Looking for the best site to buy Genshin Impact account? Learn how to buy safely, avoid scams, and choose the right Genshin Impact starter account with confidence.
At some point, almost every Genshin Impact player hits the same wall. Progress slows down, Primogems run dry, and the characters you actually want stay locked behind bad luck. That’s usually when the thought first appears — maybe it’s easier to just buy Genshin Impact account and skip the grind altogether.
It’s not a rare idea. In fact, the search for the best site to buy Genshin Impact account has become pretty common, especially among players who either missed key banners or don’t want to spend months catching up. A ready-made account can offer what feels like a clean shortcut: strong characters, progress already done, and access to content that would otherwise take weeks or even months.
But there’s a flip side to that convenience. Buying an account isn’t like purchasing a skin or a battle pass. You’re stepping into a grey market where trust matters more than anything else. Some deals are legitimate, others… not so much.
This guide isn’t here to scare you off or push you in. The goal is simple — help you understand how this whole thing works, what to watch out for, and how to make smarter decisions if you decide to go down this route.
Why Players Look to Buy Genshin Impact Accounts
Genshin Impact is designed to reward patience. The longer you play, the more you unlock. But let’s be honest — not everyone has the time or energy to log in daily, farm materials, and save for banners that may or may not pay off.
That’s one of the main reasons people start considering a Genshin Impact starter account buy. Instead of starting from zero, you jump straight into an account that already has a solid foundation. Maybe it includes a couple of limited 5-star characters, maybe it’s just a well-leveled profile — either way, it saves time.
There are a few common situations where buying an account starts to make sense for players:
- They missed a limited banner and don’t want to wait for a rerun
- They’re switching servers and don’t want to restart from scratch
- They tried rerolling and gave up after too many failed attempts
- They simply want to experience late-game content without the early grind
What’s interesting is that many buyers aren’t new players at all. Quite often, they already know the game — they just don’t want to repeat the slow part again.
Still, it’s not purely about convenience. For some, it’s also about control. Gacha systems are unpredictable by design. Buying an account, on the other hand, gives you something fixed — you see exactly what you’re getting.
Is It Legal and Safe to Buy a Genshin Impact Account?
Here’s where things get a bit more complicated.
Officially, HoYoverse does not allow account trading. It’s clearly stated in their terms of service, which means any transaction happens outside the game’s rules. That alone doesn’t mean you’ll instantly get banned — but it does mean you’re not protected if something goes wrong.
And things do go wrong sometimes.
The most common issue isn’t even bans — it’s account recovery. The original owner might still have access to old credentials or recovery data. In some cases, buyers lose accounts days or even weeks after the purchase.
Then there’s the platform itself. Not every buy Genshin Impact account site is built with security in mind. Some act more like open marketplaces where anyone can list anything, which increases the chances of running into dishonest sellers.
There’s also a broader context worth mentioning. The reason these markets exist at all is partly tied to how modern games handle monetization. Randomized rewards can be frustrating, especially when real money is involved. Regulators have pointed this out before.
“players spent ‘hundreds of dollars on prizes they stood little chance of winning’” — Samuel Levine, Director of the FTC Bureau of Consumer Protection (source: Wikipedia, Genshin Impact page)
That kind of system naturally pushes some players to look for alternatives — including buying accounts that already have what they want.
So, is it safe? It can be, but only if you understand the risks and take them seriously. There’s no safety net here, so every decision matters more.
Pros and Cons of Buying Genshin Accounts
Buying an account can feel like a smart shortcut — until it isn’t. The only way to approach it realistically is to weigh both sides without ignoring the uncomfortable parts.
What makes it appealing:
- You get instant access to characters that are otherwise locked behind luck
- No need to replay early quests or grind basic materials
- You can jump straight into higher-level domains and events
- Sometimes it’s cheaper than spending on multiple banners
What should make you pause:
- The account can be taken back if the seller is not trustworthy
- There’s always a chance of restrictions or bans
- You won’t get any official help if something breaks
- Not every listing is as good as it looks
One detail people often overlook is emotional attachment. When you build an account yourself, every character and item has a story behind it. Bought accounts don’t have that same connection — and for some players, that matters more than they expect.
What Makes the Best Site to Buy Genshin Impact Account
If you decide to go ahead with a purchase, the platform you choose matters just as much as the account itself.
The best site to buy Genshin Impact account isn’t necessarily the one with the lowest prices. In fact, extremely cheap offers are usually the first red flag. A good platform focuses on reducing risk, not just making quick sales.
One of the first things to look for is how payments are handled. Marketplaces that use escrow systems give you a layer of protection — your money isn’t released until you confirm that everything is as promised.
Seller transparency is another big factor. Reliable platforms show seller ratings, past transactions, and sometimes even verification badges. That kind of information makes it easier to separate experienced sellers from random listings.
