In this post, we will answer the question – is Windows Defender good enough for 2026? Also, we will reveal its effective use cases as well as alternatives.
With the increasing spate of cyber attacks, which have become much more sophisticated than ever before, PC users have been asking; would Windows Defender be enough come 2026? Follow us as we attempt to provide a credible answer to this question.
Windows Defender is the proprietary antivirus program for Windows PCs. And it comes pre-installed on modern PCs, particularly Windows 8/8.1/10/11.
However, the antivirus has been viewed as somewhat “substandard”, compared to other notable AV programs. This, coupled with the increasing sophistication of cybercriminals, has raised questions over the reliability of the software.
Nonetheless, in spite of the widespread assumption, WinDefender remains one of the best out there. And while the program has been below-par in the past, recent upgrades have significantly jacked up its performance.
However, the controversial question is still hanging over it: Is Windows Defender enough for 2026? Read on!
Table of Contents
Is Windows Defender Enough For 2026?
While Windows Defender has undergone significant improvements and gained ground against standard antivirus programs, it remains insufficient for comprehensive cybersecurity in 2026.
This insufficiency stems from the evolving nature of cyber threats and the limitations of single-layered security solutions.
The Changing Landscape of Cyber Threats
- Diversification of attack vectors: Cyberattacks have moved beyond traditional virus injections. Today, a diverse range of threats including malware, adware, spyware, ransomware, and trojans pose significant dangers.
- Evolving sophistication: Malicious programs have become increasingly sophisticated, employing advanced techniques like camouflage and disguise. This makes them difficult to detect, bypassing even robust antivirus defenses.
- Hidden and persistent: Many malware strains remain hidden within the system, mimicking legitimate applications or extensions. This stealthy approach further hinders detection and mitigation efforts.
Limitations of Single-layered Defense
- Rigid detection methods: Traditional antivirus programs rely on known virus signatures for detection, leaving them vulnerable to novel or disguised threats.
- Limited scope of protection: Antivirus programs primarily focus on malware detection and removal, neglecting other critical aspects of cybersecurity like data protection and online privacy.
Moving beyond Windows Defender
While Windows Defender offers basic protection, it falls short in addressing the multifaceted nature of modern cyber threats. A layered approach to cybersecurity is crucial for comprehensive protection. This may involve:
- Multi-layered antivirus solutions: Combining multiple antivirus engines with different detection mechanisms can offer broader coverage against diverse threats.
- Advanced threat detection tools: Employing sandboxing, behavioral analysis, and machine learning enhances the ability to identify and neutralize novel or disguised malware.
- Data security solutions: Encryption, data backup, and intrusion detection systems provide additional layers of protection for sensitive information.
- Privacy-focused tools: VPNs, ad-blockers, and anti-tracking software can help safeguard privacy and control online data exposure.
Best Third-Party Antivirus to Pair With Windows Defender
The obvious downside of Windows Defender, which is basically in the area of malware detection, is obtainable in other standard AV packages. Forget the hype; no antivirus program offers absolute protection against malware, which is the key element of cyber attacks today.
Therefore, to reinforce your system and internet security setup, you need a stand-alone “anti-malware” package – to augment Windows Defender.
While Windows Defender has improved significantly in recent years, its limitations against evolving threats require additional security measures. Pairing it with a third-party solution can offer a more comprehensive defense against malware, ransomware, and other cyber threats.
Additionally, here are some recommended antivirus programs you can use to replace Windows Defender:
Summarily, Windows Defender is enough to serve your “virus protection” needs; however, you should consider getting a third-party antivirus program or antimalware as a backup. Nonetheless, it’s recommended to get a standard anti-malware tool, like Malwarebytes, as a support program.
