This post will delve into the cyber security practices of major league teams. Read on.
From the outside looking in, professional sports and cyber security don’t seem to have much in common. However, there have been multiple high-profile hacks in major league sports in recent years — particularly in the MLB.
The St. Louis Cardinals were fined for hacking the Houston Astros in 2014… three years before the Astros were charged for hacking covert signs from multiple opponents in 2017.
Oddly enough, the four major leagues in North America, including the NHL, MLB, NFL, and NBA, don’t provide cyber security measures for their teams. Instead, each franchise is responsible for managing its own security networks. Until recently, there wasn’t too much emphasis placed on protecting digital channels from spies.
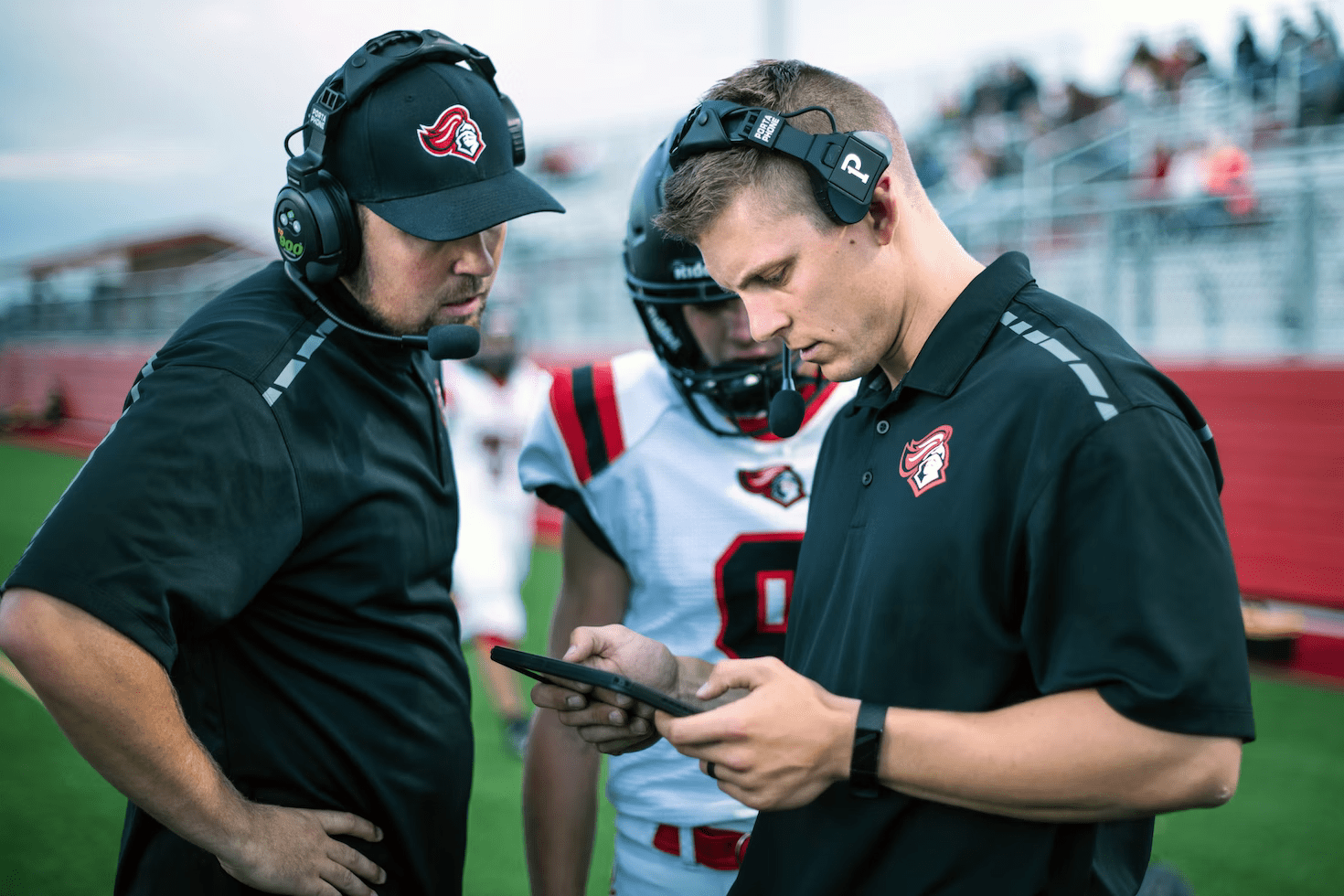
The most prevalent reason for cyber hacking is to glean some clue into a team’s plans, signs, plays, and more. However, there are other concerns, including protecting private data from players and staff, as well as financial information and accounts. Still, the primary focus is on a team’s intercommunication.