It’s also worth checking how disputes are handled. Even in unofficial markets, some sites offer basic refund policies or mediation if something goes wrong. It’s not perfect, but it’s better than having no options at all.
And finally, think about what happens after the purchase. A good platform will guide you through securing the account — changing login details, unlinking previous connections, and making sure the original owner can’t easily take it back.
In the end, choosing where to buy is less about finding the perfect deal and more about avoiding the worst-case scenario.
Top Features to Look for in a Genshin Impact Account
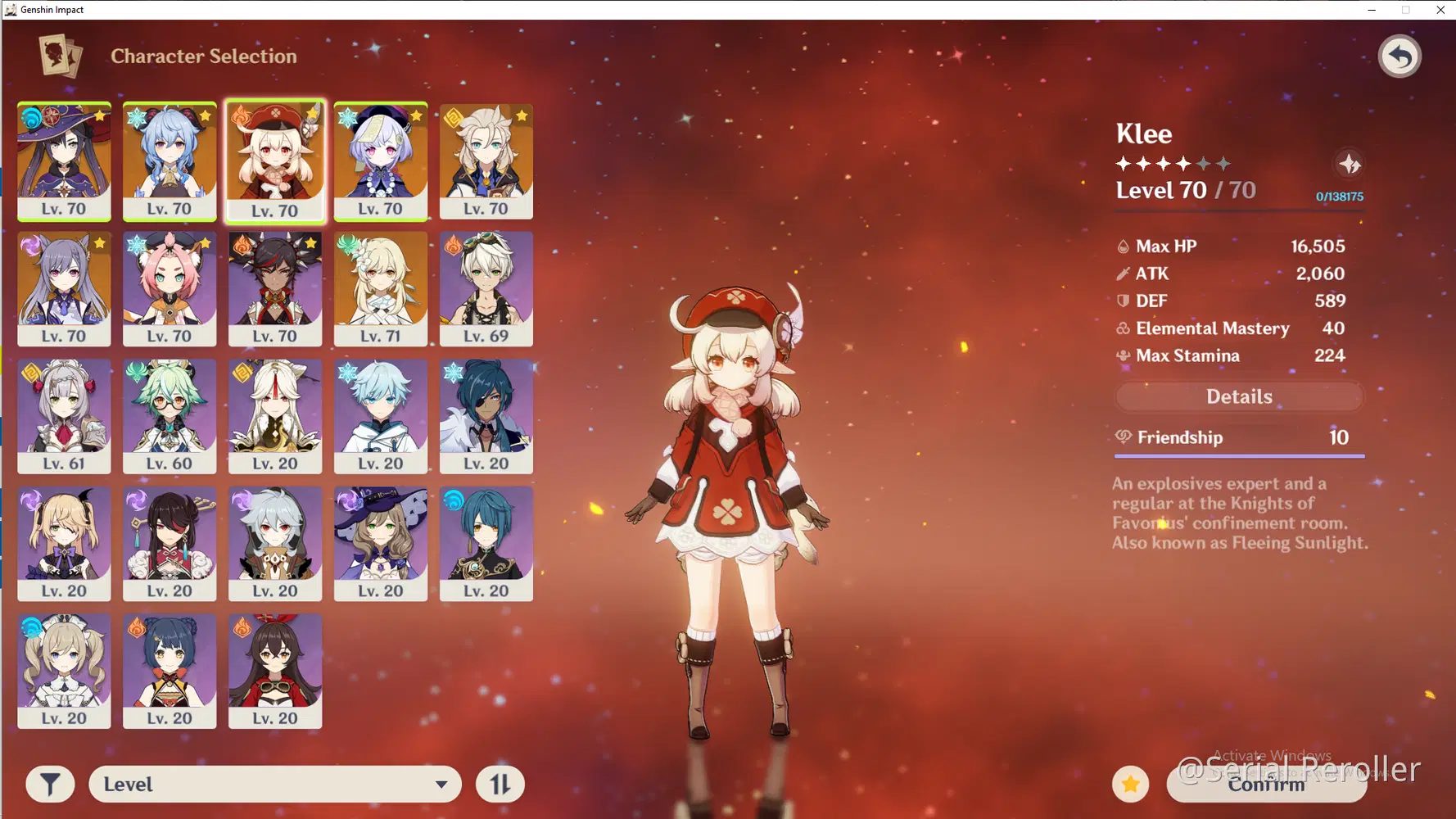
When you start browsing accounts, they can all blur together pretty quickly. Same characters, similar screenshots, almost identical descriptions. But once you slow down and actually compare them, differences show up — and some of them matter more than others.
If you’re considering a Genshin Impact starter account buy, it helps to look past the surface and focus on what you’ll actually use after logging in.
