Learn how to protect your computer from malware in this post.
Malware, short for malicious software, is a broad term used to describe any software designed to damage, disrupt, or gain unauthorized access to a computer system. Cybercriminals use malware to steal personal information, commit fraud, and cause severe damage to your computer.
Protecting your computer from malware is crucial to safeguard your personal information and prevent unauthorized access to your system.
READ ALSO: Comprehensive Malware Guide: Safeguarding Your Digital World
Table of Contents
What Is Malware?

Malware, short for malicious software, is a term used to describe harmful programs or code that invade and damage computer systems, networks, and devices.
Malware can take partial control over a device and interfere with its normal functioning. It can steal or delete data, alter computer functions, and spy on user activity.
The motives behind malware vary, from making money to causing disruption or making political statements. Cybercriminals often use malware to steal sensitive information such as passwords and financial data.

Common signs of malware infection include:
- a slow computer
- inundation of annoying ads
- system crashes
- mysterious loss of disk space
- increased internet activity
- changes in browser settings
- disabled antivirus software
- loss of access to files or the entire computer
It is important to have a reliable cybersecurity program to detect and remove malware. With the increasing use of technology in our daily lives, it is crucial to be aware of the potential risks posed by malware and take appropriate measures to protect ourselves from these threats.
In this comprehensive guide, we will discuss the best practices you can follow to protect your computer from malware.
We have gathered information from various sources to provide you with a complete overview of the steps you can take to ensure the safety of your computer.
READ ALSO: Network Firewalls: Comprehensive Guide For Non-Tech-Savvy People
How To Protect Your Computer From Malware
1. Use Strong Passwords

Protecting your computer from malware is crucial, and using strong passwords is one of the most basic yet essential steps you can take to safeguard your personal information.
Malware can cause severe damage, and cyber criminals use password-cracking tools to gain access to your sensitive data. However, by implementing a few simple measures, you can keep your computer safe from cyber threats.
One such measure is to use a strong password. A strong password that contains a combination of upper and lower-case letters, numbers, and special characters is much harder for hackers to crack. Remember to avoid using easily guessable passwords like your name, date of birth, or common words.
Taking this simple step can make a significant difference in keeping your computer and personal information secure.
Alternatively, you can make use of password managers to manage your strong passwords:
2. Use a Firewall

A firewall is a security tool that serves as a proactive measure in monitoring and controlling incoming and outgoing network traffic. Its primary function is to act as a barrier between your computer and the internet, thereby effectively blocking unauthorized access to your system.
This ensures that your system is safe from various types of online threats, especially malware. Firewalls are designed to detect and prevent malware from infiltrating your system by analyzing all data packets that enter and leave your computer.
Firewalls are essential tools for protecting your computer from malware, which is a significant online threat.
Malware is a malicious software that is designed to damage or gain access to computer systems without the owner’s knowledge or consent. This can lead to data theft, financial loss, and other severe consequences.
Firewalls can prevent malware from entering your computer and causing damage by identifying and blocking malicious traffic. By using a firewall, you can ensure that your computer is safe and secure from online threats.
GlassWire is a recommended firewall solution to protect your computer against malicious software.
3. Install Antivirus Software

As a computer user, it is imperative that you safeguard your system from various online threats, and malware is undoubtedly one of the most prevalent ones that can wreak havoc on your system.
However, by installing an antivirus software, you can keep your computer protected from these malicious programs.
READ ALSO: The Best Antivirus Software
Antivirus software works by scanning your computer regularly for malware and other harmful programs. It efficiently removes the detected threats and ensures that your system runs smoothly without any interruption.
Apart from detecting and removing malware, antivirus software also alerts you if you are about to download a potentially harmful file or visit an unsafe website. It acts as a protective shield between your computer and the internet, ensuring that your online activities remain safe and secure.
However, it is essential to note that malware is constantly evolving, and new threats are emerging every day. Hence, it is imperative that you keep your antivirus software updated to ensure that you have the latest protection against these emerging threats.
Regular updates ensure that your antivirus software stays up-to-date with the latest malware definitions, and your system remains protected from the latest security vulnerabilities.
So, make sure to install a reliable antivirus software and keep it updated regularly to stay protected from the ever-increasing number of malware threats.
Recommended Antivirus Solutions
4. Keep Your Software Updated

