Here, I will show you the top proxy service providers in 2026.
In today’s digital age, privacy and security are paramount. Whether you’re a small business owner, a freelancer, or an individual seeking to safeguard your online activities, using a proxy service is a prudent choice.
Proxies act as a middleman between you and the internet, offering a layer of anonymity and security. However, with so many proxy providers, finding the best one for your needs can be challenging.
In this comprehensive guide, we’ll explore the top proxy service providers, their features, performance, and pricing plans. Get ready to take control of your internet freedom.
Understanding the Importance of Proxy Services
The internet has websites that track your every move, third-party advertisers that collect your data, and geo-restrictions that limit your access to certain content.
Proxy services solve these issues as intermediaries between your device and the websites you visit. With a proxy, your online activities are routed through a different IP address, making it difficult for websites to track your true identity.
Additionally, proxies can help you bypass geo-restrictions and access content otherwise unavailable in your region. Whether you’re concerned about your privacy, want to access blocked websites, or need to gather publicly available data, a reliable proxy service is essential.
The Criteria for Selecting the Top Proxy Service Providers
Choosing the right proxy service provider can be daunting, given the many options available. To narrow down the list, we evaluated each provider based on several key criteria:
- Proxy Pool Size: A larger proxy pool allows for more IP options and better performance.
- Response Time: Faster response times ensure smooth browsing and data retrieval.
- Supported Protocols: Proxies that support a variety of protocols offer greater compatibility.
- City-Level Targeting: The ability to select proxies in specific cities enhances flexibility.
- Pricing: The cost-effectiveness of the service in relation to its features and performance.
- Encryption and Security: Proxies that prioritize user privacy and data protection.
- Customer Support: Responsive and knowledgeable support is crucial for a seamless experience.
Based on these criteria, we have compiled a list of the top proxy service providers. Let’s dive into the details of each provider and explore their unique offerings.
Best Proxies Deals
Featured Top Proxy Service Providers
1. Oxylabs – Best for Enterprise-Grade Proxy Solutions
Oxylabs offers an extensive network of over 175 million residential proxies, covering all countries and cities worldwide. Users can achieve precise proxy selection for their specific needs with additional targeting options based on the autonomous system number (ASN).
Oxylabs also provides static, non-rotating residential proxies procured directly from ISPs, balancing speed and resilience. Unlike the standard rotating residential proxies, these static proxies support the SOCKS5 protocol.
In addition to residential proxies, Oxylabs offers a pool of over 2 million data center IPs dedicated exclusively to each user. These data center proxies also support the SOCKS5 protocol and can be automatically rotated using the proxy rotator add-on.
Oxylabs stands out with its next-gen residential proxies, which leverage machine learning and AI to mimic regular browsing behavior. This advanced technology helps bypass blocks and captchas more effectively.
Oxylabs provides a convenient solution for web scraping tasks with its Scraper APIs tool. Users can retrieve data in HTML or JSON format, streamlining the data-gathering process.
Oxylabs offers tiered pricing plans to accommodate different user needs. As the commitment level increases, the cost per proxy decreases, making it more cost-effective for larger-scale users.
Key Features of Oxylabs:
- Extensive network of over 175 million+ residential proxies worldwide.
- Targeting options based on autonomous system number (ASN).
- Static non-rotating residential proxies for speed and resilience.
- Next-gen residential proxies with machine learning and AI capabilities.
- Data center proxies with automatic rotation using the proxy rotator add-on.
- Scraper APIs for streamlined web scraping tasks.
Best for: Large enterprises, data scraping at scale, market research, and cybersecurity firms.
Why Choose Oxylabs? If you need a robust, secure, and scalable proxy solution backed by cutting-edge technology, Oxylabs is a top-tier choice.
2. Decodo (formerly Smartproxy) – Best for Versatile and User-Friendly Proxies
Decodo (formerly Smartproxy) stands out for its vast pool of high-quality IPs, ease of use, and competitive pricing. With over 55 million rotating residential proxies and a total of 65 million+ IPs across 195+ locations, Decodo offers unmatched flexibility for web scraping, automation, and data collection.
