In this post, I will talk about how AI development helps startups move from idea to launch faster.
Startups face a common challenge: they need to turn ideas into products quickly before resources run out or competitors get ahead. Traditional development methods often take six months or longer to launch a basic product. This timeline can drain budgets and miss market opportunities. However, artificial intelligence has changed how fast startups can move from concept to launch.
AI tools now help startups build functional products in just two to six weeks instead of months. These tools automate tasks that used to require significant time and manual effort. Teams can use AI for market research, code generation, product design, and testing. As a result, startups validate their ideas faster and spend less money on early development.
The impact goes beyond speed. Startups that use AI in their development process make better decisions based on data rather than guesswork. They can test multiple approaches quickly and find what works for their target market. This approach helps new companies compete with established players and attract investors sooner.
How AI Streamlines Startup Development
AI tools cut the time from concept to launch by automating research, speeding up code generation, and simplifying product testing. Startups can validate ideas faster, build prototypes in weeks instead of months, and iterate based on real data rather than guesswork.
Reducing Product Development Time
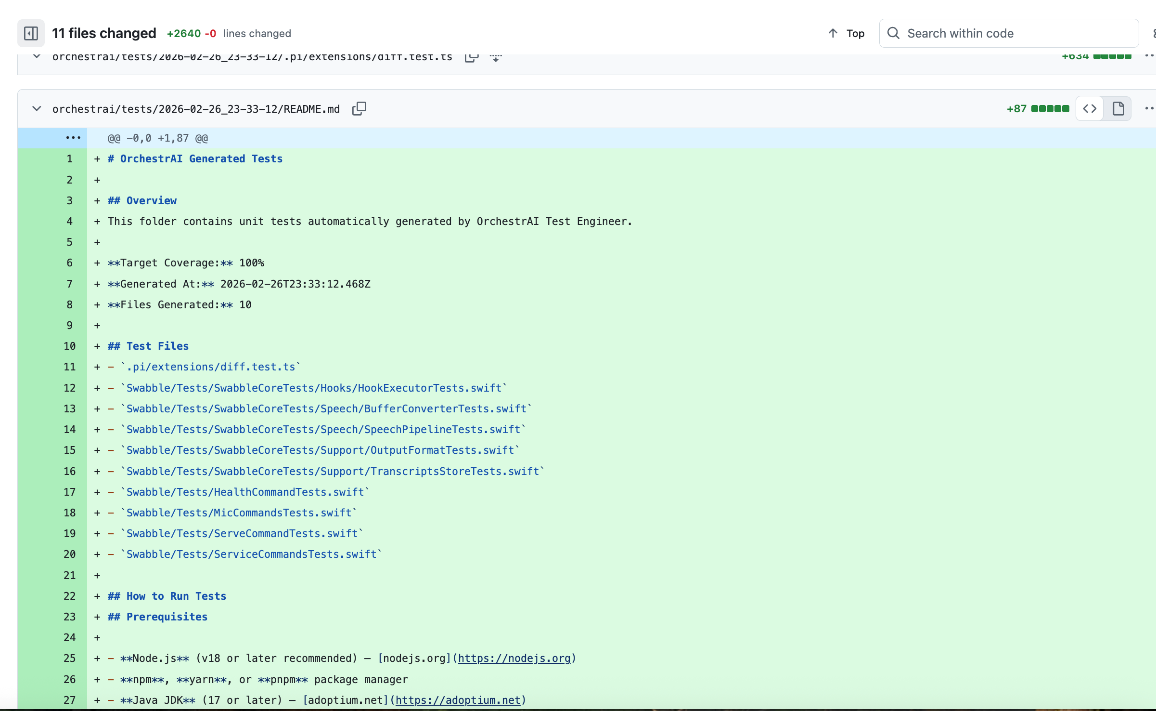
AI code generators write functional software components based on simple descriptions. Developers describe what they need in plain language, and AI produces the corresponding code structure. This automation eliminates hours of repetitive programming work and lets technical teams focus on unique features that differentiate their product.
