Wondering what Utopia P2P Ecosystem is all about? We’ve got you covered!
The rapid growth of cybercrime combined with the violation of the rights of Internet users, including the tracking and use of personal data, has exposed the problem of online security.
In 2019, the question of what private tools to use is more relevant than ever. Additionally, the reliability and safety of their use are subject to increased scrutiny.
Therefore, it is necessary to use a system that protects the user’s personal information and authentication data from leakage. What do we offer? To use the Utopia P2P Ecosystem.
Privacy Tools Of The New Generation!
Utopia P2P Ecosystem is a closed encrypted ecosystem, which was developed using the latest technologies of encryption and data protection on the Internet.
READ ALSO: Ways To Prevent Supply Chain Attacks
Data leakage protection
The ecosystem is built on the principle of peer-to-peer architecture. This means that there is no single server where all the information and data about users is stored. Now each user is a peer, that is, both client and server at the same time. So, the risk of data leakage is zero.
Therefore, using the anonymous messenger uMessenger users can exchange encrypted text and voice messages, access to which provides a personal key that is generated during registration. Additionally, you can create private channels or user chats and mark them for easy searching on uMap.
Safe keeping
To store and protect all data, the ecosystem utilizes multi-level encryption based on the high-speed Elliptic Curve 25519, which is responsible for data protection, as well as 256-bit AES, which encrypts and stores data. Thanks to this, all communication occurring through uMail is securely protected. Users can transfer confidential files and documents to each other.
READ ALSO: 4 Common VPN Encryption Protocols Explained
User anonymity
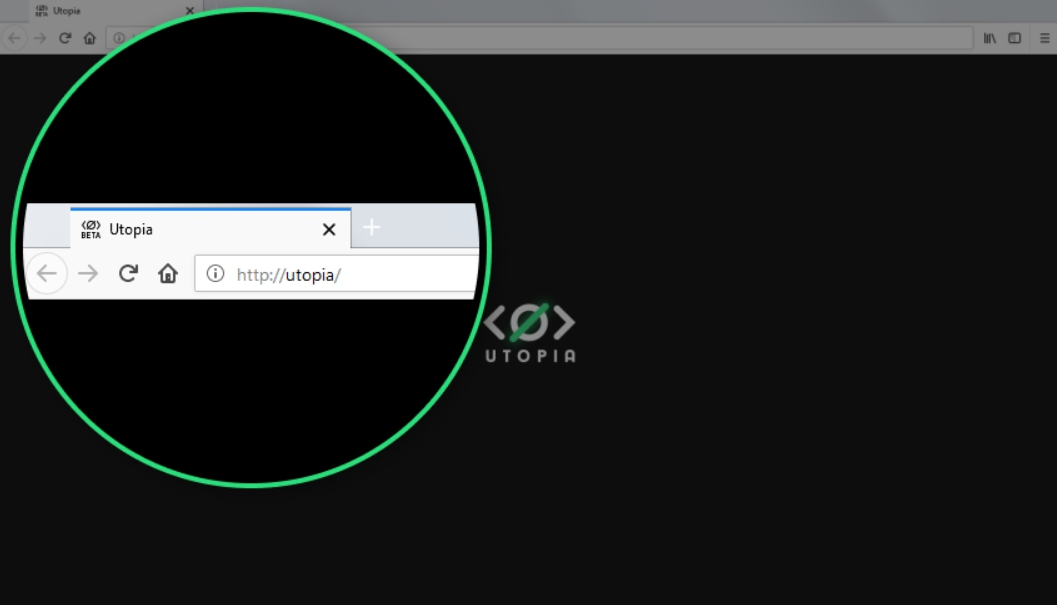
To maintain anonymity on the web, users can use the Idyll browser, which does not track data about the user’s online activity. This is possible since Utopia is a closed ecosystem, where all the necessary sites are located. Therefore, there is no need to leave it. In addition, thanks to the tunnel data feature, each user can add new sites to the ecosystem.
Secure payments
A built-in uWallet that stores cryptocurrency, known as Cryptons, is responsible for the security of financial transaction operations. Using them, you can make or receive payments without entering bank card data. The whole procedure is completely anonymous. Besides, there is the possibility of earning cryptons directly in the ecosystem. To do this, the user can install a Mining bot, which, for every 15-minute session in the ecosystem, will accrue cryptons.
READ ALSO: Mobile Payment Security Concerns – Four Big Things To Consider
Usage convenience
The ecosystem can be used on any electronic device, as it is supported by virtually any software, including iOS, Windows, or Linux. Additionally, for a successful start, the person needs uninterrupted access to Wi-Fi. The ecosystem takes care of everything else. It features a user-friendly interface with a choice of themes, including black and white.
Utopia P2P Ecosystem: Frequently Asked Questions
Is Utopia P2P truly anonymous?
Utopia claims end-to-end encryption for messages, calls, and file transfers, making it difficult for anyone to intercept or eavesdrop. However, achieving true anonymity online is challenging. Factors such as IP address logging and user activity monitoring within the platform may raise questions about complete anonymity. Additionally, relying on user-generated encryption keys introduces potential vulnerabilities if not managed properly.
READ ALSO: Best Crypto Trading Platform
How secure are financial transactions in Utopia?
Utopia uses its own cryptocurrency, Crypton, for financial transactions. However, the platform’s relative newness raises concerns regarding its long-term stability and security compared to established cryptocurrencies. While claims of strong encryption and decentralized storage are made, independent audits and a proven track record in handling large-scale transactions are still lacking.
What are the potential legal implications of using Utopia?
Utopia’s focus on privacy might raise concerns for law enforcement agencies concerned about illegal activities facilitated on the platform. While Utopia claims adherence to local laws and regulations, users should research their local laws regarding encrypted platforms and cryptocurrency usage to avoid potential legal issues.
It’s important to remember that no online platform can guarantee complete anonymity or absolute security. While Utopia offers advanced privacy features, it is essential to understand its limitations and potential legal implications before using the platform. Consider researching independent reviews, audits, and user experiences before making informed decisions about using the Utopia P2P Ecosystem.
Utopia P2P Ecosystem – Evident Proof!
Invasion of privacy is the goal of many: special services, governments, Microsoft, cybercriminals, and even your neighbor living across the street.
However, there are methods to prevent this. For example, the Utopia P2P Ecosystem utilizes only advanced and reliable methods of protection.
If you want comprehensive protection of your data on the Internet, the choice is obvious!
INTERESTING POSTS
- Telios Review – Decentralized And Secure Email Service Provider
- Is TorGuard VPN Free? Unbiased TorGuard VPN Review
- What Is Defencebyte Antiransomware? An Honest Review
- Is Gmail A Social Media? [Here’s The ANSWER]
- 5 Best Freelancing Job Websites For Cyber Security
- Do I Need Antivirus App On iPad? [Here’s The ANSWER]
- 15 Best BullGuard Antivirus Alternatives
- Things To Look Out For When Making Payments Online
- The Best Cyber Security Technology Trends You Must Know