All residential proxies now come with a limited-time 40% discount (Use Code: RESI40), while other products offer a free trial for new users.
Decodo ensures blazing-fast speeds (<0.3s avg response time) and 99.99% uptime, making it one of the most reliable providers. The quick rotation policies prevent detection and bans, while HTTPs and SOCKS5 support adds extra versatility.
Smartproxy’s intuitive dashboard allows users to filter proxies by location and session type (rotating or sticky). Additionally, browser extensions for Chrome and Firefox make proxy management seamless while browsing.
Pricing is bandwidth-based, with pay-as-you-go and monthly subscription options.
Key Features of Decodo:
- 55 million+ rotating residential proxies (Use Code RESI40 for 40% off)
- 65 million+ total IPs across 195+ locations
- <0.3s average response time with 99.99% uptime
- Free trials available for all non-residential products
- Easy setup with an intuitive dashboard and browser extensions
- Supports both HTTPs and SOCKS5 protocols
- Fast customer support response (40s average wait time)
Best For: Digital marketers, social media managers, sneaker copping, and general web scraping.
Why Choose Decodo? If you’re looking for a versatile, high-performance proxy service with competitive pricing and seamless usability, Decodo is an excellent choice.
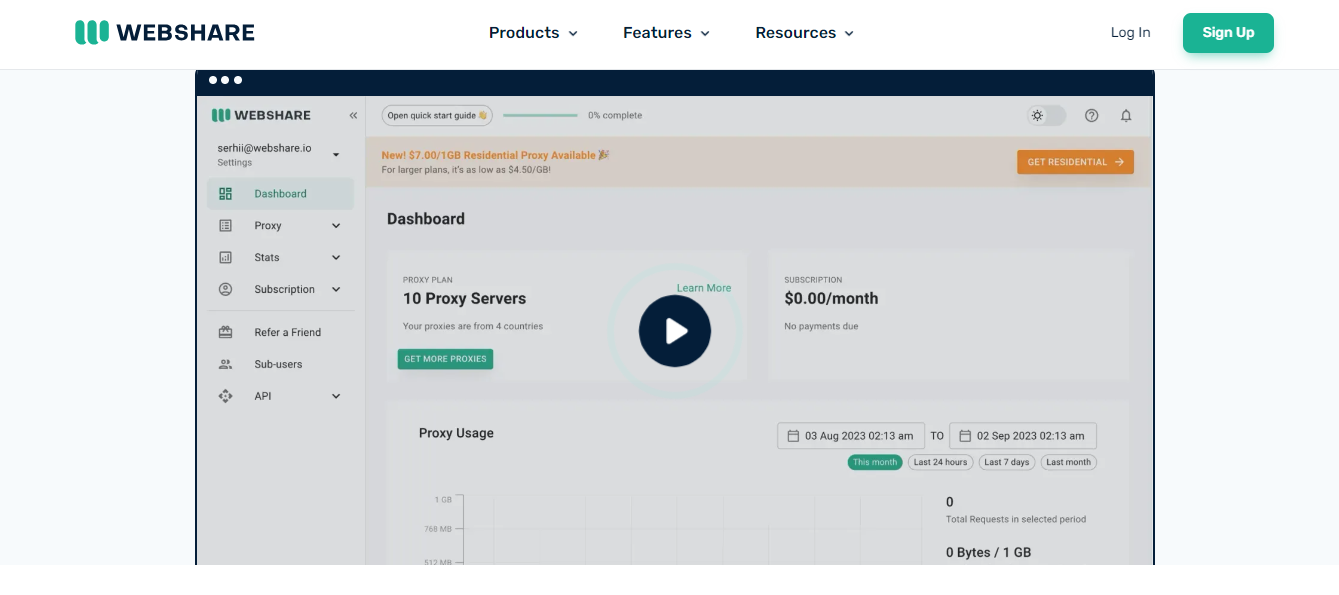
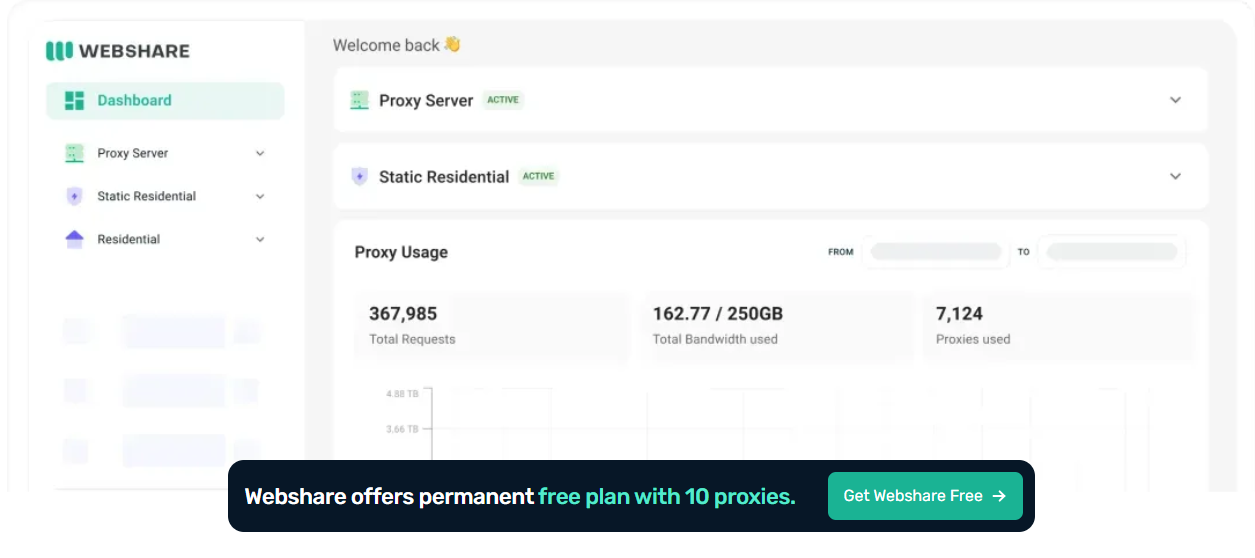
3. Webshare – Best for Budget-Friendly Proxy Solutions