In today’s age of technological advancements, malware has become a major concern for computer users. It can break into your system and cause irreparable damage to your data. That’s why it’s imperative to keep your software up to date at all times.
Outdated software can leave your computer vulnerable to cybercriminals who are constantly on the lookout for ways to exploit software vulnerabilities.
To ensure that your computer is well-protected against such malicious attacks, it is highly recommended to install software updates as soon as they become available. This applies not just to your operating system and web browser but also to any other software installed on your computer.
Installing software updates can help you mitigate the risks associated with cyber threats and keep your data safe from prying eyes. It is a simple yet effective way of preventing malware attacks and safeguarding your system against cyber threats.
So, make sure to regularly check for software updates and install them without any delay. By doing so, you can rest assured that your computer is always secured against potential threats.
5. Minimize Downloads

As technology continues to advance, the risk of malware invasion has become a significant concern for individuals and businesses alike. Malware is a malicious software program created by cybercriminals to infect and damage computer systems.
It can be introduced into your computer through various channels, with downloads being one of the most common ways. Cybercriminals are known to disguise malware as legitimate files, making it difficult for users to distinguish between safe and harmful downloads.
In order to protect your computer from malware, it is vital to exercise caution when downloading files. It is prudent to minimize downloads and only download files from trusted sources.
It is not uncommon for cybercriminals to make use of free software downloads to introduce malware into unsuspecting users’ computers. Therefore, it is crucial to be cautious of free software downloads and conduct thorough research before downloading anything.
By being vigilant and cautious, you can protect your computer from the harmful effects of malware.
Remember that prevention is always better than cure, and taking the necessary steps to minimize malware downloads can save you from significant financial and personal loss. Be a responsible computer user and protect your valuable information from cybercriminals.
6. Use a Pop-Up Blocker

Pop-up ads have become an increasingly pervasive annoyance for computer users worldwide. Not only can they disrupt your browsing experience, but they can also pose serious risks to your computer’s security.
Cybercriminals have cleverly integrated malware into pop-up ads, using them as a tool to trick unsuspecting users into inadvertently downloading malicious software or visiting dangerous websites.
To protect your computer from these potential threats, it is crucial to employ effective security measures.
One such measure is the installation of a reliable pop-up blocker. This powerful tool acts as a shield, preventing these bothersome ads from appearing on your screen in the first place.
By blocking pop-up ads, you significantly reduce the chances of falling victim to cyberattacks and unintentionally downloading malware.
By implementing a pop-up blocker, you can navigate the internet with peace of mind, knowing that your computer is shielded from the dangers lurking within pop-up ads. This proactive approach to safeguarding your computer ensures a smooth and secure browsing experience.
So, take the necessary steps to protect your computer from malware and utilize a pop-up blocker to ward off those pesky and potentially harmful ads that can compromise your online security.
READ ALSO: Computer Viruses Guide: Eradicate Digital Threats
7. Enable Click-to-Play Plugins

In order to effectively protect your computer from malware, it is crucial to take proactive measures. One such measure is to be cautious about the plugins you use, as certain plugins like Flash and Java can potentially deliver malware to your computer.
To mitigate this risk, it is highly recommended to enable click-to-play plugins in your web browser. By doing so, you gain control over which plugins run automatically, thereby significantly reducing the risk of malware infections.
This simple yet effective step empowers you to safeguard your computer and its sensitive data from potential threats.
So, make sure to prioritize the security of your computer by enabling click-to-play plugins and enjoy a worry-free browsing experience.
Your computer’s safety should never be compromised, and by taking this precautionary step, you can rest assured that you are doing your part to keep it secure.
So, don’t wait any longer – take action today to protect your computer from malware and enjoy a safer online experience.
8. Don’t Click on Links in Emails

