Want the best DediPath alternatives? Look no further!
DediPath, a well-known hosting provider offering dedicated servers, VPSs, and cloud hosting, unexpectedly ceased its operations, leaving countless customers searching for reliable alternatives.
The sudden closure has created a sense of urgency among businesses and individuals who rely on hosting services for their websites, applications, and online projects.
This article will explore some of the best DediPath alternatives to help you navigate this transition seamlessly. We’ll take a closer look at each alternative and highlight why they make for a worthy choice as a DediPath replacement.
Table of Contents
Why Is DediPath Shutting Down?
DediPath, a US-based hosting provider, shut down its operations on August 31, 2023, with less than 24 hours’ notice to its customers. The company cited financial difficulties as the reason for the closure.
In an email to customers, DediPath said it had been “facing some financial challenges” and “exhausted all options to avoid this outcome.” The company apologized for the inconvenience and said it would work with customers to migrate their data and services to other providers.
The sudden closure of DediPath has been met with disappointment and anger from its customers. Some customers have taken to social media to express their frustration, while others have complained to the Better Business Bureau.
The reasons for DediPath’s financial difficulties are partially transparent. However, the company was struggling to compete with larger hosting providers. DediPath was a relatively small company, and keeping up with the rising infrastructure and bandwidth costs may have been challenging.
The closure of DediPath is a reminder of the risks associated with using small hosting providers. When choosing a hosting provider, it is essential to research and ensure the company is financially stable. You should also ensure that the company has a good reputation and offers good customer support.
If you are a DediPath customer, start looking for a new hosting provider as soon as possible. Many reputable hosting providers are available, and you should be able to find one that meets your needs.
Choosing the Best DediPath Alternative
The best DediPath alternative for you will depend on your specific needs and budget. Consider the following factors when choosing a new hosting provider:
- Price: Dedicated servers can be expensive, so finding an affordable pricing provider is essential.
- Performance: Dedicated servers should provide reliable and consistent performance.
- Features: Ensure the provider offers the needed features, such as unmetered bandwidth, root access, and DDoS protection.
- Support: Ensure the provider offers good customer support if you need help with your dedicated server.
- Location: If you need a dedicated server in a specific location, ensure the provider has data centers.
- Uptime: Look for a provider with a good uptime guarantee.
- Scalability: If you need to be able to scale your dedicated server up
READ ALSO: Performance vs Pricing: How US VPS Plans Compare
Best DediPath Alternatives
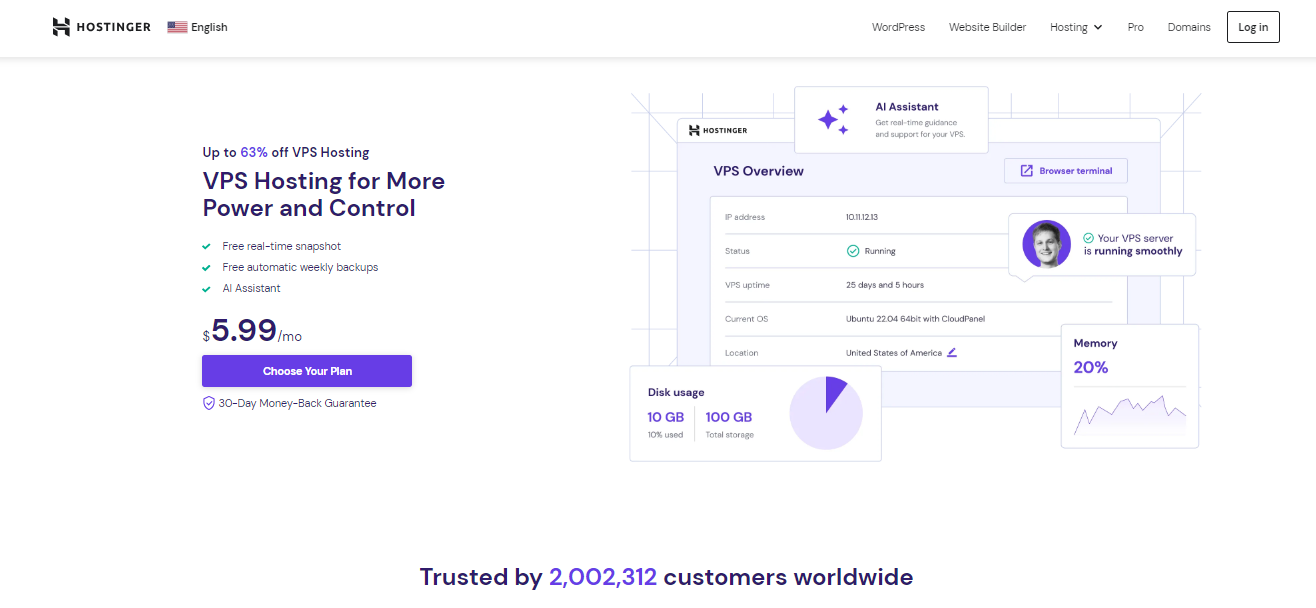
1. Hostinger
Hostinger is a hosting provider with a global presence and a strong reputation for its affordability and performance.