Webshare strongly emphasizes privacy and security, offering a reliable proxy service with robust speed monitoring. With its claim of being the fastest proxy service provider, Webshare aims to deliver exceptional browsing speed and performance. The global proxy network is fully encrypted and protected, ensuring a secure browsing experience.
Webshare supports both HTTP and SOCKS5 proxy protocols, providing flexibility and compatibility. Users can choose between authentication or password authentication, depending on their specific requirements.
One standout feature of Webshare is its available free proxy plan. Although limited to 10 free IPs, this permanent plan does not require a credit card, allowing users to test the service without any financial commitment. Webshare offers several paid plans with different tiers and features to suit various user needs.
While Webshare offers attractive features such as a free tier, high-level security, and emphasis on anonymity, it does lack in some areas. Limited support options and fewer proxy locations may be drawbacks for some users. Nonetheless, the free proxy plan is worth determining if Webshare meets your needs.
Key Features of Webshare:
- Free trial available with 10 free IPs.
- Available free tier without a time limit.
- Robust speed monitoring for optimal performance.
- Emphasis on privacy and security.
- Multiple paid tiers for different user needs.
- Support for HTTP and SOCKS5 protocols.
Best for: Small businesses, freelancers, casual users, and those on a budget.
Why Choose Webshare? If you’re looking for an affordable yet reliable proxy solution with flexible pricing, Webshare is the way to go.
