png)






![Programs For Mining On Different Hardware [MUST READ] Programs For Mining On Different Hardware [MUST READ]](https://secureblitz.com/wp-content/uploads/2022/03/The-Programs-For-Mining-On-Different-Hardware-768x402.png)







![How To Avoid Malicious Chrome Extensions [8 PROVEN Methods] How To Avoid Malicious Chrome Extensions [8 PROVEN Methods]](https://secureblitz.com/wp-content/uploads/2021/05/How-To-Avoid-Malicious-Chrome-Extensions-768x402.png)