Key Features:
- Affordability: Hostinger offers some of the most budget-friendly hosting plans in the industry, making it an ideal choice for individuals and small businesses.
- User-Friendly Control Panel: Their custom control panel is intuitive, making it easy to manage websites, domains, and hosting settings.
- Data Centers: Hostinger has servers in multiple locations, ensuring fast loading times for your websites.
- 24/7 Customer Support: Their support team is available around the clock to assist with hosting-related issues.
Why Hostinger is the Best DediPath Alternative:
Hostinger’s affordability, user-friendly interface, and global reach make it an excellent choice for those who migrate from DediPath. Whether you need shared, VPS or cloud hosting, Hostinger has you covered.
2. Namecheap
Namecheap, initially known for domain registration, has expanded its offerings to include reliable hosting services.
Key Features:
- Free Website Builder: Namecheap includes a website builder with their hosting plans, making it easy for beginners to create a professional-looking site.
- cPanel: They offer the popular cPanel control panel for easy website management.
- Security: Namecheap strongly emphasizes security, providing various security features and SSL certificates.
- Uptime: Namecheap boasts excellent uptime, ensuring your websites remain accessible to visitors.
Why Namecheap is the Best DediPath Alternative:
Namecheap’s commitment to security and user-friendly features makes it a dependable choice. It’s an excellent option for those who need shared hosting and value domain management in one place.
3. Interserver Hosting
Interserver Hosting specializes in VPS hosting and dedicated servers, making it an attractive choice for businesses and advanced users.
Key Features:
- VPS Hosting: Interserver’s VPS hosting offers competitive pricing and customizable configurations.
- Dedicated Servers: They provide robust, reliable server options with ample resources for high-demand applications.
- 24/7 Support: Their support team is available 24/7 to assist with server-related issues.
- Uptime Guarantee: Interserver offers an uptime guarantee, ensuring your services remain online.
Why Interserver Hosting is the best DediPath Alternative:
Interserver Hosting’s specialization in VPS and dedicated server hosting makes it an excellent option for businesses and advanced users seeking robust, reliable hosting solutions.
4. GoDaddy
Another notable mention among the best DediPath alternatives is GoDaddy.
GoDaddy is a household name in the hosting industry, offering a wide range of hosting services.
Key Features:
- Global Network: GoDaddy has a vast network of data centers worldwide, ensuring fast loading times and reliability.
- cPanel: They provide cPanel for easy website management.
- Support: GoDaddy offers 24/7 customer support to assist with any hosting-related issues.
- Diverse Hosting Solutions: GoDaddy caters to businesses of all sizes, from shared hosting to dedicated servers.
Why GoDaddy is a Good DediPath Alternative:
GoDaddy’s extensive experience in hosting, global infrastructure, and diverse hosting options make it a solid choice for those transitioning from DediPath.