Other Top Proxy Service Providers In 2026
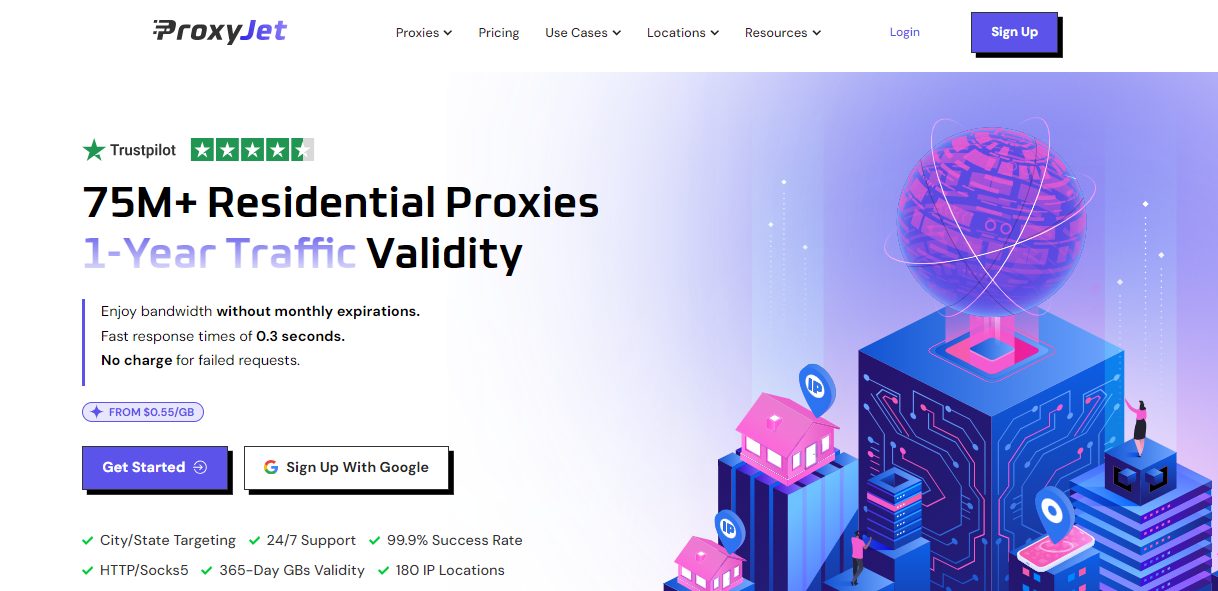
1. ProxyJet – Best for High-Speed and Reliable Performance
When it comes to choosing a reliable and versatile proxy service provider in 2026, ProxyJet stands out as a top contender. This premium provider delivers a comprehensive range of proxy solutions designed to meet the evolving needs of both casual users and businesses.
ProxyJet offers high-speed, highly anonymous proxies that guarantee privacy and secure access to restricted content. Whether you need proxies for data scraping, bypassing geo-restrictions, or managing social media accounts, ProxyJet’s network covers it all with impressive global reach.
One of ProxyJet’s key strengths is its focus on user convenience. With dedicated IP pools, multiple locations worldwide, and seamless compatibility with popular tools and software, ProxyJet offers a service that is easy to integrate and use.
Their robust infrastructure ensures low latency and uptime, making it ideal for users who demand performance and reliability. Combine that with competitive pricing tiers and round-the-clock customer support, and ProxyJet becomes the go-to choice for unlocking true internet freedom.
==>> Get ProxyJet
2. Live Proxies – High-Performance Proxy Solutions with Advanced Features
Live Proxies provides a premium range of rotating mobile, rotating residential, and static residential proxies designed for businesses and individuals who require high anonymity, low detection rates, and reliable performance. Their solutions are optimized for tasks like web scraping, social media automation, sneaker copping, market research, and bypassing geo-restrictions.
Key Features of Live Proxies
- Rotating & Sticky IPs – Live Proxies offers both rotating and sticky sessions, allowing users to maintain the same IP for up to 60 minutes or opt for frequent IP changes, depending on their needs.
- Real Residential & Mobile IPs – Their IPs originate from legitimate home and mobile networks, ensuring high trust scores and lower chances of detection.
- Global Coverage – Live Proxies provides IPs from numerous countries, including the US, UK, Canada, and more, making it ideal for location-based tasks.
- Unlimited Bandwidth & High Uptime – Select unmetered plans ensure unrestricted data usage, with a 99.9% uptime guarantee for seamless browsing and scraping.
- Private IP Allocation – Users receive exclusive IPs that are not shared with other customers targeting the same platforms, improving reliability.
- Easy Integration & Developer-Friendly – Live Proxies supports HTTP, HTTPS, and SOCKS5 (upon request) protocols and offers an easy-to-use API for seamless integration with third-party tools.