READ ALSO: 12 Best Free Antivirus Software for your Windows PC [Not Free Trial]
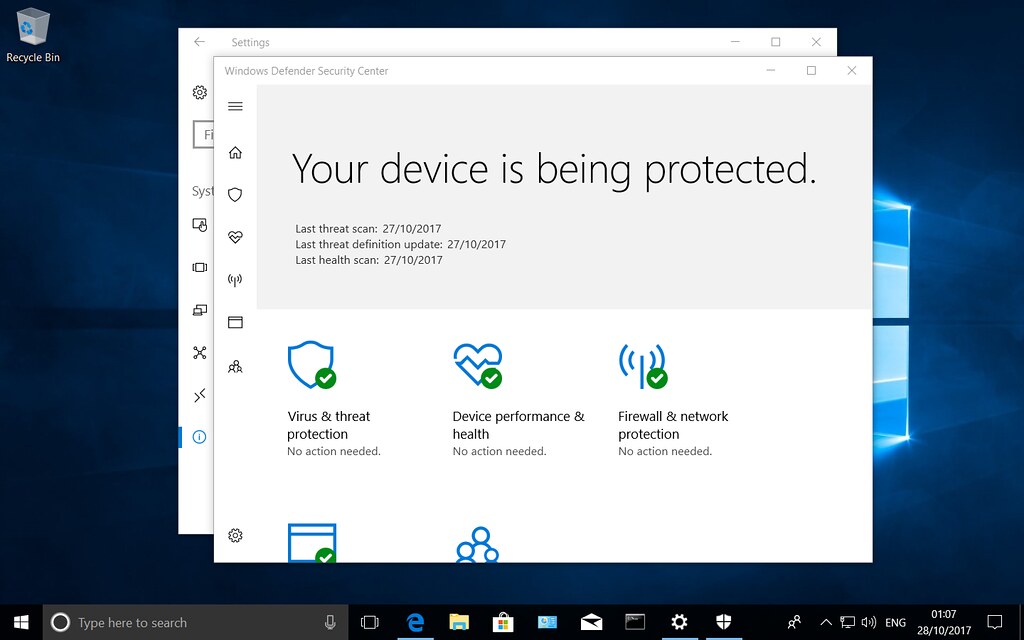
Microsoft Defender: Your Built-In Antivirus Powerhouse
Windows Defender, formerly known as Microsoft Security Essentials, is the free, built-in antivirus solution for Windows 8/8.1 and Windows 10. This means you already have a robust security tool at your disposal, eliminating the need for a separate third-party antivirus program for most users.
So, is Windows Defender enough?
Let’s delve into its capabilities and see how it stacks up:
What Windows Defender Offers:
- Real-time protection against viruses and threats: This includes blocking malware, spyware, and other harmful software before it can harm your PC.
- Network firewall: This monitors incoming and outgoing network traffic, blocking suspicious activity and protecting your computer from online threats.
- App and browser control: You can manage which apps can access your system resources and which websites you can visit, providing an extra layer of security.
- Performance and system health optimization: Helps keep your computer running smoothly and efficiently.
- Free updates and upgrades: Microsoft regularly provides updates and upgrades to Windows Defender, ensuring you always have the latest protection.
How Does Windows Defender Compare?
In the past, Windows Defender often fell short of other antivirus programs. However, recent updates have significantly improved its reliability and effectiveness:
- Independent Labs: Other independent labs have also praised Windows Defender’s performance, often ranking it among the best free antivirus solutions available.
- Enhanced Zero-Day Protection: Windows Defender now boasts an improved 99.7% detection rate for zero-day attacks, according to AV-Test’s October 2023 report. This signifies a significant advancement in combating previously unseen threats.
- AI-Powered Threat Detection: Microsoft leverages advanced machine learning and artificial intelligence to detect and neutralize emerging malware strains. This proactive approach helps stay ahead of even the most sophisticated threats.
- Improved Performance Optimization: Recent updates have further optimized Windows Defender’s resource utilization, ensuring it runs seamlessly without impacting your system’s performance.
- Enhanced Tamper Protection: Windows Defender now features strengthened tamper protection, making it more resistant to malicious attempts to disable or manipulate its functionalities.
- Cloud-Based Threat Intelligence: By leveraging Microsoft’s vast global security intelligence network, Windows Defender receives real-time updates on the latest threats and vulnerabilities, ensuring continuous protection.
Why Choose Windows Defender?
- Free and Pre-Installed: It’s readily available on your Windows system, eliminating the need for additional software purchases and installations.
- Effective Threat Detection: With consistently high detection rates for known and emerging threats, Windows Defender provides reliable protection against a wide range of malware.
- Minimal System Impact: Its optimized design ensures smooth operation without compromising your computer’s performance.
- Automatic Updates and Improvements: Microsoft continuously updates Windows Defender with the latest security definitions and features, ensuring you always have the best protection available.
- Seamless Integration with Windows: As a built-in solution, Windows Defender integrates seamlessly with the Windows operating system, providing a user-friendly and streamlined security experience.
READ ALSO: The Ultimate Antivirus Software Guide: What Is An Antivirus?