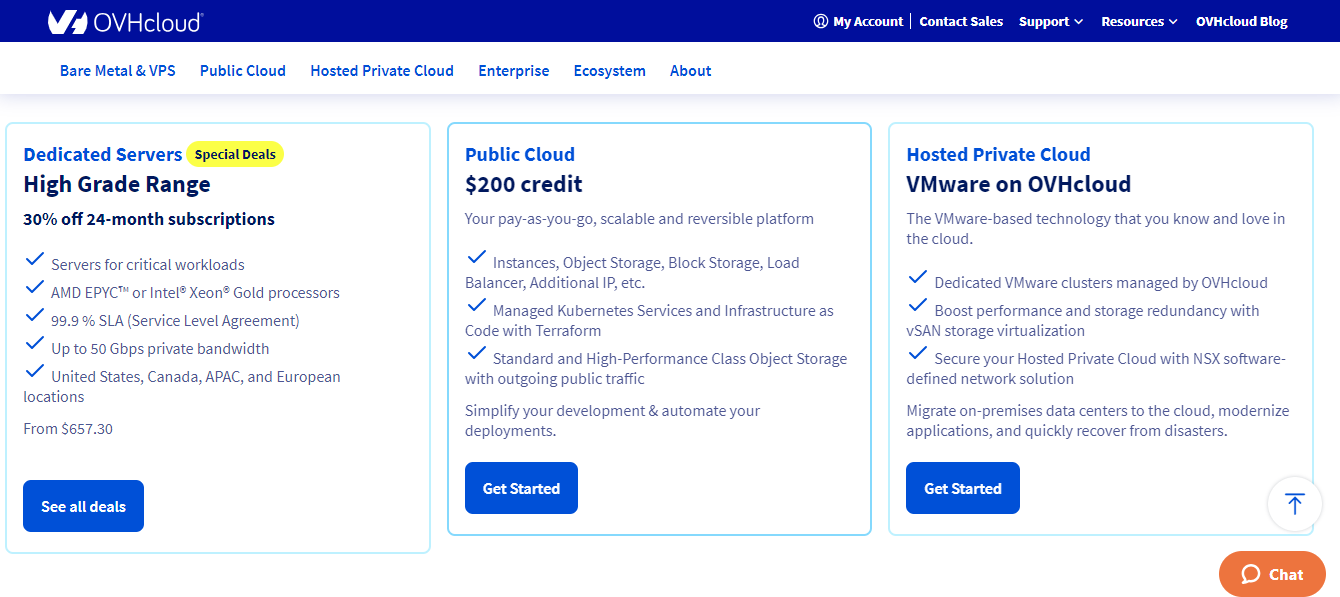
5. OVH Cloud
OVH Cloud is a European hosting provider with a solid global presence, known for its robust infrastructure and security measures.
Key Features:
- Diverse Hosting Solutions: OVH Cloud offers dedicated servers, VPS hosting, and cloud services.
- Robust Infrastructure: They are known for solid network infrastructure and data center security.
- Data Privacy: OVH Cloud takes data privacy seriously, protecting your sensitive information.
- Global Reach: With data centers in various regions, OVH Cloud provides low-latency access for your users.
Why OVH Cloud is a Good DediPath Alternative:
OVH Cloud is a strong contender for your hosting needs if you value robust infrastructure and data security. Their diverse range of hosting options caters to different requirements.
6. eUKhost
eUKhost is a UK-based hosting provider known for its reliable hosting services and commitment to data security.
Key Features:
- Performance: eUKhost focuses on delivering high-performance hosting solutions with fast loading times.
- Diverse Hosting Options: They offer shared hosting, VPS hosting, and dedicated servers.
- Security: eUKhost implements robust security measures to protect your websites and data.
- Customer Support: Their 24/7 customer support ensures assistance whenever you need it.
Why eUKhost is a Good DediPath Alternative:
eUKhost’s emphasis on performance, data security, and reliable support makes it a trustworthy choice for businesses and individuals looking for a DediPath alternative.