Pricing & Plans
Live Proxies offers flexible pricing plans tailored for both individual users (B2C) and business clients (B2B):
- Rotating Mobile Proxies – Starting at $55 for 4GB/month, with 3G, 4G, and 5G support.
- Rotating Residential Proxies – Available from $45 for 4GB/month, ideal for web scraping and ad verification.
- Static Residential Proxies – From $65 for 50 IPs/month, perfect for account management and eCommerce operations.
- Enterprise Solutions – Custom plans with dedicated IP allocations for large-scale operations.
Why Choose Live Proxies?
With its high-speed, undetectable proxies, exclusive private IP pools, and dedicated support, Live Proxies is a top-tier provider for businesses and individuals who demand secure, reliable proxy solutions. Whether you need proxies for SEO monitoring, sneaker bots, social media, or brand protection, Live Proxies ensures maximum anonymity and stability.
==>> Visit Live Proxies to explore their proxy solutions.
3. IPRoyal: Affordable Proxies for Various Use Cases
IPRoyal stands out for its versatile selection of proxies and cost-effective pricing. With over 2 million ethically sourced residential proxies from 195 countries, IPRoyal offers a wide range of options for various use cases.
Additionally, IPRoyal provides 6 million IPs from data center proxies and niche-specific sneaker proxies, catering to different user preferences.
IPRoyal’s user interface is beginner-friendly, making it easy to navigate and utilize the available features. The support services provided by IPRoyal are exceptional, ensuring that users receive prompt assistance when needed. However, the limited self-help documentation may require contacting the IPRoyal team for more complex issues.
IPRoyal offers different subscription options to accommodate various user needs. The pricing is among the most affordable in the market, making it an attractive choice for individuals and businesses.
With responsive customer support, various proxies, and competitive pricing, IPRoyal is a leading proxy service provider.
Key Features of IPRoyal:
- Over 2 million ethically sourced residential proxies from 195 countries.
- 6 million data center proxies and niche-specific sneaker proxies.
- Beginner-friendly user interface.
- Exceptional support services.
- Affordable pricing options.
- Versatile selection of proxies for different use cases.
4. ColdProxy – Best for Flexible Pricing and Scalable Proxy Infrastructure
ColdProxy is a proxy infrastructure provider offering flexible proxy solutions for businesses, developers, agencies, and data-driven teams. With access to over 70 million IPs across 195+ countries and locations, ColdProxy supports use cases such as web scraping, automation, SEO monitoring, ad verification, market research, and geo-targeted data collection.
What makes ColdProxy stand out is its flexibility. The platform offers multiple proxy options, including residential IPv4, residential IPv6, and datacenter IPv6 proxies. Users can choose between different pricing models, bandwidth options, speed tiers, and plan durations, including hourly, daily, weekly, and monthly plans depending on the product.
ColdProxy is designed for users who need stable performance and scalable access without being locked into one fixed model. Whether a user needs pay-per-GB bandwidth, unmetered traffic, rotating sessions, or sticky sessions, ColdProxy provides options that can be adjusted based on workload size and operational needs.
The platform supports HTTP(S) and SOCKS5 protocols, making it compatible with most browsers, automation tools, scraping frameworks, and data workflows. ColdProxy also provides geo-targeting options such as country, city, ZIP and ASN-level targeting, which is useful for localized testing, ad verification, SEO tracking, and region-specific data collection.
Key Features of ColdProxy
- Over 70 million IPs across 195+ countries and locations
- Residential IPv4, residential IPv6, and datacenter IPv6 options
- Flexible pricing, including pay-per-GB and unmetered plans
- Hourly, daily, weekly, and monthly plan options depending on the product
- Different bandwidth and speed configurations
- Rotating and sticky session support
- HTTP(S) and SOCKS5 protocol compatibility
- Geo-targeting by country, city, ZIP and ASN
- Stable performance for automation, scraping, and monitoring workflows
- 24/7 customer support
Best For:
ColdProxy is best for users who need flexible proxy infrastructure for web scraping, automation, SEO monitoring, ad verification, localized testing, and large-scale data collection.