Is Windows Defender Enough for Windows 7, 8, 10, and 11?
Windows 7
While Windows Defender still technically runs on Windows 7, it is not recommended as your primary antivirus solution. Microsoft stopped supporting Windows 7 in 2020, which means Windows Defender no longer receives updates or bug fixes. This leaves your system vulnerable to new threats that emerge after support ends.
Instead, consider switching to a third-party antivirus program that still supports Windows 7. Some popular options include Best Antivirus For 2023: Windows, Mac, Linux, iOS & Android.
Windows 8
Windows Defender offers basic protection for Windows 8, but it may not be sufficient for everyone. It performs well in detecting and removing viruses, but it lacks some features found in more advanced antivirus programs, such as:
- Real-time protection against ransomware and phishing attacks.
- Parental controls.
- Firewall protection.
- Password management.
If you need these additional features, consider using a third-party antivirus program.
Windows 10
Windows Defender has significantly improved in recent years and now provides excellent protection for Windows 10. It offers real-time protection against viruses, ransomware, phishing attacks, and other threats. It also includes features like parental controls and firewall protection.
For most users, Windows Defender is sufficient to protect their Windows 10 computer. However, if you need advanced features or want peace of mind, you can consider using a third-party antivirus program.
Windows 11
Windows Defender continues to evolve and is the recommended antivirus solution for Windows 11. It offers comprehensive protection against all types of threats, including zero-day attacks, malware, ransomware, and phishing attacks. It also integrates seamlessly with Windows 11 and has minimal impact on system performance.
For most users, there is no need to look beyond Windows Defender for their antivirus needs on Windows 11.
READ ALSO: Best Parental Control Software for 2026
Is Windows Defender Enough for Virus Protection?
Yes, Windows Defender is enough for virus protection for most users. While it may not offer all the bells and whistles of some paid antivirus programs, it provides excellent protection against the most common threats, including:
- Viruses
- Malware
- Ransomware
- Spyware
- Phishing attacks
Here are some reasons why Windows Defender is a good choice for virus protection:
1. Free and Pre-installed: Windows Defender comes pre-installed on all Windows 10 and 11 machines, so there is no need to purchase or install any additional software. This makes it a convenient and cost-effective option for most users.
2. Excellent Detection Rates: Windows Defender has received consistently high marks from independent testing labs for its ability to detect and block malware. In recent tests, it has been found to detect over 99% of all known malware threats.
3. Real-time Protection: Windows Defender provides real-time protection against malware, meaning it is constantly scanning your system for threats and taking action to block them before they can cause any damage.
4. Regular Updates: Microsoft regularly releases updates for Windows Defender that include the latest virus definitions and security features. This ensures that you are always protected against the latest threats.
5. Low System Impact: Windows Defender is designed to be lightweight and efficient, so it will not slow down your computer.
6. Built-in Features: Windows Defender includes a number of useful features, such as:
- Firewall: Protects your computer from unauthorized access by hackers.
- Parental Controls: Allows you to monitor and restrict your children’s online activity.
- Tamper Protection: Helps to prevent malware from disabling or modifying Windows Defender.
However, there are a few limitations to Windows Defender:
- Lacks some advanced features: Some paid antivirus programs offer additional features, such as password management, file encryption, and VPN protection.
- May not be sufficient for high-risk users: If you use your computer for sensitive activities, such as online banking, you may want to consider using a more robust antivirus program.
READ ALSO: 7 Strange Tips For Selecting An Antivirus Program
Is Windows Defender Enough for Malware Removal?
Windows Defender has come a long way in its ability to remove malware. While it might not have been the most effective solution in its early days, Microsoft has significantly improved its capabilities, making it a capable defense against various threats, including:
- Viruses
- Malware
- Ransomware
- Spyware
- Rootkits
- Phishing attacks
Here’s a breakdown of Windows Defender’s effectiveness in malware removal:
Pros:
- Improved Detection Rates: Independent testing labs consistently give Windows Defender high marks for detecting and blocking malware. Recent tests show a detection rate exceeding 99% for known malware threats.
- Real-time Protection: Windows Defender constantly scans your system for threats and takes action to block them before they can cause harm.
- Offline Scan: The offline scan mode specifically targets rootkits and other malware that hides when connected to the internet.
- Free and Pre-installed: No need to purchase additional software, making it convenient and cost-effective.
- Low System Impact: Designed to be lightweight and efficient, ensuring minimal impact on your computer’s performance.