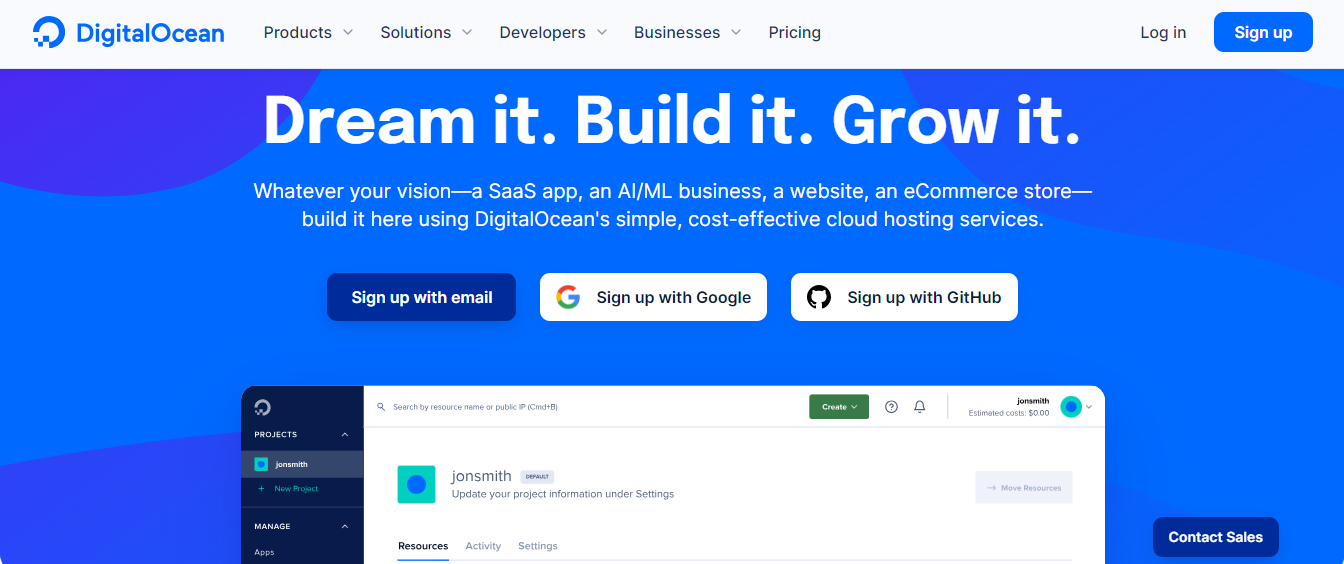
7. Digital Ocean
Another entry among the best DediPath alternatives is Digital Ocean.
Digital Ocean is a cloud infrastructure provider renowned for its developer-friendly solutions.
Key Features:
- Scalability: Digital Ocean’s cloud services are highly scalable, accommodating growing websites and applications.
- Developer-Friendly Tools: They provide a wide range of developer-friendly tools and resources.
- Community Support: Digital Ocean has an active community and extensive documentation to assist users.
- Global Data Centers: Data centers in various regions ensure low-latency access.
Why Digital Ocean is a Good DediPath Alternative:
Digital Ocean’s cloud infrastructure is well-suited for developers and businesses requiring scalable and flexible hosting solutions. Also, get a free $200 credit when you click on the link below.