Why Choose ColdProxy?
ColdProxy is a strong option for users who need a balance of flexibility, scalability, and performance. Its range of proxy types, pricing models, session options, and geo-targeting capabilities makes it suitable for both smaller projects and larger operational workflows.
5. DigiProxy: Powerful Residential Proxy Network With Global Reach
DigiProxy stands out as a premium proxy service provider offering high-speed, high-anonymity residential proxies optimized for diverse use cases. Whether you’re engaged in web scraping, SEO monitoring, ad verification, market research, or sneaker copping, DigiProxy provides a secure and reliable proxy network with flexible features.
With millions of residential IPs across 100+ countries, DigiProxy ensures seamless browsing, low detection rates, and robust performance. The service supports HTTP and SOCKS5 protocols, making it compatible with most tools and automation frameworks.
DigiProxy also offers a user-friendly dashboard for real-time analytics and IP management, along with 24/7 customer support to assist with technical needs.
Key Features of DigiProxy:
- Large pool of ethically sourced residential IPs in 100+ countries
- Fast and stable connections with automatic IP rotation
- Support for HTTP and SOCKS5 protocols
- High anonymity and low block rate
- Real-time dashboard with detailed usage insights
- Scalable pricing plans for individuals and enterprises
- 24/7 customer support
DigiProxy is a solid choice for users who demand reliability, speed, and global coverage in their proxy services.
==>> Get DigiProxy
6. Bright Data: Extensive Proxy Pool and Advanced Targeting Options
Formerly known as Luminati, Bright Data boasts an impressive proxy pool of over 72 million IP addresses. This vast selection of proxies includes rotating residential IPs, static residential IPs, and mobile IPs.
With coverage in all countries and cities, Bright Data offers comprehensive targeting options, allowing users to fine-tune their proxy usage based on specific requirements.
Bright Data provides a Proxy Manager, an open-source tool compatible with Windows, macOS, and Linux. This tool enables users to define rules for IP rotation, optimize bandwidth usage, and blacklist IPs that yield poor results. With support for HTTP, HTTPS, and SOCKS5 protocols, Bright Data ensures compatibility with various applications.
While Bright Data offers many features and exceptional proxy capabilities, pricing can be complex. Additional parameters, such as targeting levels, impact the final cost of the proxy.
Monthly subscriptions and pay-as-you-go plans are available to accommodate different user needs. Bright Data’s pricing may be higher than its peers, but it is justifiable for large-scale proxy users with specific requirements.
Key Features of Bright Data:
- A vast proxy pool of over 72 million IPs.
- Coverage in all countries and cities.
- Rotating residential IPs, static residential IPs, and mobile IPs.
- Proxy Manager for customizable IP rotation and bandwidth optimization.
- Support for HTTP, HTTPS, and SOCKS5 protocols.
- Comprehensive support infrastructure.
7. Rampage Retail: Cutting Out the Middleman for Lower Costs
Rampage Retail takes a unique approach by buying proxies from leading providers and reselling them wholesale. This strategy allows users to access high-quality proxies at lower rates, as Rampage Retail can leverage higher-end plans at a reduced cost. By cutting out the middleman, Rampage Retail offers cost-effective options to its customers.
With an extensive database of proxies, Rampage Retail offers a wide selection of IP options for different user needs. The simplified tier structure and global proxy coverage make finding proxies that fit specific requirements easy. However, limited support options and the absence of a free trial or tier may be drawbacks for some users.
Rampage Retail is a promising option for those seeking affordable proxies without compromising quality. The transparent approach to pricing and access to leading proxy services make it a compelling choice for various use cases.
Key Features of Rampage Retail:
- Lower costs through wholesale access to leading proxy services.
- Simplified tier structure for easy selection.
- Global proxy coverage for versatile use cases.
- Lower prices compared to direct provider purchases.
- Extensive database of proxies for diverse IP options.
READ ALSO: Oxylabs Black Friday 2025 Deals
Top Proxy Service Providers: Frequently Asked Questions
What are proxy service providers?