A few things are worth checking every time:
- Adventure Rank — high rank sounds great, but it can also mean most of the easy rewards are already gone. Mid-level accounts often feel more flexible.
- Main characters — not just how many 5-stars are there, but which ones. A couple of strong, well-built units can carry you further than a long, random list.
- Weapons — people underestimate this part. A good weapon can change how a character performs completely.
- Server — sounds obvious, but it’s easy to overlook. Playing on the wrong region can mean higher ping and a worse experience overall.
- Account access — this one is critical. You want full control, with the ability to change email and passwords without any complications.
- Leftover resources — some accounts come with a decent amount of Primogems or materials, which gives you room to keep progressing.
One small but important detail: don’t get distracted by quantity. More characters doesn’t automatically mean better. Sometimes a cleaner, more focused account is actually easier to enjoy.
Choosing the Right Platform
At first glance, most marketplaces look the same. Same promises, same type of listings, same general idea. But once you spend a bit of time comparing them, you start noticing patterns.
Here’s a simple way to look at how different platforms usually differ:
| Feature | Platform A | Platform B | Platform C |
| Buyer Protection | Yes, with escrow | Minimal | Yes |
| Seller Verification | Present | Rare | Present |
| Refund Options | Available in some cases | None | Limited |
| Prices | Average | Lower | Higher |
| Overall Risk | Medium | Higher | Lower |
There’s no perfect choice here. Cheaper platforms can look tempting, but they often come with more uncertainty. More secure ones tend to cost a bit more, but you’re paying for fewer unexpected surprises later.
How to Safely Buy a Genshin Impact Account
This is the part where rushing usually leads to regret.
Using a buy Genshin Impact account site isn’t complicated, but it does require a bit of patience. Most problems happen when people skip basic checks or trust listings too quickly.
A few simple habits can save you a lot of trouble:
Take a minute to look at the seller, not just the account. If there’s a history, reviews, or ratings — read them. If there’s nothing at all, that’s already something to think about.
Be careful with prices that feel unusually low. In most cases, there’s a reason for that, and it’s not a good one.
If the platform offers some kind of payment protection, use it. It gives you time to log in, check the account, and make sure everything matches the description.
And once you get access — don’t wait. Change everything you can: email, password, linked services. The faster you lock it down, the better.
Conclusion: Is It Worth Buying a Genshin Account in 2026?
It really depends on what you want from the game.
If your goal is to skip the early grind and jump straight into stronger content, buying an account can feel like a practical shortcut. For some players, that’s enough reason.
But it’s not a perfect solution. There’s always a bit of uncertainty involved, no matter how careful you are. And for some people, that alone makes it not worth it.
If you do decide to go this way, it’s better to focus on reliability rather than chasing the lowest price. Choosing the best site to buy Genshin Impact account won’t remove all risks, but it can reduce them to a level most players are comfortable with.
At the end of the day, it’s less about whether it’s right or wrong — and more about whether it fits the way you want to play.
FAQ
- Is it safe to use a buy Genshin Impact account site?
It can be relatively safe if you stick to platforms with buyer protection and experienced sellers. Still, there’s no full guarantee. Since these transactions are unofficial, you’re always relying on the platform’s internal rules rather than game support. - Can you get banned after buying an account?
There is always a chance. The game’s rules don’t allow account transfers, so unusual activity can sometimes trigger restrictions. It doesn’t happen in every case, but it’s a risk you shouldn’t ignore. - What is the best Genshin Impact starter account buy option?
Usually, it’s something balanced — not an overpacked account, but also not empty, but also not empty. A couple of strong characters, decent progress, and room to grow tends to be the most practical setup. - How do I avoid scams when buying an account?
Look at the seller’s reputation, avoid deals outside trusted platforms, and don’t rush. If something looks too cheap compared to similar listings, it’s better to skip it than to take the risk. - Are cheap accounts worth it?
Sometimes, but often they come with hidden issues. Lower price usually means higher risk, whether it’s account recovery or inaccurate details. Saving money upfront can cost more later. - Can the original owner recover the account?
Yes, especially if the account wasn’t fully secured after purchase. That’s why changing all access details immediately is not optional — it’s necessary. - Is buying an account better than starting from scratch?
It depends on your priorities. Buying saves time, but starting fresh gives you full control and a more natural progression. Different players value different things.
INTERESTING POSTS
- Password Explained in Fewer than 140 Characters
- Identity Protection Explained in Fewer than 140 Characters
- Cybersecurity Explained: Protecting Yourself in the Digital Age
- Buy Proxy: The Ultimate Guide To Choosing The Best Proxy Service in 2026
- DEAL: Buy Surfshark VPN And Get Surfshark Antivirus For Free
- 11 Best Password Generators Of 2026