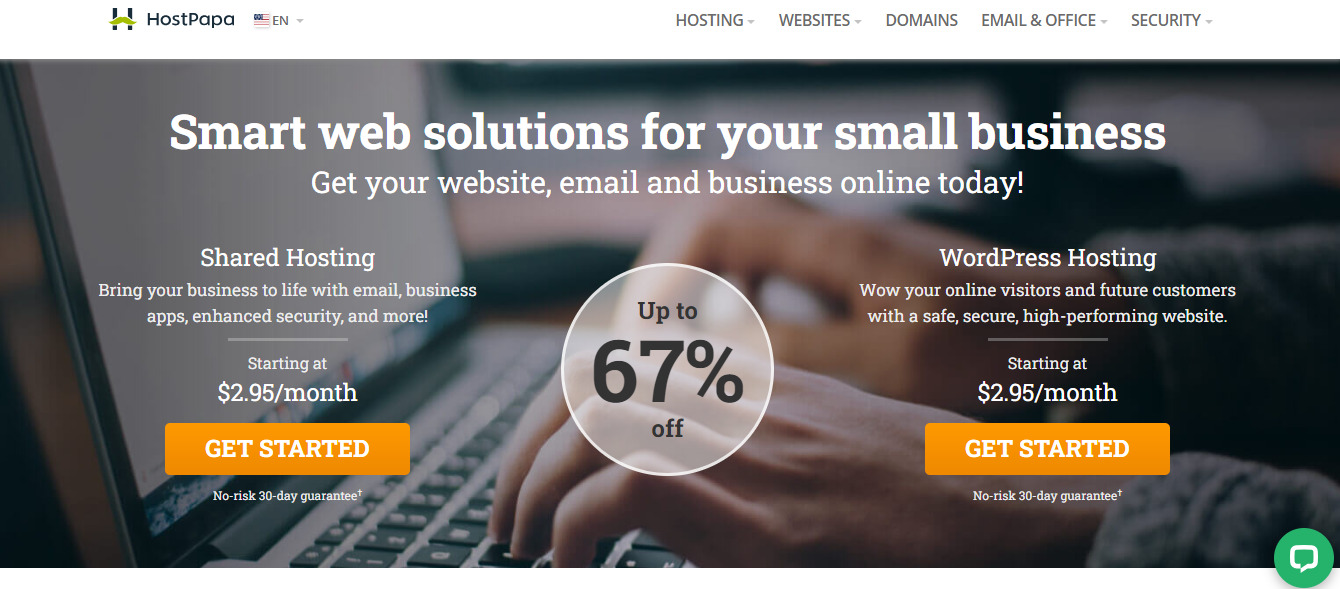
8. HostPapa
HostPapa is an environmentally conscious hosting provider offering shared, VPS, and reseller hosting.
Key Features:
- Sustainability: HostPapa prioritizes renewable energy and sustainability in its operations.
- Diverse Hosting Solutions: They offer various hosting plans to suit different needs.
- Customer Support: HostPapa provides 24/7 customer support to address any issues promptly.
- Free Website Migration: They offer free website migration services to ease the transition.
Why HostPapa is a Good DediPath Alternative:
If environmental sustainability is essential to you, HostPapa is an excellent choice. Their hosting services, combined with their commitment to green energy, make them a unique alternative.
9. Rebel Web Hosting
Rebel Web Hosting is a Canadian hosting provider known for its performance and security measures.
READ ALSO: Web Host Agents Scam Exposed [Eye Opener and Must Read]
Key Features:
- Speed: Rebel Web Hosting prioritizes speed with SSD-based storage and optimized server configurations.
- Security: They implement robust security measures to protect your websites and data.
- WordPress Hosting: Rebel Web Hosting offers specialized WordPress hosting plans.
- 24/7 Support: Their support team is available around the clock to assist with hosting issues.
Why Rebel Web Hosting is a Good DediPath Alternative:
Rebel Web Hosting’s focus on speed, security, and WordPress hosting makes it an excellent choice for businesses and individuals seeking high-performance hosting.
10. Bluehost
Last on our list of the best DediPath alternatives is Bluehost.
Bluehost is a hosting provider recommended by WordPress.org, making it an ideal choice for WordPress users.
Key Features:
- WordPress Integration: Bluehost offers specialized WordPress hosting with one-click installation.
- Scalability: They provide scalable hosting solutions to accommodate growing websites.
- Uptime: Bluehost maintains excellent uptime, ensuring your websites are accessible.
- 24/7 Support: Their support team can always assist with hosting-related queries.
Why Bluehost is a Good DediPath Alternative:
Bluehost’s close association with WordPress, scalability, and reliable support make it an attractive option for WordPress users and businesses needing hosting services.
What Is Web Hosting?
Web hosting is the service of storing websites on a server and making them accessible to users on the internet. When you create a website, you need to find a web hosting provider who will store your website’s files and make them available to visitors.
There are many different types of web hosting providers, each with its own advantages and disadvantages. Some of the most common types of web hosting include:
- Shared hosting: This is the most affordable type of web hosting. Your website will be hosted on a server with other websites. This means that your website’s resources will be shared with other websites, which can affect its performance.