Proxy service providers are companies that offer proxy services to individuals and businesses. These services allow users to route their internet traffic through proxy servers, enabling them to access the internet with different IP addresses and enhanced privacy.
What factors should I consider when choosing a proxy service provider?
When choosing a proxy service provider, consider factors such as:
- Type of Proxies: Choose data center, residential, or mobile proxies based on your needs.
- Geographical Coverage: Providers with various server locations can offer better geo-targeting.
- Reliability: Look for providers with high uptime and stable connections.
- Speed: Consider the speed of proxies, especially for tasks like web scraping or online activities.
- Security: Ensure the provider offers secure connections and data encryption.
- Customer Support: Good customer support can help resolve issues quickly.
- Pricing: Compare pricing plans to find a balance between features and cost.
What are some top proxy service providers? Some well-known proxy service providers include:
- Decodo: Known for its rotating residential proxies and global coverage.
- Oxylabs: Provides data center, residential, and real-time crawler proxies.
- ColdProxy: Known for affordable residential and data center proxies.
- ProxyRack: Offers a mix of data center, residential, and mobile proxies.
- Geosurf: Offers residential and mobile proxies with a focus on geo-targeting.
- Storm Proxies: Offers rotating residential and private dedicated proxies.
- Microleaves: Provides residential and data center proxies for various purposes.
What are the different types of proxies offered by these providers?
Proxy service providers typically offer data center proxies, residential proxies, and, in some cases, mobile proxies. Datacenter proxies come from data centers, while residential proxies come from IP addresses. Mobile proxies use IP addresses from mobile devices.
What is proxy rotation, and why is it important?
Proxy rotation involves cycling through different proxy IP addresses to avoid detection or bans by websites. It’s important for tasks like web scraping or accessing restricted content, as it prevents websites from identifying and blocking your IP address.
Can I use proxies for both privacy and security?
Yes, using proxies can enhance both privacy and security. Proxies mask your IP address, offering a layer of privacy, and can also help protect your personal information from being directly exposed to websites.
READ ALSO: How to Set Up an MCP Server (2026 Guide)
What are some common use cases for proxy services?
- Web Scraping: Extract data from websites without being blocked or triggering CAPTCHAs.
- Ad Verification: Verify the accuracy of online ads and campaigns across different locations.
- SEO Monitoring: Check search engine rankings and local search results.
- Market Research: Gather competitive intelligence from various sources.
- Access Geo-Restricted Content: Bypass region-based restrictions and access content from different countries.
Are there any legal considerations when using proxy services?
Yes, it’s important to use proxy services legally and ethically. Misusing proxies for activities that violate terms of service, engage in hacking, or infringe on privacy laws can lead to serious consequences.
When choosing a proxy service provider, it’s advisable to research thoroughly and consider your specific needs to ensure you’re getting a reliable and suitable service for your requirements.
Conclusion: Empowering Internet Freedom with the Top Proxy Service Providers
In an era where privacy and security are paramount, using a reliable proxy service is crucial. The top proxy service providers offer a range of features, performance, and pricing options to suit various user needs.
Whether you’re looking for rotating residential IPs, data center proxies, or advanced targeting capabilities, these providers have you covered. From the affordable ColdProxy, to the comprehensive IP pool of Decodo to the cost-effective options of IPRoyal, each provider brings something unique to the table.
With the right proxy service, you can unlock internet freedom, protect your privacy, and easily access the content you desire. Choose the provider that aligns with your specific requirements and take control of your online activities today.
INTERESTING POSTS
- The Advantages Of Mobile Proxies
- 14 Best Proxy Service For 2026 [Tested, Reviewed & Ranked]
- The Best Datacenter Proxies
- 4 Differences Between Residential Proxies and Datacenter Proxies
- How to Remove the Wave Browser Virus: A Step-by-Step Guide
- Is Carbonite Safe To Use? [Unbiased ANSWER]
- How To Safeguard Your Business From Cyberattacks
- How to Safely Remove Viruses from Your Computer: A Comprehensive Guide
- StatesCard Review: Is This Card Worth Your Wallet?
- VeePN Review: The Ultimate VPN Solution for Security and Privacy