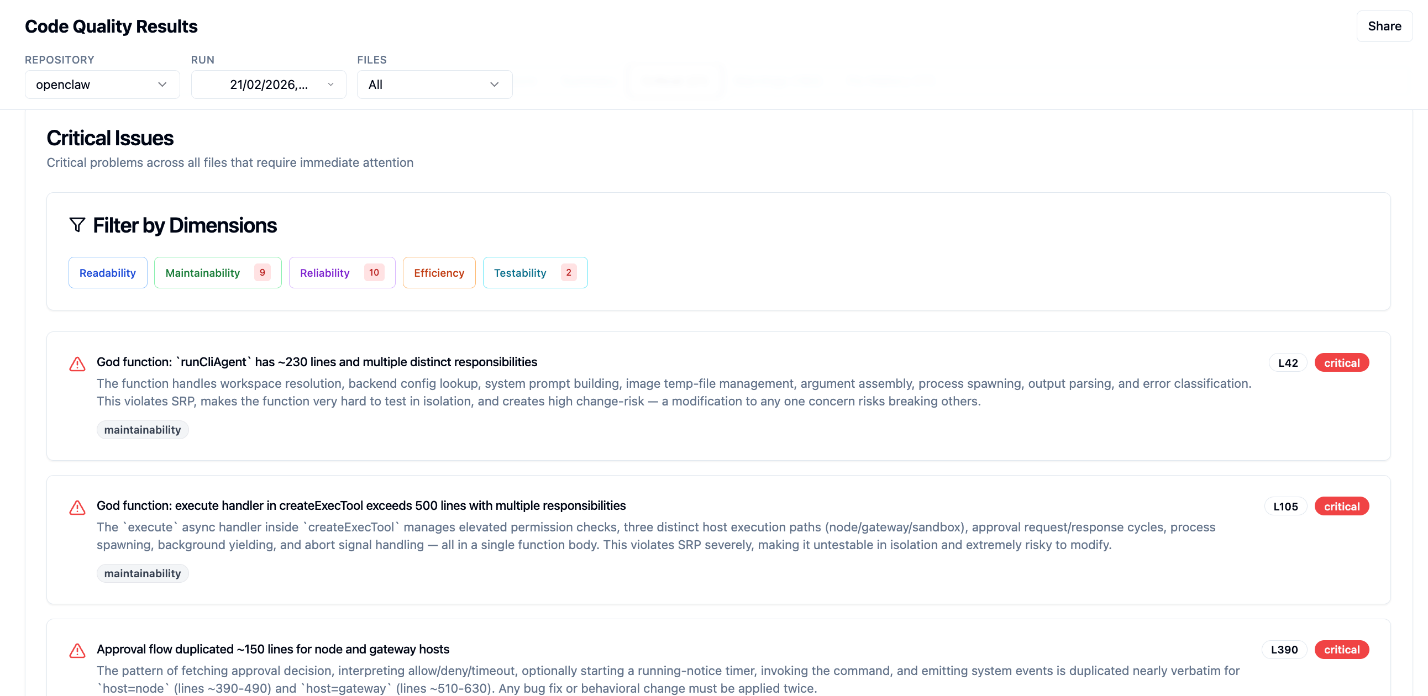
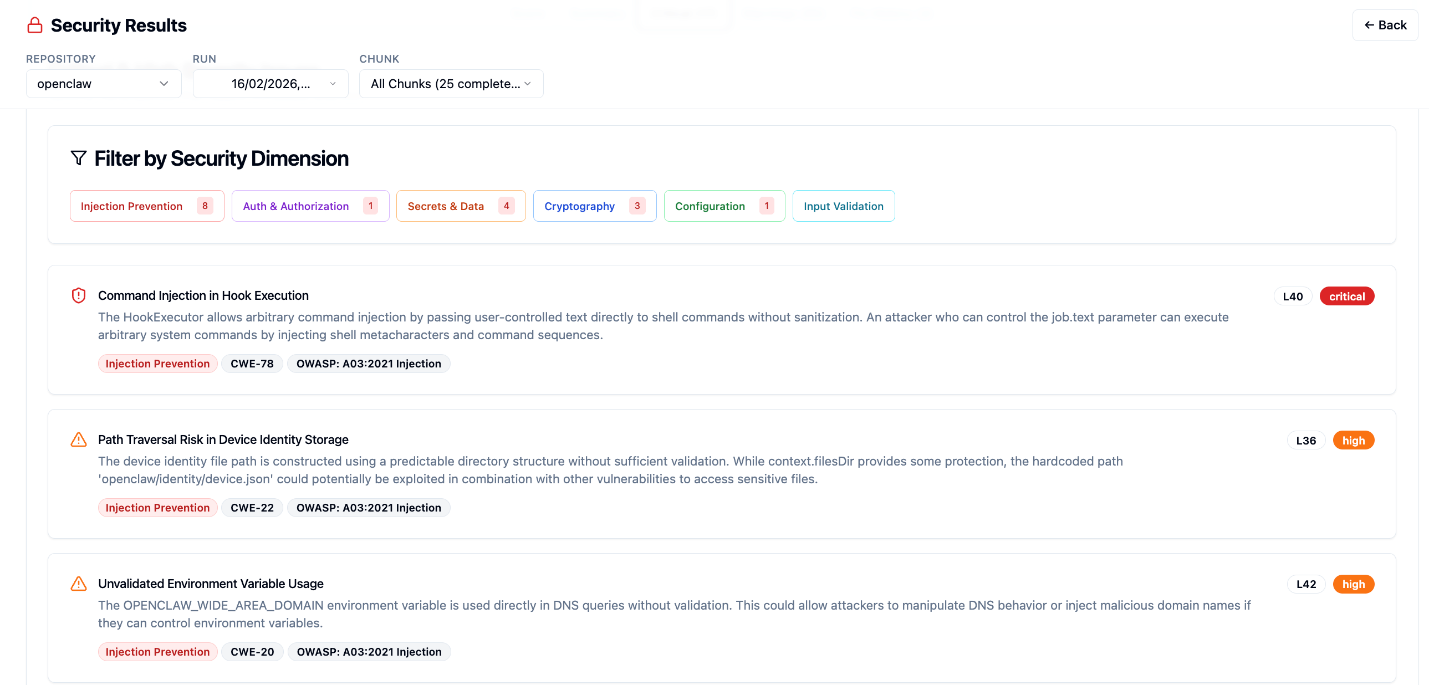
AI tools also identify bugs and security vulnerabilities before they become problems. Automated testing catches errors that human reviewers might miss during manual code reviews. The result is cleaner, more stable software that requires fewer rounds of fixes and patches.
Teams that implement custom RAG application development can build smarter products that access and process company-specific information. This technology connects AI models to proprietary data sources, so applications provide more accurate and relevant responses to user queries. Development cycles shrink because AI handles complex data retrieval tasks that would otherwise require custom backend systems.
Accelerating Ideation and Market Validation
AI analyzes market trends and customer data in minutes rather than weeks. Founders can use AI-powered tools to scan competitor landscapes, identify gaps in the market, and predict demand before they commit resources. This approach replaces traditional market research methods that often require expensive consultants or lengthy surveys.
Machine learning models process customer feedback from social media, reviews, and forums to reveal unmet needs. Startups gain clarity on whether their idea solves a real problem for their target audience. AI can also simulate different business scenarios to test assumptions about pricing, features, and market positioning.
The technology allows teams to run multiple validation tests at once. For example, AI chatbots can conduct hundreds of customer interviews simultaneously to gather feedback on product concepts. This parallel processing helps founders make data-driven decisions about which ideas deserve further development and which ones should be abandoned early.