- Regular Updates: Microsoft regularly releases updates with the latest virus definitions and security features, keeping you protected against evolving threats.
Cons:
- Limited Advanced Features: Some paid antivirus programs offer additional functionalities like password management, file encryption, and VPN protection.
- Might Not Be Sufficient for High-Risk Users: Users involved in sensitive activities, like online banking, might benefit from a more robust antivirus solution.
READ ALSO: 10 Best Antivirus for a Basic Laptop [Must Read]
Is Windows Defender Enough for Small Business?
Windows Defender offers a strong foundation for small business security, but it might not be enough on its own.
While it boasts excellent features like:
- Virus and Malware Detection: Provides reliable protection against common threats.
- Microsoft Defender Security Center Integration: Enables centralized monitoring of multiple computers, vulnerability assessments, and security recommendations.
- Detailed Security Reports: Offers comprehensive insights into your system’s security status.
- File Encryption with Labels: Enhances data security for sensitive information.
However, some limitations make it less than ideal for all small businesses:
- Limited Advanced Features: Lacks functionalities like password management, advanced threat prevention, and endpoint protection, which are crucial for data security and compliance.
- Management Challenges: Manually managing security across multiple computers can be cumbersome for growing businesses.
- Limited Protection for Mobile Devices: This does not offer mobile security solutions, leaving mobile devices vulnerable.
Therefore, whether Windows Defender is enough for your small business depends on:
- Size and Complexity: Small businesses with few computers and basic security needs might find it sufficient.
- Industry and Data Sensitivity: Businesses dealing with sensitive data or operating in regulated industries might require additional security features.
- Budget: Paid antivirus solutions offer more comprehensive protection but require investment.
Here’s a balanced approach for small businesses:
- Leverage Windows Defender: Utilize its built-in features for basic protection.
- Invest in a Business-Grade Antivirus: Consider a paid solution with advanced features like centralized management, mobile security, and endpoint protection.
- Implement Security Best Practices: Implement strong passwords, regular backups, and employee training to minimize vulnerabilities.
- Review Security Needs Regularly: As your business grows and data becomes more sensitive, re-evaluate your security needs and adjust your approach accordingly.
Remember, a layered security approach is crucial for small businesses. Combining Windows Defender with additional solutions and best practices can ensure robust protection for your valuable data and assets.
It is recommended that you invest money in one of the best antiviruses for small businesses.
READ ALSO: Free VPN vs Premium VPN – Which one should I go for?
What Are the Limitations of Windows Defender?
While Windows Defender has significantly improved over the years, it still has limitations that some users might find inconvenient or deal-breaking.
Here are some of its key limitations:
1. User Interface Complexity
- The dashboard can be overwhelming for beginners, with a complex layout and unclear navigation.
- Microsoft’s attempt at a professional aesthetic might have sacrificed user-friendliness.
2. Activation and Deactivation
- The process for enabling and disabling Windows Defender can be confusing and unintuitive.
3. Detection Consistency
- While it effectively detects most threats, Windows Defender’s ability to identify some emerging threats might not be as consistent.
4. Browser Protection
- Limited functionality with popular browsers like Firefox and Chrome, leaving users vulnerable to online threats and phishing attacks.
- Although add-ons and extensions exist for these browsers, their effectiveness is questionable.
5. Parental Control Limitations
- Parental control features work only with Microsoft browsers, hindering their effectiveness in monitoring children’s online activities across all platforms.
6. Performance Impact
- Users have reported performance slowdowns during system scans, particularly on older or less powerful PCs.
- While faster on high-end systems, the scan speed still lags behind some competitors.
7. Lack of Additional Features
- Unlike many antivirus programs, Windows Defender lacks features like password management, a VPN, and advanced threat prevention.
8. Limited Customization
- Users have limited control over how Windows Defender operates, making it difficult to tailor its behavior to their specific needs.
It’s important to note that these limitations may not be significant for all users. However, for those who prioritize user-friendliness, comprehensive protection, and advanced features, a paid antivirus solution might be a better choice.
Ultimately, the decision of whether Windows Defender is enough for you depends on your specific circumstances and priorities. Weigh the limitations against its benefits and consider exploring other options if necessary.
Do I Need Antivirus Software If I Have Windows Defender?
While Windows Defender offers good protection against most threats, you may still consider installing another antivirus program depending on your specific needs and priorities.