- VPS hosting: This is a more expensive type of web hosting than shared hosting. You will be allocated a virtual private server (VPS) that is dedicated to your website. This means that your website will have its own resources and will not be affected by the performance of other websites.
- Dedicated hosting: This is the most expensive type of web hosting. You will be allocated a dedicated server that is exclusively used for your website. This means that you will have complete control over the server and its resources.
- Cloud hosting: This is a newer type of web hosting that uses a network of servers to host your website. This means that your website will be more reliable and scalable than with traditional web hosting.
WordPress hosting: This is a type of web hosting that is specifically designed for WordPress websites. WordPress is a content management system (CMS) that makes it easy to create and manage a website. WordPress hosting providers offer features that are specifically designed to improve the performance and security of WordPress websites.
What is the Best DediPath Alternative?
Hostinger is the best DediPath alternative for most users. It offers affordable, reliable, and feature-rich dedicated servers. Hostinger also offers a 30-day money-back guarantee, so you can try their services risk-free.
Here are some of the reasons why Hostinger is a great DediPath alternative:
- Affordable: Hostinger’s dedicated servers start at just $79.99 per month, making them one of the most affordable options available.
- Reliable: Hostinger has a 99.9% uptime guarantee, so you can be confident that your website will be up and running 24/7.
- Feature-rich: Hostinger’s dedicated servers have various features, including unmetered bandwidth, root access, and DDoS protection.
- Money-back guarantee: Hostinger offers a 30-day money-back guarantee, so you can try their services risk-free.
If you are looking for a reliable and affordable DediPath alternative, Hostinger is a great option.
Best DediPath Alternatives: Frequently Asked Questions
Unfortunately, DediPath ceased operations in September 2023, leaving users scrambling for alternatives.
Here are answers to frequently asked questions about finding the best DediPath alternatives:
What are the most important factors to consider when choosing a DediPath alternative?
Several factors play a crucial role:
- Server Specifications: Match your specific needs for CPU, RAM, storage, and bandwidth. Consider the type of workload you’ll be running (e.g., web hosting, gaming, development).
- Location: Choose a data center location that offers optimal latency and performance for your target audience or application.
- Pricing: Compare different providers’ pricing models, including upfront costs, monthly fees, and any additional charges.
- Features and Support: Look for features like backups, disaster recovery, control panel access, and reliable customer support.
- Reputation and Reliability: Research the provider’s reputation and track record for uptime, security, and customer service.
What are some popular DediPath alternatives?
Several providers offer comparable services, each with its own strengths and weaknesses:
- Hostinger: Renowned for reliable infrastructure, competitive pricing, and global data centers.
- OVH Cloud: Offers various server options, including dedicated, cloud, and VPS, with a strong European presence.
- Interserver Hosting: Known for affordable dedicated and cloud servers, but with limited data center locations.
- GoDaddy: Offers high-performance dedicated servers with flexible configurations and good customer support.
- Namecheap: Popular for affordable VPS and cloud server options, but dedicated server options may be limited.
Conclusion
These best DediPath alternatives offer various features and services to cater to multiple hosting needs. Consider your specific requirements, budget, and preferences when selecting an option.
Nevertheless, I highly recommend Hostinger, Namecheap, Interserver Hosting, GoDaddy, and OVH Cloud as alternatives to DediPath.
Each hosting provider has its strengths, whether it’s affordability, performance, or specialized services, to ensure a smooth transition after DediPath’s shutdown.
Be sure to back up your data and plan your migration carefully to make the transition seamless.
INTERESTING POSTS
- 15 Best And Most Secure Web Hosting Services [Tested & Ranked]
- 10 Best Web Hosts Reddit Users Love And Upvoted
- 6 Tips To Share Information Using Cloud Storage Secretly
- How To Host Website on Namecheap
- Best VPN For 2023
- Best Antivirus For 2023
- 7 of the Best VPN For Upwork (With Dedicated IP Address)
- Best Google Products Alternatives
About the Author:
Daniel Segun is the Founder and CEO of SecureBlitz Cybersecurity Media, with a background in Computer Science and Digital Marketing. When not writing, he's probably busy designing graphics or developing websites.