Enhancing Prototyping and MVP Creation
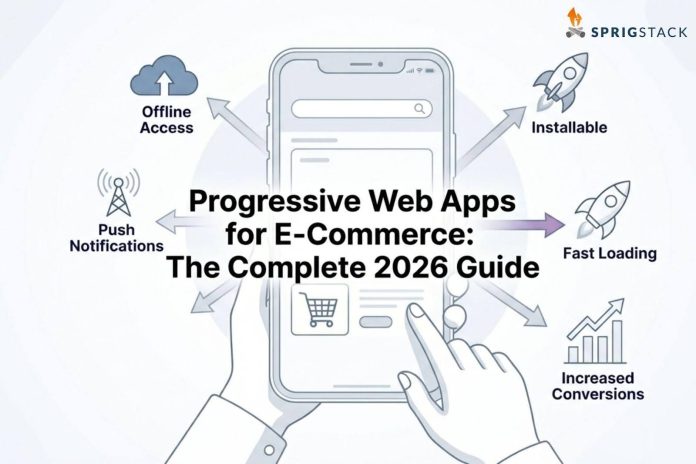
AI design tools generate user interfaces from wireframe sketches or text descriptions. Startups create clickable prototypes in days without hiring full design teams. These tools apply best practices for user experience automatically, so even non-designers produce professional-looking products.
AI-powered no-code platforms let non-technical founders build functional MVPs. Users drag and drop components while AI handles the underlying logic and database connections. This democratization of development means business experts can test their ideas without waiting for technical cofounders or development agencies.
The technology also personalizes user experiences from day one. AI algorithms track how early users interact with prototypes and adjust features accordingly. Startups gather usage data, identify which functions matter most to customers, and refine their MVPs based on actual behavior. This feedback loop happens in real time rather than after formal user testing sessions, so products improve continuously from the first user interaction.
Implementing AI Solutions for Rapid Launch
AI tools can reduce development time by up to 70% and cut costs by 60% for startups. Teams that use AI in their development process reach product-market fit 2.3 times faster than those who rely on traditional methods alone.
Optimizing Workflow Automation
AI automates repetitive tasks that normally consume hours of a founder’s day. Development teams now use AI assistants to write code, test features, and fix bugs without manual intervention. These tools handle tasks like database setup, API connections, and security checks in minutes rather than weeks.
Marketing workflows benefit from AI automation as well. Startups can schedule social media posts, generate email campaigns, and create content calendars through AI-powered platforms. The technology also manages customer service by responding to common questions and routing complex issues to human team members.
Operations become more efficient through intelligent automation. AI systems process invoices, track expenses, and generate financial reports with minimal human oversight. For example, some startups reduce administrative work by 85% through automated document processing and data entry. This allows founders to focus on strategy and growth instead of paperwork.
Facilitating Scalable Infrastructure
AI helps startups build systems that grow with their user base. Cloud platforms with AI capabilities adjust server resources based on real-time demand. This means a startup pays only for what it needs at any given moment instead of over-provisioning from day one.
Development teams can deploy applications faster with AI-assisted infrastructure management. The technology predicts traffic patterns and scales computing power before demand spikes occur. It also identifies potential system failures and fixes them before users notice any problems.
Many startups now launch functional MVPs in 2 to 6 weeks using AI development tools. This timeline represents a significant improvement over the traditional six-month development cycle. The speed advantage lets teams test their ideas with real users much sooner and adjust based on feedback.
Leveraging AI for Customer Insights
AI analyzes user behavior to reveal patterns that humans might miss. Startups can track how customers interact with their products, which features they use most, and where they encounter friction. This data helps teams make informed decisions about product improvements and feature priorities.
Predictive analytics show which customers are likely to churn before they leave. Teams can then take action to retain those users through targeted outreach or product adjustments. The same technology identifies the most valuable customer segments and helps startups allocate resources more effectively.
Sentiment analysis tools process customer feedback from reviews, social media, and support tickets. AI categorizes this feedback by topic and urgency, so teams can address the most important issues first. Some platforms even suggest specific product changes based on aggregate user sentiment and competitive analysis.
Conclusion
AI has changed how startups move from idea to launch. Founders now have access to tools that automate tasks, speed up development, and provide data-backed insights. These technologies help teams build faster and make smarter decisions without the need for large budgets or big teams.
Startups that use AI strategically gain a clear advantage in today’s market. They can test ideas quickly, adapt based on real feedback, and reach customers sooner than competitors who rely on traditional methods.
INTERESTING POSTS