Here’s a breakdown of the factors to consider:
Reasons to stick with Windows Defender:
- Free and Pre-installed: No need for additional purchase or installation.
- Effective Protection: Provides robust protection against common viruses, malware, ransomware, and phishing attacks.
- Real-time Protection: Continuously scans your system for threats.
- Minimal System Impact: Designed to be lightweight and not affect your computer’s performance.
- Regular Updates: Microsoft constantly updates Windows Defender with the latest virus definitions and security features.
Reasons to consider another antivirus program:
- Limited Advanced Features: Lacks features like password management, VPN, and advanced threat prevention.
- User Interface Complexity: The dashboard might be confusing for beginners.
- Performance Impact: Scans can slow down older or less powerful PCs.
- Limited Browser Protection: Less effective with popular browsers like Firefox and Chrome.
- Parental Control Limitations: Only works with Microsoft browsers.
- Inconsistent Detection: Might miss out on some emerging threats.
- No Customization: Limited control over how Windows Defender operates.
If you prioritize user-friendliness, comprehensive protection, advanced features, or specific functionality not available in Windows Defender, then investing in another antivirus program might be beneficial.
Remember:
- Installing another antivirus program automatically disables Windows Defender.
- Paid antivirus programs often offer more features and customization options.
- Consider your individual needs and threat profile before making a decision.
- Combining Windows Defender with other security best practices can significantly enhance your protection.
Ultimately, the choice of whether to use another antivirus program alongside Windows Defender is a personal one. Weigh the pros and cons carefully and choose the solution that best suits your security needs and preferences.
Are Windows Defenders and Windows Firewalls Enough for My PC?
 To answer the question, you should note that both Windows Defender and Windows Firewall offer value.
To answer the question, you should note that both Windows Defender and Windows Firewall offer value.
While both Windows Defender and Windows Firewall offer valuable security features, whether they are sufficient for your specific needs depends on your individual circumstances and priorities.
Here’s a breakdown of their strengths and limitations:
Windows Defender
Strengths
- Free and pre-installed.
- Effective protection against common threats.
- Real-time protection.
- Minimal system impact.
- Regular updates.
Limitations
- Limited advanced features.
- Complex user interface.
- Performance impact on older PCs.
- Limited browser protection.
- Parental control limitations.
- Inconsistent detection of some threats.
- No customization options.
Windows Firewall
Strengths
- Free and pre-installed.
- Effective at filtering data and blocking harmful programs.
- Blocks unauthorized connections.
- Allows creation of advanced rules.
- Comparable functionality to most third-party firewalls.
Limitations
- Unfriendly user interface.
For most users, Windows Defender and Windows Firewall can offer a good level of protection against common threats. However, if you need:
- Advanced features: Password management, VPN, advanced threat prevention.
- Improved user experience: Simpler interface and easier navigation.
- Comprehensive protection: Enhanced browser protection, parental controls, consistent threat detection.
- Customization options: Control over how security programs operate.
Then considering additional software solutions might be beneficial.
Here are some additional points to consider:
- Combining Windows Defender and Windows Firewall with other security practices like strong passwords and regular backups can significantly improve your overall protection.
- The effectiveness of these programs depends on your individual threat profile and online activities.
- Paid security solutions often offer more features and customization options.
Ultimately, the decision of whether Windows Defender and Windows Firewall are enough for you depends on your specific needs and security priorities. Weigh the pros and cons carefully and choose the solution that best suits your situation.
READ ALSO: Top 5 Antivirus Platforms For Your Computer
Conclusion
Windows Defender represents a good starting point for basic antivirus protection. However, its limitations and the evolving threat landscape demand a more comprehensive approach to cybersecurity in 2026.
Utilizing a layered security strategy that combines antivirus with additional tools and best practices can provide robust protection against the ever-evolving threats of the digital world.
Note: This post has been updated for freshness.
RELATED ARTICLES:
- 7 of the Best Windows 7 Antivirus After Support Ends
- How to Lock and Unlock your Windows PC with a Pendrive
- Full Review of Heimdal Security – Versatile Security Suite
- Full ESET Smart Security Premium Review
- Full Review of Airo Antivirus software for Mac – Powerful & Intelligent Antivirus




















![When Is Hacking Illegal And Legal? [Honest Answer] when is hacking illegal and legal](https://secureblitz.com/wp-content/uploads/2020/07/when-is-hacking-illegal-and-legal.jpg)