Phishing emails are a disturbingly widespread tactic employed by cybercriminals to propagate malware.
These craftily designed messages frequently lure unsuspecting individuals into clicking on links that direct them to malicious websites or downloading attachments containing harmful malware.
Thus, it is of the utmost importance to exercise extreme caution when encountering such emails. To protect your computer from the threats posed by these malevolent messages, it is crucial to adopt a series of proactive measures.
First and foremost, refrain from clicking on any links embedded within emails unless you are absolutely certain of their legitimacy.
Conduct a thorough examination of the sender’s email address, as it often serves as a telltale sign of illegitimate correspondence.
Be especially wary of emails that exhibit an aura of urgency or contain suspicious requests. By implementing these precautionary measures, you can effectively safeguard your computer from the detrimental impact of malware.
Recommended Email Solutions
9. Remove Unused Software
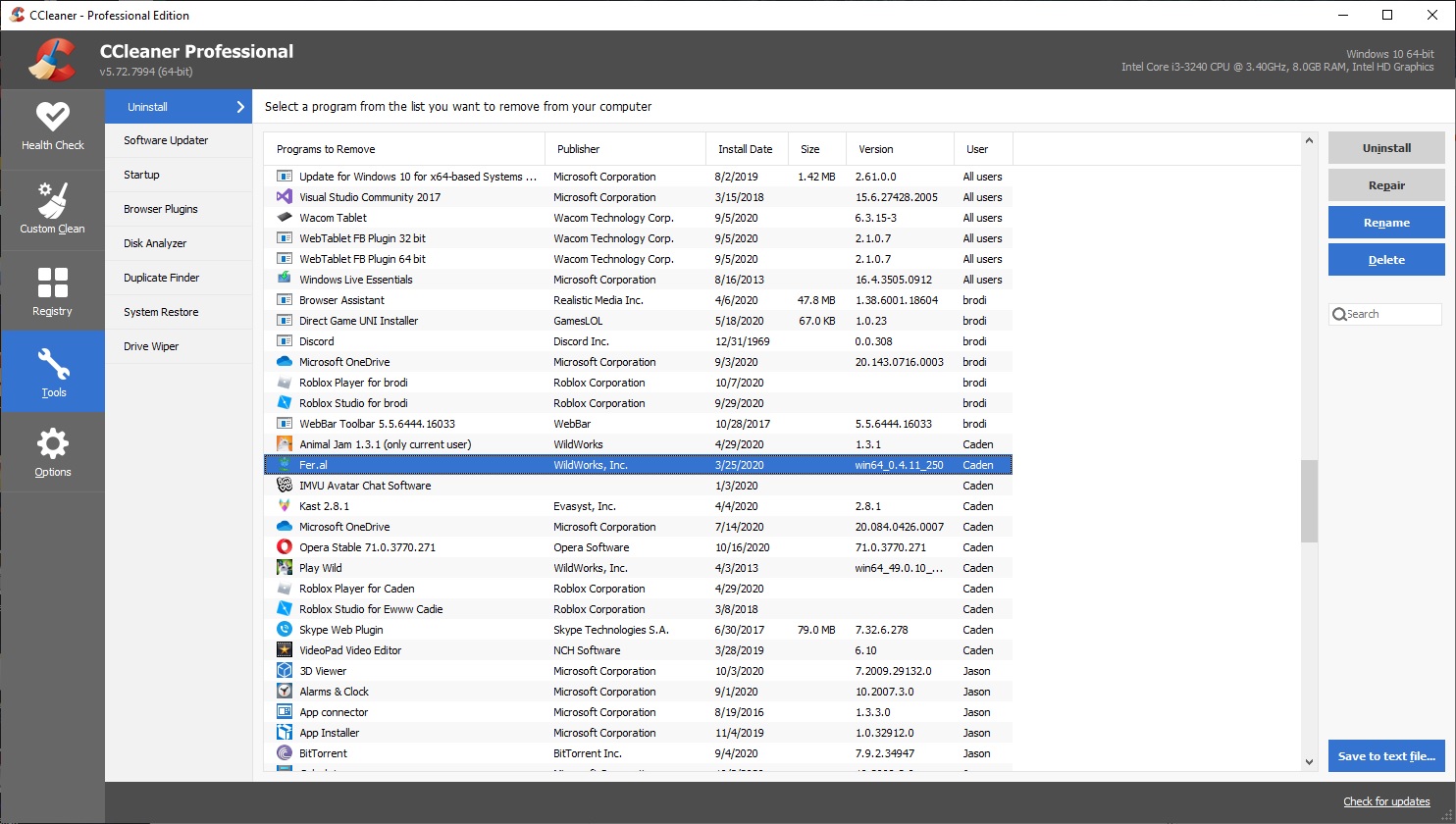
It is crucial to protect your computer from malware, and one way to do so is by addressing the security risks associated with unused software.
Cybercriminals are constantly on the lookout for vulnerable targets, and outdated or unused software presents an ideal opportunity for them to gain unauthorized access to your system.
To mitigate this risk, it is strongly recommended to remove any software that you no longer use.
By eliminating unused software from your computer, you not only declutter your system but also significantly reduce the chances of malware infections.
Outdated software often lacks the necessary security updates, making it an easy target for cyberattacks.
Therefore, it is vital to regularly review your installed programs and uninstall any applications that are no longer needed.
Taking this proactive approach to managing your software not only enhances the overall security of your computer but also ensures optimal performance. By removing unnecessary software, you free up valuable system resources, allowing your computer to function more efficiently.
To protect your computer from malware, it is advised to adopt a cautious approach towards software management. Regularly update your existing programs to the latest versions and promptly remove any unused software.
By doing so, you create a safer digital environment for yourself, minimizing the risk of cyber threats and safeguarding your valuable data.
CCleaner is a recommended solution for removing used software from your computer.
10. Back Up Your Data