After all, many analysts zero in on a team’s plan of action, which is constructed behind closed doors. A team’s greatest asset is its game plan, which is tailored down to each minute detail, including location, opponent, and more. This type of unknown is what makes sports so exciting to follow for fans—a layer of unpredictability.
In fact, this is the basis for multiple sports industries, including betting and fantasy leagues. For example, a Caesar’s sportsbook promo includes a $1,500 bet insurance. The bonus is designed to protect a bettor’s first wager as they learn to use data to predict sporting outcomes. The unpredictability of the game is what drives interest in betting on sports in the first place.
Leaking a team’s plan or approach to a game would spell disaster for the team and the league, along with sportsbooks and fantasy leagues. The priority for cyber security has never been higher—so, what are teams doing to protect themselves digitally?
READ ALSO: Document Collaboration Among Remote Teams: Tools And Strategies For Success
Table of Contents
Securing Communication Channels
Athletes and major league staff weren’t likely trained with cyber security in mind. One of the biggest ways that teams put themselves at risk is by sending large amounts of data—often through casual channels like emails.
And given the widespread usage of wearable technology, from heart rate monitors to movement trackers, there are more channels to protect than ever. Today, some third-party security networks offer encryption, which helps protect the gigabytes of information being sent to and from the front office.
The Double-Pronged Threat: IoT vs. Single Points
One way for a team to protect their information is to avoid spreading their communication channels across a wide range of platforms. The tighter, the better. At the same time, a team should be wary of keeping all its information in one location.
So, where’s the happy balance, especially when the growing availability of IoT offers seamless cross-platform connections?
To avoid a single point of failure in terms of cybersecurity, a team should use multiple channels to store and send information. Many times, these are categorized by finances, planning, data, and on-site channels (such as vendors and ticketing).
Documenting Incidents & Creating Response Plans
Creating a robust cybersecurity approach looks different for each major league team. Most teams now work with cybersecurity groups in order to streamline their approach. Invariably, a cybersecurity group will document instances of single points of failure. This is done both to prevent activities like hacking and to build out a procedure in the event that a critical system goes down.
In other words, a cybersecurity group works with a team to help educate front office managers on creating various incident response plans. An incident response plan creates unique procedures in the event certain systems are hacked, whether data centers, financial logs, or venue management.
The idea is to identify which areas are most at risk of being compromised and then create specific security protocols for each. Proactive planning is one of the hallmarks of cybersecurity planning, from backing up data to consistently testing IT infrastructure for weaknesses.
A Final Word
There you have them! The cyber security practices of major league teams.
INTERESTING POSTS
- Cybersecurity: Addressing A Current Issue By Planning For The Future
- Meet AudiBrow: Secure Podcast Web Browser
- 5 Cybersecurity Tips To Protect Your Digital Assets As A Business
- A Step-by-Step Guide To Website Development
- Key Functions Performed By The Security Operations Center (SOC)
- Merging And Combining: How To Merge PDF Files Into A Single Document
- 2 Tips For Picking A Sports Betting App
- Tips & Tricks To Improve Your Streaming Experience
About the Author:
Marie Beaujolie is a computer network engineer and content writer from Paris. She is passionate about technology and exploring new ways to make people’s lives easier. Marie has been working in the IT industry for many years and has a wealth of knowledge about computer security and best practices. She is a regular contributor for SecureBlitz.com, where she writes about the latest trends and news in the cyber security industry. Marie is committed to helping people stay safe online and encouraging them to take the necessary steps to protect their data.




![Cybersecurity Tips From Squid Game TV Series [MUST READ] Cybersecurity Tips From Squid Game TV Series](https://secureblitz.com/wp-content/uploads/2021/10/Cybersecurity-Tips-From-Squid-Game-TV-Series.png)