Backing up your data is not only a good practice, but it is also critical to protect your computer from malware. Malware infections can wreak havoc on your personal information and files, leaving you vulnerable and potentially losing access to all your valuable data.
By regularly backing up your data, you are taking a proactive approach to safeguarding your computer and ensuring that even if it does become infected with malware, you can easily recover your files.
This simple step can save you from a lot of stress and frustration in the long run. So, don’t wait until it’s too late. Take the necessary steps to protect your computer from malware, starting with backing up your data regularly.
By backing up your data, you are effectively creating a safety net for your computer. This safety net ensures that no matter how severe the malware infection is, you will always have a copy of your files stored securely. It’s like having a spare key to your house in case you lose the original one.
Recommended Cloud Backup Solutions:
Similarly, backing up your data provides you with a backup plan in case the worst happens. It’s a proactive measure that safeguards your personal information and files.
Moreover, backing up your data is not as complicated as it may seem. There are various options available to suit your needs and preferences. You can choose to back up your data to an external hard drive, a USB flash drive, or even a cloud storage service. The choice is yours.
The important thing is to ensure that you have a backup strategy in place. It’s like having an insurance policy for your data, giving you peace of mind knowing that your valuable information is protected.
How To Protect Your Computer From Malware: FAQs
Here are answers to some frequently asked questions on protecting your computer from malware:
What are ways to prevent malware?
There are several ways to prevent malware infections:
- Keep your software updated: This includes your operating system (Windows, Mac, etc.), web browser, and any other applications you use. Updates often contain security patches that fix vulnerabilities malware can exploit.
- Use a reputable antivirus and anti-malware program: These programs can scan your computer for malware and remove it. There are both free and paid options available.
- Be cautious about what you click on: Phishing emails and malicious links can install malware on your computer. Don’t click on suspicious links or attachments, even if they appear to be from someone you know.
- Beware of free downloads: Free software can sometimes be bundled with malware. Only download software from trusted sources.
- Enable firewalls: Firewalls can help block unauthorized incoming connections that might try to install malware.
What is the best protection against malware?
A layered approach is most effective. Using a combination of the methods mentioned above (updated software, antivirus, safe browsing habits) will significantly reduce your risk.
How do I make sure my computer is malware free?
- Regularly scan your computer with your antivirus or anti-malware program. Most offer scheduled scans to proactively check for threats.
- If you suspect your computer might already be infected, some antivirus programs offer on-demand scans or specific tools for malware removal. Note: In severe cases, professional help from a computer technician might be necessary.
How do I protect my Windows 10 from malware?
The advice above applies to Windows 10 as well. Windows 10 actually comes with a built-in antivirus program called Microsoft Defender that can provide basic protection. You can choose to use this or another reputable antivirus program.
What is the best software to protect your computer from hackers?
While antivirus software can help protect against malware attacks often used by hackers, a comprehensive security approach is ideal. This includes using strong passwords, being mindful about what you download and click on, and potentially using a firewall and other security tools depending on your specific needs. There’s no single “best” software solution, but reputable antivirus programs can be a valuable line of defense.
Conclusion
Protecting your computer from malware is crucial to safeguard your personal information and prevent unauthorized access to your system.
By following the steps outlined in this guide, you can ensure the safety of your computer and reduce the risk of malware infections.
Remember to always keep your software updated, use strong passwords, and be cautious of downloads and emails from unknown sources. Stay vigilant and stay safe.
INTERESTING POSTS
- How To Secure Your Computer Against Cyber Threats Like 007
- Types Of Pop-ups Every eCommerce Store Should Have
- How To Install Surfshark VPN On Your Devices
- Oh No! The data of 21 million free VPN users has been exposed
- Online Privacy – Why It’s Important And How To Protect It
- How To Check If Someone Is Using Your Social Security Number
- What Is A Fake Antivirus? Overview And How To Spot Them
About the Author:
Meet Angela Daniel, an esteemed cybersecurity expert and the Associate Editor at SecureBlitz. With a profound understanding of the digital security landscape, Angela is dedicated to sharing her wealth of knowledge with readers. Her insightful articles delve into the intricacies of cybersecurity, offering a beacon of understanding in the ever-evolving realm of online safety.
Angela's expertise is grounded in a passion for staying at the forefront of emerging threats and protective measures. Her commitment to empowering individuals and organizations with the tools and insights to safeguard their digital presence is unwavering.